We understand how tedious it is to manage an employee's identity lifecycle manually. But, if not manually, can there be a better way? This blog answers your query and explains how you can automate identity lifecycle management & enhance productivity.
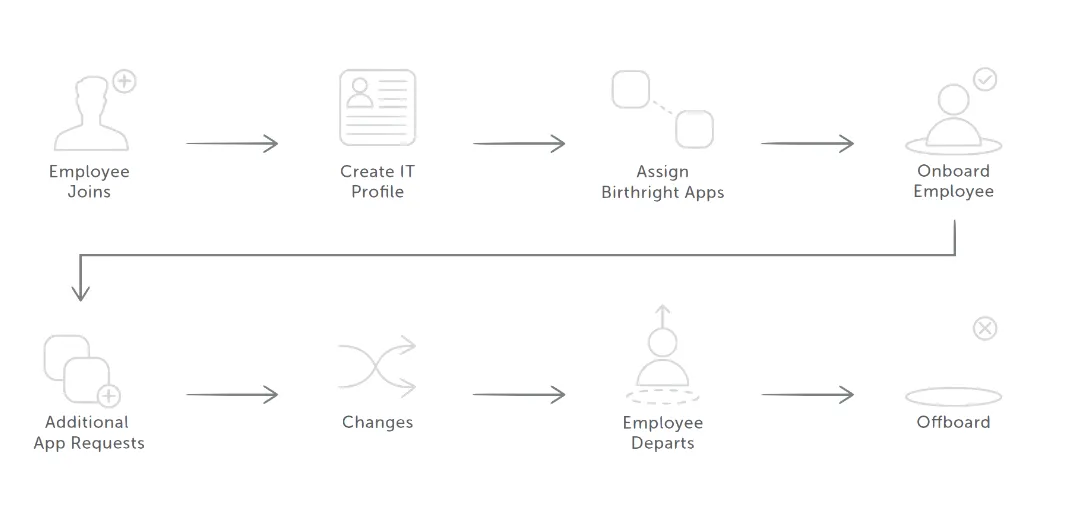
It's evident that digital identities and their associated permissions change with time. For example, after a promotion, the privileges must be elevated, whereas when a new employee joins, you need to provide the required access permissions. On the other hand, the entire process gets reversed when an employee resigns.
These processes are manual and a time sink for your IT operations team. If not done correctly, it can lead to severe security exposures. To ensure high levels of productivity and security, it's crucial to have an efficient way of managing the lifecycle of digital identities. Before diving into the ways, let's understand identity lifecycle management.
What Is Identity Lifecycle Management?
A digital entity is information on an entity's relationship with an organization. For example, it could be a partner, a customer, or an application. The entity's relationships evolve with time, and digital identities must adapt accordingly. This is where identity lifecycle management (ILM) comes in.
Identity lifecycle management refers to managing the user identities and evolving access privileges of employees and contractors throughout their tenure—from day one to separation.
Ever thought about what processes are involved in establishing lifecycle management? If not, here we discuss it in detail.
Process For Establishing Lifecycle Management In An Organization
It cannot be denied that managing digital identities is a complex and tedious task, especially as it relates to correlating real-world objects, such as a person and their relationship with an organization, with digital representation.
Here are the steps for establishing identity lifecycle management in an organization:
- Ensure whether there is a system of record in place or not. For instance, the organization might have Workday as an HR system, which is authoritative for providing the current list of employees and their departments. Besides, some may have an email system such as Exchange Online authoritative for an employee's email address.
- Afterward, connect those systems of record with databases or directories used by applications and fix any inconsistencies found. For example, a directory may have outdated data, such as an account for a former employee that you no longer require.
- Look for processes that can help supply authoritative information without a system of record. For instance, some organizations have digital identities for visitors but need to keep a database for them. Thus, you need to look for a way that helps you determine when you don't require a digital identity for a visitor.
- Ensure the changes from the system of record or other processes are copied to each directory or database that requires an update.
Following the above process will be a manageable task for small-sized organizations. For example, when someone is hired, an IT specialist can create an account for that employee in a directory and provide the access they would need. But is it feasible for mid-size or large organizations? Definitely not.
