Exploring user lifecycle management software is a great way to streamline processes within an organization. These tools are pivotal in ensuring that the entire lifecycle of users—from their onboarding to offboarding—is managed efficiently and accurately.
Let's dive into some of the top user lifecycle management software that helps organizations automate and optimize these crucial processes.
User lifecycle management (ULM) is the comprehensive oversight and administration of an individual user's journey within an organization. It encompasses the complete span of a user's association with the company, starting from their onboarding through their active tenure and finally concluding with their offboarding or departure. It's basically the end-to-end management of an individual's life cycle within the company's ecosystem.
Furthermore, the software that is used to manage the entire lifecycle of an individual within the organization is referred to as user lifecycle management software. This advanced tool helps your IT team manage various tasks, including provisioning access, managing user permissions, monitoring activity, facilitating roles or responsibilities changes, and ensuring a secure and efficient departure from the organization.
This was just an overview of user lifecycle management, so before we explore different tools, let's first have a deeper and more clear understanding of user lifecycle management.
What is User Lifecycle Management (ULM)?
User lifecycle management orchestrates the entirety of a user's journey within an organization, spanning from onboarding to departure. Its focal point is the strategic and tactical administration of user identities, ensuring seamless access to resources and services throughout their tenure. ULM involves efficient onboarding processes, assigning access permissions aligned with roles, and promptly revoking access upon departure.
This meticulous approach aims to streamline user management, bolster security, and uphold efficient access control across the organizational ecosystem. Notably, ULM operates on the principle of consolidating each user's identity within the infrastructure, granting comprehensive access based on predefined settings. This strategy simplifies access management and enhances security measures.
Furthermore, user lifecycle management encompasses a set of five processes, which are:
- Onboarding: Integrating a new user into the organization's systems and workflows. This involves setting up accounts, granting appropriate access permissions, and providing necessary resources to ensure they can start working efficiently.
- Provisioning: Managing user access to applications, databases, networks, and other IT resources based on their roles and responsibilities. This includes granting, modifying, or revoking access as needed during the user's tenure.
- Usage Monitoring: Continuous monitoring of user activities, access logs, and behavior to detect any anomalies or security risks. This step ensures compliance with organizational policies and identifies potential security threats.
- Modification and Updates: Adjusting user access levels or permissions in response to changes in roles, responsibilities, or organizational needs. Regular updates also include ensuring software and security patches are applied to maintain system integrity.
- Offboarding: The process of securely deactivating user accounts and revoking access to all organizational systems, applications, and data when a user leaves the company. This step is crucial for preventing unauthorized access and safeguarding sensitive information.These processes aim to streamline the user's journey within the organization, ensuring efficient access management while upholding security standards and compliance requirements.
Why Do You Need A User Lifecycle Management Software?
Active directory users and computers serve as the main tools for user account creation and management. Nevertheless, these tools come with constraints, including challenges in bulk onboarding, accurate user data handling, log maintenance, and timely offboarding.
IT admins turn to automated user lifecycle management software to ensure efficient operations and reliable security. This advanced solution facilitates smooth onboarding, user management, communication control, thorough analysis, and streamlined offboarding, providing a comprehensive solution for efficient and secure user lifecycle management.
That’s not all; there are some other benefits as well.
Key Benefits Of Implementing A User Lifecycle Management Software
Here are some key advantages of implementing a user lifecycle management software:
- Automates the onboarding and offboarding process: User lifecycle management tools seamlessly automate user onboarding and offboarding processes, saving time, minimizing errors, and reducing the reliance on manual intervention. Furthermore, these tools precisely control access and permissions, aligning user privileges with roles and responsibilities.
- Provides accurate user data that helps manage their access throughout their tenure: User lifecycle management tools help maintain accurate and up-to-date user data, reducing the risk of errors and mismanagement of access during different stages of their lifecycle and ensuring that data is consistent across the organization.
- Offers centralized management platform: With the help of these tools, your IT admins can seamlessly manage users’ onboarding and offboarding processes from a centralized interface. Furthermore, this also makes it easier for IT admins to monitor and control user access across various systems and applications.
- Provides reporting and analytics capabilities: User lifecycle management software often come with reporting and analytics features, allowing organizations to gain insights into user activities, track user roles, positions, or department changes, and identify potential security risks.
