User Access Reviews (UARs), also widely known as access certification and periodic access review, are crucial to access management to mitigate potential risks. However, managing this complex task manually can be time-consuming, tedious, and prone to errors. The solution lies in automating user access reviews, empowering your IT team to simplify the process effectively and efficiently.
User Access Reviews (UARs) are often overlooked as just routine audits, but they hold significant importance in this ever-changing world of access management. It's crucial for you, as an IT manager, to understand that UARs go beyond meeting compliance requirements.
They are essential for ensuring the security of your organization's SaaS app data, streamlining IT operations, and verifying that users have appropriate and legitimate access rights.
UARs allow you to answer important questions within your organization, such as who has access to what, the level of access permissions each user possesses, and which access rights are authorized and approved.
Further, by conducting regular UARs, your IT team can identify unauthorized or inappropriate access, ensuring a secure and controlled access environment. However, managing the entire process manually can pose significant challenges for your IT team, but your team can seamlessly mitigate these challenges through automation.
Before we dive into detail about how automating user access reviews can help your IT team streamline the process. Let’s first walk through a few of the challenges that are encountered by IT teams while manually managing the UARs process.
Challenges Faced By IT Team While Managing User Access Reviews Manually
When done manually, UARs can be a time-consuming process that involves reviewing each user's access rights to ensure alignment with their job responsibilities and security policies.
In general manual user access review process involves the given below step:
- Generating a list of user accounts and their access privileges across various systems and applications.
- Sending the list to managers or other designated reviewers for approval or revocation of access privileges.
- Then, managers manually review access privileges and suggest changes as needed.
- Accordingly, the IT team collects managers' feedback, updates access privileges, and implements changes across systems and applications.
After going through the steps, you might have understood that manually managing user access reviews is labor-intensive, especially for organizations with many users or complex access structures. This complexity can lead to errors and pose security and compliance risks.
You must be wondering what kind of challenges one can encounter. To help you understand better, we have listed below a few common challenges that IT teams encounter. - Access creep or orphaned accounts: Infrequent reviews can result in employees retaining unnecessary access or accounts remaining active after an employee leaves, creating security vulnerabilities.
- Delay in detection of policy violations: Manual reviews may not immediately identify policy violations, allowing them to persist and potentially lead to breaches.
- Human error: Mistakes in interpreting access permissions or missing policy violations can occur during manual reviews, increasing security and compliance risks.
- Inefficient resource utilization: Manual reviews consume valuable time and resources, diverting them from higher-value tasks such as threat detection and incident response.
To address these challenges effectively, the optimal approach is to automate the process. By doing so, your team will accelerate the user access review process efficiently and reduce errors. So let’s look into the benefits of automating UAR and how it enables your IT team to streamline the entire process.
How Can Automating User Access Reviews Help Your IT Team?
Below are a few of the significant advantages of automating the user access review process
- Saves your IT team's productive time: By automating UARs, your team can save significant time that would otherwise be spent on manual reviews. This allows your security and compliance teams to focus on more strategic tasks.
- For example, with automation and integrations, there's no need for your team to engage in back-and-forth communication or spend time gathering insights to review access. Instead, they can effortlessly access all the necessary and up-to-date information in a matter of moments. This process, which would have taken days to accomplish manually, is now streamlined and expedited through automation.
- Helps in improving accuracy: Automated UARs greatly enhance accuracy by reducing the chances of errors that can occur during manual reviews. They also provide more comprehensive data, enabling thorough analysis of user access, and can generate legitimate reports accordingly, which will help during an audit.
- Enhanced Security: Automating UARs enhances security by ensuring proper user access management in line with your organization's security policies. It helps identify potential security risks, enabling your IT team to proactively take safety measures to mitigate them.
