The Challenge
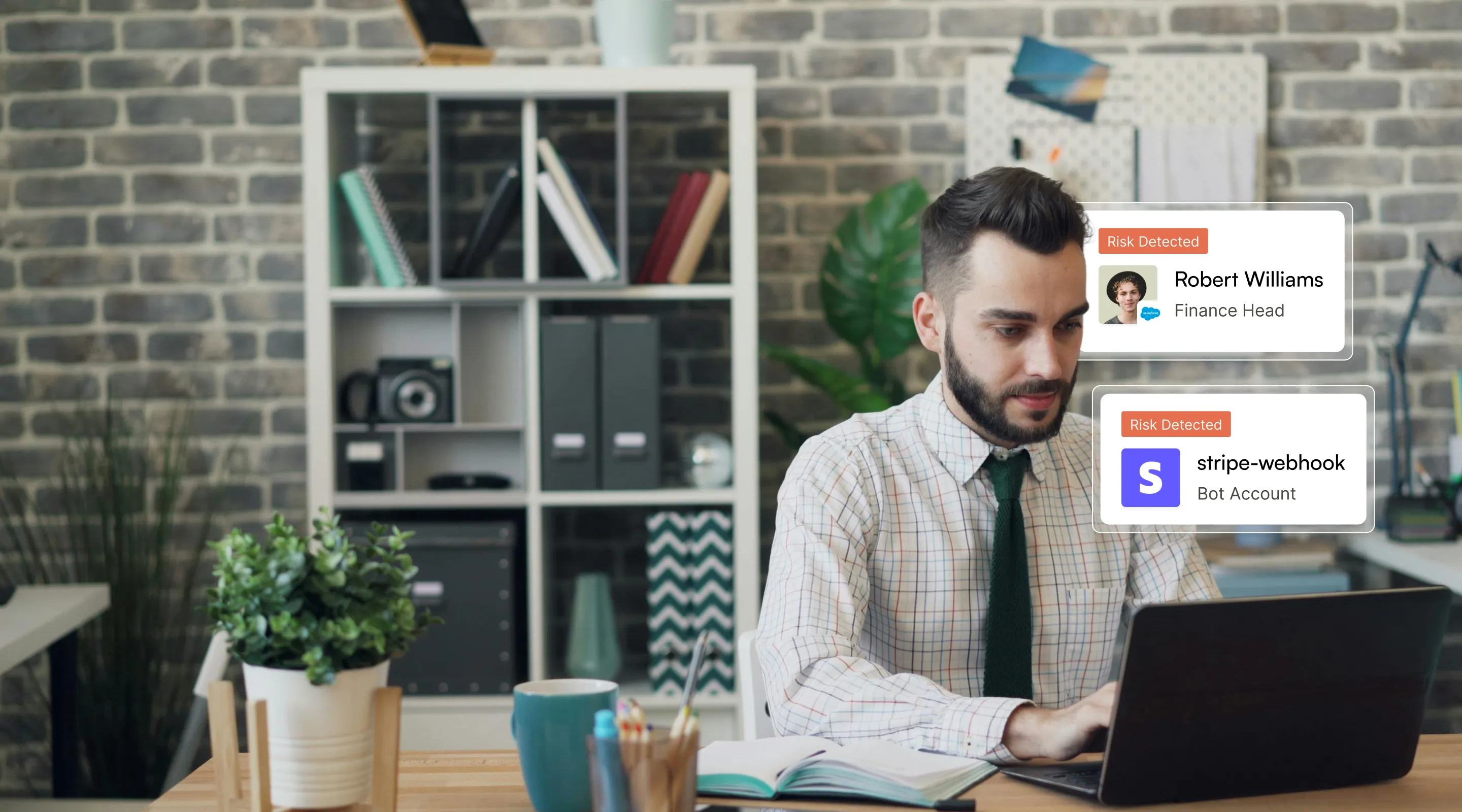
Identity Risk Changes Faster Than Access Reviews
80% of breaches involve compromised identities.1 Yet most organizations still rely on periodic access reviews while permissions change constantly across SaaS apps, cloud infrastructure, and service accounts. Risk accumulates quietly until an incident exposes it. Identity risk is continuous. Your defenses should be too.
