Securely revoking access from the departing employees is one of the most pivotal tasks for the IT team to manage. Even one slightest oversight can pave the way for security breaches. This can further jeopardize data integrity.
However, by implementing an automated access review solution, your IT team can streamline the offboarding process. In this article, we’ll learn how automated user access reviews can benefit while offboarding.
Is your IT team still relying on manual methods to offboard employees? If so, as an IT manager, you need to understand that manually revoking access from departing employees and those no longer needing specific app access can bring forth various challenges. Such as, IT teams are unable to effectively maintain data security and adhere to compliance requirements.
Moreover, manually revoking access has limitations; for example, your IT team can only manage a finite number of employees' access manually. So if they revoke access from multiple employees at once, it could lead to oversights. Such oversights could result in departing employees retaining access, potentially sharing it with unauthorized parties, or utilizing that access to hack critical systems.
So the optimal solution to avoid such a scenario is to opt for an automated user access review system. By doing so, your team gains the ability to systematically review employees' access privileges, ensuring that those who no longer need to have access to apps, data, and systems have their permissions promptly revoked. This safeguards essential SaaS app data and ensures adherence to security compliance standards.
There are other pitfalls as well of manually reviewing user access such as risk of lingering access rights, this situation usually occurs when IT team fails to promptly revoke or modify access rights, it can result in former employees retaining access to critical systems, data, or networks.
So, now that you are familiar with the common risks associated with manual user access review, let's find out how automated user access review can help mitigate these risks/challenges.
Ways Automated User Access Reviews Helps Your IT Team Securely Offboard Employees?
Here’s how an automated user access review system can be a game-changing solution to manage and govern employee offboarding processes.
By Eliminating Manual Offboarding Process Through Automation
By implementing an automated IGA solution, your IT team can automate and streamline the entire offboarding process, making it more efficient and consistent. Also, it eliminates the need for manually tracing employees' access data and documenting/recording it, saving your IT team productive time.
To help you understand better how IGA solutions work, let me introduce you to Zluri. It is a modern autonomous, and automated IGA platform that enables your IT team to streamline the employee offboarding process with its automated user access review capabilities. Let’s see how it functions.
Firstly, when the employee(s) departs from the organization due to resignation, termination, or sabbatical, your IT team gets updated about the same with Zluri. How does it do that? It integrates with the HR system, so whenever certain changes occur in the employee lifecycle, Zluri promptly retrieves the updated employee data and presents it in a centralized dashboard. And your IT team cross-checks what all changes have taken place from that centralized dashboard.
Once your IT team obtains all the details, including which all employees need to be offboarded, their last working date, and more. Your IT team can proceed further with the revocation process.
So, to automate the offboarding process, your IT team needs to create an offboarding workflow that will automatically revoke access from the departing employee(s)with just a few clicks.
How to create an offboarding workflow in Zluri? Here’re the steps that your team needs to follow:
- Step 1: From Zluri's main interface, click on the workflow module and select the offboarding option from the drop-down list. Proceed by clicking on New Workflow.
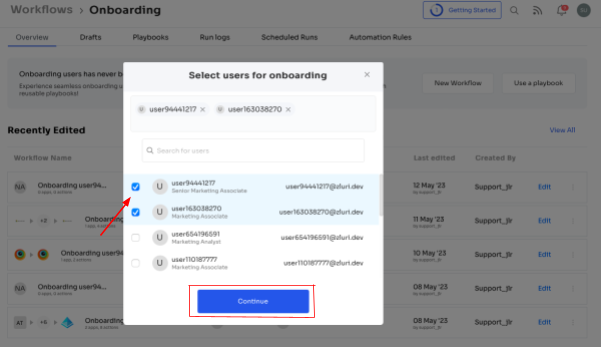
- Step 2: A popup labeled 'Select the user for offboarding' will appear. Select the employee(s) you want to offboard, or you can look for them in the 'search box. Click on continue after selecting the employee.