Furthermore, to effectively automate UARs, it is advisable to follow these three practices:
- Step 1: Establish clear policies
Before implementing an automated UAR process, define clear policies and procedures that outline how user access will be reviewed and managed. - Step 2: Use effective automation tools
Choose suitable tools that align with your organization's needs and requirements. SecurEnds, preferred by many customers over comprehensive IGA software, offers cost-efficiency and usability benefits. - Step 3: Thoroughly monitor the process
Regularly monitor the automated UAR process to ensure its effectiveness and promptly address any issues that may arise.
Now that you have gained a basic understanding of how automating your user access review can significantly streamline the process, let’s find a tool that will help you automate the process. Though there are multiple tools available, Zluri emerges as an exceptional solution in the market, offering efficient capabilities to automate the process effectively.
So here’s how Zluri is the perfect automated platform for your IT team to streamline access certification.
Automate Your Access Certification Process With Zluri
Is your IT team burdened by the manual gathering of app access data for user reviews, and you need an immediate solution for it, then look no further because with Zluri your search comes to an end. Zluri is an automated platform designed to assist your IT team in effortlessly identifying which users have access to which SaaS applications and data, the level of permissions they are holding, and much more, thanks to its standout capabilities. Also, with visibility into accurate data points, reviewers can review access without any hassle.
Zluri sets itself apart from competitors by offering a range of exclusive key features and prioritizing data stored in SaaS apps and compliance. This further helps streamline the access review process.
For example, two major challenges frequently encountered by IT teams, i.e. lack of access visibility and audit fatigue. Traditionally, IT teams rely on manual methods or inefficient IGA solutions to review access, collecting data in formats like Excel sheets and JSONs, reducing the accuracy of data, and not to forget the errors involved during the process.
So what Zluri does is it mitigates these challenges by introducing 9 discovery methods i.e. MDMs, IDPs & SSO, direct integration with apps, finance & expense management systems, CASBs, HRMS, directories, desktop agents (optional), and browser extension (optional), that provide your IT team with comprehensive data.
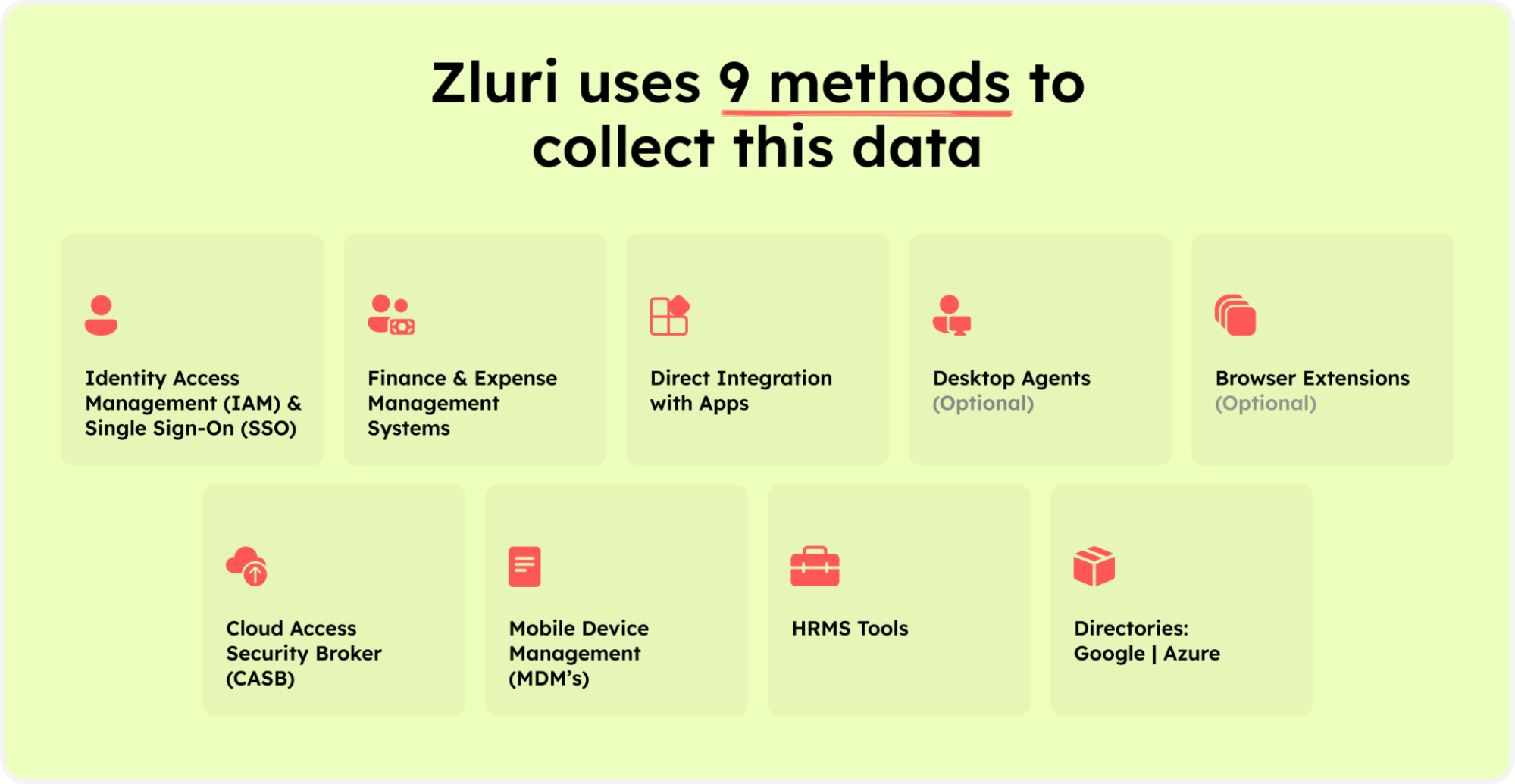
Zluri’s nine discovery methods
This includes crucial information such as which users have access to which apps, activity status (active or inactive), and more, significantly enhancing their visibility into access data. This valuable data is conveniently presented through a centralized dashboard.
With this information in hand, your IT teams can generate accurate reports, streamlining the access review process. It also automates the access review process making it more efficient and audit-ready, effectively reducing audit fatigue.
Zluri is not restricted to these capabilities only, it has more to offer. So let's learn in detail about its other key access review capabilities and see how they simplify and automate the access review process:
Key Access Review Capabilities of Zluri
Given below are the key capabilities of Zluri’s access review that enables your IT team to streamline the access review process effectively and efficiently:
- Review Automation
With Zluri, you can automate the entire review process, enabling your IT admin to make the access review process 10x faster and reduce 70% efforts. It allows your IT team to evaluate user access automatically, eliminating the need for manual review tasks.
- Auto Remediation
Zluri simplifies access remediation by automatically revoking access based on predefined conditions. When certain criteria are met, such as expired user accounts or policy violations, it enables your IT team to immediately take action and revoke access.
Another example is an employee with administrative-level access to a specific application, although their job role does not necessitate such elevated permissions. Ideally, he should only have user-level access to the application. To tackle this situation seamlessly, Zluri automatically modifies the employee's access permissions, downgrading them to the appropriate user-level access, aligning precisely with their job requirements.
Doing so, minimizes the risk of unauthorized access and strengthens your overall security posture.
- Auto-Generated Reports
With the help of these features, your team no longer has to spend time manually generating reports. It gathers the app access-related data and automatically generates reports such as access patterns, which users are no longer actively using a particular application, login/logout attempts, and unauthorized access attempts. It provides your IT team with up-to-date insights and analytics.
Furthermore, by delivering reports directly to your inbox, Zluri ensures your team stays informed and can seamlessly track access review outcomes.