- Helps in cost savings: Automation and efficiency improvements brought about by user lifecycle management software can result in cost savings in terms of time and resources required for user management tasks.
- Improves user experience: Streamlined onboarding processes contribute to a positive user experience, allowing new users to quickly access the tools and resources they need to be productive.
Now that you understand the importance of user lifecycle management software, let’s proceed further and explore different types of user lifecycle management software.
Top 8 User Lifecycle Management Software
Given below are some of the well-recognized user lifecycle management software that you can consider implementing to streamline the user lifecycle management process.
1. Zluri
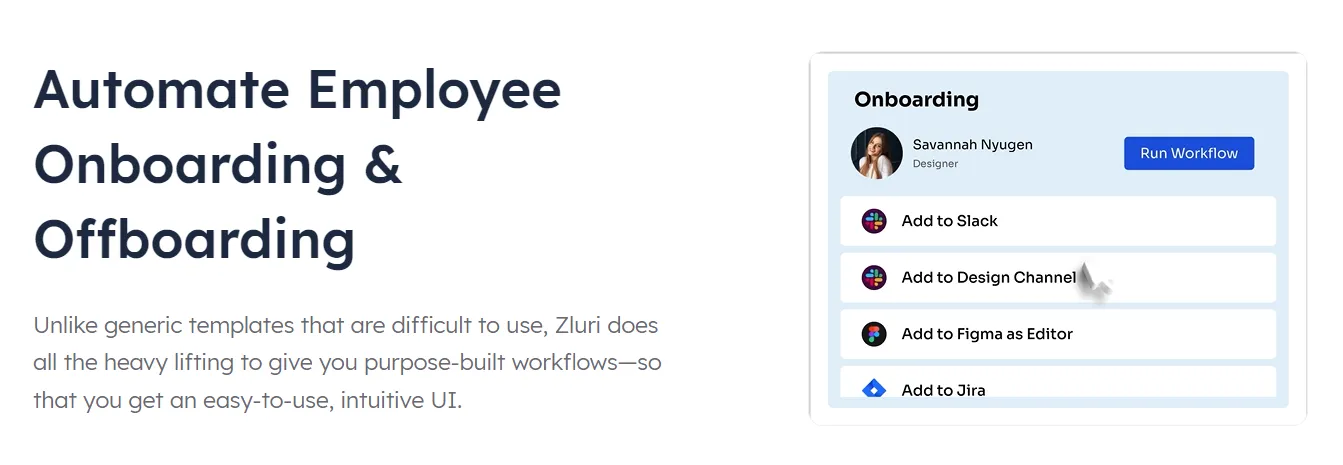
Zluri distinguishes itself as an outstanding access management platform. It proficiently oversees every phase of a user's lifecycle within the company, from seamlessly onboarding new users to securely offboarding them when their tenure concludes. Zluri automates the entire process.
Let’s explore Zluri’s various capabilities that help with user’s lifecyle.
- Zero-touch onboarding and offboarding for Google Workspace SSO Customers:
Zluri's zero-touch automation revolutionizes the onboarding and offboarding processes for Google Workspace SSO users. Manual user account creation and access provisioning are things of the past. With Zluri's access management, IT teams effortlessly streamline these processes, assigning roles and granting necessary app access with just a few clicks.
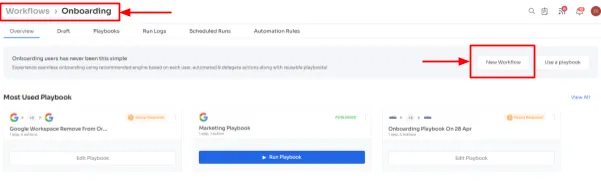
Even for applications lacking SCIM support, Zluri's innovative approach empowers IT teams to craft customizable onboarding workflows tailored to the organization's needs. This saves valuable time and ensures consistency and accuracy.
New employees immediately gain access to essential SaaS applications, seamlessly integrating into their roles from day one. This frees up your IT team to focus on strategic initiatives.
- Access Beyond SCIM for Customers Using Different SSO Providers:
Recognizing the diverse SSO landscape, Zluri goes beyond SCIM limitations to accommodate customers using various SSO providers such as Okta or Jumpcloud.
By leveraging direct API integration with applications, Zluri enables seamless user provisioning even for applications lacking SCIM support. This ensures consistent access management across all SSO platforms, enhancing operational efficiency for IT teams.
