Managing an increasing array of devices poses a major challenge for IT managers, requiring meticulous oversight to ensure security and updates. Endpoint management software addresses these complexities by centralizing device management. This article will introduce top endpoint management tools, showcasing their key features.
As the number of devices grows, so does the complexity of ensuring each one is secure, up-to-date, and compliant with organizational policies. This task demands significant time and resources, often leading to inefficiencies and potential security vulnerabilities.
Endpoint management software emerges as a powerful solution to streamline device management processes. By centralizing control and automation, these tools alleviate the administrative burden on IT teams. They offer comprehensive features such as remote monitoring, patch management, and compliance enforcement, empowering you to maintain a secure and efficient endpoint environment.
We will explore the top 10 solutions available in the market, providing insights into their key features, strengths, and considerations for implementation. But before that let’s learn more about endpoint management software.
Endpoint Management Software: An Overview
Endpoint management software is a critical component of modern IT infrastructure, empowering IT teams to efficiently and securely oversee the vast array of devices connected to their networks. These devices, often referred to as \"endpoints,\" include desktop and laptop computers, servers, smartphones, tablets, and IoT (Internet of Things) devices.
Endpoint management software provides a centralized platform for monitoring, securing, configuring, and maintaining these devices, ensuring they operate effectively while adhering to security and compliance standards.
Key Features of Endpoint Management Software
Endpoint management software is a critical component of modern IT infrastructure, enabling organizations to efficiently oversee and secure their endpoints, including mobile devices, computers, and other network-connected devices. Here are the key features to consider when evaluating and selecting endpoint management software:
- Centralized Control: Endpoint management software provides a centralized console or dashboard for administrators to monitor and manage all endpoints from a single location. This streamlines tasks, reduces complexity, and enhances overall efficiency in managing diverse devices.
- Security Management: It includes robust security features such as threat detection, antivirus protection, and patch management. This ensures that all endpoints are safeguarded against malware, vulnerabilities, and cyber threats, enhancing the organization's security posture.
- Policy Enforcement: Endpoint management software allows organizations to create and enforce policies that govern device usage, access controls, and security configurations. This ensures compliance with organizational rules and industry regulations.
- Remote Management: IT admins can remotely access and control endpoints for troubleshooting, maintenance, and security purposes. This feature minimizes downtime, resolves issues quickly, and enhances user support.
- Configuration Management: IT administrators can remotely configure devices, ensuring they comply with company policies and security standards. This includes setting up operating systems, applications, and network settings.
- Data Backup & Recovery: The software may include data backup and recovery capabilities, ensuring that critical data on endpoints is regularly backed up and can be restored during data loss.
- Reporting and Analytics: Endpoint management software offers reporting and analytics tools to provide insights into device performance, compliance, security threats, and usage patterns. This data helps organizations make informed decisions and respond to emerging issues.
- User and Access Management: It offers tools for managing user authentication, authorization, and permissions. This ensures that only authorized users have access to specific resources, enhancing data security and privacy.Selecting an endpoint management software that encompasses these key features is fundamental to maintaining a secure, efficient, and well-managed IT infrastructure while ensuring compliance with organizational policies and regulatory requirements.
Advantages Of Endpoint Management Software
Benefits of Endpoint Management Software:
- Enhanced Security: Endpoint management software bolsters cybersecurity efforts by ensuring that all devices are protected against threats and vulnerabilities, and that security policies are consistently enforced.
- Improved Efficiency: Automation and remote management capabilities reduce manual IT tasks, streamline workflows, and lower operational costs.
- Compliance Assurance: Organizations can maintain compliance with industry regulations and internal policies through policy enforcement and monitoring capabilities.
- Asset Visibility: The software provides a complete view of all endpoints in the network, aiding in asset management and reducing the risk of unauthorized devices connecting to the network.
- Remote Work Support: With the rise of remote and hybrid work models, endpoint management software facilitates the management of devices regardless of their location.
- Scalability: As organizations grow and add more devices to their networks, endpoint management software can scale to accommodate these changes.Now that we've covered the primary benefits, let's delve into essential factors that require your attention before making a choice in endpoint management software:
Factors to Consider When Selecting Endpoint Management Software
Selecting the right endpoint management software is crucial for maintaining a well-functioning and secure IT infrastructure. Here are several factors to consider when choosing endpoint management software:
- Compatibility and Scalability:
- Ensure the software is compatible with your organization's existing hardware, operating systems, and software applications.
- Consider future growth and scalability requirements, as your organization may acquire more devices over time. The software should be able to handle this growth seamlessly.
- Security Features:
- Evaluate the software's security capabilities, including antivirus, firewall, encryption, and intrusion detection/prevention systems.
- Look for features like patch management to keep all devices up to date with the latest security updates.
- Remote Management:
- The ability to remotely configure, monitor, and troubleshoot devices is essential, especially for organizations with remote or distributed teams.
- Ensure that the software offers robust remote management capabilities, such as remote desktop control and remote software deployment.
- Automation and Workflow Integration:
- Automation can significantly streamline endpoint management tasks. Check if the software offers automation capabilities for routine tasks and workflows.
- Integration with other IT management tools and systems (e.g., IT service management, network monitoring) can enhance efficiency.
- Reporting and Analytics:
- Robust reporting and analytics features can help IT administrators gain insights into device performance, security, and compliance.
- Look for customizable reports and dashboards.
- Vendor Reputation and Support:
- Research the reputation of the software vendor. Read reviews, check for customer testimonials, and evaluate the vendor's track record.
- Consider the level of support offered, including customer support, documentation, and training options.
- Cost and Licensing:
- Understand the pricing model of the software, whether it's based on the number of devices, users, or other factors.
- Factor in the total cost of ownership, including licensing fees, maintenance costs, and any additional hardware requirements.
With these factors and conducting thorough research, you can choose a solution that meets your organization's needs for security, efficiency, and scalability while ensuring a smooth and productive IT environment.
In this post, we will discuss various endpoint management software you can use to secure your organization's endpoints.
But first, let me introduce you to Zluri, a SaaS management platform that not only manages your SaaS stack but also secures it:

The increasing adoption of Software solutions and BYOD policies has led to a significant rise in the number and diversity of endpoints connected to corporate networks. Hence, cloud asset discovery and continuous monitoring are imperative for corporate devices.
A suitable solution, such as Zluri, excels in efficiently managing applications across various endpoints within organizations. It achieves this by employing nine effective discovery methods: MDMs, IDPs & SSO, direct integration with apps, finance & expense management systems, CASBs, HRMS, directories, desktop agents (optional), and browser extension (optional).
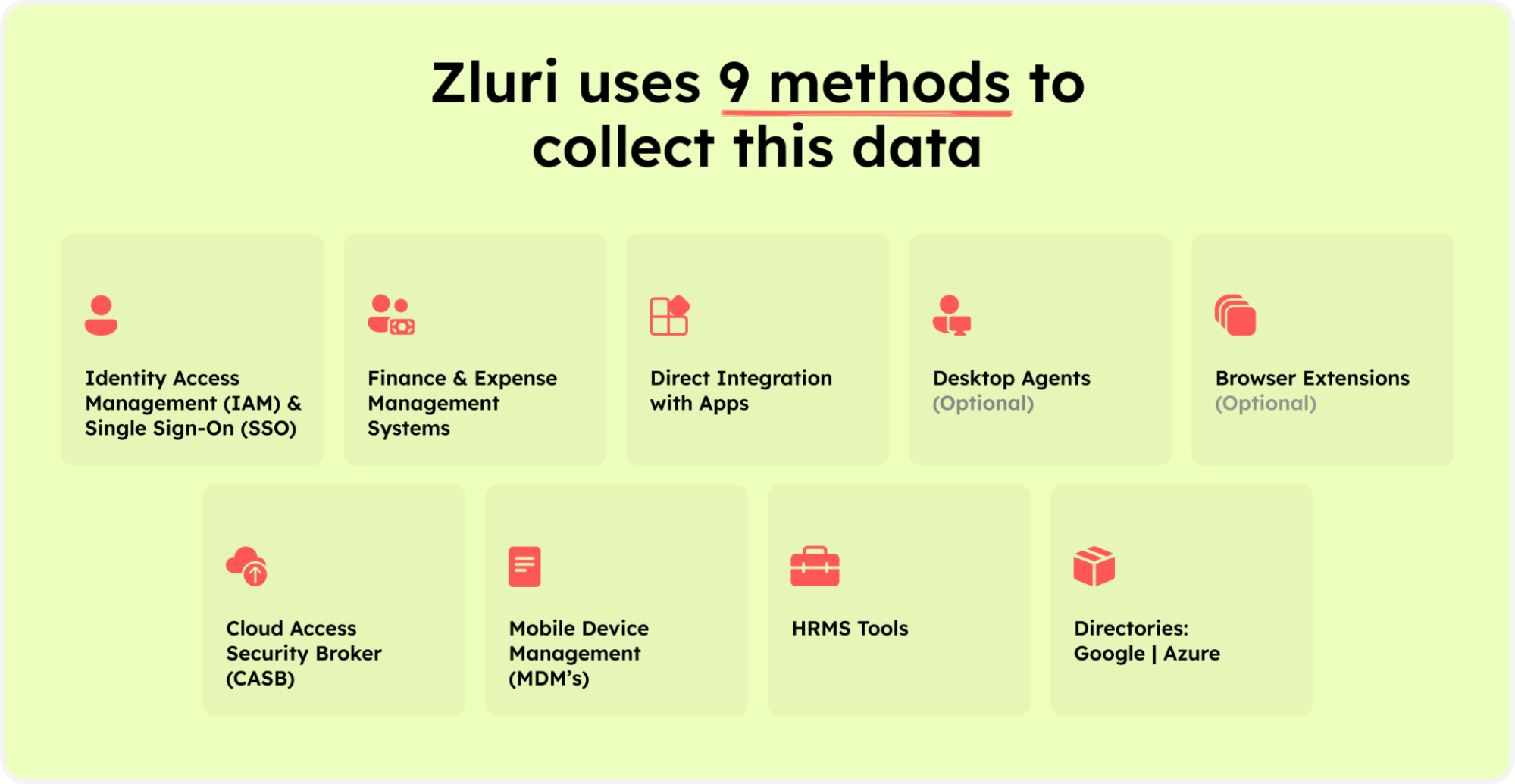
Zluri’s nine discovery methods
Among these methods, desktop agents and browser extensions prove especially valuable for IT teams, enabling the detection of applications on organizational endpoints. For instance, desktop agents collect data on installed apps, device details, sign-in/out activities, and background app processes.