- Recurring Certification
Through automated scheduling, your IT team can set up regular access reviews (after every 3-6 months). This ensures that access permissions are continuously assessed and aligned with users' roles and responsibilities and standard access policies.
- Anomaly Detection
Zluri utilizes advanced AI-driven anomaly detection to identify risky access patterns and potential misconfigurations that may go unnoticed by human reviewers. Analyzing access data and user behavior enables your IT team to detect anomalies that indicate security threats or compliance issues.
This proactive detection strengthens your system's security and allows your team to take action to mitigate risks.
- Certification Templates
Zluri provides pre-built certification templates that simplify the review process across. Your IT team can also customize the templates to align with specific requirements.
- Continuous Reviews
Zluri ensures that access permissions are regularly assessed through continuous reviews. This ongoing process guarantees that access remains up-to-date and aligned with access transitions/modifications. By continuously monitoring access and making adjustments as necessary, your IT team can maintain a secure and compliant access environment.
- AI Compliance
Zluri provides real-time notifications, keeping your team informed of compliance-related activities and changes. By adhering to regulatory standards and automating compliance checks, Zluri helps you meet all the compliance requirements and simplifies audit processes.
Now let’s see how your IT team can automate the access review process with Zluri.
Steps To Automate Access Certification In Zluri
Your IT team/GRC team needs to follow the given below steps to automate the access certification process:Step 1: From Zluri’s main interface, click on the ‘Access Certification’ module.
Step 2: Now select the option ‘create new certification.’ You have to assign a certification name and designate a responsive owner to oversee the review.
Step 3: Under Set Up Certification, choose the ‘Application’ option. Proceed further by selecting the desired application for which you want to conduct the review and choose a reviewer (generally, the primary reviewers are the app owners) accountable for reviewing access to that particular application.
After that, you need to select the fallback owner/reviewer, if the primary reviewer is unavailable, the fallback owner can review the user access (you can select anyone for the fallback reviewer, whom you think is responsible enough). Also, the reviewers will get notified through the mail that they need to conduct a review.
Once you are done selecting the reviewers, you can click on Next.