Fragmented visibility
Identity data is spread across IdPs, SaaS apps, directories, and cloud platforms.
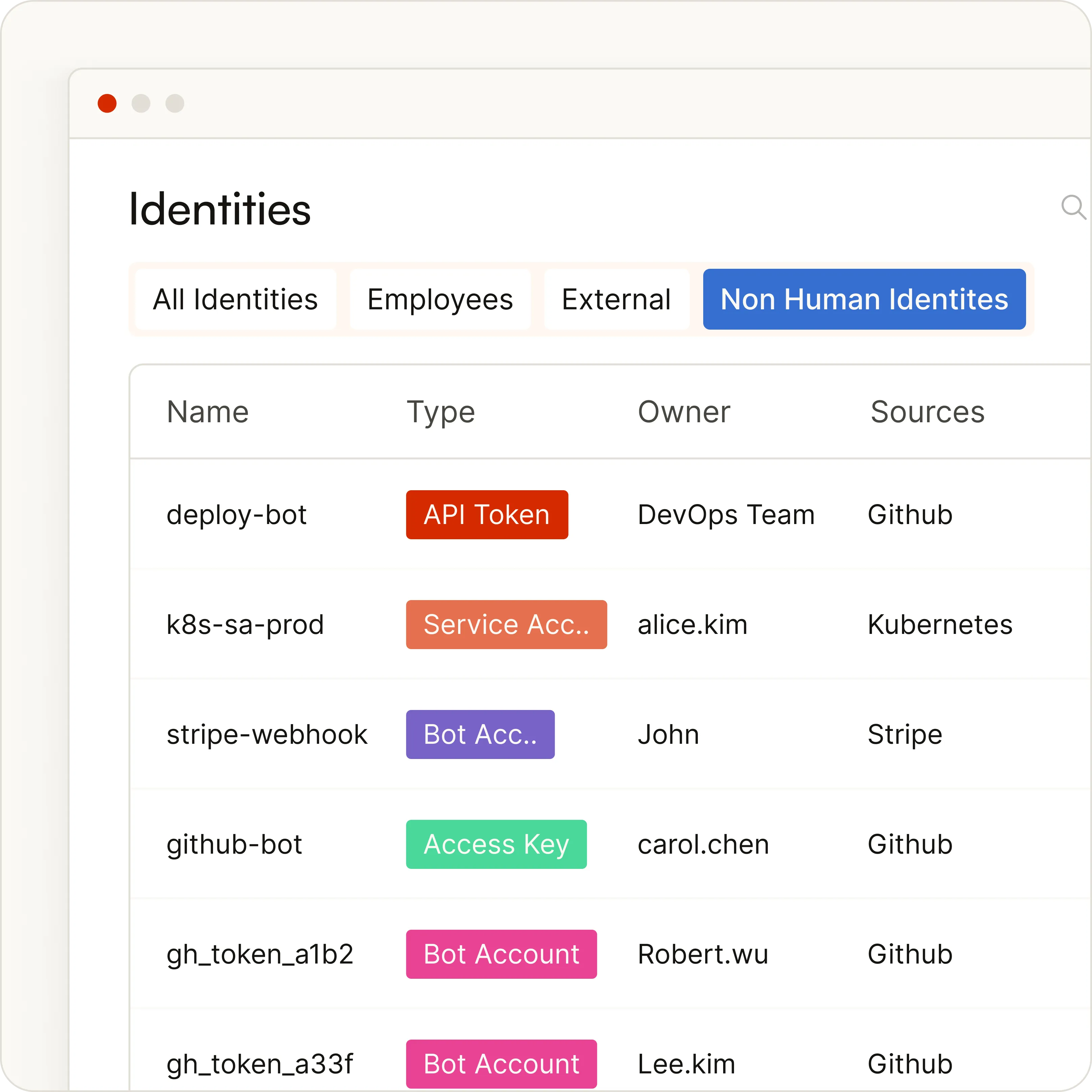
Exploding non-human identities
Bots, API keys, service accounts, and AI agents now outnumber human users.