Is there a better way? Well, yes, automated identity lifecycle management. Automation enables the organization to scale effectively and keeps the identities accurate.
How Zluri Helps Automate Identity Lifecycle Management?
Wouldn't it be great if you could create \"smarter\" processes using an automated playbook that does the work for you? If YES, what makes it possible?
Well, it's Zluri- a SaaS Management Platform that helps automate the entire lifecycle of an employee, i.e., onboarding, mid-lifecycle change, and offboarding. You must be thinking, how does it do that? And why only Zluri?
Here are the features that make Zluri the best automation tool for identity lifecycle management:
a. 360° view of identity & apps in one place
- Gain visibility and control over user-application relationships.
- Track user activity & authorization. Fix false permissions & entitlements.
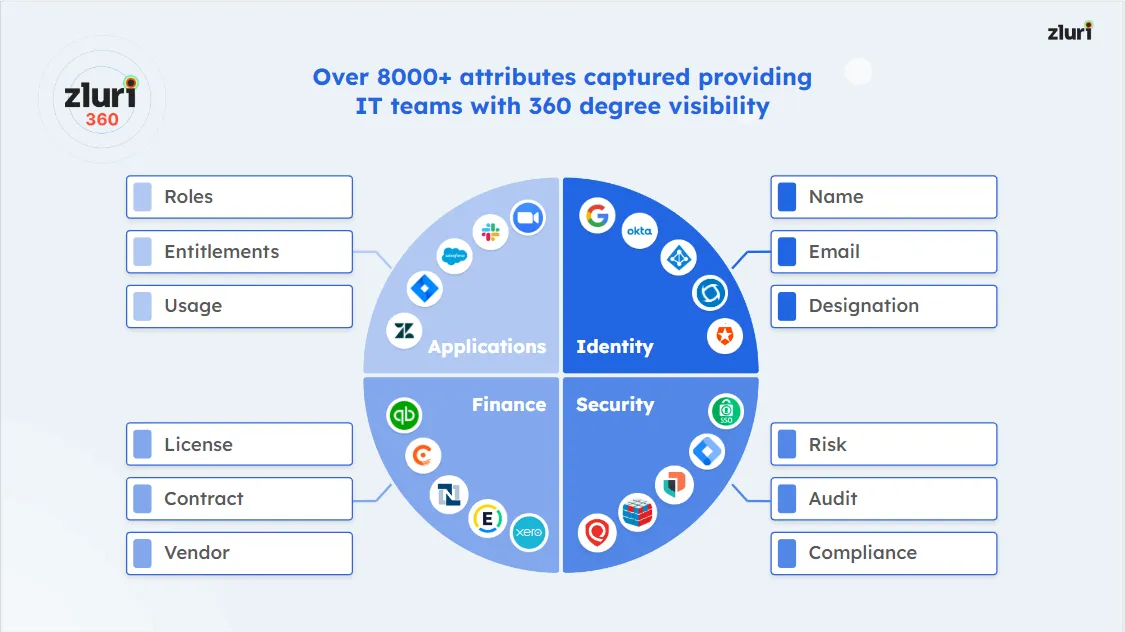
b. Security
- Simplify auditability and bolster security and governance.
- Provision the right app for the right role, with exact permissions, objects, and actions.
c. Automate
- Boost productivity with streamlined, automated provisioning from Day 1.
- Save costs by auto-de-provisioning users when they offboard.
d. Control
- Enable quick and easy access management
- Delivers app-store-like user experience
- Build ticketless, no-code approval workflows
How Zluri automates the employee lifecycle?
1: Onboarding
Initially, the new joiners had to wait weeks to access the tools they needed to do their job, resulting in frustration and productivity. Instead, with automation, organizations can provide them with everything they need on day one.
- Contextual App Recommendations
It provides suggestions based on the joining employee's department and role.
- Intelligent in-app Suggestions
This helps you add employees to channels, groups, or projects they will be working on. Not just that, Zluri goes beyond app-level suggestions.
