The Challenge
You Can’t Secure What You Can’t See
Identity is now the primary attack surface, spanning humans, service accounts, AI agents, and APIs. Securing it means understanding how identities and access paths connect, not just managing them.
Identity now includes humans, machines, and AI agents
Access is created and used at machine speed across SaaS and cloud. Governance built for humans alone no longer works.
Non-human identities lack ownership
Service accounts, tokens, bots, and AI agents persist without clear accountability or lifecycle control.
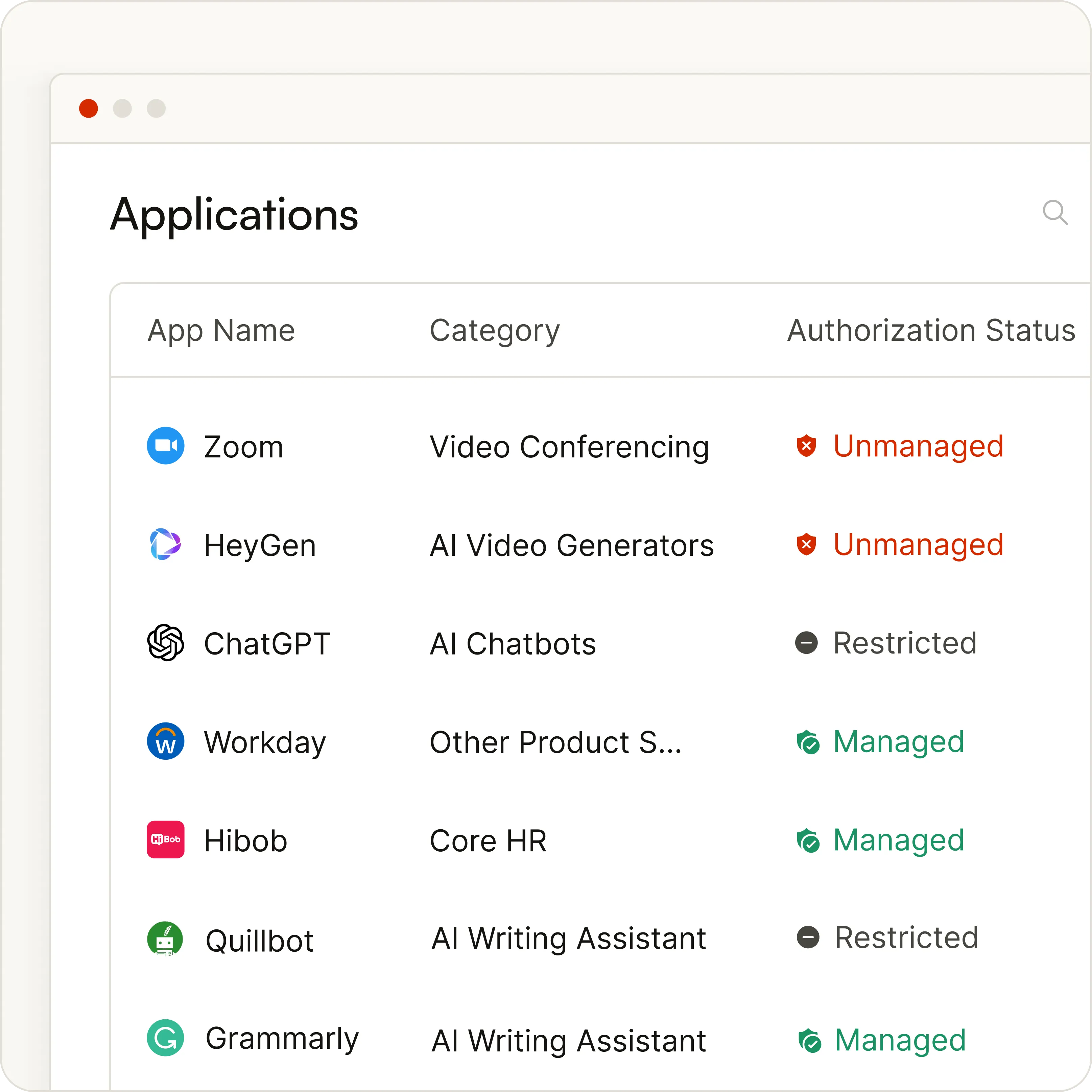
Shadow AI expands exposure
Agent-based integrations and OAuth apps create unseen access paths beyond approved systems.
Visibility is fragmented
Identity, entitlement, and activity data live in silos, leaving risk without context.
Risk is detected too late