Entitlement creep
Temporary access quietly becomes permanent.
Manual remediation
Security teams still investigate identity risk through tickets and spreadsheets.
capabilities
Identity Security That Runs Continuously
Zluri ISPM replaces periodic reviews with continuous identity security monitoring and remediation.
Discover & Map
Discover Every Identity
Most tools only see identities connected to your IdP. Zluri goes deeper, giving visibility across human and non-human identities in minutes.
Discover identities across SaaS apps and cloud platforms
Map entitlements across 300+ integrations
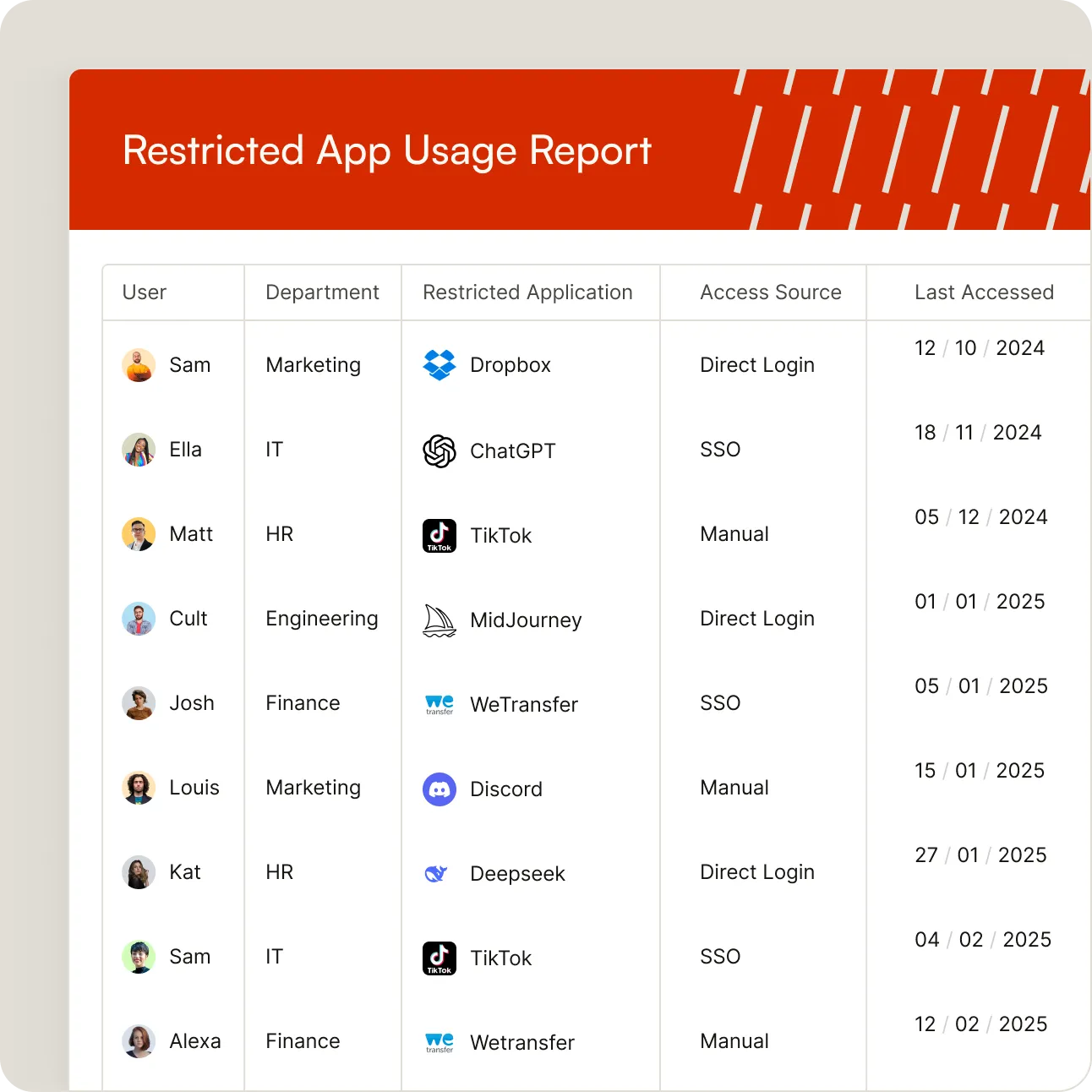