- Step 3: Your team will be able to view all the applications your employee can access. Now when you click on the app, Zluri will display some suggested actions under recommended actions. Select any of those or multiple actions, and then execute the required action for your chosen applications.
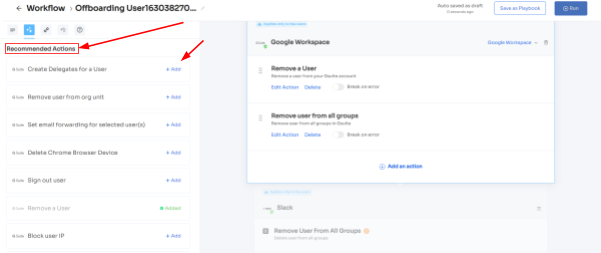
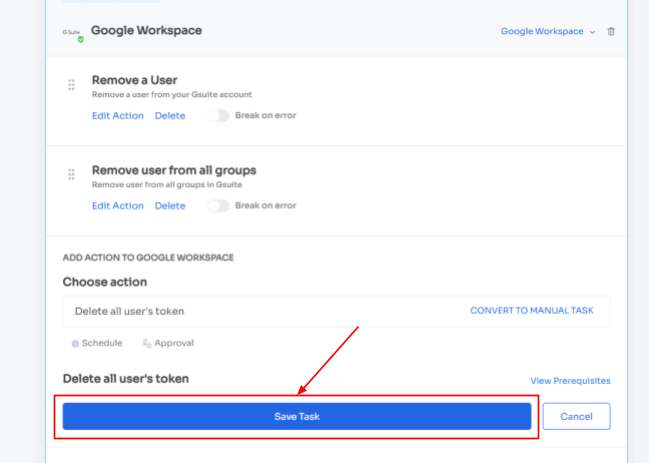
- Step 4: To add other actions, click Add an Action, fill in the required details, and proceed by clicking on Save Task; the actions will be saved.
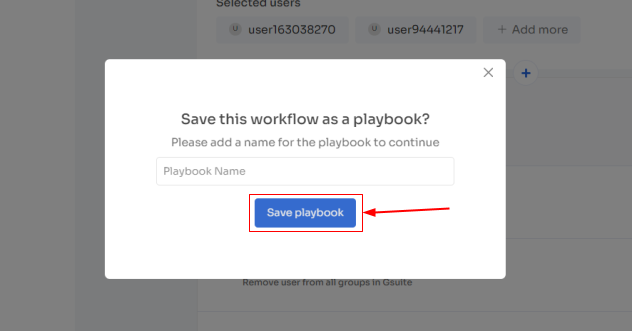
- Step 5: Save the workflow by clicking Save as Playbook. A dialogue box will appear, instructing to name the playbook.
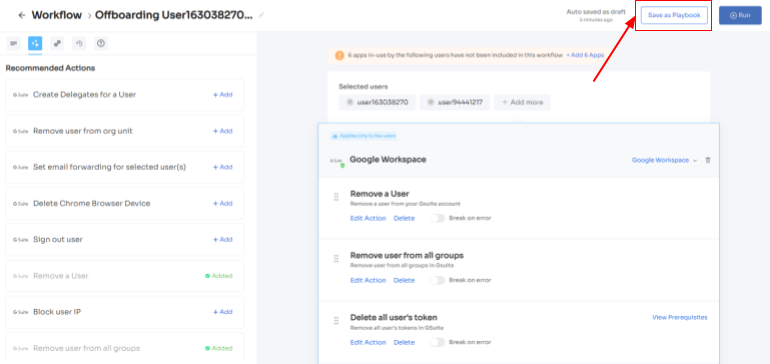
- Add a name, click Save Playbook, and the offboarding workflow is ready.
- For added efficiency, Zluri offers automated playbooks (i.e., collections of recommended applications for automation) that can be customized for different roles, departments, and designations. This feature streamlines the offboarding of employees, making it as easy as a few clicks to set up their access.Further, by eliminating the manual process, your IT team can minimize the risk of errors and ensure that access removal is carried out in a standardized manner.
Helping Your IT Team Conduct Access Reviews
Your IT team needs to conduct thorough scans across different systems, SaaS applications, and critical resources to ensure that no access privileges are overlooked while offboarding.
Let’s see how Zluri IGA helps your team conduct access review. After completion of the offboarding process, your team can conduct an access review with Zluri. This helps ensure that all the access has been revoked promptly from the departing employees and minimizes the risk of error or oversight that often occurs in manual review procedures.
So how does this access review work? Firstly, Zluri utilizes its unified access review feature that helps your IT team determine ex-employees had access to which all particular SaaS apps and data. To gain this insight, Zluri utilizes an access directory that centralizes all user access-related data in one centralized place.
With the valuable data points provided by the access directory, your IT team can thoroughly examine if ex-employees are left with any access. And accordingly, your team can take actions to restrict or suspend ex-employee access.
Furthermore, to ensure the departing employees do not breach in, Zluri's activity & alerts capabilities come as a great help. This feature provides your IT team with real-time alerts on any suspicious actions attempted by unauthorized users (ex-employees).
Apart from that, to streamline the reviewing process, Zluri automates the access review process, so that your IT team no longer has to go back and forth to gather and verify employees' access data. Not only that, by automating this process, you get 10 x better results than manual methods and save your IT team's efforts by 70%.
So how can you automate the access review process? All your IT team needs to do is create a certification, select the apps and users you want to review, and the rest of the reviewers will review and update you about the compilation via email. Here’s how you can create access certification in Zluri:
Step 1: From Zluri’s main interface, click on the ‘Access Certification’ module.
Step 2: Now select the option ‘create new certification.’ You have to assign a certification name and designate a responsive owner to oversee the review.
Step 3: Under Set Up Certification, choose the ‘Application’ option. Proceed further by selecting the desired application for which you want to conduct the review and choose a reviewer (generally, the primary reviewers are the app owners) accountable for reviewing access to that particular application.
After that, you need to select the fallback owner/reviewer, if the primary reviewer is unavailable, the fallback owner can review the user access (you can select anyone for the fallback reviewer, whom you think is responsible enough). Also, the reviewers will get notified through the mail that they will conduct a review.
Once you are done selecting the reviewers, you can click on Next.

