Access management is a systematic solution that an organization should follow to streamline IT processes. It will help businesses attain efficiency and improve productivity by managing access control appropriately and eliminating manual handling of IT tasks.
Organizations rely on traditional methods of managing access control which is prone to human errors, reduce productivity, and deliver inefficient results. For example, it takes several days to grant access and revoke access from the employees, which consumes the productive time of IT admins and affects the IT processes. Furthermore, monitoring overall access permissions without an appropriate control system becomes a complex task.
The organization requires flexible and efficient access control solutions to meet the business's needs. This is where access management plays a major role in an organization to overcome all the potential challenges and effectively deal with them by automating the IT processes.
Let's first understand in detail the definition of access management and how it works in business processes so that you gain a better idea of how it will be helpful for your growing organization.
What Is Access Management & How Does It Work?
Access management is the process of monitoring, identifying, controlling, and managing authorized access of users to a SaaS application or a system. This solution helps businesses to secure crucial data from unauthorized users who can hamper data security. In addition, it adds an extra layer of protection over business networks to prevent cyberattacks or data breaches.
Access management ensures only the right users get access and privileges to assigned SaaS apps in the organization. It monitors the access activities, such as login attempts by both authorized and unauthorized users, and restricts the users from unauthorized access.
It securely grants access to new employees upon onboarding and revokes access at the time of deprovisioning. Additionally, it controls the overall access permissions to streamline the business processes.
Given below are a few important points of access management:
- It enhances efficiency by automating the manual provisioning and deprovisioning process.
- It ensures that assigned employees can gain access to the required data on time, which helps in increasing productivity.
- It verifies the employee's identity before granting authorized access to SaaS apps.
- Passwords were a significant factor in data breaches, so it replaced password solutions with single-sign-on and multiple-factor authentication, which is less time-consuming and more secure.
- Additionally, access management systems follow effective protocols and standards to protect individual employees' credentials from cyber attacks.
How does access management work?
Access management is more flexible and secure than a traditional password and username solutions. In addition, it streamlines the access control processes in the organization. In general, access management performs two tasks in business processes:
First, the access management system verifies the employees, applications, and on-premises hardware by authenticating credentials against the organization's database.
Second, it restricts access to assigned users and only grants certain levels of privileges to the users. This solution provides a portion of access to the assigned users. For example, the IT admin will get access to conduct and record a meeting in a zoom app, but the employee will only get access to conduct a meeting.
This blog will discuss why you should implement access management in your organization.
3 Reasons Why Access Management Is Necessary
Listed below are three reasons why access management is crucial for your business to effectively manage access control and mitigate the challenges faced by IT admins.
1. Streamlines IT processes
Organizations hire new employees frequently to meet the requirements and attain the business goal faster. However, to onboard multiple new employees and granting them access to the resources becomes a tedious task for the IT admins to handle manually.
Businesses follow a ticketing system, where an employee's approval goes through many processes before getting accepted. It's a time-consuming process with vast possibilities of human errors that reduces efficiency and impact overall productivity.
Organizations can opt for an efficient SaaS platform such as Zluri to properly manage access control.
With Zluri, you can eliminate the manual handling of access control and automate it to reduce human errors. It simplifies the provisioning process by granting authorized access to apps to authorized users upon onboarding. This tool restricts unauthorized users from accessing the apps by keeping track of all the login access activities.
Zluri allows you to create an onboarding workflow for the employees that you can reuse for other new hires of the same department, role, or position. Although you can create a workflow once and use it multiple times, Zluri eliminates repetitive and mundane tasks to streamline the process.

