As an IT manager, safeguarding digital assets against potential threats and vulnerabilities is crucial. This is where identity governance and administration (IGA) stands out. IGA acts as the compass that navigates the complex network of digital identities within an organization. It encompasses the processes and technologies that ensure the right individuals have the appropriate access to systems, applications, and data.
Cybersecurity risks are rising alarmingly and no longer happen from external sources alone. A study points out that insider threats (intentional and unintentional) are the reason for 60% of security incidents. This forces the IT and security teams to rethink how they manage user access and identities in their organization so that they leave no room open for any security breaches and vulnerabilities.
Every day, the IT landscape becomes more complex with further applications and new users added to the network. Any mistake with access provisioning or delay with deprovisioning can further increase insider risk possibilities. It just doesn’t stop here. Even a minor security breach can cause data loss, system shutdown, loss of revenue and reputation, and other serious issues.
To prevent this, IT teams should have control over who has access to what applications and data and govern this process so that no one has access to any resource or data they are not supposed to access. This is basically the identity administration part.
Along with this, there is another challenge that IT and security teams must consider: getting visibility into what happens once the users log into company systems and ensuring policies protect sensitive information about their customers, partners, and employees. Furthermore, if you have a watchdog to monitor this, then it becomes much easier to report or audit digital assets. This part comes under identity governance.
This was just a glimpse of identity governance and administration. There is more to explore. So, let’s first start by understanding what identity governance and administration mean.
What Is Identity Governance And Administration?
Identity governance is about visibility, segregation of duties, attestation (evidence in the form of reports for auditing purposes), role management, analytics, and reporting. Meanwhile, identity administration is associated with account administration, credentials administration, user and device provisioning, and managing entitlements.
Identity governance and administration is the process of managing user identities to IT tools, resources, and solutions to keep identity-related threats away from your digital assets. In simple terms, identity access governance means ensuring the right level of access to the right users for the right applications at the right time. You achieve this by associating policies and controls with user privileges to different applications and restricting them from unauthorized access.
Key Components Of Identity Governance
Below, we have listed down the key components of identity governance and provided a brief explanation of the same:
- Access Visibility
It is about understanding user identities, their associated permissions, and their activities within an organization's systems and applications. It involves gaining insights into who has access to what resources, how access rights are granted, and how they are being used. Enhanced visibility allows the IT team to manage user access effectively and detect any unauthorized or suspicious activities, helping to prevent security breaches and mitigate risks.
- Policies
Policies in IGA are a set of rules/ guidelines (such as access control policies, SoD policies, role-based access control policies, compliance policies, and more) that are enforced to manage identities/users, control access to SaaS apps data, and strengthen the overall organization's security posture. By implementing IGA policies, your IT team can securely ensure proper access is granted, modified, and revoked from the users, reducing the risk of authorized attempts or any potential security breaches. It also helps maintain data privacy and governance and meets compliance standards.
- Segregation Of Duties
It aims to prevent fraud and errors by separating critical tasks or permissions among different individuals or roles. By enforcing SoD, your IT team can balance maintaining accountability, reduce the risk of unauthorized actions, and enhance the integrity of critical processes.
- Certification
It involves reviewing and validating user access rights and permissions regularly, ensuring user access aligns with business requirements, security policies, and regulatory compliance. Further, the reviewers (manager/app owner/ maker or creator) verify and approve user access requests, identify and remove unnecessary access privileges, and confirm that access remains appropriate over time.
- Role-Based Access Management
It focuses on assigning roles and responsibilities to users based on their job functions and organizational needs.
- Audit Reporting
All the identity and access-related data and activities are documented in the reports, which further helps your IT team track user access patterns, monitor compliance status, understand user behavior (such as login/logout time), what level of permissions the users have, and does it align with their job, and more. By generating reports, your IT team can easily detect any potential security threats and take immediate action to mitigate them. Also, these documents are much needed during audits, so IT teams need to generate regular reports to keep all data up-to-date and audit-ready for the future.
Key Components Of Identity Administration
Below, we have listed down the key components of identity administration and provided a brief explanation of the same:
- Account Administration
Managing user accounts, including creating, modifying, and deleting accounts. This component ensures user accounts are properly set up, maintained, and deactivated when necessary.
- Credentials Administration
It is a security practice that combines policies, strategies, and technologies to safeguard login credentials, as these credentials are used to identify and authenticate users who require access to system resources.
- User And Device Provisioning
This component involves automating the process of granting appropriate access privileges to users and their devices based on their roles and responsibilities. It also ensures that access is promptly revoked when users leave the organization or change roles.
- Managing entitlements
This component is particularly about what users can do within an application they can access, i.e., privileges and entitlements. With custom rules, IT admins can control this and allow or restrict permissions to different users.
Now, let’s find out why identity governance and administration is important.
What Is The Importance Of Identity Governance and Administration?
Earlier, the security perimeter (number of users accessing apps and data) used to be small and straightforward to govern and maintain compliance with.