Step 4: Select Users for Review, choose the departing employees whom you want to review for the selected application. Once you are done selecting the users click on next. You will be able to view all the information related to the users. Then you need to specify the criteria or parameters such as user department, job title, usage, and more. Now click on update and then click on next.
Note: Select those relevant data points only that you wish your reviewers to see while reviewing the access. By filtering the criteria appropriately, you enable your reviewers to make swift and well-informed decisions, streamlining the review process and ensuring efficiency.


Step 5: Now the Configure Action page will appear, basically, here you have to choose actions. These actions will run post the review. Since we are conducting a review for departing employees your IT team needs to choose: deprovisioning playbook action.
If the reviewers find any access permission is left with departing employees, they simply state that they want to suspend the access permission, and Zluri will automatically revoke access from the user. This feature of Zluri is known as an auto-remediation feature.
Step 6: Additionally, you can even schedule the actions by setting up the start date and within what time span you want the review to be completed.

Step 7: Lastly you can keep track of the automated access review process by clicking on the ‘Review Status’ and view whether the review is still pending, modified, declined, or approved.
Also, you can add multiple applications and follow the same process for each selected application.
Zluri also provides the owner access to a snapshot view of the entire certification process status. Also, they can get an overview of the pending reviews and monitor the status of each app’s review, including their assigned reviewers and their completion status.
You can even send reviewers reminders who are yet to complete their reviews.
Further, to streamline the process for reviewers, Zluri provides reviewers with all the user access data in a single screen, i.e. reviewer screen. For the same screen, reviewers can approve, modify, and decline access by verifying the data, and also they have to add relevant comments on the same.
Now, you will be able to view the entire status of the review process on the chart and once the process is completed and the owner (assigned reviewer of the certification process) is fine with the review. You can click on conclude, and it will straight away send the reports to the reviewers' email.
- Documenting The Entire Access Removal Process & Generating Curated Reports Your IT team needs to have evidence that the entire access removal process is followed according to the standardized protocol. So what Zluri does is, it provides audit logs and reports, documenting the access removal process. These records serve as evidence of compliance with security policies and regulations, facilitating easy demonstration of the steps taken to manage user access during employee offboarding.Further, these reports help, in case of audits or investigations. Your IT/GRC team can easily showcase the systematic and security measures taken to manage user access throughout the employee offboarding phase. For example, if any auto-remediation has taken place, Zluri will record the same in its system. So, that your IT team can further cross-check if any error/mistakes occur during the departing employee access reviewing process So in short, Zluri's IGA automated access review empowers your IT team to efficiently manage the complex offboarding process, enhance security, and uphold regulatory compliance, all while minimizing the burden of manual tasks and potential errors.So, don't wait any longer! Book a demo now and see how Zluri’s IGA can help your IT streamline the offboarding process.









.svg)



.svg)
.svg)
.svg)
.svg)

.svg)

.svg)

.svg)
















.webp)







.webp)
.webp)





.webp)