As an IT manager, safeguarding your organization's most critical information is paramount. It's crucial to consider data loss prevention tools that empower you to exert precise control over data usage and sharing. These tools fortify your defenses against data loss and breaches. This is where Forcepoint Data Loss Prevention helps you.
Forcepoint DLP is a data loss prevention solution protecting sensitive information against thefts and advanced dangers. It gives you the ability to view all your information and offer insight into your files and applications.
Let's know more about Forcepoint data loss prevention.
Key Features of Forcepoint DLP
Here are a few key features of Forcepoint DLP.

- Forcepoint DLP provides the features of user activity monitoring and insider threat detection and protects sensitive data like credit card data, PII & PHI, company financials, etc.
- Forcepoint DLP helps you to ensure regulatory compliance for GDPR, CCPA, etc., across 80+ countries. It provides security solutions that meet compliance standards while enabling users to view all data anytime.
- One of the key features of Forcepoint DLP is that it protects intellectual property using advanced DLP that assesses how people use data, coaches your people to make good decisions with information, and prioritizes incidents by risk.
Though Forcepoint DLP is a good tool, if you're looking for a budget-friendly solution, it may not be suitable for you.
Drawbacks of Forcepoint DLP
Below mentioned are the drawbacks of Forcepoint DLP.
- You may face challenges with Forcepoint DLP because their support system takes time to resolve problems. When technical issues arise, waiting for support to fix them can lead to downtime and disruptions in the company's data protection efforts.
- The initial configuration process can be challenging and time-consuming. This complexity can delay the deployment of data protection measures, leaving your team dealing with intricacies that may require additional resources and expertise.
- Forcepoint DLP may not integrate seamlessly with third-party applications, posing a potential problem for your team. When integration is lacking, you may need to invest extra time and effort to bridge the gaps, which can hinder overall operational efficiency.
Customer Rating
- G2: 4.3/5
- Capterra: 4.7/5
In this article, we will discuss a wide range of Forcepoint DLP alternatives and competitors. But before discussing the list, let's introduce Zluri here.
Leverage Zluri to Enhance your Data Loss Prevention Efforts
Zluri offers a SaaS management platform that can help you safeguard your valuable data in cloud-based solutions. Here's how it works:
- Centralized Oversight: Zluri offers a central hub where you can keep an eye on all the apps your organization uses in one place. This is like having a complete view of your apps and the data within. You can see who's using them, who has access, and how they are used.
- Data Loss Protection: With this powerful overview, you can quickly spot any risks or vulnerabilities in your data management strategy. It's like having a radar for potential data loss threats.
- Unique Discovery Techniques: Zluri leverages nine discovery methods to help you discover every app in your system, including MDMs, IDPs & SSO, direct integration with apps, finance & expense management systems, CASBs, HRMS, directories, desktop agents (optional), and browser extension (optional).
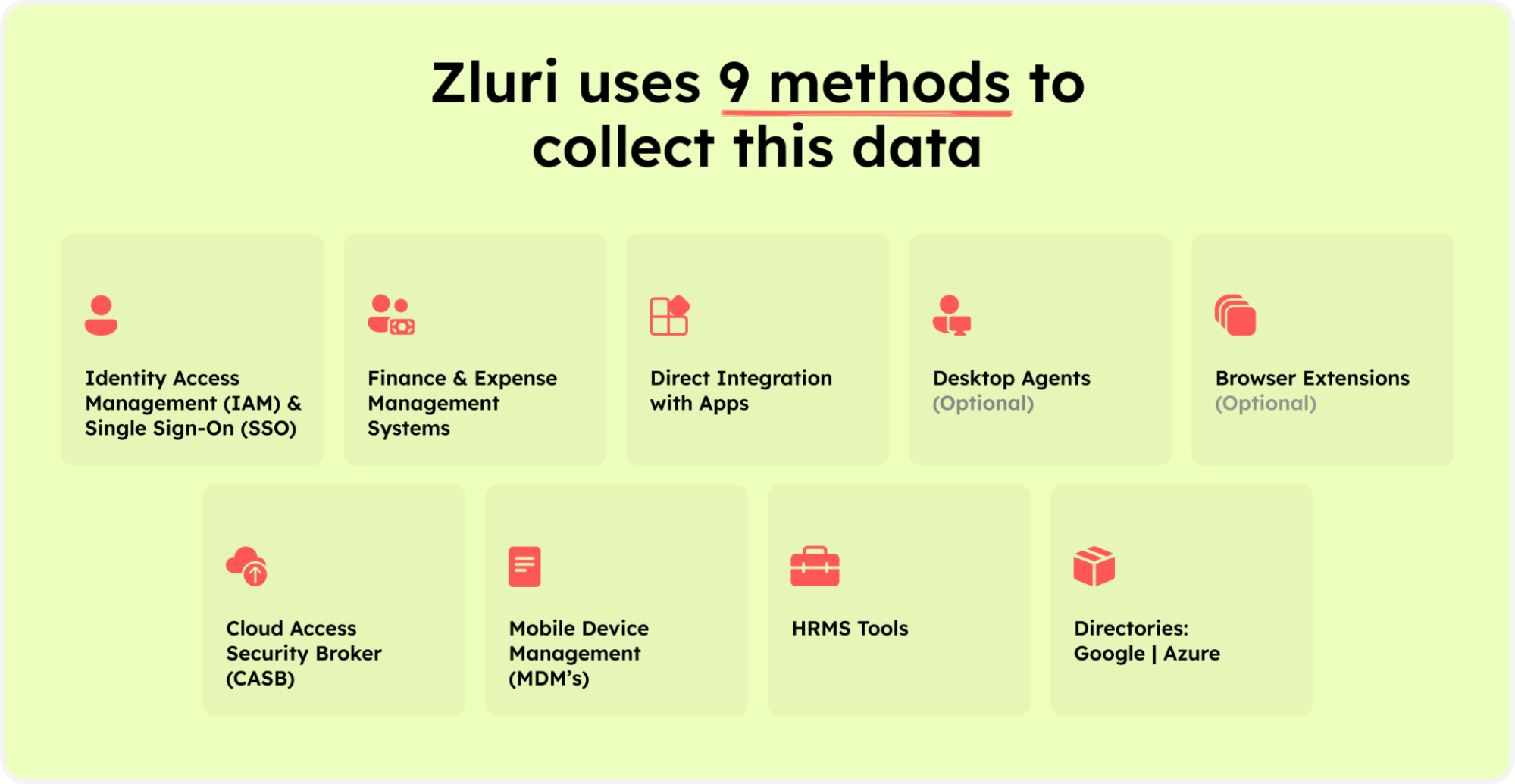
- Zluri’s nine discovery methods
- Automated Safety Net: Even with a 360-degree view, mistakes can happen. For example, when you need to revoke access for employees who are leaving, it's easy to overlook some app access points. Zluri eliminates this risk with automated de-provisioning, ensuring access is swiftly revoked, data is safely transferred, and apps are secured.
- Risk Assessment: Zluri isn't just about seeing your apps; it also helps you understand the security risks associated with each one. You get a comprehensive report on the risk level, pinpointing high-risk apps, data-sharing policies, and access permissions.
- Risk Calculation: Zluri calculates this risk score by analyzing four key factors. It takes into account recent security events, data sensitivity, regulatory compliance, and external security ratings. This info is distilled into a simple 1 to 5 rating, allowing you to make informed decisions to prevent data loss.
Top 10 Forcepoint DLP Alternatives
Now, let’s discuss the Forcepoint DLP alternatives.
1. McAfee DLP Endpoint