- Secure User Deprovisioning:
Zluri prioritizes security by offering secure user deprovisioning capabilities. Through automated processes, Zluri facilitates the swift and centralized revocation of application access for departing employees.
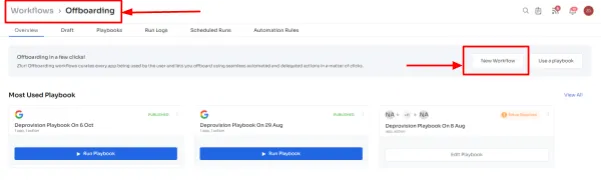
This minimizes the risk of unauthorized access and ensures sensitive company data remains protected.
Features
- HRMS Integration: Zluri seamlessly integrates with your HRMS, providing real-time access to employees' profiles. Automatic updates are triggered for changes like new hires or role adjustments.
- In-App Suggestion: Zluri allows employees to add themselves directly to different channels, groups, or projects within the application. This streamlines collaboration and ensures seamless integration into relevant teams and projects.
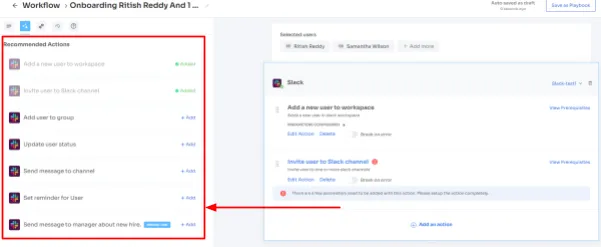
- Contextual App Recommendations: Zluri offers contextual app recommendations tailored to each employee's department and role during onboarding workflows. This eliminates manual app searching, saving valuable time and ensuring access to necessary tools from the outset.
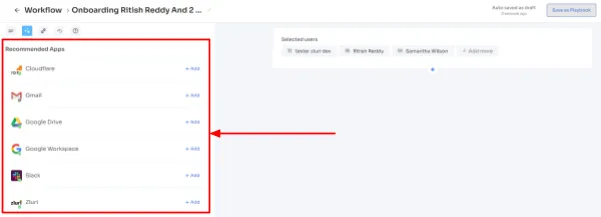
- Automated Playbook: Zluri's playbooks streamline workflows by enabling users to save and reuse customized processes. This eliminates the need to recreate tasks repeatedly, enhancing operational efficiency.
- App Launcher & Access Request: Zluri prioritizes employee experience with an app launcher featuring pre-approved SaaS apps. Employees can quickly request access from this curated selection. Upon request, your IT team verifies identities and reviews applications for security and compliance.

Book a demo now and try it.
Customer Rating
- G2: 4.8/5
- Capterra: 4.8/5
2. Okta
Okta's lifecycle management helps your IT admin eliminate manual onboarding and offboarding processes through automation. It allows them to grant access based on role, designation, or department and revoke all access upon departure.
This also helps improve your employee experience as they don't have to wait longer to get onboarded and start their work from the day of joining.
Furthermore, it revokes access and suspends users' accounts quickly with just a few clicks, allowing your team to recuperate software licenses and save on costs. Also, it secures the SaaS app data from security breaches or hacking through a still-active account.
Features
- Okta's lifecycle management handles access provisioning for all employees from one place and integrates with your HR system to streamline auto-provisioning and deprovision access processes. Additionally, if you want to customize your workflow, you can simply do it through Okta workflows without the need for coding.
- It conducts audits and generates reports showing which employees can access a given application and which were recently deprovisioned. This helps you get a centralized view of users and their account access.
Customer Rating
- G2: 4.5/5
- Capterra: 4.6/5
3. OneLogin
OneLogin's identity lifecycle management platform is designed to automate provisioning processes for the swift onboarding of users. It imports entitlement definitions from various applications, providing flexible rules to determine each user's entitlements. For instance, upon creating a new user in Salesforce, the identity provisioning system can simultaneously assign them to specific groups like Admin, Marketing, or Sales.
Also, this user lifecycle management software recognizes the critical need for offboarding. Thus, it acts as an effective \"kill switch\" to prevent unauthorized access from former employees.
Features
- Acknowledging the unique needs of different organizations, OneLogin's user provisioning tool allows the importation of custom attributes from external directories. These attributes can be seamlessly pushed to compatible applications, including Jive, Samanage, or Salesforce.