Meanwhile, browser extensions operate locally within the organization, monitoring browser activities across multiple browsers. Furthermore, with its continuous monitoring , Zluri provides visibility into critical apps with high threat levels and risk scores. It issues alerts to prevent the use of apps that pose risks to data confidentiality, bolstering cybersecurity measures.

Don't wait any longer—discover and manage all the SaaS applications across your organization's diverse endpoints. Book a demo with Zluri today!
Now, let's proceed with our list of endpoint management software.
Top 10 Endpoint Management Software
Here is a provided list of top endpoint management software. We've carefully crafted this list based on our expert analysis, drawing insights from leading software review platforms such as Gartner and G2.
1. Hexnode Unified Endpoint Management

Hexnode MDM is a versatile endpoint management software for managing fleets of Android, iOS, and Windows devices effortlessly from one centralized console. With its user-friendly endpoint manager, organizations can seamlessly implement policies like bring-your-own devices (BYOD), ensuring a high level of security and enhancing the user experience.
IT teams can remotely secure, encrypt, lock, and wipe data from a central location, boosting the security posture. In essence, it's an all-in-one platform for safeguarding various endpoints, distributing software, managing assets, and enforcing security policies across networks.
Key Features
- It allows IT admins to automatically lock devices when they remain unused for a specified period. For example, if an employee's computer or mobile device is left unattended or idle for a set duration, the system will initiate an automatic lock to ensure data security and prevent unauthorized access.
- IT teams can manage the endpoint of all devices to ensure employees are working securely. It allows you to exercise control over various aspects of their devices, including configuration, updates, security policies, and user access.
- Support multiple platforms such as Android, Windows, iOS, tvOS (Apple TV). Such compatibility is essential for supporting the diverse technology landscape within modern organizations.
Customer Rating
- G2- 4.6/5
- Capterra- 4.7/5
2. Miradore