McAfee DLP Endpoint, a notified Forcepoint DLP alternative, is a data loss prevention cloud app that protects sensitive data of your organization on the network, in cloud environments, and at the endpoints. It extends on-premises DLP policies to the cloud for consistent data loss detection.
It ensures compliance by addressing day-to-day user actions, such as emailing, cloud-posting, downloading to removable devices, and more. It provides you with real-time feedback that helps you to shape hybrid cloud security awareness and culture.
It provides comprehensive protection for all possible leaking channels, including removable storage devices, the cloud, email, instant messaging, web, printing, clipboard, screen capture, file sharing applications, etc.
Pros
- One of the standout features of McAfee DLP endpoint software is its user-friendliness. This means your team can quickly adapt to and integrate the software into their daily routines without the need for extensive training.
- Another notable advantage of McAfee DLP endpoint is its responsive customer support. When your team encounters issues or have questions about the software, they can rely on McAfee's support team for timely assistance, minimizing downtime and disruptions.
Cons
- One issue with McAfee DLP endpoint software is that it can sometimes generate alerts that aren't entirely accurate. These alerts may signal potential security threats that don't actually exist, causing unnecessary interruptions in the workflow of your IT team.
Customer Rating
- G2: 4.7/5
- Capterra: 4.3/5
2. Check Point DLP