Dormant accounts, excessive privileges, and autonomous agents remain active until after impact.
capabilities
What Makes IVIP Best-in-Class: Granular Visibility. Continuous Intelligence. Instant Action.
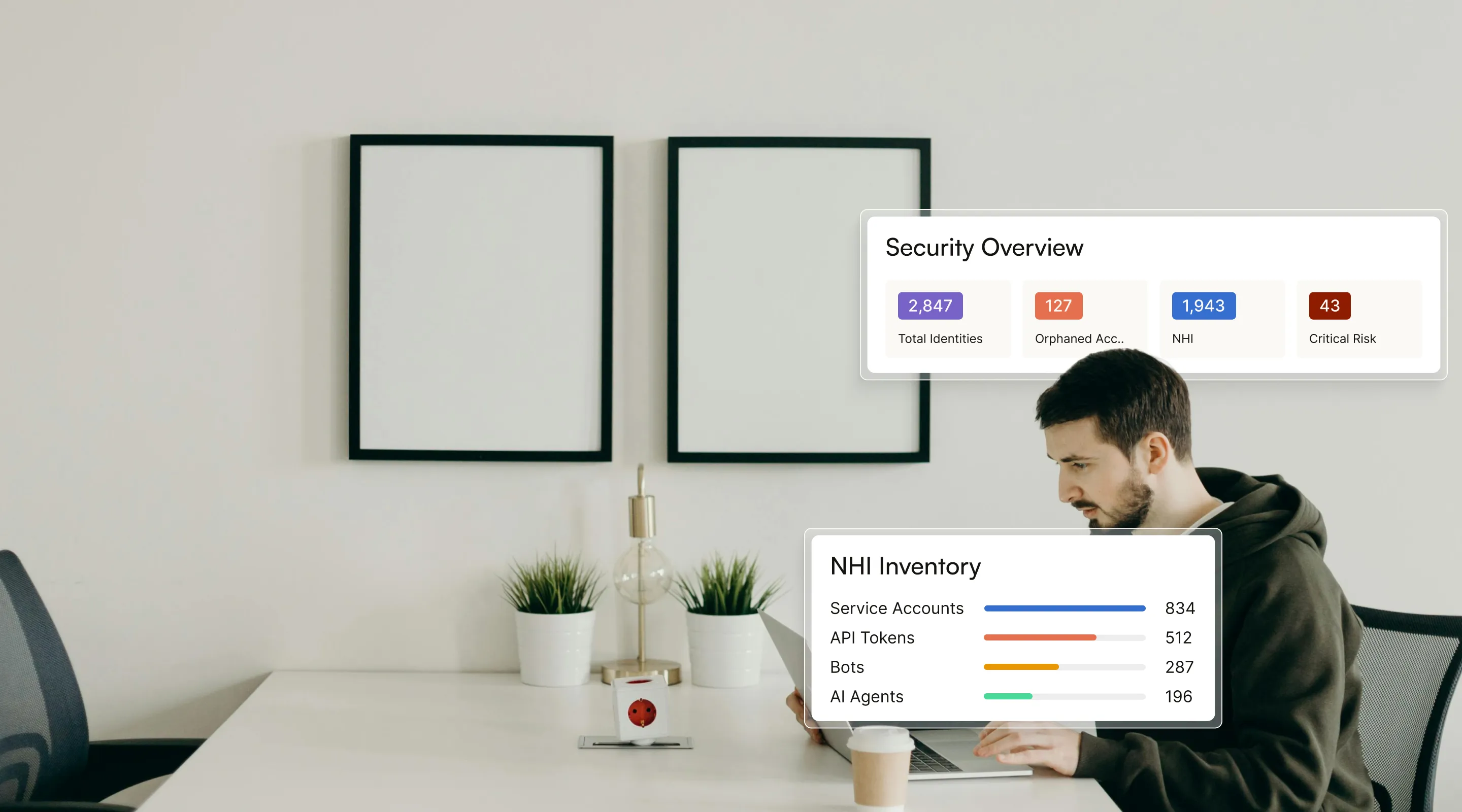
Patented Discovery Engine
Discover Every Identity. Everywhere.
IVIP ingests identity data across SSO, HR, finance, CASB, MDM, directories, endpoints, APIs, and on-premises systems to create a single, unified inventory beyond SSO-only detection.
Track every human and non-human identity across SaaS, cloud, and on-premises environments from day one
Govern service accounts, tokens, bots, workloads, and AI agents with enforced ownership and lifecycle control
Detect unmanaged and shadow IT or AI apps in real time with authorization context
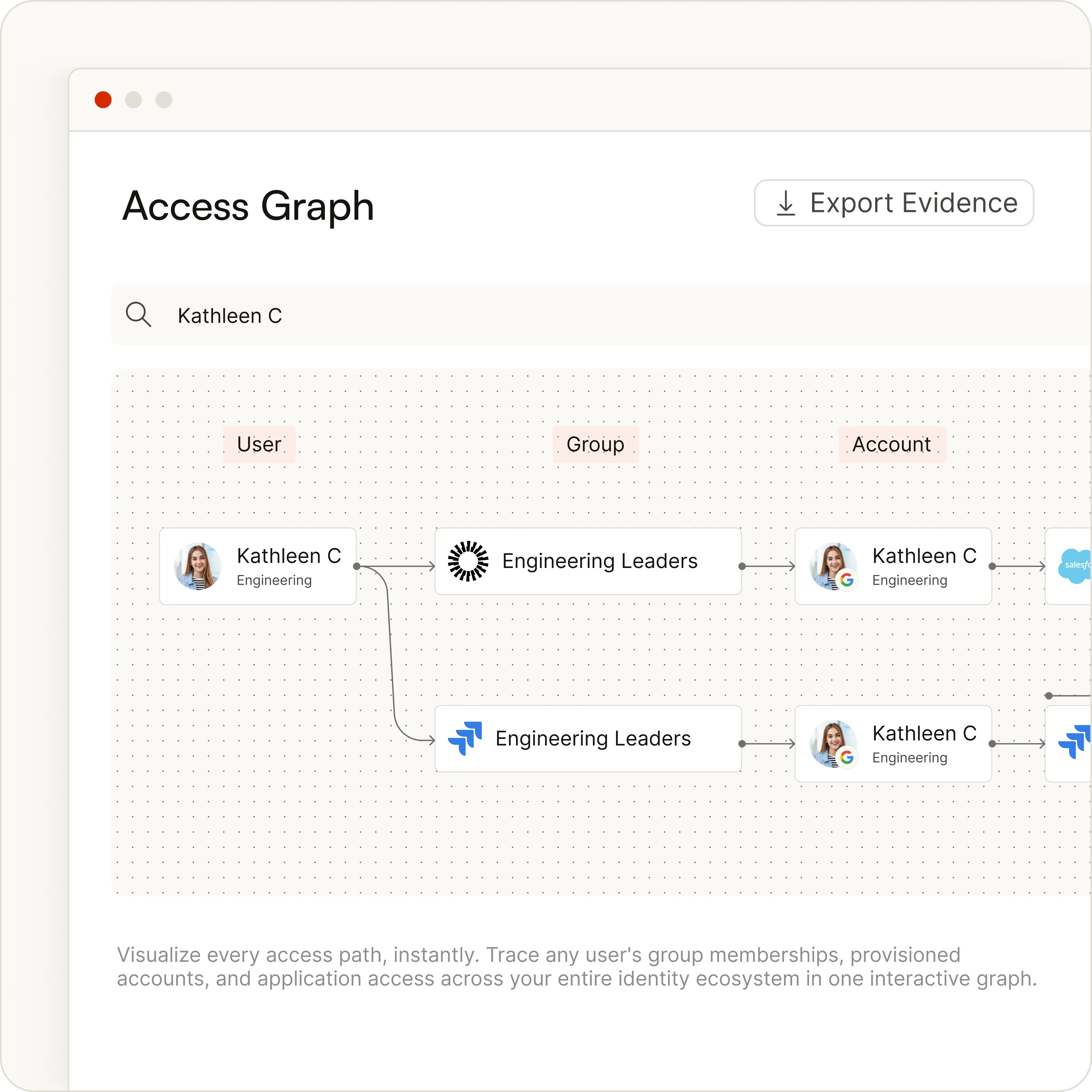
Unified Identity Graph
See How Every Identity Connects
Permission lists show who has access. IVIP shows how it was granted, how it spreads, and where risk concentrates. The Identity Graph connects identities, roles, entitlements, grant sources, and activity into a single, system-wide model.
Visualize access paths across human and non-human identities
Surface dormant access, orphaned accounts, and privilege creep
Expose escalation paths and toxic combinations before they are exploited
Continuous Activity Intelligence
Act on Risk in Real Time
Static reports create noise. IVIP continuously analyzes identity behavior, entitlement changes, and access patterns to surface what actually matters
Detect anomalies and peer outliers instantly
Identify dormant, orphaned, and overprivileged identities
Dynamically score and prioritize risk by impact and exposure

