PDF forms routed by email, manager approvals tracked in inboxes, DBAs getting forwarded requests for systems that aren't connected to Active Directory, and terminations that require going to every DBA because nobody knows which systems the employee actually had access to. If this describes your current access provisioning process, you're not alone — this is exactly how access management works at most mid-market organizations before they formalize it. The periodic access review that catches all the errors is also the only real audit mechanism. And the process frustrates everyone involved: HR, IT, the DBAs, and the managers who get pulled in to approve things they don't fully understand.
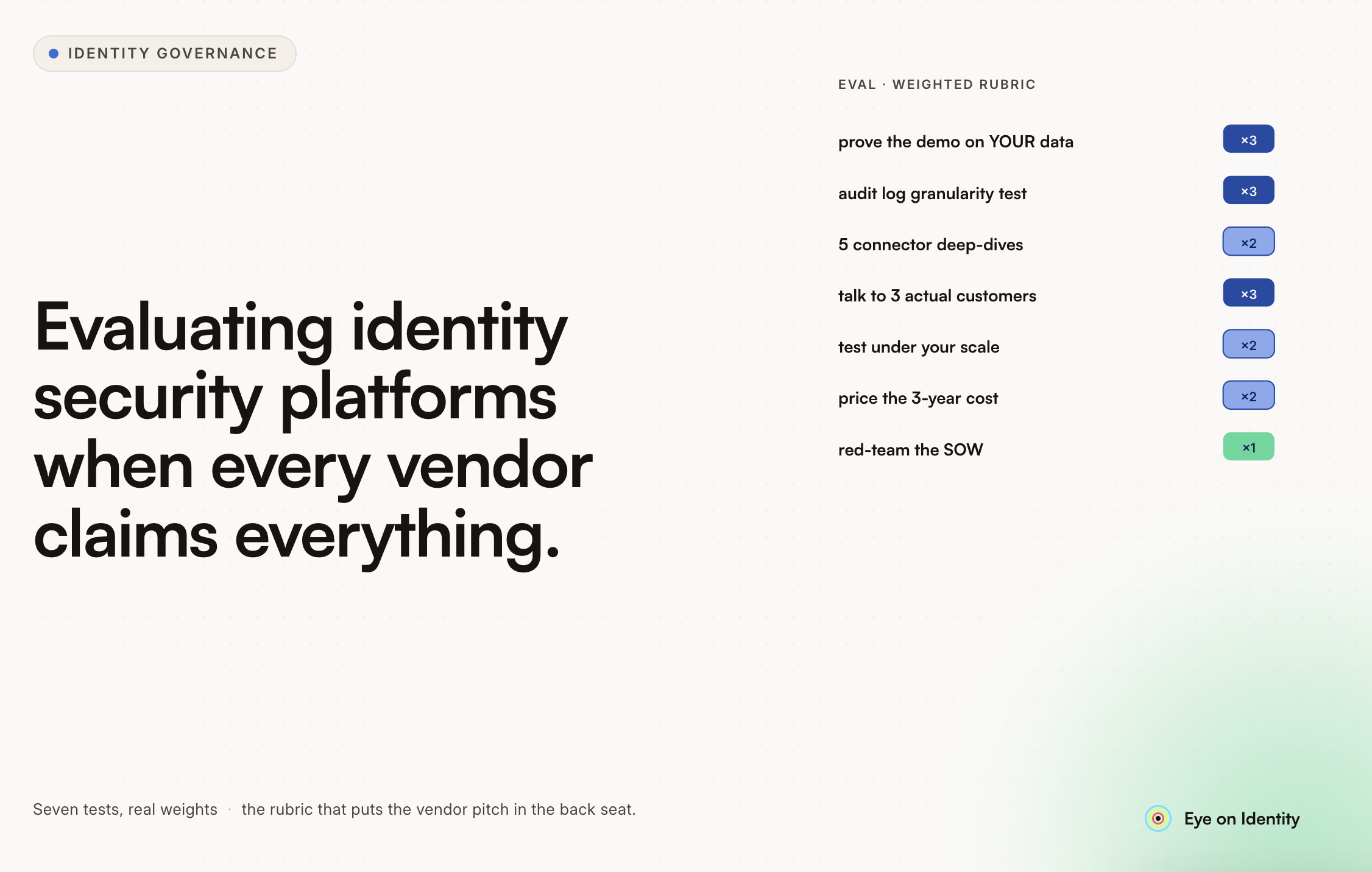
The question the original thread posed — is there off-the-shelf software that handles all of this? — has a clear answer. The category is Identity Governance and Administration. The harder question is what to actually look for.