- OneLogin Workflows enables your IT team to deploy custom logic to streamline onboarding and offboarding processes with precision and efficiency.
Customer Rating
- G2: 4.4/5
- Capterra: 4.6/5
4. Microsoft Entra
Microsoft Entra is another of the best user lifecycle management software that offers a robust suite of features designed to enhance user productivity and fortify organizational security by automating identity lifecycle processes.
By incorporating customizable workflow templates, Microsoft Entra facilitates the swift onboarding of new employees. It grants access right on day one, ensuring new team members hit the ground running and maximize productivity from the outset.
Also, it responds promptly to role changes within the organization by effortlessly updating, adding, or removing access to resources. Thus, Microsoft Entra's lifecycle management ensures agility in managing access, enabling seamless transitions when team members' roles evolve.
Not only that, this user lifecycle management software ensures that users go through a secure and compliant offboarding process when they leave the organization. This gives peace of mind to both the organization and the person leaving. Also, timely and securely deprovisioning users adds an extra layer of security.
Features
- Entra's lifecycle management seamlessly integrates with HR systems like Workday, SAP SuccessFactors, Microsoft Dynamics 365, and Aquera to automatically provision or deprovision user access based on HR signals.
- It utilizes templates to automate common identity and access tasks, such as the initial setup for new users and updates related to roles, teams, or locations for existing employees.
Customer Rating
- G2: 4.5/5
5. Sailpoint
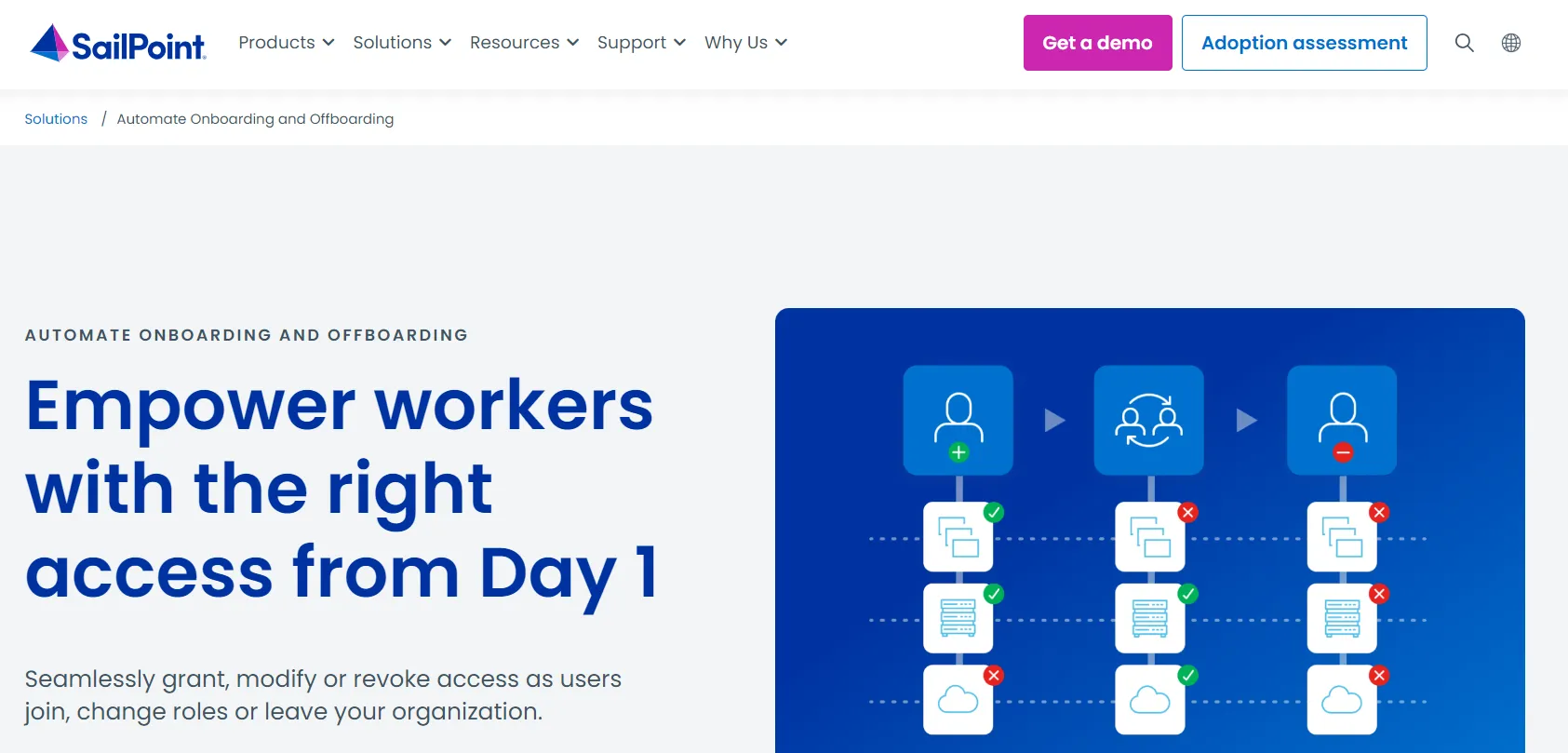
Sailpoint user lifecycle management software facilitates the seamless onboarding of new hires by automating and accelerating the provisioning process. This not only boosts user productivity from day one but also prevents human errors, ensuring efficiency for both workers and IT teams.