Miradore is a cloud-based unified endpoint management (UEM) solution designed to empower organizations to effectively oversee various devices and hardware, including smartphones, laptops, desktops, tablets, printers, and virtual reality (VR) headsets.
IT admins can gain remote control through a single dashboard and implement robust security policies to ensure endpoint security. The software also facilitates deploying Android and iPhone operating system (iOS) software on employees' devices. Additionally, administrators can automate various tasks, reducing the need for manual efforts while enjoying the benefits of this unified endpoint management solution.
Key Features
- It allows you to update settings, automate patch management, and deploy software on Windows devices. This contributes to a smoother operational flow, enhancing overall efficiency and security.
- Provides information on Macs' encryption status, apps, and hardware specifications and automates device enrollment and configuration tasks. It facilitates enhanced data security, simplified administration, and significant time savings for IT teams.
- It empowers employees with secure remote work capabilities, ensuring they can work from any location without compromising data security.
Customer Rating
- G2- 4.8/5
- Capterra- 4.4/5
3. Microsoft Endpoint Manager (MEM)

Microsoft Endpoint Manager (MEM) empowers organizations to let employees work securely anywhere by allowing them access to resources from any device at anytime. Its application-level controls and intent-based policies ensure that users only access the necessary resources. Further, this security solution enables automated remediation of workspace applications.
All the endpoints network devices (on-premise, remote, personal, etc.) are managed centrally via a single console, and admins can remotely deploy devices and software in the devices. Its cloud security across virtual endpoints helps to protect users' remote devices against threats using Microsoft Zero Trust technology with unique capabilities.
MEM ensures device type and application compliance to control data flow outside trusted mobile devices and apps through mobile app management (MAM) and mobile device management (MEM) policies.
Key Features
- Microsoft Endpoint Manager enables unified endpoint security with Zero Trust security controls, so organizations can ensure that their entire network is consistently protected.
- Empower to manage, onboard, and report on encryption, antivirus, firewall, and other security technologies to protect your organization's data.
- Allows to manage all types of endpoints: on-premises and remote, corporate-owned and personal, desktop and mobile. This ensures a diverse and secured bring-your-own-devices (BYOD) ecosystem.
Customer Rating
- G2- 4.6/5
4. Ivanti Unified Endpoint Manager (UEM)

Ivanti Unified Endpoint Manager allows organizations to manage devices like laptops from anywhere. It facilitates IT administrators to automate the provisioning of devices and software deployment. Further, it helps discover devices' software assets and resolve issues quickly, even in remote working environments.
It helps to analyze systems, resolve problems, and reduce desk-side visits by resolving issues remotely. Ivanti Unified Endpoint Manager also integrates information technology (IT) and business data on a single dashboard to make data-driven decisions.
Furthermore, Ivanti UEM allows admins to secure and manage Windows and Mac devices, and with add-on capability, Ivanti Endpoint helps manage the iPhone operating system (iOS) and Android devices, too.
Key Features
- It goes beyond merely identifying devices and software within your organization's network; it also excels in data normalization. This process involves structuring and standardizing the collected data, creating a coherent and consistent dataset.
- Ivanti Endpoint Management's automation capabilities extend to provisioning and software deployment, offering organizations unparalleled flexibility and efficiency.
Customer Rating
- G2- 4.1/5
5. Citrix Endpoint Management

Citrix Endpoint Management is the central hub for managing an enterprise's applications, devices, and data, enabling employees to work securely from anywhere. With Citrix Endpoint Management, organizations can cultivate a workspace environment that's both user-friendly and fortified with robust security measures.
This comprehensive solution centralizes the management of all endpoints, empowering IT teams to fortify remote work environments and enhance employee productivity. It seamlessly integrates with various operating systems and your organization's existing tools, making it highly adaptable.
Irrespective of an employee's device's security state, Citrix Endpoint Management ensures safeguarding the organization's network against potential or security threats. It accomplishes this by securing data through multi-factor authentication (MFA), encryption layers, and a unique micro virtual private network (VPN), ensuring a secure enterprise-level workspace.
Key Features
- IT teams can manage all endpoints and configure devices from a single console cannot be overstated. This centralized approach streamlines IT operations significantly
- It provides alerts for unmanaged devices and has robust reporting capabilities. When an unmanaged device attempts to access the network or sensitive data, the system promptly generates an alert.
- Allows deploying applications remotely through an enterprise app store and applications push and removal. This ensures that employees get access to needed applications wherever they are.
Customer Rating
- G2- 4/
- Capterra- 4/5
6. VMware Workspace ONE