Why PDF Forms and Manual Routing Break Down at Scale
The current process has an internal logic to it. PDF forms create a paper trail. HR validation confirms the person is an active employee. Manager approval adds an oversight layer. DBA routing ensures each system gets handled by someone who knows it. Periodic access reviews catch what slips through. On paper, the controls are all present.
The failure mode is operational, not conceptual. Each handoff in a manual chain is a place where the process can stall, get skipped under pressure, or produce an incomplete record. A termination that requires notifying every DBA to check and disable access across all systems depends on someone knowing which DBAs to notify and following through on every one. When nobody in the process has a complete view of where an employee has access — because that information is scattered across AD, individual system databases, and historical email trails — the periodic review that catches errors isn't a quality check, it's the primary control. That's a fragile position for an internal audit function.
One commenter in the thread described the right architecture plainly: when it's set up well, there should be no request process. The HRIS is the source of truth. Account creation happens automatically when someone is hired. Role-based access is assigned automatically based on job code and department. The system reaches into non-AD applications via their APIs. The request-and-approval workflow exists for access beyond the standard entitlement set, not for every new hire and every change.
What an Automated Access Provisioning System Actually Needs to Do
Before evaluating any tool, it's worth being specific about the problem components — because the request in the original thread had several distinct requirements that not every IGA platform handles equally well.

Web-based request intake with automated approval routing. The form doesn't disappear — it moves to a web portal where employees request access, and the routing happens automatically based on who owns the application and what the approval policy is. The manager approves via email or Slack without having to log into a separate system. The IT admin or DBA gets notified only after approval is complete. No manual forwarding, no inbox management, no ambiguity about where a request currently sits.