Check Point DLP, a prominent Forcepoint DLP alternative, combines technology and user remediation to prevent data loss, educate users on corporate data policies and enforce it according to the organization's requirements.
It can track and device control the movement of sensitive data in your organization. It helps you to stay compliant with regulations and industry standards. It deploys your predefined policies in monitor mode and enables integrated DLP on any Check Point Firewall.
Pros
- Check Point DLP offers you a powerful tool for efficiently monitoring data storage and sharing within their organization. This means you can keep a close eye on how sensitive information is being handled, ensuring it complies with various regulations and internal policies.
- One of the standout benefits of Check Point DLP is its robust reporting and logging feature. It helps you keep track of who is accessing, sharing, or modifying sensitive data. This enhanced visibility allows you to make informed decisions and take proactive steps to protect your company's data assets.
- Check Point DLP goes the extra mile by offering automated alerts, enabling you to take immediate action to address potential security threats, preventing data breaches and minimizing the impact on the organization.
Cons
- One challenge with Check Point DLP is that it cannot seamlessly integrate with third-party systems. This lack of compatibility can result in additional complexities and inefficiencies in managing your entire infrastructure.
- Check Point DLP primarily concentrates on securing the entire network layer of your organization's data. You might find it limiting when dealing with data security across different layers of your IT environment, such as application-level security or endpoint protection.
Customer Rating
- G2: 4.7/5
3. GTB Technologies

GTB Technologies DLP, a leading Forcepoint DLP competitor, helps your organization secure and protect sensitive data. It helps in real-time monitoring and protection of your data on computers, laptops, servers, cloud repositories, and cloud workloads. It eliminates data breaches automatically on-premises, at the endpoint, and in the cloud.
GTB Technologies DLP helps to ensure the critical information of your organization is not leaked, misplaced, or accessed by any unauthorized users. It also prevents accidental or malicious sharing of data.
Pros
- With GTB Technologies, you can efficiently set up and customize policies to protect their organization's sensitive data without any hassle. Your team can easily navigate the system without the need for extensive training or technical expertise.
- GTB Technologies DLP simplifies data loss prevention policy creation, empowering you to craft robust data protection policies quickly and effectively. With GTB Technologies, you can confidently enforce policies that safeguard sensitive information, all with minimal effort.
- GTB Technologies DLP offers you a seamless process for scanning entire network traffic and data. By providing a clear view of traffic and data, GTB Technologies empowers your team to proactively protect their organization's valuable information assets.
Cons
- One notable drawback of GTB Technologies DLP is its customer support. This lack of responsive and customer support can hinder your IT team's ability to resolve problems quickly and efficiently.
- Another limitation of GTB Technologies DLP is the absence of an option to update agents directly from the console. Without this convenient feature, you may need to manually update each agent, which can be time-consuming and error-prone.
Customer Rating
- G2: 4.4/5
4. Teramind DLP

Teramind DLP , a prominent Forcepoint DLP alternative, is a data loss prevention tool that detects and prevents user actions symptomatic of insider threat protection to your data. It helps you to redefine the process you operate with data-driven behavior analytics.
Teramind DLP monitors users that help to secure an organization’s data even in vulnerable remote environments. It enriches the incident response to user, investigations, and threat intelligence with irrefutable evidence.
Pros
- One of Teramind DLP's notable strengths lies in its ability to monitor and enforce organizational policies seamlessly. You can establish and customize policies to align with their company's specific requirements, ensuring compliance management with industry regulations and internal standards.
Cons
- One significant drawback of Teramind DLP is its relatively high price tag when compared to alternative endpoint data loss prevention solutions. This higher cost can pose challenges for you and your team who may have limited budgets or need to allocate resources judiciously.
- Another issue that your team may encounter with Teramind DLP is subpar customer support. This can hinder productivity, increase downtime, and create additional stress for your IT team who rely on responsive and knowledgeable support when dealing with software-related issues.
Customer Rating
- G2: 4/5
- Capterra: 4.6/5
5. Spirion

