Struggling with PCI DSS compliance? Our expert-curated checklist simplifies the process, helping you avoid costly breaches and maintain customer trust. By following this checklist, you can ensure your systems are secure, stay compliant, and focus on other critical IT tasks with confidence.
The complexity and volume of the Payment Card Industry Data Security Standard (PCI DSS) requirements can lead to gaps in compliance, increasing the risk of data breaches and financial penalties. These challenges can create significant stress for IT managers, who must navigate the intricacies of the standard while maintaining day-to-day operations.
To address these concerns, having a clear and comprehensive PCI DSS compliance checklist is essential. Such a checklist can guide you through each requirement, ensuring nothing is overlooked. It helps streamline the compliance process, making it more manageable and less stressful.
This article provides a detailed PCI DSS compliance checklist designed to help you efficiently meet all necessary standards, protect sensitive data, and avoid potential pitfalls. By following this checklist, you can achieve and maintain compliance with confidence, safeguarding your organization from risks associated with non-compliance.
But before exploring the PCI DSS compliance checklist, let's know more about it.
What is PCI DSS Compliance?
PCI DSS is a set of security standards established to protect the integrity and confidentiality of credit card data. This framework is a collaborative effort of major credit card companies to thwart data breaches and unauthorized access to payment card information. The standards encompass a range of security measures, including network protection, data encryption, access controls, and regular system monitoring.
Example: Securing Online Payments through PCI DSS Compliance:
Consider an e-commerce platform that processes thousands of online transactions daily. To ensure PCI DSS compliance, your IT team implements encryption protocols to safeguard credit card transaction information during customer transactions. The organization maintains a secure network by regularly updating firewall configurations and conducting vulnerability assessments.
Access controls are enforced, allowing only authorized personnel to handle cardholder data. The system undergoes continuous monitoring, detecting and promptly addressing any potential security threats, as a crucial part of PCI compliance requirements. Regular security audits and testing ensure the effectiveness of the implemented measures, creating a robust defense against data breaches.
What Happens If You're Not PCI DSS Compliant?
As an IT manager, understanding the repercussions of non-compliance is essential for safeguarding your organization's reputation and financial well-being.
- Financial Implications: Failure to adhere to PCI DSS (Payment Card Industry Data Security Standard) can result in severe financial consequences. Non-compliance may lead to hefty fines imposed by regulatory bodies, impacting your bottom line.
Additionally, in the event of a data breach, the financial fallout can extend to legal fees, compensation for affected parties, and a tarnished brand image, which can devastate your organization. - Reputational Damage: Non-compliance with PCI standards can severely damage your company's reputation. A data breach resulting from lax security measures can lead to a loss of customer confidence, with long-lasting effects on brand perception.
- Legal Ramifications: If you are not PCI compliant, then it might expose your organization to legal consequences. Regulatory bodies have strict requirements to protect consumer data; failure to meet these standards can lead to legal action.
Proactively maintaining PCI compliance helps avoid legal troubles and demonstrates your commitment to upholding industry regulations. - Increased Vulnerability to Cyber Threats: A lack of PCI compliance opens the door to cyber threats. Hackers are constantly evolving their tactics to exploit vulnerabilities in payment systems. Non-compliance makes your organization an attractive target for data breaches, potentially compromising sensitive information.
- Limited Business Opportunities: Non-compliance with PCI compliance standards may hinder your organization's ability to engage in partnerships, limiting business opportunities. By prioritizing PCI compliance, you protect your organization and open doors to potential collaborations that require a secure and trustworthy business environment.
Now, let's take a look at the required PCI DSS compliance checklist.
12 PCI DSS Compliance Checklist
Ensuring PCI DSS compliance is a crucial responsibility to protect your organization's cardholder data from unauthorized access. To help you navigate this complex journey effectively, here is the PCI DSS compliance checklist for 2025:
1. Implement a robust firewall solution & ensure it is properly configured
To protect cardholder data, a strong firewall is needed. Firewalls control traffic flow in and out of networks, acting as defenders between your private network and the internet. This PCI DSS compliance checklist prevents potential hackers from gaining access.