Also, this tool addresses the risk of over-provisioning or unauthorized access by former employees, providing a crucial layer of security. SailPoint also ensures compliance requirements are met, offering validation, audit, reporting, and metrics features.
Features
- SailPoint’s role-based provisioning policies ensure that the workforce’s access remains within the bounds of their job description. This aligns access privileges with organizational hierarchies, ensuring a clear separation of duties.
- SailPoint reduces security risk by meticulously managing worker accounts. It ensures that former employees no longer have access to resources, while current workers are equipped only with what they need, mitigating potential security risks.
Customer Rating
- G2: 4.4/5
- Capterra: 4.1/5
6. Jumpcloud

Jumpcloud is a widely known identity lifecycle management software that allows your IT team to centrally manage one identity and set of credentials per user. This user lifecycle management software enables the automation of identity creation for new users, manages access changes during the identity lifecycle, and facilitates seamless identity and access termination upon a user's departure.
Furthermore, Jumpcloud's identity lifecycle management gives your IT team complete control over user identities, no matter where they are. Whether you use it by itself or with other tools, Jumpcloud ensures that administrators and users have a smooth experience, no matter where they're located.
Features
- Jumpcloud simplifies access control through group-based strategies, including automated dynamic groups. This feature allows instant access provisioning for new users based on their roles or departments. In the same way, when a user departs the organization, suspending their account automatically revokes their resource access, safeguarding confidential data and processes.
- Jumpcloud reinforces identity security throughout a user's employment by layering multi-factor authentication, conditional access policies, and single sign-on across identities. This ensures that identities remain secure and compliant with organizational policies.
Customer Rating
- G2: 4.5/5
- Capterra: 4.6/5
7. MiniOrange
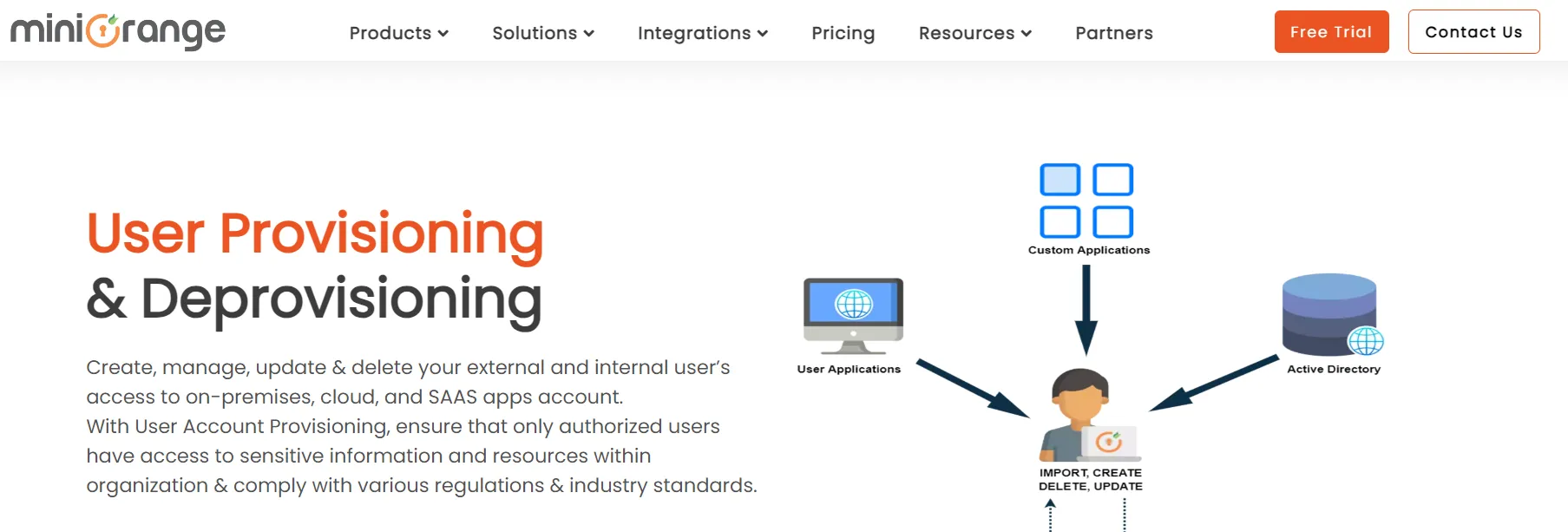
MiniOrange’s user lifecycle management solution ensures that any changes in user access across applications sync in real-time with the platform and all other integrated directory apps within a second. This immediate synchronization minimizes delays and ensures accuracy.
Also, this tool offers automatic bidirectional synchronization that ensures that all integrated directories and applications stay updated after a user is modified within MiniOrange. Furthermore, MiniOrange supports integration with various HR applications/systems, AD, LDAP, and other IDPs and directories, including Azure AD and LDAP.
Features
- MiniOrange enhances security by implementing role-based access control, only granting user access when necessary. This prevents potential security breaches and unauthorized access to critical company data.