You can select apps that you want to grant access to employees from the recommended apps and click on the run. It will automatically grant secure access to assigned employees. With the help of in-app suggestions, you can add employees to different channels. Furthermore, you can save your workflow in the playbook to run it later or reuse it.
Additionally, it provides a single dashboard where you can monitor all the access permissions to streamline the IT processes.
Furthermore, by automating the provisioning process with Zluri, the organization will save on operational costs, which can be utilized in other necessary IT tasks which help your business improve productivity and attain efficient results.
2. Enhances employee experience
During the onboarding process, new employees had to wait for a long time to get approval from IT teams to access SaaS apps. Even upon the change in role, they had to wait for access permissions to specific applications, which hampers the flow of work and reduces productivity.
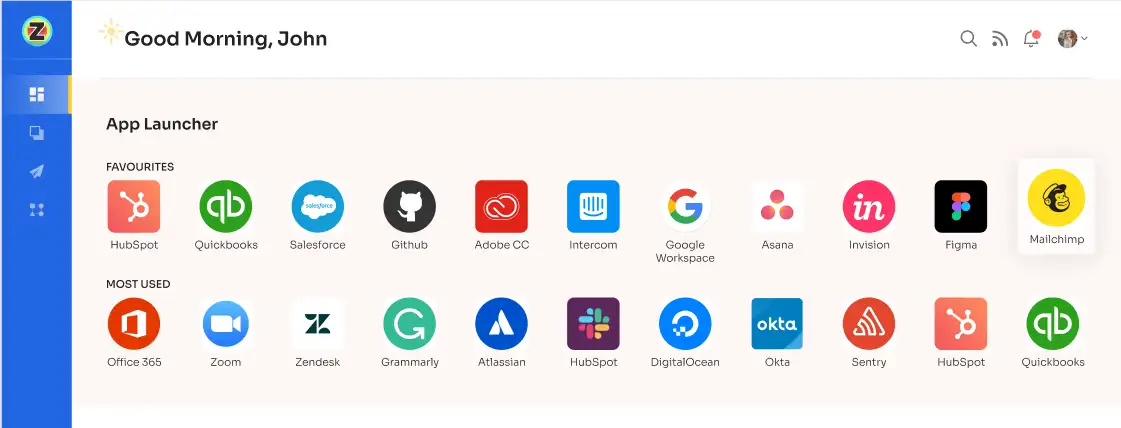
To reduce the waiting time of employees and enhance their experience, Zluri offers an Employee App Store, a self-serve model. New and existing employees can select SaaS applications of their choice from the employee app store and gain quick access to them.
With Zluri, employees will be fully aware of all the SaaS apps available in the organization. As a result, they can choose alternative apps that are present in the SaaS stack of the business before making a purchase and reduce wasting time on researching and evaluating external apps. Furthermore, if employees want access to an app that is not present in the EAS, they can also request it.
Now, with Zluri, employees do not have to wait for the approval of the IT team to grant them access to the required app and waste crucial time that time can spend on more productive work. Employees can start from day one of joining without wasting much time, which will help the business increase its productivity and attain organizational goals faster.
3. Improves data security & compliance
IT teams used to revoke access manually from the ex-employees at the time of offboarding. It gets difficult for the IT team to deactivate multiple employees' accounts simultaneously, which impacts the deprovisioning process, and chances of delay in revoking access come into the picture.
There are possibilities where IT teams can miss out on revoking the access of certain SaaS apps from the ex-employee who has the power to hamper the data as they still have access permissions. This can result in data breaches and even identity theft.
Furthermore, organizations could only track down some of the access permissions due to increased SaaS adoption, resulting in being unable to revoke all access to SaaS apps and resources from the ex-employee at a given period.
Businesses used to purchase SaaS app licenses in bulk without verifying if the apps met the business compliance regulatory standards. Later, the organization has to pay hefty penalties for the SaaS apps for not meeting the compliance regulations, which impacts the overall SaaS budget of the business.
To eliminate inefficient workflow, illegal access, and non-compliant apps, organizations can opt for Zluri.
With Zluri, businesses can view all the access permissions in a single place which becomes more manageable for IT teams to revoke access to all the apps from the employee without delaying the deprovisioning process. Also, it helps keep track of which app's access is still pending to be revoked to avoid missing out on access permissions that will prevent cyberattacks.
You can create an offboarding workflow with Zluri where you can view, in the overview tab, all the places from where you need to remove the employee that help you revoke access from all the apps, remove from all the groups and deactivate the account. Once you create the workflow, you can directly run it or save it to the playbook to run it later.
Additionally, upon a change in an employee's role, you can decide which access to apps to keep and which ones to remove, saving time upon reprovisioning.

With Zluri, you can view all the critical apps and users in your organization. This will help you choose apps that meet compliance regulations and restrict critical users from accessing apps to ensure the privacy and security of the data.
It allows you to view the threat level of a SaaS app, such as SaaS apps with access permission to read, write, modify, and delete have higher threat levels than applications with just read and write access permission. Accordingly, organizations can decide to whom to assign restricted access permissions to SaaS applications.

Furthermore, you can even check the risk score of apps based on events, shared data, compliance, and security probes, which will give you in-depth data on SaaS apps and whether it meets security and compliance standards.

Additionally, it also helps eliminate shadow IT by discovering all the SaaS apps and monitoring the access activities of employees. That will help the organization prevent security and compliance risks.









.svg)