But firewalls aren't limited to external network protection alone. They can also serve as an additional layer of defense within your network, encircling databases that hold crucial cardholder information. You establish an indispensable element of comprehensive network security parameters by diligently configuring and maintaining your network firewalls.
Remember, a well-implemented and meticulously maintained firewall is a formidable ally when it comes to safeguarding sensitive data. So, ensure you have one in place to fortify your defenses and keep your cardholder data secure from malicious actors.
2. Customize & strengthen settings beyond the vendor's default configuration
Many vendors provide devices like firewalls and routers with default passwords, usernames, and administration accounts. While these defaults may make installation easier, they are widely known among hacker communities and can be exploited to compromise your systems. Therefore, changing them before integrating the system into your network is imperative.
This PCI compliance requirement focuses on hardening your network and making it more challenging for hackers and threat actors to gain unauthorized access. You significantly enhance your network's security posture by adhering to this requirement.
To strengthen your network's security, it is vital to change default passwords in the following areas: operating systems, security software, application and system accounts, point-of-sale (POS) terminals, Simple Network Management Protocol (SNMP) community strings, Wireless Equivalent Privacy (WEP) keys, and Default Service Set Identifier (SSID) passwords.
Remember, the security of your network is only as strong as its weakest link. Implementing these changes ensures your systems are better protected against potential cyber threats and unauthorized access.
3. Prioritize the protection of cardholder data
Safeguarding cardholder data must be a top priority in information security. In the realm of data protection, adopting a layered defense approach is crucial. While hackers may successfully breach networks and gain access to credit card payments and databases, implementing robust encryption protocols for data at rest can render stolen information virtually unreadable.
Encrypting data on company servers adds an extra layer of protection. Even if attackers steal sensitive information, they will encounter significant challenges decrypting it. Encryption mitigates the risk of unauthorized use and safeguards cardholder information by transforming the data into an unintelligible format.
By encrypting cardholder data at rest, you can fortify the organization's data protection strategy, mitigate the risk of data breaches, and uphold compliance with industry standards. This demonstrates a commitment to safeguarding sensitive information, maintaining customer trust, and staying one step ahead of cyber threats.
4. Employ encryption for cardholder data-in-motion
Protecting sensitive information, such as cardholder data, is a top priority for any organization. As an IT manager, you understand the risks associated with data transmission over the public internet. That's why it's crucial to implement robust encryption measures to ensure data security in transit.
Data traveling from one location to another is particularly susceptible to theft, especially when it traverses the public internet. Cybercriminals are constantly looking for vulnerabilities to exploit, making it essential to fortify your organization's defenses.
Encrypting cardholder data renders it unreadable to anyone who intercepts it during transit. Whether the data moves between servers within your organization or is transmitted to a mobile application, encryption is a powerful safeguard against unauthorized access.
5. Regularly update and maintain antivirus software
By implementing and following secure practices, one of the PCI checklists, you can safeguard sensitive data, protect against malware, and minimize potential risks. Antivirus software plays a critical role in defending your systems against malware attacks. However, it is not sufficient to simply install basic antivirus software and assume your organization is protected.
To maximize effectiveness, ensure that your antivirus is constantly updated. New malware threats emerge regularly, and antivirus vendors release updates to combat them. You can enhance its ability to detect and neutralize the latest threats by keeping it up to date.
In addition to updating antivirus software, apply regular patches to address vulnerabilities in your systems and applications. Unpatched software can provide entry points for malware attacks. Establish a robust patch management process to ensure timely application of security updates.
Keeping your systems protected from malware and regularly patching vulnerabilities are essential steps toward maintaining a secure IT environment.
6. Establish and adhere to secure systems & application development practices
Following established best practices and industry standards is vital to achieve secure systems and software applications. This includes adopting secure coding practices, employing rigorous testing methodologies, and leveraging secure development frameworks. By implementing this PCI compliance checklist, you can create a robust foundation that minimizes the risk of exploitable weaknesses in their software and systems.
