SaaS decentralization creates a flexible environment for employees to operate seamlessly in business processes. It improves productivity as it gives freedom to the employees to choose their required apps.
However, this can bring security and compliance risks like data breaches, cyberattacks, etc., to organizations. Following the best practices can empower the IT teams to mitigate these risks.
We are aware of hybrid work; this isn't a minor or temporary trend. It is a growing trend in the competitive market post-pandemic. Due to this, there is an increase in SaaS adoption, allowing employees to work individually on their tasks. This will enable employees to quickly sign up for SaaS apps, leading to a decentralized business environment.
Employees can make their own decisions in the decentralized business processes. This further enhances the user experience, saves time, and reduces their workload. In addition, individual employees can better understand the SaaS apps and get more workspace flexibility. Also, it helps meet the organizational goals on time.
However, IT teams working in a decentralized organization face issues as well. It brings compliance and security risks like data breaches, cyber-attacks, and more to the organization.
Additionally, decentralized SaaS governance may increase IT costs when employees purchase duplicate software or discontinue using the existing software without terminating the license or subscription. This makes the organization complex and adds governance challenges.
This post will allow you to avail yourself of the benefits of a decentralized approach while still following the few best practices to protect your organization from any potential security and compliance risks.
Decentralized SaaS Governance Best Practices
Let us now discuss the best practices you can follow to have control over your decentralized SaaS governance.
1. Use a SaaS management platform
Decentralization can lead to security and compliance risks due to the IT team lacking visibility into the SaaS applications. SaaS management platform allows IT teams discover and gain insights into an organization's SaaS apps.
With an SMP, you can get an overview of the risk and threat level of the application and make decisions accordingly. After identifying the non-compliant applications, the IT team can restrict or terminate the application. Based on that, the IT admin can suggest other applications to the users with similar functionality.The IT team can suggest users with alternative apps with the same functions for better workflow.
An SMP like Zluri provides visibility into the organization’s SaaS applications. It allows you to discover applications in 9 different discovery methods. As per KuppingerCole’s report, Zluri provides a single source of truth for all SaaS applications in an organization.

Zluri’s nine discovery methods
Moreover, Zluri helps you to stay secure and compliant with ISO 27001, SOC 2, GDPR, etc. We help you maintain SaaS compliance and make you audit-ready.

The IT team can discover which applications have low or high risks, threat levels, and compliance in this SaaS platform. In addition, we offer you security and compliance information for each SaaS application, including events, shared data information, compliance, and security probes.

With Zluri, you can view critical apps with high threat levels and risk scores with risk levels. This alerts you to refrain from using critical apps that can lead to compliance violations and make you pay hefty fines during audits.
For example, an organization is using Asana as a project management tool. With Zluri, you identify the threat levels of Asana, and due to the high threat level, it gets classified as a critical app. This indicates you to avoid using this application and prevent security risks like cyberattacks.

Critical Apps

Critical users
2. Automate your onboarding and offboarding process
In decentralized business processes, there needs to be a systematic way for onboarding and offboarding. IT teams sometimes need to provide required access to apps during manual onboarding. The employees sign up for the applications independently, and the IT teams need to be made aware of it.
Moreover, when an employee leaves the organization, the app remains active, and the employee continues to have access to it. So it's necessary to revoke access to the applications on time. This will prevent the organization from any security threats and help to stay compliant.
Automating your onboarding and the offboarding process can help you eliminate security and compliance risks. With Zluri, IT teams can automate the onboarding and offboarding process in the organization. It allows you to create workflows for provisioning and deprovisioning users, consisting of a set of actions required to complete the tasks. This workflow can be saved as a playbook for future use if required.
Furthermore, you can choose multiple users to onboard and select the apps required to grant secure access to employees. This can reduce security & compliance risks.

On the other hand, the offboarding process is crucial when an employee leaves the organization. A lack of a systematic approach to the offboarding process can lead to data breaches and cyberattacks. With Zluri, the IT teams can revoke or terminate access during the deprovisioning of the employee. This will ensure that an ex-employee has no more access to the data or any organization apps. Hence, reducing the security and compliance risks of the organization in the future.

