The Challenge
Your SoD controls weren't designed for modern application environments
Most governance teams inherit SoD processes built for on-prem ERPs. When applied to modern SaaS stacks, the gaps become audit findings.
Policies live in spreadsheets
SoD rules are scattered across CSVs, emails, and tribal knowledge. No centralized policy engine means no consistency and no enforcement.
Visibility is periodic, not continuous
Access reviews happen quarterly at best. In between, toxic combinations accumulate undetected, turning into control failures at audit time.
Coverage stops at the ERP boundary
Legacy IGA tools enforce SoD within SAP or Oracle. SaaS applications like Salesforce, Workday, and ServiceNow sit outside the policy perimeter entirely.
Alert fatigue from poor identity resolution
Without accurate identity consolidation across systems, teams waste cycles triaging false positives instead of resolving real risk.
Remediation is unstructured
Violations are flagged but lack a clear resolution path. No assigned owners, no escalation logic, no proof of remediation for auditors.
Application-level conflicts go undetected
Toxic combinations within individual applications, like vendor creation and payment approval in the same ERP - persist because no tool is enforcing per-app SoD rules.
HOW IT WORKS
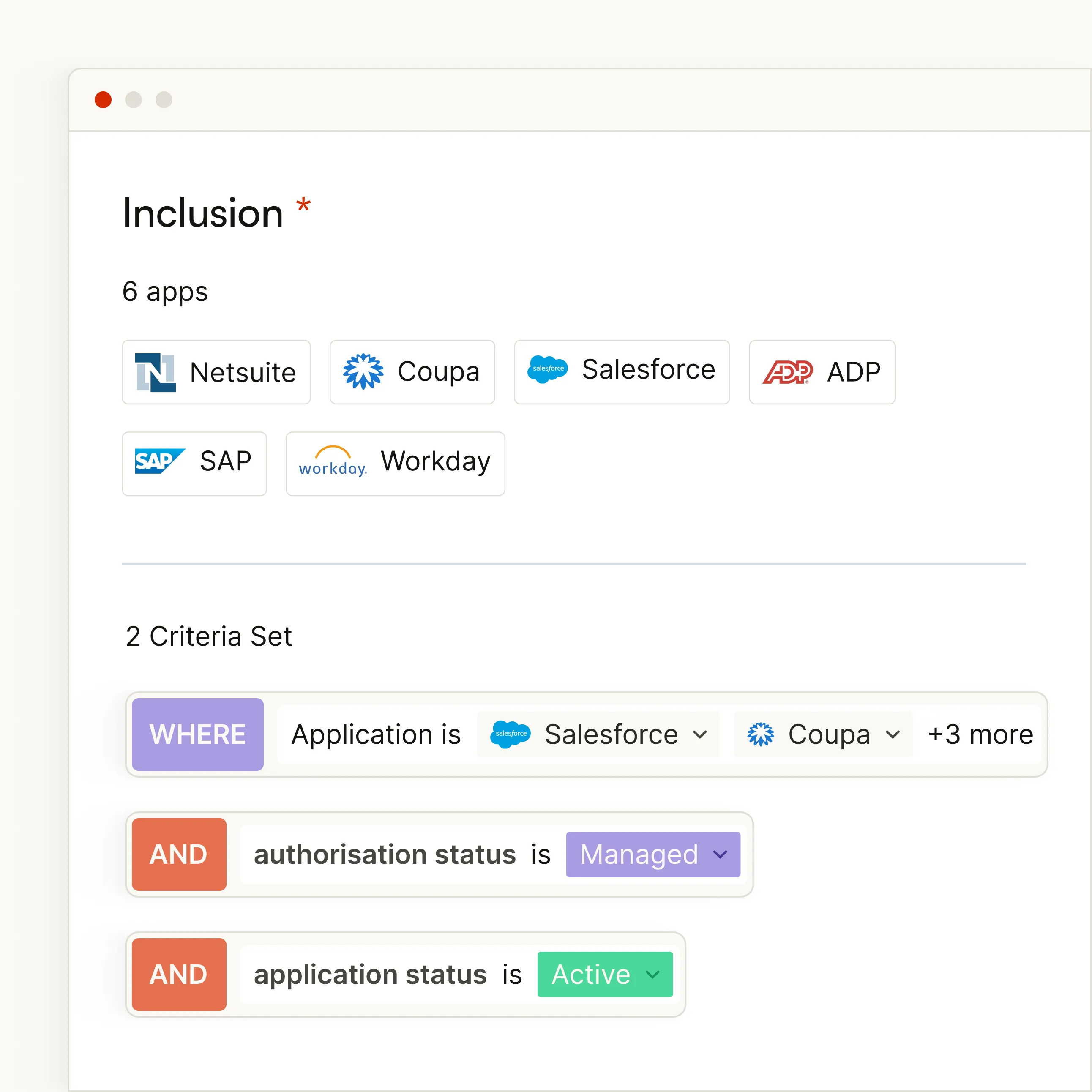
Select the application and target user population for your SoD policy. Zluri ingests entitlements from any connected application, (including custom apps via API) so you can enforce controls wherever access exists.
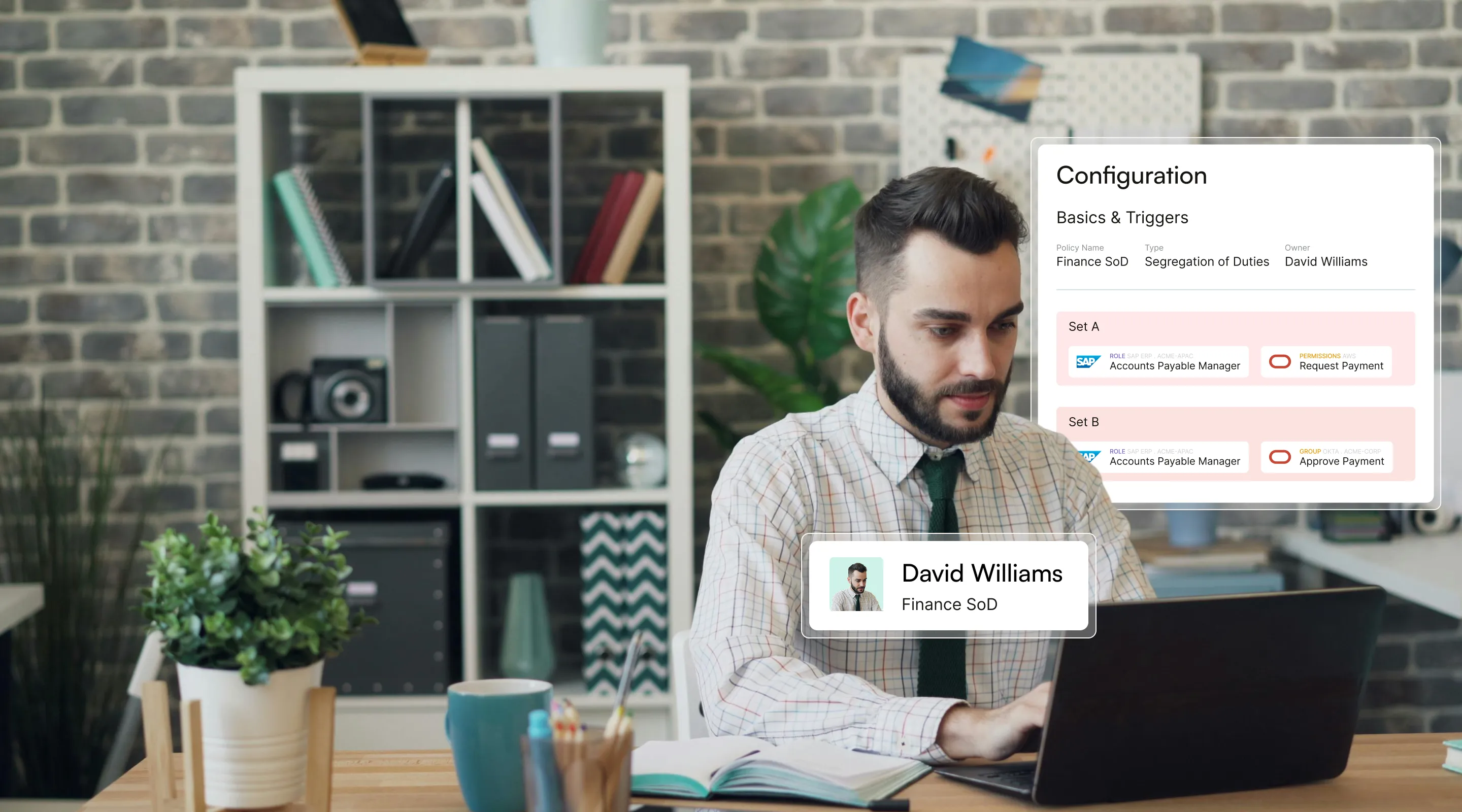
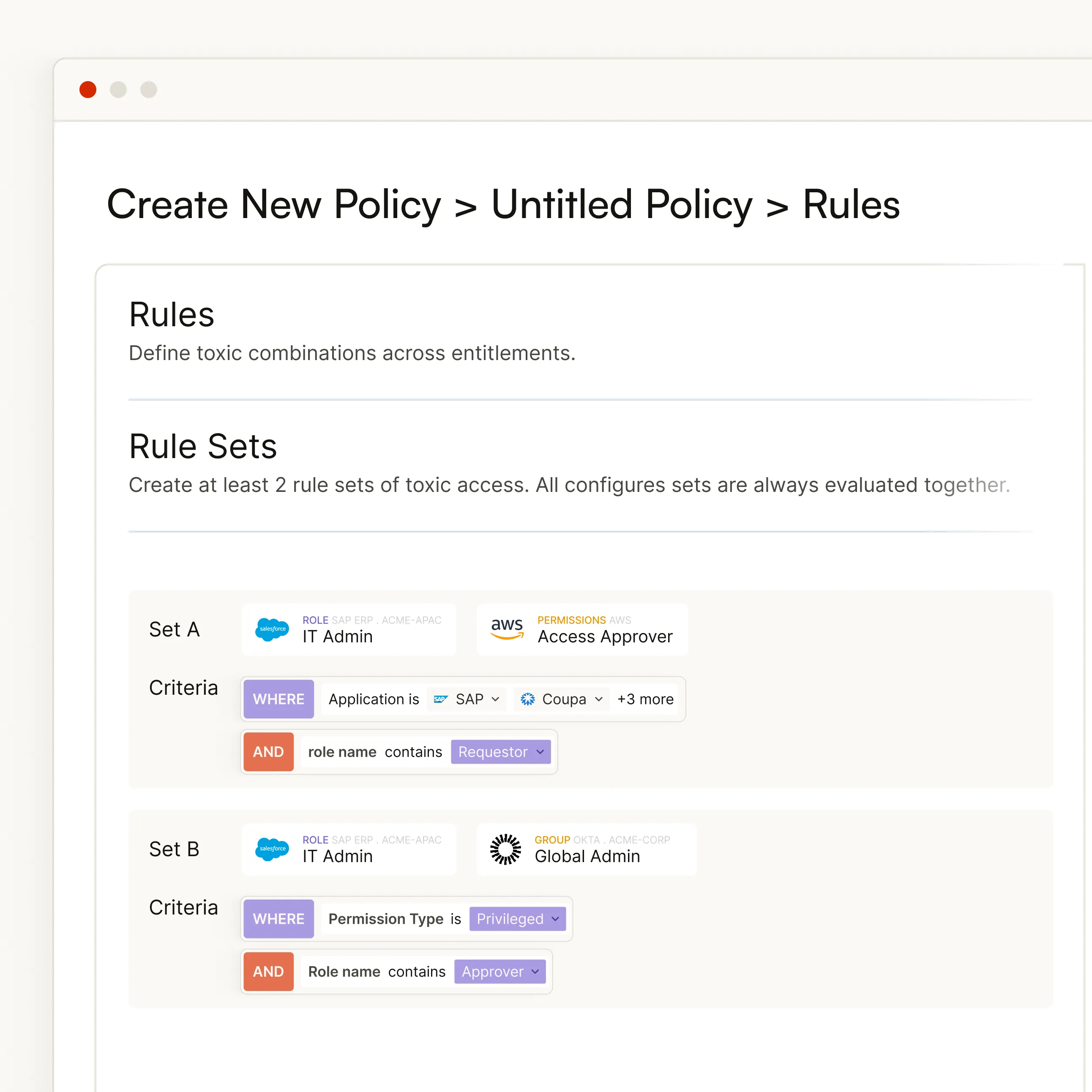
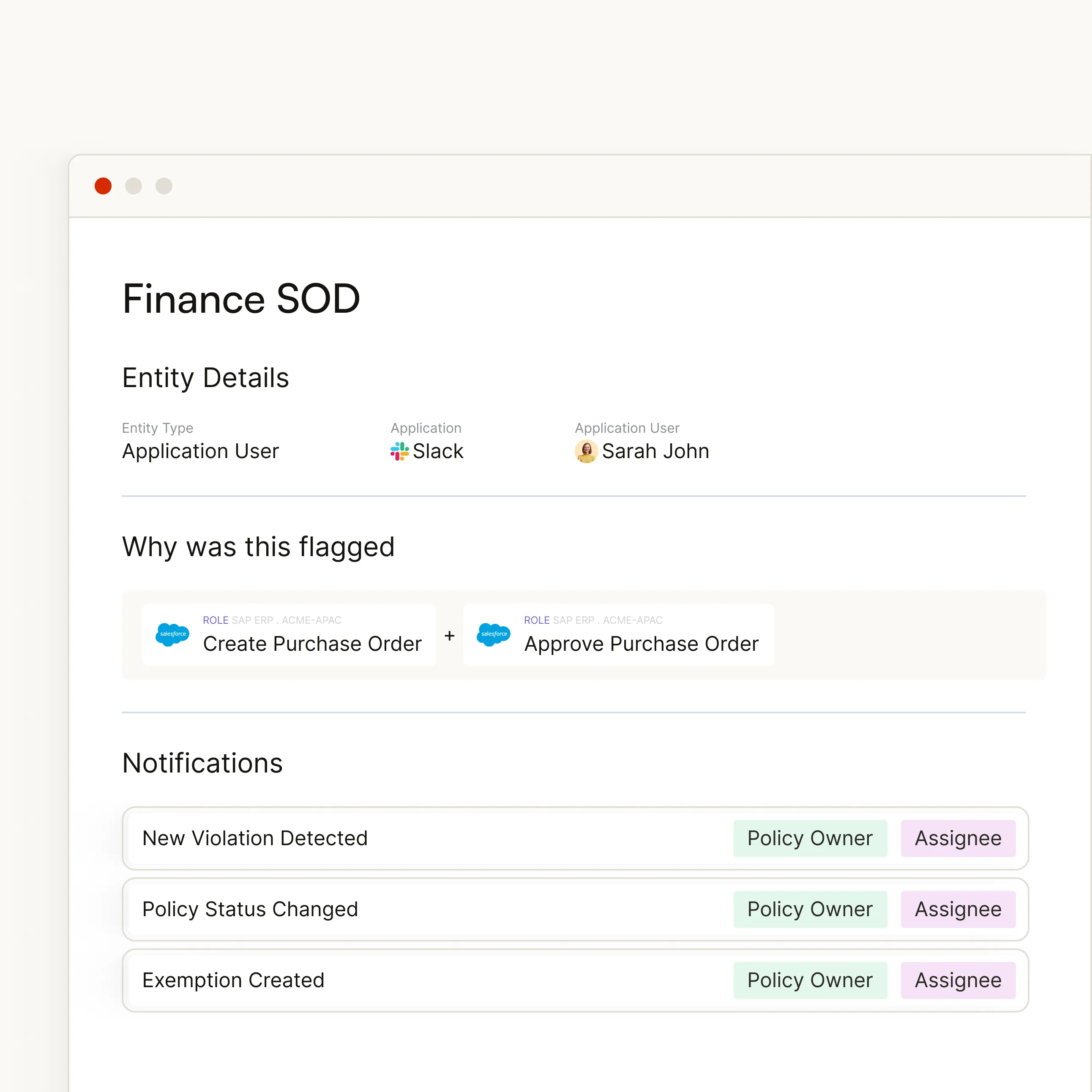