However, the journey to secure systems does not end after deployment. Continuous security maintenance is a critical aspect of maintaining a secure environment. As technology evolves, new vulnerabilities and threats require ongoing monitoring, patching, and updates.
Regular security assessments, security vulnerability scans, and penetration testing are essential to promptly identify and remediate potential weaknesses.
7. Enforce need-to-know policies to restrict access to cardholder data
The foundation of need-to-know basis policies lies in limiting access privileges to only those employees who require such access to perform their job responsibilities. Doing so can significantly reduce the likelihood of stolen passwords or unauthorized access, compromising the integrity and confidentiality of cardholder data.
To implement need-to-know policies effectively, consider the following best practices:
- Regular Access Reviews: Regularly reviews access logs and access privileges based on employees' roles and responsibilities to ensure alignment and minimize unauthorized access.
- Multi-Factor Authentication (MFA): Implement two-factor authentication to add an extra layer of security by requiring additional verification factors beyond passwords.
- Comprehensive Training: Educate employees about the importance of need-to-know policies, the risks of unauthorized cardholder data access to devices, access to network resources, and their individual responsibilities in maintaining data security through regular training sessions.
- Access Monitoring and Auditing: Deploy robust monitoring and auditing systems to track access activities and audit logs, detect anomalies, and promptly investigate potential security incidents.
By adhering to these best practices, you can effectively implement need-to-know policies, minimize security risks, and safeguard cardholder data within your organization. These proactive measures foster a culture of security, enhance data protection, and contribute to long-term organizational resilience against evolving cyber threats.
8. Implement strong authentication mechanisms for accessing all systems
By assigning each user a unique ID, your IT team gains the ability to track access attempts and quickly identify any unusual behavior. This level of visibility helps detect potential security breaches or unauthorized access more efficiently. With this information at hand, you can take prompt action to mitigate risks and prevent any potential data breaches or malicious activities.
Consider adopting multi-factor authentication (MFA) or sensitive authentication to strengthen your security measures further. MFA requires users to provide additional verification steps beyond just a username and password. This extra layer of security significantly reduces the likelihood of unauthorized access, even if login credentials are compromised.
Implementing MFA strengthens your security posture and provides peace of mind to your organization, employees, and customers. It demonstrates your commitment to protecting sensitive data and ensures compliance with industry regulations and standards.
9. Secure areas with physical access to critical keys
Securing cardholder data goes beyond network protection. Compliance mandates strict control over physical access to areas where cardholder information is stored physically and digitally. To ensure comprehensive security, it is crucial to implement measures that restrict and monitor entry into these sensitive spaces and protect the cardholder data environment.
One essential step is the installation of security cameras and other surveillance systems. These tools should be deployed to continuously monitor and record all individuals who access the areas containing cardholder data. Doing so will create a robust deterrent against unauthorized access and provide a means for retrospective investigation if any security incidents occur.
Physical access restrictions serve as an additional layer of defense, preventing unauthorized individuals from physically tampering with or stealing cardholder data. You should collaborate closely with facilities management and other relevant stakeholders to establish stringent access control mechanisms.
10. Maintain continuous monitoring of network access, systems, and cardholder data
Implementing continuous monitoring, being one of the best PCI DSS compliance checklists, offers several key benefits. Firstly, it enables proactive threat detection, allowing IT managers to stay one step ahead of potential attackers. Any suspicious activity or unauthorized access attempts can be identified promptly by monitoring access in real-time, enabling swift response and containment.
Secondly, continuous monitoring helps establish a baseline of normal network behavior. By constantly analyzing traffic patterns, the system can learn what constitutes typical network activity, thereby making it easier to identify anomalies that may indicate an ongoing security breach.
Moreover, automated systems provide the advantage of scalability. As your network grows, monitoring manually becomes increasingly challenging. However, automated tools can handle large volumes of data, ensuring that no potential threats go unnoticed amidst the vast amount of network traffic.
11. Conduct regular security testing & assessments of systems & processes
As an IT manager, you must understand that security plans are not one-time solutions but dynamic processes. As soon as a plan is deployed, it starts to degrade due to emerging threats, evolving technologies, and changing business requirements. As one of the PCI DSS compliance checklists, regular security tests keep you ahead of risks, ensuring systems are up-to-date and fortified against threats.