HRIS validation against Active Directory records. The specific ask in the thread — a tool that bounces active employee IDs against AD records on a daily or weekly basis — is a standard IGA function. The HRIS is connected as the authoritative source of employment status, and the provisioning platform syncs against it on a scheduled basis (typically every 24 hours by default, with real-time webhook support for platforms that provide it). Users who are active in the HRIS have active AD accounts. Users who are terminated in the HRIS have disabled accounts. The comparison happens automatically rather than requiring manual reconciliation.
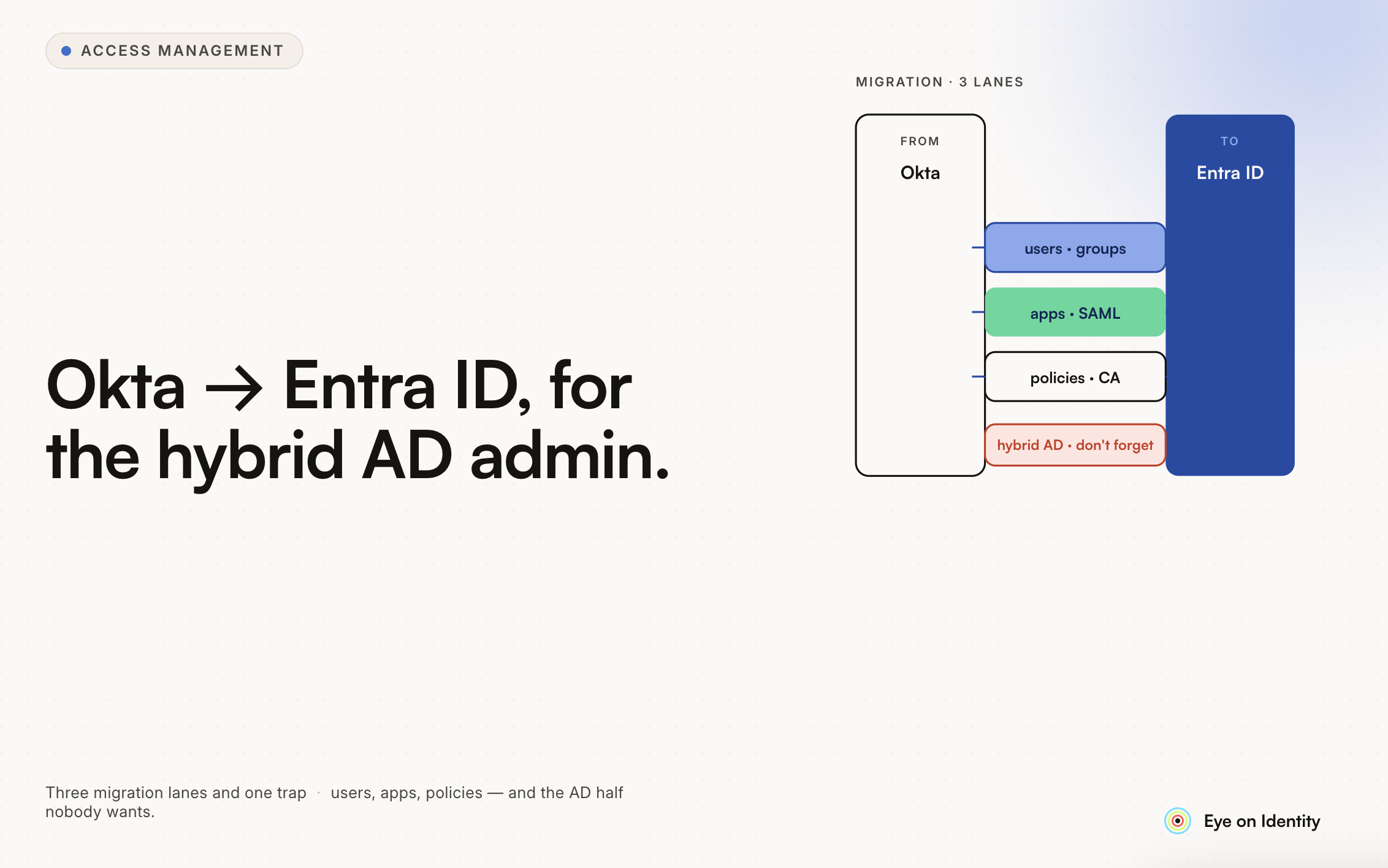
Routing to DBAs for non-AD systems. This is the requirement that most AD-centric solutions handle poorly. Systems that don't have an API and aren't connected to Active Directory need a human to take action — the DBA or system admin who manages that specific platform. Automated routing means the right person gets a tracked task when access is approved, not a forwarded email. The task is marked complete when the action is taken. The audit trail captures the full chain: request, approval, DBA action, completion.
Termination coverage across all systems. The blindspot described in the thread — managers not knowing all the systems an employee has access to — means termination workflows can't rely on the manager to produce the access list. The IGA platform needs to build that list from its own discovery: what applications the user is actually accessing, not just what IT thinks they have access to.
How Modern IGA Platforms Handle Each Part of This Problem
Zluri addresses the specific workflow the thread described, and it's worth walking through each component concretely.

Replacing the PDF form. Employees request access through a web-based app catalog rather than filling out a form. The request is automatically routed to the designated approver — manager, app owner, or both in sequence — based on configurable approval policies. Approvers can act directly from email or Slack without logging into a separate tool. The entire approval chain is logged with timestamps and actor identities, so the audit trail that previously lived in email threads is now structured and queryable.
Bouncing HR records against AD. Zluri connects to the HRIS as the authoritative source of identity and employment status, syncing on a 24-hour cycle by default (with real-time webhook updates for supported HR platforms). An on-premises LDAP agent connects directly to Active Directory, continuously syncing users and groups. When the HR record shows an employee as active, the AD account reflects that. When the HR record shows a termination, the AD account is disabled automatically. The comparison that currently requires a manual periodic process runs continuously in the background.