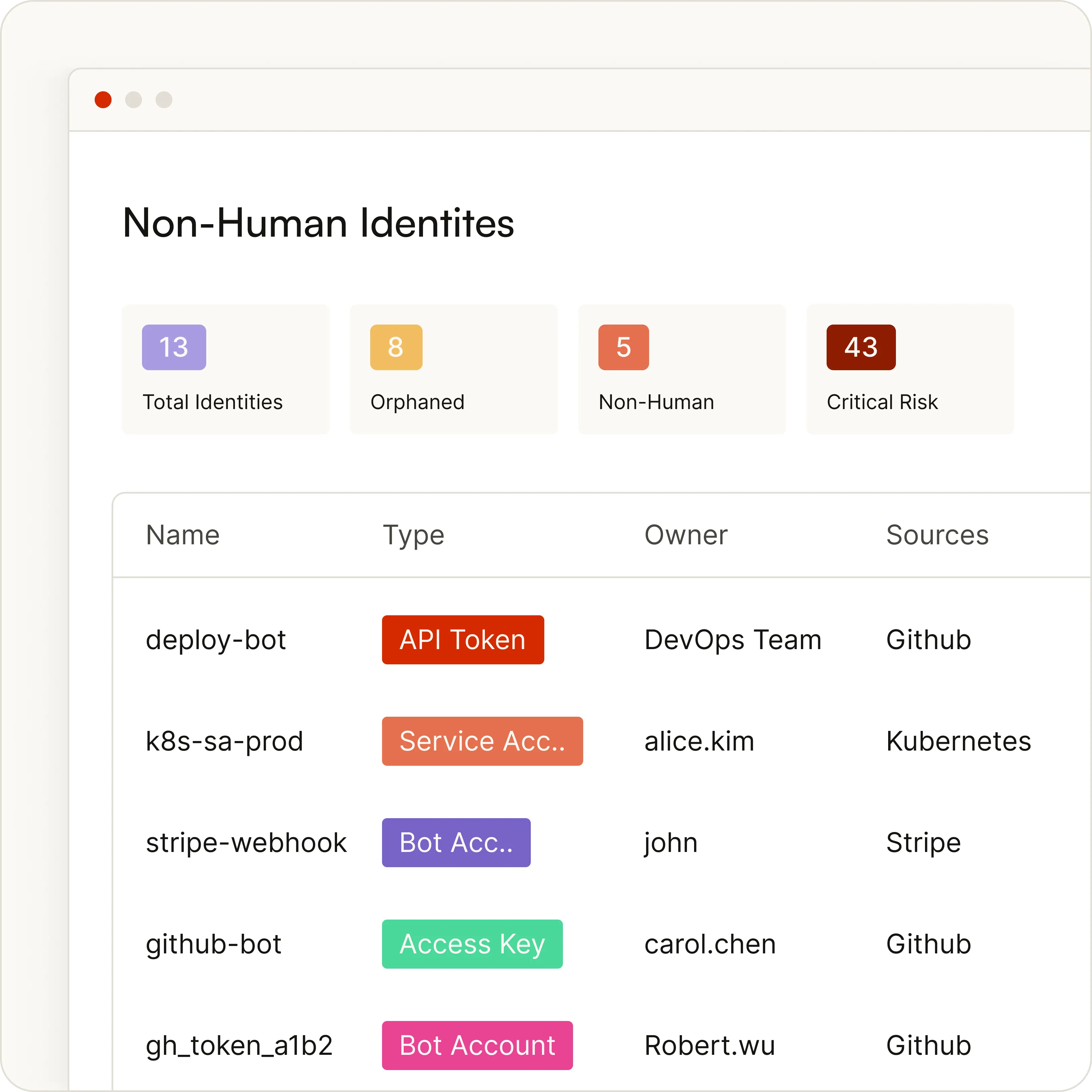
Non-Human Identity Governance
Govern Machine Identities Like Human Ones
Service accounts, tokens, bots, workloads, and AI agents often operate without ownership or control. IVIP brings structure, visibility, and accountability to every non-human identity.
End-to-end lifecycle visibility from creation to decommission
Enforced ownership with alerts on inactivity or permission drift
Risk-based prioritization to surface the most exposed identities first
The IVIP Architecture


Use cases
Every Identity Team. One Platform.
Identity risk impacts every function. IVIP delivers the context each team needs to act decisively.
Security Leaders
Prioritize high-risk identities and reduce breach exposure.
IT and Access Teams
Streamline access reviews with real-time ownership and usage insight.
Cloud and DevSecOps
Surface machine identities and prevent permission sprawl.
Audit and Compliance
Maintain defensible audit trails without last-minute data scrambles.
why zluri
Built for Modern Identity Complexity
Capability

Traditional IGA
Discovery
App Catalog & Intelligence
%201.svg)
Shadow IT and AI
Non-Human Identity Governance
Risk Insights
%201.svg)
Deployment
Proof of Value

“Autify aligns with SOC 2, and we seriously care about security. Undiscovered SaaS applications created a security vulnerability. Zluri’s closed this security gap efficiently and effectively.”
Takumi, Manager, IT & Administration

“We thought we had a couple of 100 applications. After we engaged Zluri, we discovered well over 2500 apps in our ecosystem!”
Terry LaRock, Head of Procurement

“With Zluri, we quickly discovered all the different applications and current usages inside every platform. We noticed several apps were not utilized by multiple users in the last 30 or 60 days.”
Lior Zagury, Director of Global IT









.svg)