Choose from predefined toxic rule sets at the application level, or define custom rules using Set A / Set B conflict pairs. Each rule maps roles, permissions, or groups that should never coexist on the same user.
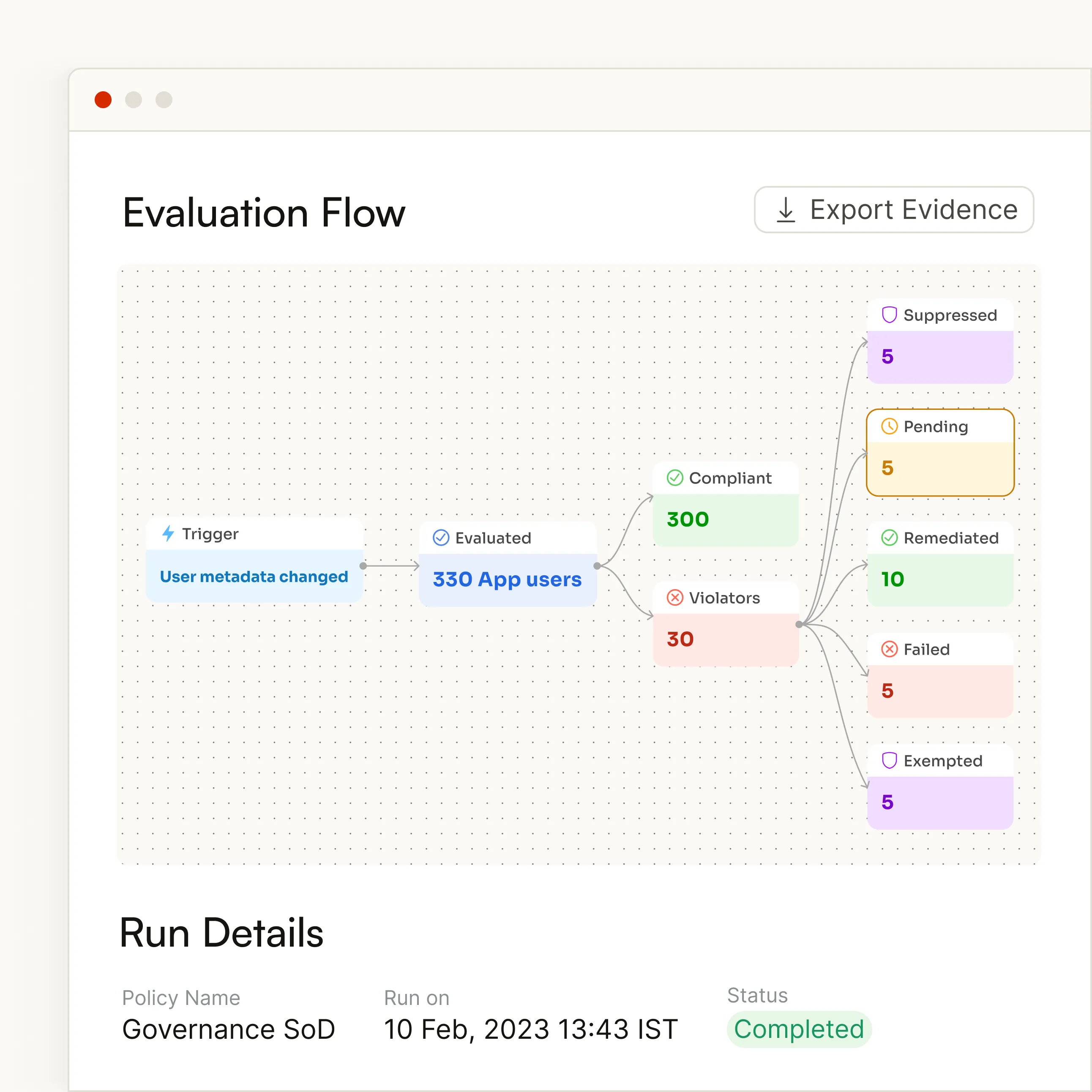
Define how violations are handled when detected: alert the policy owner, route for manual review, or trigger automated access removal. Every action is logged for audit evidence.