However, with the emergence of numerous applications and a vast digital landscape, the new perimeter has become huge, chaotic, and complex to govern in terms of who has access to what.

For example, traditional approaches to security often stop at authentication, where access is granted to applications one time after verifying, without keeping track of what happens afterward. While this approach may work in small-scale environments, it becomes inadequate for growing or larger organizations. The subsequent access management becomes invisible to the IT team, making it difficult to remain secure and compliant.
While IAM (Identity and Access Management) primarily focuses on identifying individuals and managing their access to applications at a high level, IGA (Identity Governance and Administration) focuses explicitly on governing the access rights of users within each application. This includes assessing whether a user should have access to an application in the first place and what level of permissions they should possess.
This is where an identity governance and administration solution becomes crucial. It enables organizations to govern and manage user access, including determining what resources they have access to, the duration of their access, and when access should be modified or revoked. IGA ensures that access governance is enforced effectively within the organization.
Furthermore, by implementing effective identity governance and administration, your IT team can find out answers to common questions:
- Whether the user is actively using the application (by detecting login and logout time)
- How long the users have not used the application
- Whether the user has unnecessary access permission to any SaaS app and data
- Which access needs to be modified or revoked
By keeping track of and recording all the above information, the IT and security team can seamlessly govern access, reducing the risk of unauthorized access attempts, over-provisioning, or other security breaches.
Apart from that, identity governance and administration also helps mitigate a few other challenges. So, let's have a look at those challenges in detail.
2 Key Challenges Encountered By IT Teams In The Absence Of A Modern IGA Solution
Given below are two core challenges faced by the IT team in the absence of an identity governance and administration solution:
1. Access Gaps
In today's access system, a significant challenge arises from an existing gap that needs to be addressed. You must be wondering how the access gap occurs. Users access different types of applications; these applications are categorized under IT-managed apps and team-managed apps.
While IT-managed applications don't pose that much of a challenge as they can be centrally managed, the same cannot be said for the team or individually managed apps, which are owned by external parties and may have been acquired on an ad hoc basis.
The focus on traditional security solutions is more on authentication, not on what happens on a regular basis once a user is authenticated.

IT teams face difficulty managing access to team-managed apps and lack visibility into who has access to these applications and whether the granted access rights are appropriate.
Note: Generally, identity governance and administration solutions do not focus on shadow IT; they emphasize managing access to team-managed and IT-managed applications, as these are the already detected apps. So, only these apps are within the scope of governance.
So, to mitigate these challenges, you can consider implementing an IGA.
2. Being Secure And Staying In Compliance
One of the significant problems is that your IT team struggles to govern and control access rights, leading to security and compliance risks. Without proper governance, it becomes difficult to determine who has access to what resources, potentially resulting in unauthorized permissions. For example, a user might have edit access when they should only have view access to your Salesforce account, posing security and compliance risks.
This challenge occurs because IT teams often resort to manual processes, such as requesting user lists from various app owners, gathering information on access, roles, and licenses, and maintaining all this data in spreadsheets. However, this approach is neither efficient nor scalable.