DBA routing for non-AD systems. For applications without API support or AD integration, Zluri generates automated manual tasks when an access request is approved or a termination is processed. The task is routed directly to the DBA or system admin responsible for that specific application, delivered via email, Slack, or automatically created as an ITSM ticket in Jira or ServiceNow. The DBA marks the task complete within Zluri, which logs the action and closes the loop. Nothing falls through because someone forgot to forward an email.
Solving the termination blindspot. Zluri's discovery engine builds a complete map of every application an employee is actually accessing — not just what's in AD or what IT provisioned intentionally, but applications accessed via browser activity, SSO logs, and financial transaction data (for subscription tools that don't appear in the identity stack). When a termination is triggered in the HRIS, the offboarding workflow is populated with this complete application list automatically. Deprovisioning runs against the full scope of access, not the partial picture any single system would produce.
Periodic access reviews for internal audit. Instead of pulling spreadsheet exports from each DBA and reconciling manually, Zluri's access certification module lets you schedule review campaigns, route them automatically to the appropriate reviewers, and generate the proof-of-review documentation without manual assembly. High-risk access and inactive users get flagged automatically for prioritized review. The output is audit-ready without requiring someone to compile it.
What to Discuss at the Meeting with IT, HR, and the DBAs
The meeting the OP mentioned — IT, HR, and all the DBAs in the room — is the right starting point, and the conversation will go further if the problem components are separated before evaluating solutions.
The first question is where the HRIS data actually lives and how reliable it is. Automated provisioning is only as good as the HR data feeding it. If employment status, manager relationships, department, and role data are inconsistent or incomplete in the HRIS, that's a prerequisite data quality project.
The second question is which applications have APIs and which require DBA action. This determines how much of the provisioning workflow can be fully automated versus handled through tracked manual tasks. Most environments have a mix of both, and a platform that handles both within the same workflow is more valuable than one that only automates the easy cases.
The third question is what the termination process needs to look like. If the current gap is that nobody knows all the systems an employee has access to, the discovery question — how does the platform identify access beyond what IT explicitly provisioned — is the most important evaluation criterion for the offboarding scenario.
Frequently Asked Questions
Is there off-the-shelf software to automate user access provisioning with manager approvals?
Yes — Identity Governance and Administration (IGA) platforms handle this end-to-end: web-based access requests, automated approval routing to managers and app owners, HRIS validation, provisioning for AD-connected systems, and tracked manual task routing for systems without API integration. SailPoint IdentityIQ and Zluri are both purpose-built for this use case.
How do you automatically bounce active employee IDs against Active Directory records?
IGA platforms connect to the HRIS as the authoritative employment record and sync against AD on a scheduled basis (daily by default, real-time with webhook support). Users active in the HRIS have active AD accounts; terminated employees have disabled accounts. The reconciliation runs automatically rather than as a manual periodic process.
How do you handle terminations for systems not connected to Active Directory?
For systems without API or AD integration, IGA platforms generate tracked manual tasks routed to the DBA or system admin responsible for each application. The task is triggered automatically at offboarding, delivered via email, Slack, or ITSM ticket, and marked complete when the DBA takes action. Every step is logged in the audit trail.
How do you make sure all systems are included in offboarding when managers don't know an employee's full access?
A discovery engine that identifies application access beyond what IT explicitly provisioned — using SSO logs, browser activity, and financial transaction data — builds the complete access picture at offboarding. The offboarding workflow is populated from this discovered access list, not from what managers or IT remember.
How do periodic access reviews work in an automated IGA platform?
Access certification campaigns are scheduled within the platform, automatically routed to reviewers, and completed within the tool rather than via spreadsheet exports. The platform flags high-risk access and inactive users for prioritized review and generates audit-ready documentation as output.
See How Zluri Replaces Your Access Request and Offboarding Process
Most organizations at the PDF-form stage discover the scope of the access problem during audits rather than before them. See how Zluri handles access requests, HRIS validation, DBA routing, and termination coverage — and what replacing the current process actually looks like for your specific environment.






.svg)