HOW IT WORKS
Select the application and target user population for your SoD policy. Zluri ingests entitlements from any connected application, (including custom apps via API) so you can enforce controls wherever access exists.

Choose from predefined toxic rule sets at the application level, or define custom rules using Set A / Set B conflict pairs. Each rule maps roles, permissions, or groups that should never coexist on the same user.

Define how violations are handled when detected: alert the policy owner, route for manual review, or trigger automated access removal. Every action is logged for audit evidence.

capabilities
The complete SoD lifecycle, from policy to proof
Predefined Toxic Rule Sets
Start enforcing SoD policies in minutes, not months
Zluri ships with predefined toxic rule sets at the application level, covering the most common conflict patterns across finance, HR, IT, and cloud applications. Select a rule set, assign it to an application, and start detecting violations immediately.
Pre-built rule sets for common toxic combinations (e.g., vendor creation + payment approval)
Custom rule builder: Define Set A / Set B pairs for any role, permission, or group
Risk level assignment per rule to prioritize remediation by severity
Flexible Application Coverage
Enforce SoD in any application - including custom ones
Zluri ingests entitlements from any connected application via API, including custom and homegrown systems. Define per-application SoD policies wherever toxic access combinations exist, not just in your ERP.
Native integrations for leading SaaS platforms (Salesforce, Workday, ServiceNow, Okta, and more)
API-first architecture: Connect any application, including custom-built systems
Entitlements normalized into roles, permissions, and groups for consistent policy enforcement
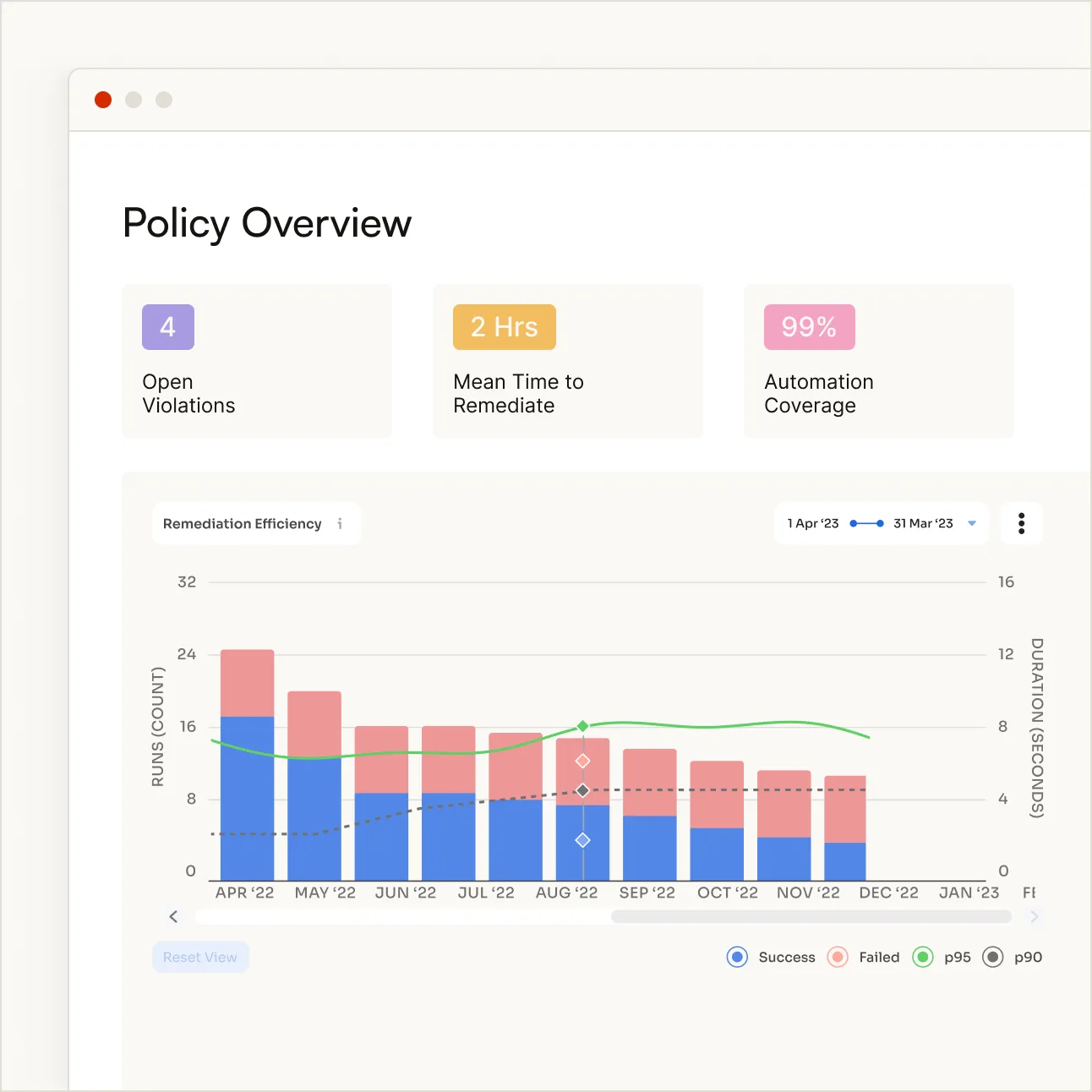
Continuous Monitoring
Catch drift the moment it happens, not months later
Zluri evaluates entitlements continuously, not just at audit time. When a toxic combination is introduced through direct app changes, role migrations, or out-of-band provisioning, the system flags it immediately.
Auto-generate violation records with full entitlement context
Alert policy owners, managers, and security teams in real time
Risk level assignment per rule to prioritize remediation by Assign risk levels to violations based on rule severity and entitlement context
Configurable Remediation
Define how every violation gets resolved
Each detected violation follows a remediation path you configure: Alert the policy owner for manual review, or trigger automated access removal. Every action is logged with full context for audit evidence.
Alert mode: Notify policy owners and managers with full violation context
Automated removal: Revoke conflicting access with zero manual intervention
Full audit trail: Every remediation action logged with actor, timestamp, and state change
Audit-Ready Evidence
Every policy action creates an auditable record
Every policy evaluation, violation, and remediation is a first-class auditable object. Every state change is logged with actor, timestamp, and context, giving your audit and compliance teams the evidence they need for SOX, SOC 2, ISO 27001, and GDPR reviews.
End-to-end violation lifecycle tracking with immutable audit trail
Policy-level logging: Who created the rule, when it was activated, what changed
Remediation evidence: Every action captured with actor and timestamp
Use cases
SoD controls across every risk domain, not just finance
Predefined toxic rule sets for the most common conflict patterns across Finance, HR, IT, Cloud, Privacy, and Identity Governance applications.