Detect shadow IT and unmanaged access paths
Correlate identity data with activity signals
Assess Risk
Prioritize the Risks That Matter
Not all identity risks are equal. Zluri analyzes exposure using risk signals like privilege level, blast radius, exploitability, and activity patterns, helping identify and fix highest impact risks first:
Over-privileged admin accounts
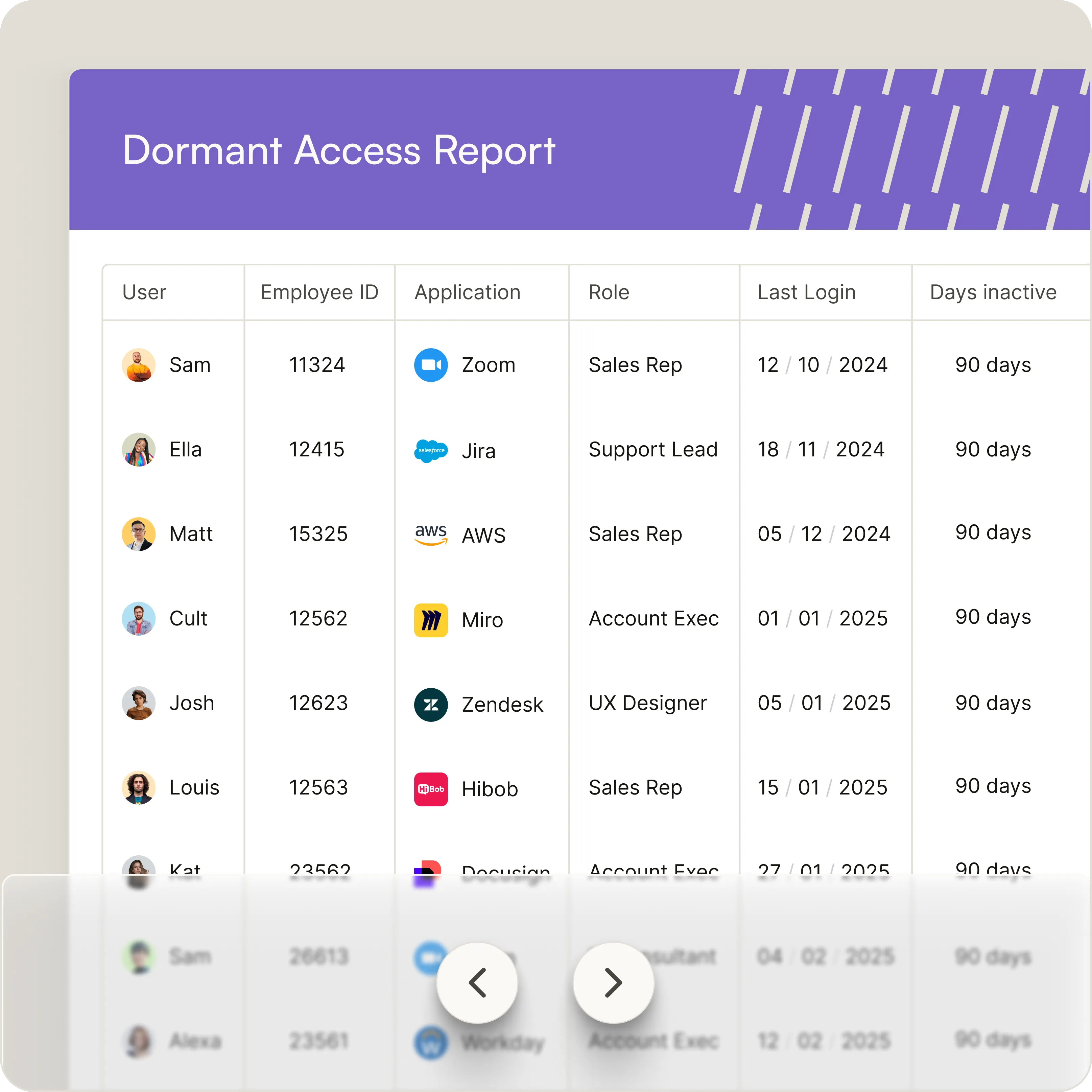
Dormant or zombie identities
MFA gaps and misconfigured policies
Toxic permission combinations
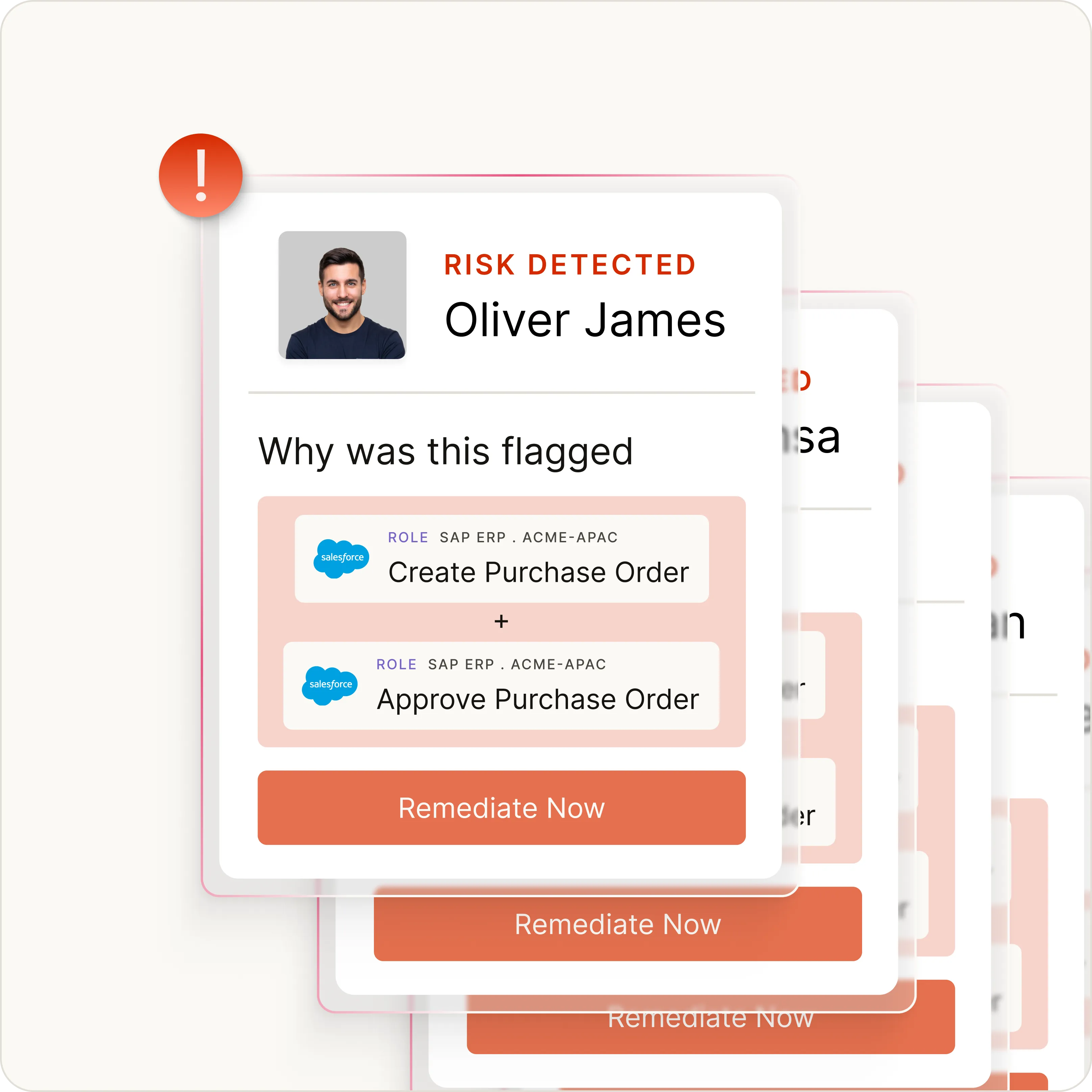
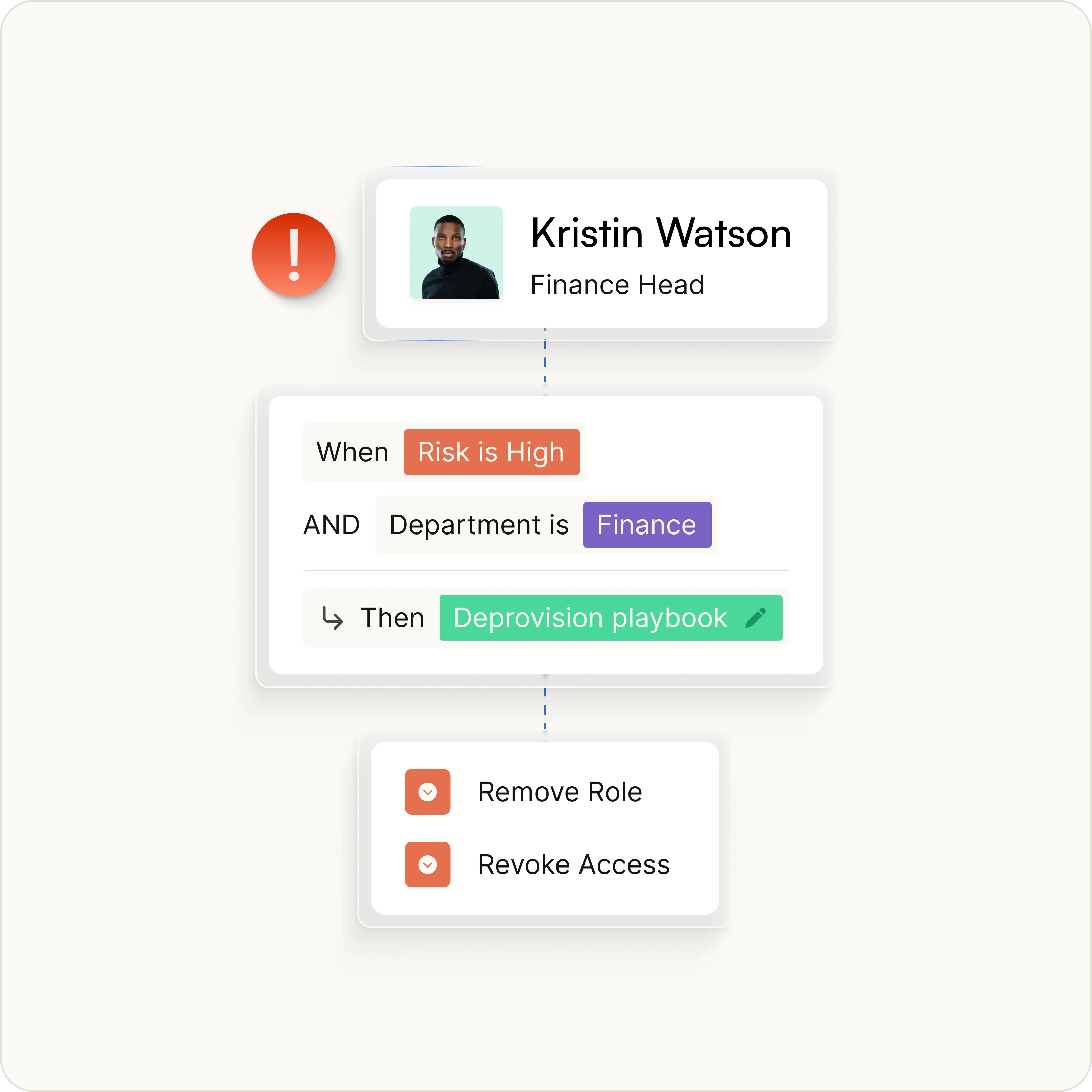
Auto-Remediate
Remediate Identity Risk Automatically