3. Educate your employees on security and compliance risks
As discussed earlier, decentralization can lead to security and compliance risks for the organization. For this reason, employees must be aware of SaaS security risks before signing up for the applications.
This is due to the need for more awareness of the employees while signing up for any SaaS apps. Hence, educating the employees on security and compliance is crucial to protect the organization and overcome the decentralized SaaS governance.
Implementing security awareness training for employees can prevent data breaches and phishing attacks. With the training, the employees will be aware of the security threats that can impact the sensitive information in the organization.
Security awareness training can reduce overall security costs. In addition, the awareness of security behaviors and threats can help companies to save money on compliance and cyberattack costs.
Further, well-planned security training can impact the level of understanding of the security practices and programs of the organization. This can prevent security disasters. In addition, when they receive the training, they understand the importance of maintaining security to protect the organization from cyberattacks.
In addition, the security training can be conducted in multiple forms like quizzes, Q&A sessions, gamification, demonstration, giving real-time security situations, etc.
With the training, you can inform the employees about the security measures required for email. For example, multi-factor authentication plays an important role in preventing security threats through email. This can be guided and implemented for each email in the organization. But understanding the importance of MFA and implementation training is essential before implementation.
Moreover, you can discuss with your employees how they can secure their work system. For example, you can guide them to use the company devices for only company-related work. This will limit personal activities on their work devices and also restrict access to work from their personal devices.
4. Use a self-serve model
A self-serve model can be used to have control over the decentralized system. This gives complete freedom to the employees to choose the appropriate apps that will meet their requirements. The primary benefit of using the self-serve model is that the IT teams will approve the apps listed in this. This will ensure the organization's security and help you comply with government regulations.
Zluri offers a self-serve model - Employee App Store (EAS). With this, employees can get information, such as security & compliance details and app alternatives. It will help them make an informed SaaS purchase decision and enhance the decentralized procurement app decision. Also, saves time that employees would need help in researching info about the app and evaluating them.
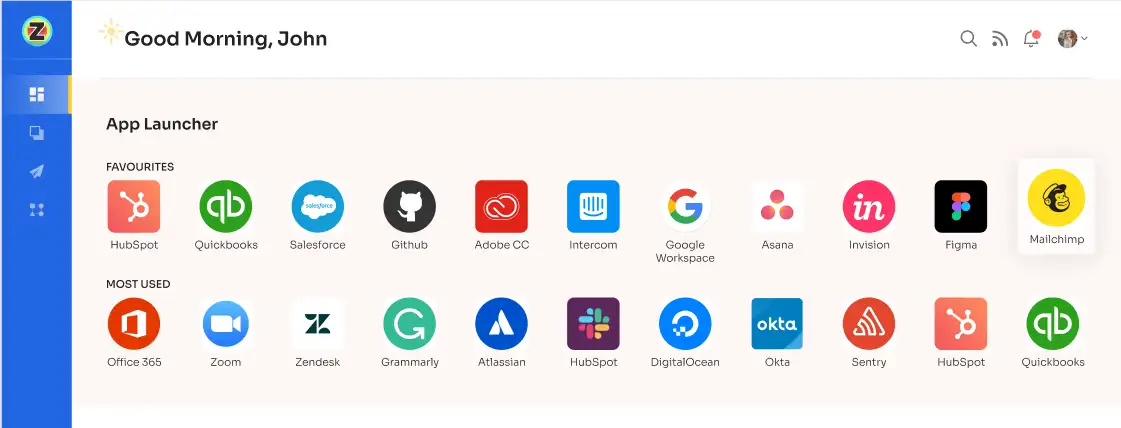
Employees can see the risks and threat levels of the app. The compliance information can be accessible for each application to provide a complete security overview for users. In addition, the employees can see recent security events from around the globe for any particular application.
Moreover, with EAS, the IT teams can automate the approval process. The employees are no longer required to wait for approval and start using the applications as needed. This will be a best practice for mastering decentralized SaaS governance.
5. Have control over the user's access
Decentralization in business processes has led to the mishandling of user access in SaaS platforms. As a result, the users have access to most of the applications present in the organizations with minimum restrictions. This needs to be clarified about who is accountable for the application.
In addition, it creates high compliance risks that can compromise the security and sensitive data of the organization.
With Zluri, the IT teams can monitor all the SaaS applications in the business processes. In this SaaS platform, you get an insight into the application. With the help of Zluri, you can assign applications to each user. You can view the application's owner, IT head, and finance head of the app.
With Zluri, you can implement role-based access control (RBAC). This can restrict the employees' permission to access the SaaS apps based on their organizational role. It will only allow the users to access for which their job demands.
Suppose an employee from the marketing department should not have access to the financial information in an application. With Zluri, you can restrict access to the finance section.
An organization must ensure that no employees have permission to access the data outside their roles. This will prevent the organization from data breaches and facilitate identity security, cyber security, etc.









.svg)



.svg)
.svg)
.svg)
.svg)

.svg)

.svg)

.svg)
















.webp)







.webp)
.webp)





.webp)