Financial Controls
Enforce segregation across procure-to-pay and order-to-cash cycles. Segregate vendor creation from payment approval, PO creation from PO sign-off, and expense submission from expense authorization.

HR & Payroll
Prevent the same user from modifying compensation records and executing payroll within your HRIS. Segregatee employee record management from termination authority to reduce insider risk.

Identity & Access Security
Eliminate privilege escalation paths where an access approver also holds global admin rights. Segregate security administration from audit log management.

Cloud & Infrastructure
Enforce environment-level Segregation of duties. Prevent any single engineer from holding admin privileges in both production and development environments.

Data Privacy & Protection
Ensure users who can access PII cannot also export or bulk-download it within the same system. Essential for GDPR, CCPA, and data protection compliance.

Identity Governance
Segregate the ability to assign roles from the ability to approve them. Detect conflicts between administrative role combinations across identity providers.
why zluri
SoD enforcement built for modern access environments
Legacy IGA platforms enforce SoD within ERP boundaries. Zluri extends policy-driven controls to any application in your environment.
Capability

Legacy IGA / Point Solutions
Application Coverage
Predefined Rule Sets
%201.svg)
Continuous Monitoring
Automated Remediation
%201.svg)
Time to Value
%201.svg)
Identity Resolution
Audit Evidence
Compliance Mapping
Policies mapped to the frameworks your auditors require
Every SoD policy in Zluri maps to the specific control requirements of major compliance frameworks, so your audit trail is structured from day one.

SOX
Section 404 Controls

SOC 2
Trust Services Criteria

ISO 27001
Access Control (A.9)

GDPR
Data Protection

NIST
AC-5 Separation



.svg)