Spirion is a data loss prevention tool that helps you gain clarity as to what sensitive data your organization has and where the data is located. It helps you to device control the data stored and used, and protect the data from any loss, making it a suitable Forcepoint DLP alternative.
When any sensitive data is found, Spirion can reduce the risk by shredding it, redacting it, or securing it. It highlights the existence of unsecured files and data owners to reduce accidental transmission and exposure of sensitive information.
Pros
- One key benefit of Spirion is its flexible and robust reporting capabilities. This feature empowers you by providing the data and insights which you need to make informed decisions about data security and strengthen your hybrid cloud security.
Cons
- One significant drawback of Spirion is its ineffective filtering system, potentially leading to false positives or missing crucial information. This limitation can have a direct impact on you and your team, making the data security efforts less efficient and more error-prone.
Customer Rating
- G2: 4.4/5
6. Endpoint Protector

Endpoint Protector, a leading Forcepoint DLP alternative, is a data loss prevention tool for Windows, Linux, and Mac. It is available as SaaS and on-premise deployment. It discovers, monitors, and protects the sensitive data of the organization.
Endpoint Protector prevents external and internal data loss and ensures that there is no loss of any sensitive information of the organization. It ensures security and compliance for employees working from home, making it a suitable Forcepoint DLP alternative.
Pros
- Endpoint Protector offers a seamless and hassle-free installation process, making it a valuable asset for you and your team. With its user-friendly setup, your IT department can save precious time and resources.
- Endpoint Protector is backed by a dedicated customer support team, providing valuable assistance and peace of mind. When you encounter challenges or have questions, your team can rely on Endpoint Protector's responsive and knowledgeable support staff to address any issues promptly.
Cons
- One drawback of Endpoint Protector is that it comes with a steep learning curve. This can pose a challenge for your team, requiring to allocate additional resources for training and onboarding, which can slow down the implementation process.
- Another limitation of Endpoint Protector is that it lacks a feature to tag data directly. Without this capability, organizing and categorizing sensitive information can become more cumbersome. You may find it challenging to efficiently manage and monitor data flow within the organization.
Customer Rating
- G2: 4.4/5
- Capterra: 4.6/5
7. Proofpoint Email DLP

Proofpoint Email DLP, a notified Forcepoint DLP competitor, is available as an on-premise and cloud-based services that helps to detect and block threats, unwanted, malicious, and imposter emails with granular search capabilities and visibility into all the messages.
It protects sensitive data from leaking out of your organization through email. Further, it identifies sensitive information, detects data exfiltration, and transmissions via email, and stops critical data loss.
Pros
- The tool doesn't just stop at blocking threats; it excels at it. Its advanced technology boasts high accuracy, ensuring that malicious emails and data breaches are kept at bay. Your IT team won't have to constantly battle with false alarms or manual intervention.
- It offers comprehensive reporting capabilities that provide insights into email activity and threat trends. This valuable information enables you to make informed decisions, identify potential vulnerabilities, and fine-tune their security policies and strategies.
Cons
- One notable drawback of Proofpoint Email DLP is the potential for poor customer support. When your team encounters problems or needs guidance, a lack of responsive and helpful support can lead to delays in resolving issues, impacting their overall productivity.
- Proofpoint Email DLP, while effective, may have a downside when it comes to email attachment scanning speed. This process can be time-consuming, especially for larger attachments or high volumes of emails, and might require additional resources to manage the workload effectively.
Customer Rating
- G2: 4.6/5
- Capterra: 4.2/5
8. Code42 Incydr