Customer Rating
- G2: 4.4/5
- Capterra: 4.4/5
8. GroupID
GroupID, now a part of Netwrix, is a tool designed to simplify user management within Active Directory and Entra ID. By automating lifecycle management, GroupID empowers business owners to take control of resource access, ultimately enhancing security and increasing IT productivity.
How does it do that? Netwrix GroupID streamlines the process of user provisioning and deprovisioning in Active Directory and Entra ID. Syncing data in bulk from authoritative sources like HRIS platforms ensures accuracy and efficiency in managing user access.
Changes made to users in one directory are instantly reflected in near real-time to a linked identity store, eliminating the need for third-party connectors. This seamless synchronization ensures that user information is always up to date across multiple directories.
Additionally, this user lifecycle management software introduces access workflows allowing users to request the necessary access. Resource owners or managers can easily approve or deny these requests, reducing the IT workload and ensuring efficient access management.
Features
- Attestation workflows in GroupID ensure users regularly confirm that their accounts are still needed. This proactive approach enables disabling unnecessary accounts, enhancing overall security and compliance.
Customer Rating
- G2: 4.9/5
Seamlessly Manage User’s Lifecycle With The Best User Lifecycle Management Software
So, here you have it: an overview of 9 user lifecycle management software options. However, the ultimate choice rests with you regarding which one to consider. Selecting the best ULM tool is a critical decision that requires careful consideration of various factors. You need to evaluate the specific needs and dynamics of your organization. Also, consideration of key factors such as cost, complexity, scalability, integration capabilities, automation features, and reporting capabilities is paramount.
Each organization has its own set of priorities, and the chosen ULM tool should seamlessly align with these priorities to maximize its impact. Ultimately, the best ULM tool not only meets the organization's immediate needs but also provides scalability, adaptability, and efficiency in managing the entire user lifecycle.
Frequently Asked Questions (FAQs)
What Is the User Account Lifecycle Process?
The user account lifecycle process refers to the various stages a user account goes through during its existence within an organization. There are three main stages involved in this process: creating an account, reviewing or updating it, and deactivating the account if needed—kind of like "CRUD."
What Does Customer Lifecycle Management Software Do?
The customer lifecycle management tool keeps track of the customer journey and guides them towards brand loyalty and advocacy. This tool also helps improve customer experiences, which makes the business more successful, and more people notice the brand, making both new and current customers happier.









.svg)