Comprehensive scans of network defenses are effective for testing security systems. They actively probe infrastructure and systems, identifying weaknesses and vulnerabilities. Regular internal vulnerability scans enable you to detect security gaps and take immediate action, reducing the chances of successful attacks and preserving digital asset integrity.
Engaging in third-party penetration testing is also valuable. It simulates real-world attacks, assessing the resilience of security measures. Collaboration with experienced professionals uncovers vulnerabilities and provides expert recommendations for system improvements. These tests offer valuable insights, enabling targeted enhancements and ensuring effective security measures.
Regular testing demonstrates proactive security commitment by IT managers. It establishes a continuous process loop to identify and address weaknesses promptly. This approach enhances overall security posture, meets compliance requirements, and builds stakeholder trust.
12. Develop and maintain comprehensive information security policies for all personnel
It's important to remember that security is not the sole responsibility of one person or team. Every individual within the organization plays a role in keeping networks and information secure. By establishing clear information security policies and providing regular training, you can ensure that everyone understands their responsibilities.
PCI compliance levels of your organization develop comprehensive information security policies that define roles and responsibilities. This ensures consistency across departments and levels of the organization, creating a unified front against security threats.
Regular security training is key to maintaining an effective information security framework. Educating employees about best practices, potential threats, and security protocols empowers them to contribute to the organization's overall security posture.
By prioritizing information security policies and training, you cultivate a culture of security within your organization. This proactive approach minimizes the risk of security incidents and protects sensitive data, reducing potential financial loss and reputational damage.
Adhering to industry standards like PCI DSS meets regulatory requirements and demonstrates your organization's commitment to security for stakeholders and customers.
Ensuring PCI DSS compliance can be a challenging and time-consuming process. With the numerous controls listed in the PCI DSS checklist, implementing and managing them all can become overwhelming while keeping up with your organization's growth. This is where Zluri, the ultimate tool designed to ease your PCI DSS compliance journey, can help.

Streamline Your PCI DSS Compliance Journey with Zluri