VMware Workspace ONE seamlessly combines remote access control, application management, and multi-platform endpoint management within a unified platform. This versatile endpoint management solution is adaptable for both cloud-based and on-premises deployment options, providing administrators with centralized control over all network-connected devices. From this central hub, administrators can efficiently deploy applications, configure policy settings, manage patches, and provision devices. Furthermore, the system features automated alerting and remediation capabilities, promptly notifying administrators and initiating corrective actions in response to high-risk login attempts.
Key Features
- It integrates easily with various IT tools, such as identity and access management tools (Google Workspace & Azure AD), IT operations, and IT service management tools, ensuring that user credentials and access permissions are synchronized effortlessly.
- It secures the endpoints of different remote devices across the company network, including mobile device management, and hence, contributes to overall data protection, cybersecurity, regulatory compliance, and employee productivity enhancement across the organization.
Customer Rating
- G2- 4.1/5
- Capterra- 4.7/5
7. ManageEngine Endpoint Central

ManageEngine's Desktop Central is a unified endpoint management tool that simplifies the management of servers, smartphones, desktops, laptops, and tablets from a centralized location. It automates tasks such as software deployment, patch management, and OS deployment. Additionally, it offers features like software license management, USB device control, and remote desktop access, and supports Windows, Mac, and Linux operating systems.
The tool also extends to mobile device management, allowing organizations to deploy profiles, configure devices, and manage mobile endpoints effectively. Overall, Desktop Central streamlines endpoint management and enhances security across various device types and operating systems.
Key Features
- Desktop Central secures the network by automating patch deployment for Windows, Mac, Linux, and third-party applications.
- IT teams can deploy software to all the endpoints within the network in just a few clicks, using its over 4500 predefined application templates.
- Regularly assess vulnerability, monitor browsers, control applications, and devices across your network to strengthen endpoint security.
Customer Rating
- G2- 4.2/5
- Capterra- 4.5/5
8. NinjaOne Endpoint Management

NinjaOne is a robust unified endpoint management tool designed to streamline IT operations and simplify teamwork. This innovative solution empowers IT departments and MSPs with unified management, remediation, and automation capabilities, all within a modern and user-friendly platform. By using NinjaOne, organizations can boost user satisfaction and significantly enhance the efficiency of their engineers.
One of its standout features is complete patching automation for various operating systems, including Mac, Linux, Windows, and robust third-party Windows applications. This cloud-based patching capability eliminates the need for complex frameworks, making patch management tasks more straightforward for IT teams. Whether it's patching an endpoint with an internet connection or handling tasks across diverse locations, domains, and networks, NinjaOne excels at automating all aspects of patch management.
Moreover, this endpoint security software is pivotal in bolstering security and ensuring compliance, alleviating the overall burden on IT teams. With its endpoint security solution and authentication to cloud platforms, NinjaOne is at the forefront of efficient and secure unified endpoint management.
Key features
- The tool provides a streamlined setup and configuration experience, making user onboarding more straightforward.
- Moreover, integrating it with various service providers, antivirus software, and security monitoring systems is a straightforward task, reducing capital expenditure and ensuring efficient operations.
Customer Rating
- G2: 4.8/5
- Capterra: 4.8/5
9. Atera