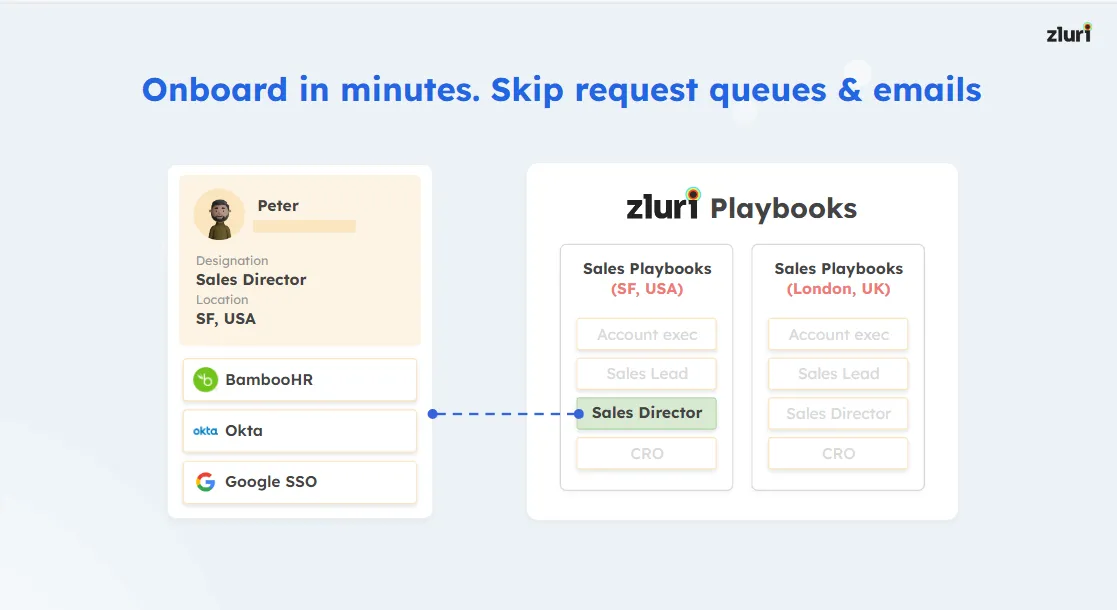
Zluri offers a collection of onboarding workflows that let the company's IT administrators easily and effectively onboard new employees.
With Zluri, you can create a set of activities required to complete a task. Then, you can use these apps again as a playbook (a collection of required app recommendations for automation); whenever needed.
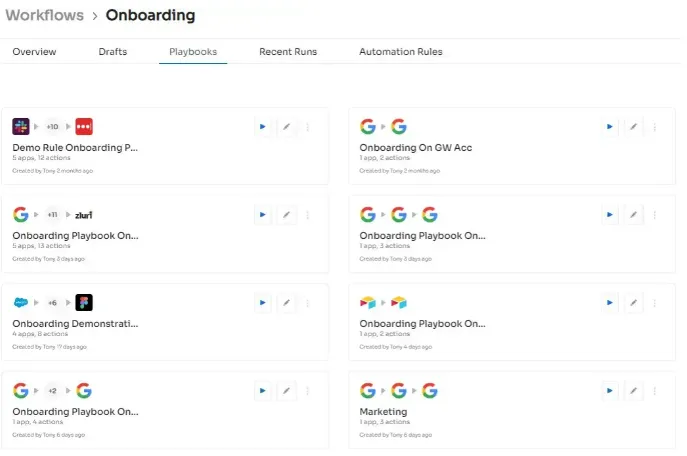
Moreover, you can create a playbook in prior for different roles. For example, a playbook for a content writer would include Slack, ProWritingAid, Trello, and Grammarly. Then, whenever a new employee joins, you can add and send them the onboarding tasks with a single click for them to complete and start using the applications.
2: Mid-lifecycle change of an employee
After spending a few years in an organization, some employees get promoted and, thus, require access to new applications. Can automation make this easier as well? Certainly Yes!
Zluri provides the Employee App Store feature that allows you to automate your SaaS approval process and assign apps & licenses without making your employees wait longer.

Here are the benefits of the Employee App Store:
- Decentralize SaaS procurement decisions:
- Employees get insight into the app alternatives that help them make informed SaaS purchasing decisions that reduce research and evaluation time.
- Keep the employees updated:
- EAS provides real-time updates on their apps or license requests. Additionally, the comments for approval, disapproval, or clarification are visible to the requestors, improving transparency in the approval process.