Due to an increase in SaaS adoption, managing access privileges becomes intricate, exposing businesses to security risks and compliance complexities. Zluri steps in as the solution, ensuring compliance through its access review platform. This robust system streamlines IT audits, enforces financial standards, and ensures adept control over user access.
A key feature of Zluri is its potent user access review capability. This feature simplifies the complex task of overseeing and assessing user permissions. By leveraging nine distinct discovery methods and integrating with over 300 applications, Zluri guarantees a comprehensive overview of your SaaS landscape.
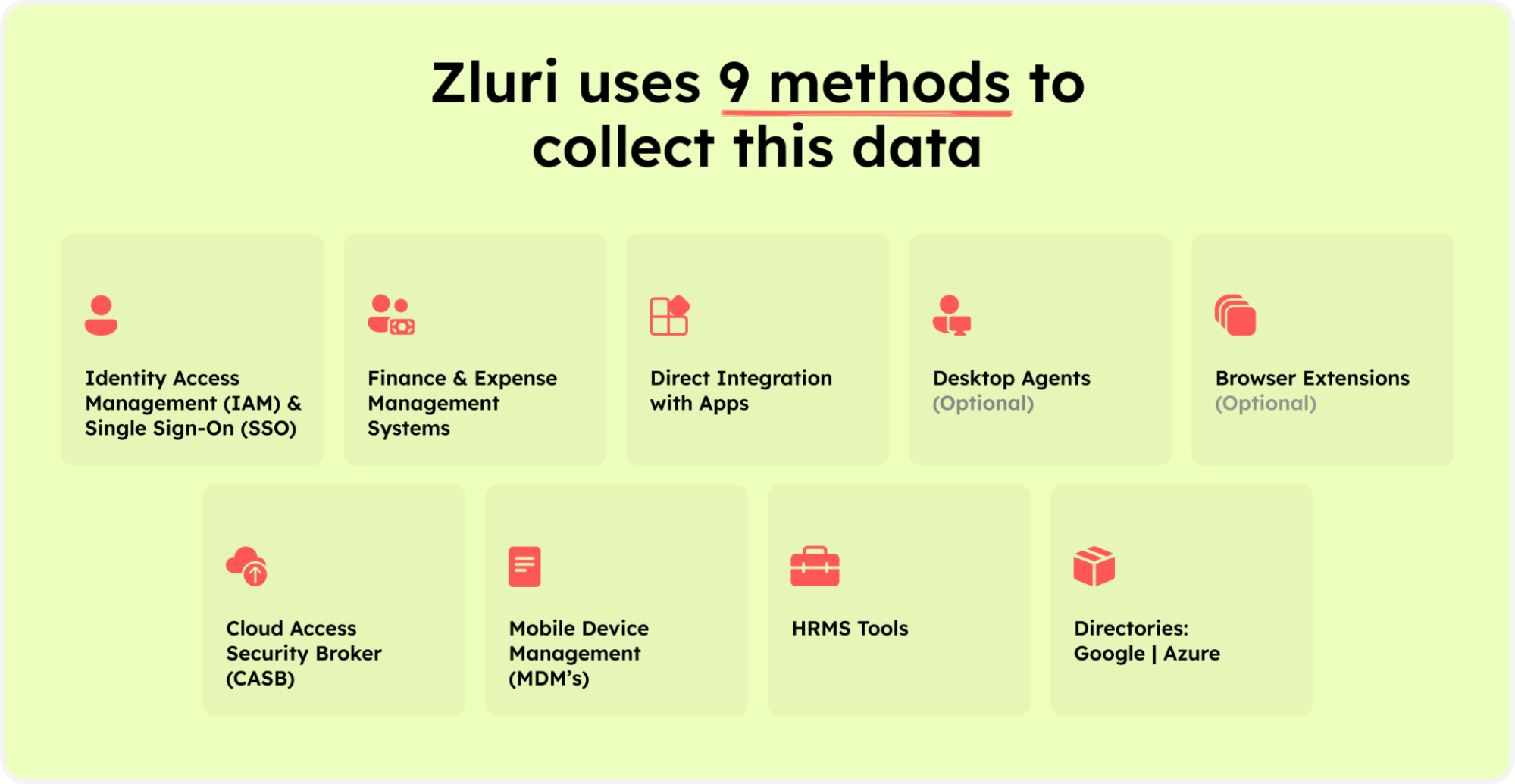
Zluri’s nine discovery methods
This centralized platform unveils all active SaaS applications, empowering your IT team with profound insights into your organizational SaaS ecosystem.
Ensuring compliance with standards like PCI DSS demands precise control over user access and strict security measures. Zluri's access review solution is pivotal. Its robust features offer comprehensive visibility across your SaaS landscape, allowing for efficient user access management and swift handling of access requests. This capability ensures that access rights are appropriate and aligned with organizational requirements.
In contexts where adherence to standards like PCI DSS is crucial, Zluri's access review serves as a powerful ally. Leveraging Zluri's functionalities provides teams with vital insights, simplifying the complexities of PCI DSS compliance seamlessly.
Unlock the Power of Unified Access with Zluri's Access Review
In today's data-driven landscape, ensuring PCI DSS compliance is paramount. Zluri's access review solution revolutionizes access management by offering a comprehensive suite of features that meet and exceed PCI DSS requirements.
Access Directory: Zluri introduces an innovative Access Directory, simplifying access privilege management. Compliant with PCI DSS, this feature consolidates user data from various sources like active directory and identity repositories. This unified approach offers a centralized view of user identities and access privileges, streamlining access rights management. For example, financial institutions benefit from Zluri's 360-degree view of access privileges across crucial applications, ensuring seamless PCI DSS compliance.
Unparalleled Admin Visibility: Zluri's unified access empowers administrators with unparalleled visibility. Meeting PCI DSS requirements for robust access controls, administrators swiftly identify access discrepancies or suspicious permissions. This proactive stance strengthens defenses against cyber threats and aligns with the principle of least privilege. For instance, e-commerce companies efficiently oversee user access privileges for payment processing systems, ensuring ongoing PCI DSS compliance.