Atera is a powerful unified endpoint management tool, offering remote monitoring and management capabilities for MSPs and IT teams. With this software, users gain a comprehensive view of multiple networks in real-time, allowing them to monitor and control various aspects effortlessly. It equips IT professionals to promptly address and resolve IT issues for customers worldwide, enhancing their support capabilities significantly.
One of Atera's standout features is its ability to deliver real-time alerts, preemptively notifying users of potential problems. This proactive approach ensures that users can prepare and take action before issues escalate.
Moreover, Atera extends its utility to businesses by providing real-time insights into vital aspects such as system resources, networking, IP monitoring, logged-in customers, SQL server, active directory, and more. This single-pane view simplifies network discovery and monitoring, making it a valuable asset for organizations.
Furthermore, the software offers robust IT automation services, streamlining administrative and maintenance tasks across workstations and servers. For instance, Atera's automated Patch Management system offers detailed reports on patching status, enabling users to install missing patches directly from these reports. This unified approach to endpoint management and network discovery positions Atera as an indispensable tool for IT professionals and MSPs alike.
Key Features
- Its robust search engine also simplifies navigation and makes the graphical user interface (GUI) exceptionally user-friendly. This enhances usability and security, protecting against unauthorized access and external threats.
- With its interactive and user-friendly interface, it ensures effortless navigation without any hassle, providing a seamless user experience.
Customer Rating
- G2: 4.8/5
- Capterra: 4.6/5
10. IBM Security

IBM Security Verify is a comprehensive solution designed to meet the diverse needs of users and empower IT teams to secure digital resources within a hybrid multi-cloud environment. It encompasses a suite of services, including single sign-on (SSO), multi-factor authentication (MFA), and identity analysis.
In addition to these services, IBM Security extends its expertise to comprehensive endpoint security management. This includes consulting and managing solutions for various endpoint protection technologies, providing a holistic approach to security.
IBM Security Verify leverages AI-driven capabilities to establish a risk-based identification framework and dynamic access policies. Key components of this solution encompass identity administration, access recertification initiatives, and identity insights, all efficiently managed through a unified interface. This simplifies the management of various security aspects, from single sign-on to software distribution and asset management.
Furthermore, IBM Security Verify excels in alert management, offering IT teams a robust platform for proactively addressing potential threats and vulnerabilities. It enhances the organization's security infrastructure and offers optional features like two-factor authentication for added security.
Key Features
- It allows you to customize and adjust risk settings according to your precise requirements through a user-friendly web-based interface.
- Moreover, any suspicious attempts to access your tools are promptly revoked, ensuring the security of your assets across the entire lifecycle.
Customer ratings
- G2: 4.3/5
- Capterra: 4.3/5
Frequently Asked Questions (FAQs)
1. What features should I prioritize when selecting endpoint management software?
Look for comprehensive security features, centralized management capabilities, scalability, compatibility with diverse devices and operating systems, automation capabilities, and a user-friendly interface to streamline operations.
2. How important is integration and compatibility with existing IT infrastructure when choosing endpoint management software?
Integration and compatibility are crucial to ensure seamless operations and avoid disruptions. Choose software that can seamlessly integrate with your existing tools, platforms, and workflows for enhanced efficiency.
3. What role does scalability play in selecting endpoint management software?
Scalability is key to supporting your organization's growth and evolving needs. Ensure that the software can scale with your business, supporting increasing endpoints and users without compromising performance or security.
4. How does unified endpoint management (UEM) differ from traditional endpoint management?
Unified endpoint management (UEM) combines multiple aspects of endpoint management into a single, centralized platform, allowing for streamlined control and security across a variety of devices and operating systems. It integrates mobile device management (MDM), mobile application management (MAM), and other features into a unified solution.
5. Can a UEM solution effectively manage both mobile and non-mobile endpoints?
Yes, a UEM solution is designed to manage a wide range of endpoints, including mobile devices, laptops, desktops, servers, and more. It offers a comprehensive approach to managing all endpoints within an organization from a central dashboard.
6. How does Mobile Device Management (MDM) differ from Unified Endpoint Management (UEM)?
MDM primarily focuses on managing mobile devices, whereas UEM extends its capabilities to manage a broader spectrum of endpoints, including laptops, desktops, and IoT devices, providing a more holistic approach to endpoint management.
MDM typically includes features like device provisioning, policy enforcement, application management, remote wipe, and device tracking, specifically tailored for mobile devices such as smartphones and tablets.
In case of deployment, UEM generally offers a more streamlined and less complex deployment compared to separate MDM solutions. As UEM encompasses a broader array of endpoint types, it simplifies management by consolidating different management aspects into a unified platform.









.svg)



.svg)
.svg)
.svg)
.svg)

.svg)

.svg)

.svg)
















.webp)







.webp)
.webp)





.webp)