Code42 Incydr is an insider threat aware data protection solution that helps the IT security teams to manage data risks and strengthen your data protection strategy. It helps you to view all your file activity across the organization.
It provides complete visibility across computer, cloud, and email systems to assess the data exposure. It protects sensitive data without slowing down your business, making it a suitable Forcepoint DLP alternative.
Pros
- Code42 Incydr offers a hassle-free setup process that's a real time-saver for you. Its user-friendly interface means your team can get up and running quickly without the need for extensive training. This means less time spent on setup and more time for your IT team to focus on critical tasks.
- With Code42 Incydr, keeping tabs on all your important files is a breeze. You can easily track the movement of files across the organization. This not only enhances security policy but also streamlines compliance management.
- Code42 Incydr stands out with its excellent customer support. You and your team can rely on a responsive support team that's there to assist with any issues or questions. This support minimizes downtime and ensures your IT team can stay productive without unnecessary interruptions.
Cons
- One challenge that you may encounter with Code42 Incydr is that it tends to be more expensive when compared to similar solutions. This can put a strain on your IT budgets, requiring careful consideration of costs and allocation of resources.
Customer Rating
- G2: 4.2/5
9. Safetica DLP

Safetica DLP, a leading Forcepoint DLP competitor, is a powerful tool designed to prevent data breaches and leaks within your organization. It puts you in control access by monitoring, managing, and securing your company's data at every step of its journey.
Safetica DLP actively prevents sensitive data from leaving your entire network. It uses advanced algorithms to detect and block unauthorized data transfers, whether intentional or accidental. This tool also helps you categorize your data, making it easier to identify what's sensitive and what's not. You can then apply customized policies to protect your most valuable assets.
Moreover, Safetica DLP is a guardian against insider threats, making it a suitable Forcepoint DLP competitor. It monitors user activity and flags any suspicious behavior, helping you stop data breaches from within your organization.
Pros
- One of Safetica DLP's key benefits is its constant monitoring of your cloud environment. Whenever it spots any suspicious activity or a potential insider threat detection, it sends real-time alerts, minimizing the risk of data breaches and cyberattacks.
- Safetica DLP classifies your information into different categories, making it a breeze to identify sensitive data. This feature empowers your team to take control access over how this data is accessed or shared.
Cons
- The updating process is a particularly challenging aspect of this software. It tends to move at a frustratingly slow pace, making it time-consuming for your IT team to keep the system up to date.
- Furthermore, troubleshooting with Safetica DLP can be quite demanding. Resolving issues takes a considerable amount of time and effort, which can be a source of frustration for your team.
- Another key concern is the pricing plan of Safetica DLP. The high pricing plan per user can significantly elevate the overall cost for a company. This might limit the adoption of Safetica DLP in organizations where cost-effectiveness is a primary concern.
Customer rating
- G2: 4.6/5
- Capterra: 4.7/5
10. Fortra Digital Guardian

Fortra Digital Guardian provides a comprehensive approach to real-time data protection, covering a wide range of data types, from structured to unstructured, across various platforms and endpoint devices. It ensures that your critical business information remains secure, no matter where it resides, be it on-premises or in the cloud.
Fortra Digital Guardian employs machine learning and behavioral analytics to identify and respond to suspicious activities in real-time. This proactive approach helps mitigate potential breaches before they can cause harm to your organization.
The tool’s DLP features enable you to define and enforce data security policies, ensuring that sensitive information doesn't leave your organization without proper authorization. Whether it's through email, removable media, or cloud services, you're in control, making the tool a notified Forcepoint DLP alternative.
Pros
- Fortra's Digital Guardian is well-known for its ability to keep our sensitive data safe. It works across all your devices, networks, device control, and data storage systems. This means whether your team is at the office or working from home, our data stays secure.
- Digital Guardian gives us a close-up look at how your data is used in your organization. This helps your team spot any weak spots or possible threats and take action.
Cons
- The initial setup and configuration of the tool can be complex and take a lot of time. This means your IT team may need significant technical expertise to get things started.
- If your organization is limited with IT resources might find it particularly challenging. It means that your IT team will need to put in extra effort and time to get the Digital Guardian properly configured.
Customer rating
- G2: 4.3/5
- Capterra: 3.8/5









.svg)



.svg)
.svg)
.svg)
.svg)

.svg)

.svg)

.svg)
















.webp)







.webp)
.webp)





.webp)