- Keep SaaS sprawl in check:
- You can prevent it by making it easier for employees to choose apps and giving them quick access to SaaS apps. Moreover, since you have visibility into all SaaS purchases, this eliminates shadow IT.
- Saves time on repetitive tasks:
- With custom SaaS workflows, you no longer have to wait for SaaS approval, requisition, and revocation tickets. With EAS, you can invest your time in other strategic work, which otherwise would have been wasted on repetitive SaaS approval tasks.
3: Offboarding
With an automated offboarding process, you can depart your employees without wasting time on long & tedious offboarding processes. Not just that, you can keep your data secure by deprovisioning them from all the apps they are using.
- Secure Deprovisioning from All Apps
Revoke access from all the apps the employee has access to rather than just SSO or Google Workspace, and secure your data from unauthorized access.
- Streamline Data Retrieval and Reassignment
Before terminating the licenses of an employee, Zluri takes a backup of data in those apps so that you can transfer it to a new owner.
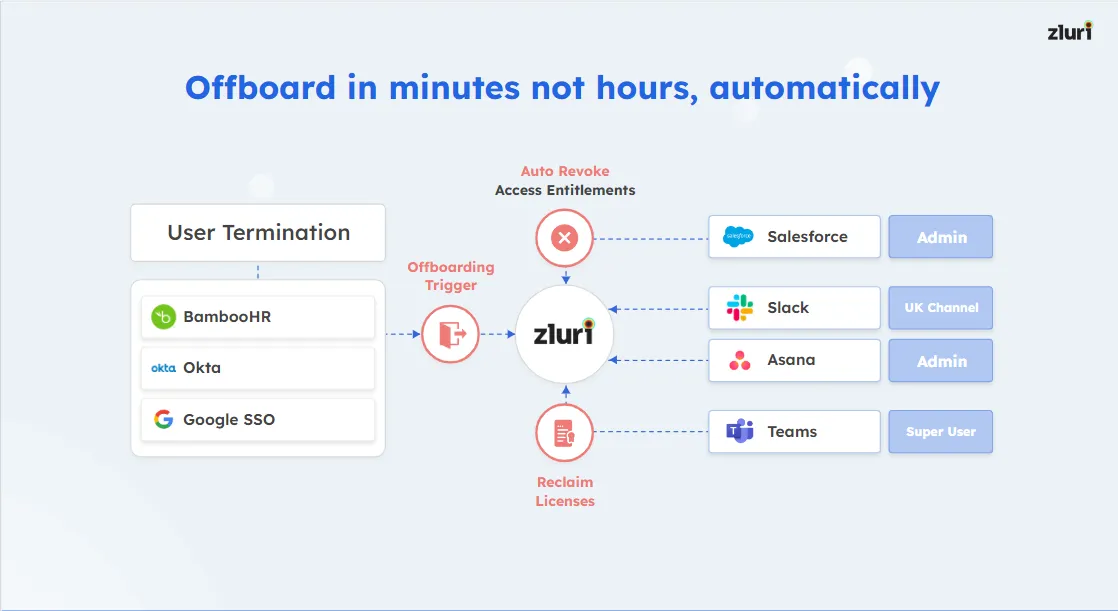
Besides saving time and effort, Zluri's offboarding automation process also helps prevent security breaches. Below are listed the four actions that ensure proper offboarding every time:
a. Access is revoked from all devices.b. Then, the data is backed up and stored.c. Afterward, the user license is revoked to ensure the user cannot use any applications.d. Lastly, the SSO is removed.
Eliminate Manual Effort & Automate Employee Lifecycle Management
You no longer need to wait for weeks to work or get approval for the required apps. Instead, you can manage an employee's identity lifecycle in a few minutes with a single click.
- Is that a new hire who needs to be added to the system?
- Which applications would a new employee require?
- Do you have to update the employee's personal information on the system?
- Has that employee left the company and needs to be disabled across systems?
Zluri makes all the above possible by automating identity lifecycle management. It accurately provisions/deprovisions the right apps to the right users without bulky ticketing and approvals throughout an employee's tenure.
Want to explore more on how Zluri can help you with Identity Lifecycle Management? Book a demo with us today!









.svg)