Most tools stop at detection. Zluri closes the loop by helping resolve identity risks instantly or routing changes through approval workflows.
Automatically revoke excessive privileges
Trigger 1500+ automated remediation actions
Build workflows with a no-code policy engine
Maintain full audit trails
Monitor & Report
Monitor Identity Posture in Real Time
Identity security is not a quarterly exercise. Zluri continuously tracks posture and keeps teams audit-ready.
Real-time identity risk dashboards
Full remediation history and audit trails
Identity risk trend analysis
Compliance reports for SOC2, ISO27001, HIPAA, and SOX
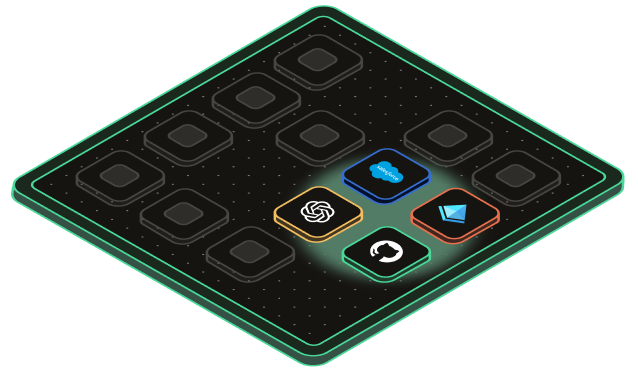
Built on Zluri’s Identity Security Platform
ISPM runs on Zluri’s unified identity platform with deep integrations across your environment.
















Use cases
From Passive Risk Monitoring to Proactive Identity Defenses
Identify and remediate identity risks before they become security incidents.
Enforce Least Privilege
Permissions expand silently as employees change roles and adopt new tools. Zluri continuously right-sizes access.
Secure Non-Human Identities
Machine identities now outnumber humans 82:12. Zluri discovers, monitors, and remediates risk across service accounts, API keys, bots, and AI agents.
Maintain Continuous Compliance
Automated evidence collection keeps organizations audit-ready.
Eliminate Offboarding Gaps
Detect and remove lingering access from former employees.
why zluri
Most ISPM Tools Detect Identity Risk. Zluri Detects and Fixes It.
Capability

Traditional IGA
Identity discovery
Activity Intelligence
%201.svg)
Non-human identity coverage
Risk Insights
%201.svg)
Remediation
%201.svg)
Deployment
Tag here
Proof of Value
10x
faster access reviews with Zluri’s automation engine
Weeks
faster access reviews with Zluri’s automation engine
Frequently Asked Questions







.webp)

.svg)