Real-time Activity Monitoring and Alerts: Staying ahead of security risks is vital for PCI DSS compliance. Zluri's access review offers real-time user activity tracking and robust alert systems. This proactive approach meets PCI DSS requirements for continuous monitoring and swift incident response. Healthcare providers leverage Zluri to monitor user activity within electronic health records systems. Its alerting system promptly notifies unauthorized access attempts, allowing prompt responses to maintain PCI DSS compliance and safeguard sensitive patient information.
Automated Reviews: Streamline Compliance Efforts with Zluri's Advanced Automation for PCI DSS
Zluri's automated reviews redefine security standards, ensuring effortless PCI DSS compliance. Our solution goes beyond conventional measures, fortifying access controls, safeguarding sensitive data, and ensuring unmatched efficiency in meeting regulatory standards.
Access Rules: Tailored Privileges for Compliance
Zluri excels in meeting PCI DSS requirements by enforcing precise access rules. Instant reviews validate user access against predefined criteria, aligning privileges with specific job functions. This proactive approach significantly reduces unauthorized access to cardholder data, enhancing both security and compliance efforts.
For example, a payment processing company like American Express relies on Zluri to enforce access rules. Finance department employees access financial applications containing cardholder data while restricting access for other departments. This precision ensures PCI DSS compliance, safeguarding sensitive data.
Scheduled Certification: Up-to-date Access Rights
Zluri's scheduled certification automates reviews to ensure access rights evolve with your security policies. Simplifying the process maintains a consistent, compliant environment, reducing the risk of data breaches from outdated permissions.
Consider a healthcare provider using Zluri's scheduled certification to review user access to patient records regularly. Automation ensures access rights align with evolving security policies, ensuring proactive PCI DSS compliance.
Auto Remediation: Proactive Security Measures
Aligned with PCI DSS Requirement 12, Zluri's auto-remediation proactively handles security threats. Automated actions swiftly address risks, reducing vulnerability windows, preventing incidents, and optimizing security resources.
Imagine a financial institution using Zluri's auto-remediation to manage security risks proactively. Upon detecting unusual user behavior, Zluri automatically blocks suspicious users, enhancing security and PCI DSS compliance.
Experience 10X faster reviews and a 70% reduction in effort with Zluri's robust features, allowing your team to focus on growth and innovation. Empower your organization to strengthen security, comply with standards, and combat cyber threats effectively.
Book a demo now to streamline compliance efforts and ensure a secure IT environment with Zluri. Compliance isn't just a checkbox—it's a seamless journey towards a secure future.
FAQs
Who regulates PCI Compliance?
PCI Compliance is regulated by the Payment Card Industry Security Standards Council (PCI SSC), established in 2006 through collaboration among leading card brands like Visa, MasterCard, American Express, Discover Financial Services, and JCB International. The council's primary goal is to set, maintain, and advance the Payment Card Industry Data Security Standard (PCI DSS), ensuring global businesses adhere to robust security practices in payment card transactions.
How do you ensure PCI DSS compliance?
Ensuring PCI DSS Compliance:
- Strengthen Security Practices:
- Enforce robust password policies to enhance security and protect sensitive data.
- Keep software updated to mitigate potential vulnerabilities and utilize the latest security features and patches.
- Practice data minimization by storing only essential information, reducing exposure risks.
- Foster a Culture of Vigilance:
- Educate and train employees to recognize and avoid suspicious links, reducing the risk of phishing and malware attacks.
- Choose Certified Solutions:
- Opt for card readers and payment software validated by the PCI Security Standards Council, ensuring compliance with industry standards.
- Employee Empowerment:
- Educate staff about the critical importance of safeguarding cardholder data, fostering a proactive security culture and a unified defense against threats.









.svg)



.svg)
.svg)
.svg)
.svg)

.svg)

.svg)

.svg)
















.webp)







.webp)
.webp)





.webp)