Step 4: Select Users for Review; choose the users whom you want to review for the selected application. Once you are done selecting the users click on next. You will be able to view all the information related to the users. Then you need to specify the criteria or parameters such as user department, job title, usage, and more. Now click on update and then click on next.
Note: Select those relevant data points only that you wish your reviewers to see while reviewing the access. By filtering the criteria appropriately, you enable your reviewers to make swift and well-informed decisions, streamlining the review process and ensuring efficiency.


Step 5: Now the Configure Action page will appear, basically here you have to choose actions. These actions will run post the review.
There are three actions:
Approved- once reviewers approve the user access, Zluri won't run any action, the users can continue with their same access without any interruption.
Rejected- when the reviewer declines or doesn’t approve the user access, you have to run a deprovisioning playbook to revoke the access of that application from the user. If the user has access to critical apps then you can request the assigned reviewer to manually deprovision the user access or else Zluri will auto remediate if it’s not a critical access.
Modify- In this last case, you again need to create a playbook to modify the user access. However, you need to state whether the access permission needs to be upgraded or degraded.
Step 6: Additionally, you can even schedule the actions by setting up the start date and within what time span you want the review to be completed.

Step 7: Lastly you can keep track of the automated access review process by clicking on the ‘Review Status’ and view whether the review is still pending, modified, declined, or approved.
Also, you can add multiple applications and follow the same process for each selected application.
Zluri also provides the owner access to a snapshot view of the entire certification process status. Also, they can get an overview of the pending reviews and monitor the status of each app’s review, including their assigned reviewers and their completion status.
You can even send reviewers reminders who are yet to complete their reviews.
Further, to streamline the process for reviewers, Zluri provides reviewers with all the user access data in a single screen, i.e. reviewer screen. For the same screen, reviewers can approve, modify, and decline access by verifying the data, and also they have to add relevant comments on the same.
Now, you will be able to view the entire status of the review process on the chart and once the process is completed and the owner (assigned reviewer of the certification process) is fine with the review. You can click on conclude and it will straight away send the reports to the reviewer's email.
So, what are you waiting for? Don't miss out on the chance! Book a demo today to see how Zluri enables your IT team to control and govern access seamlessly.









.svg)



.svg)
.svg)
.svg)
.svg)

.svg)

.svg)

.svg)
















.webp)







.webp)
.webp)





.webp)