As organizations grow, with hundreds or thousands of employees and numerous applications, the challenge of access sprawl emerges. Ensuring security policies and control, such as segregation of duties (SOD) or least privilege access, becomes essential to continue conducting business. This is because if you are non-complaint with the required compliance standards, you cannot operate within certain geographic or industries.
Moreover, governance is an ongoing process; periodic reviews (every 3 or 6 months) are crucial to align with IT team-defined governance policies. Without proper monitoring and control of access, IT teams may hit an invisible wall, losing complete control over their access environment.
However, by implementing identity governance and administration, your IT team can gain the ability to effectively manage access, monitor compliance, and ensure data security, providing the necessary control and oversight over their systems and applications.
After going through its importance, you might consider opting for an identity governance and administration tool. But before opting for one, you also need to be aware of its benefits. So, let’s explore the benefits offered by identity governance and administration solutions.
What Are The Benefits Offered By Modern IGA Solutions?
Below are the advantages of modern IGA solutions that help your IT team seamlessly control and govern access.
- Helps In Staying Compliant
Modern IGAs' intensive and detailed reporting helps the security team check if compliance is met at any given time. They can review on their own, know which resources users access at any time, and suggest better measures for improved security and fix leaks in the current system.
With well-structured roles and policies and precise reporting of user access logs, the IT and security teams can bolster the organization's compliance posture together and prevent chances for any security violations.
Besides, companies must adhere to many stringent regulations and data protection measures, like GDPR, HIPAA, SOX, etc. A holistic view of identity management across IT resources combined with the right level of access control can help the security team report the status better and be prepared for audits anytime without sweating.
Additionally, Modern IGA solutions provide detailed audit trails and reporting capabilities, allowing organizations to track and document user access activities. This helps in demonstrating compliance during audits and investigations. Also, it helps ensure that users have the appropriate access based on their roles and responsibilities, minimizing the risk of non-compliance.
- Strengthen the Organization's Security Posture
Apart from helping stay compliant, modern identity governance and administration solutions also enhance the security posture of organizations. How does it do that? With modern IGA solutions, your IT team implements fine-grained access control, ensuring only authorized users can access critical SaaS apps, data, and systems. By doing so, your IT team can prevent unauthorized access attempts and minimize the risk of data breaches.
Furthermore, it enables your team to streamline the user lifecycle management by promptly and securely granting, modifying, and revoking access privileges upon onboarding, mid-lifecycle transition, and offboarding. This helps reduce over-provisioning, eliminate inactive or orphaned accounts, and revoke all access without missing any from former employees.
Modern IGA solutions also give your IT team greater visibility into user access activities, allowing them to detect any suspicious or anomalous behavior/activity at the early stage to take immediate action and mitigate security threats.
- Improves Productivity Through Automation
Modern IGA solutions enhance security and compliance and boost organizational productivity. By simplifying access management processes and providing a seamless user experience, modern IGA solutions contribute to increased efficiency and productivity.
It automates the provisioning and deprovisioning of user access, ensuring that users have the necessary access when required and removing access promptly upon role changes or departures. This eliminates manual administrative tasks, saving time and improving productivity.
Also, these solutions often include self-service capabilities, allowing users to request access to resources without unnecessary delays. This reduces dependency on IT teams and eliminates the waiting period for access approval. Also,
Apart from that, Modern identity governance & administration solutions provide user-friendly interfaces and workflows, making it easier for your IT team to monitor and manage employees' access rights from a centralized dashboard. This reduces confusion and increases efficiency, enabling them to focus on their core tasks.
This is how modern IGA solutions can be beneficial for your IT team. But now, which identity governance and administration solution to opt for? Well, multiple platforms in the market offer an IGA solution, but the one that stands out is Zluri because of its unique capabilities. So, let's learn in detail how Zluri's IGA can be a revolutionizing solution for your organization.
How Do You Know It's the Right Time To Implement An IGA Solution?
It starts with identifying the need for a comprehensive program to manage the security and identity needs of the organization. Identity governance and administration is a perfect solution for you if:
- You have identified many mishaps around assigning privileges to IT resources and users complaining about not having access to required resources or users being left with more permissions than needed.
- Your team spends more time on administrative and management tasks of the users' lifecycle, and it always looks like they are understaffed or inefficient.
- You cannot make it easy for your users to have instant access to the right applications and enforce strong authentication policies. There are no frictionless options available for your users to access all applications and resources together in a simplified way.
- You are unable to report anytime to other teams or auditing groups about how access requests, compliance status, user activity logs, and more.
These are the cases where an identity governance & administration solution comes to help. Though multiple platforms in the market offer an IGA solution, the one that stands out is Zluri because of its unique capabilities. Let's learn in detail how Zluri's identity governance and administration can be a game-changing solution for your organization.
Zluri: An Autonomous & Automated IGA Platform
In the era where SaaS app data visibility is crucial to streamline identity governance and administration, many tools tend to overlook this crucial aspect and prioritize user data. However, Zluri’s IGA stands out by taking a different approach, placing more emphasis on SaaS app data and their relationship with user access. This approach not only greatly enhances the efficiency of the IGA process but also presents the most effective solution that IT managers should adopt.

But why only Zluri? Zluri began as a SaaS management solution, collecting extensive data about application usage. Recognizing the limitations of traditional IGA approaches that predominantly focus on user data, Zluri's IGA takes a different path by providing granular insights into specific application features usage, login/logout time, identifying unused applications, and more that impact security and compliance.
However, this is just the beginning; Zluri's IGA goes beyond expectations with its array of exquisite features designed to help your IT team effectively manage the process. So, let's have a closer look at its capabilities one by one to help you understand it better.
- Allows Your IT Team To Unveil User Access Data With Data Discovery Engine
Zluri helps your IT team to analyze and discover all the SaaS app and users related data seamlessly with its 9 discovery methods, i.e., MDMs, IDPs & SSO, direct integration with apps, finance & expense management systems, CASBs, HRMS, directories, desktop agents (optional), and browser extension (optional). With the help of these methods, your team can easily identity who has access to which applications, which are active users, what permission is granted to them, whether the employee accessing the apps falls under critical users, and more.
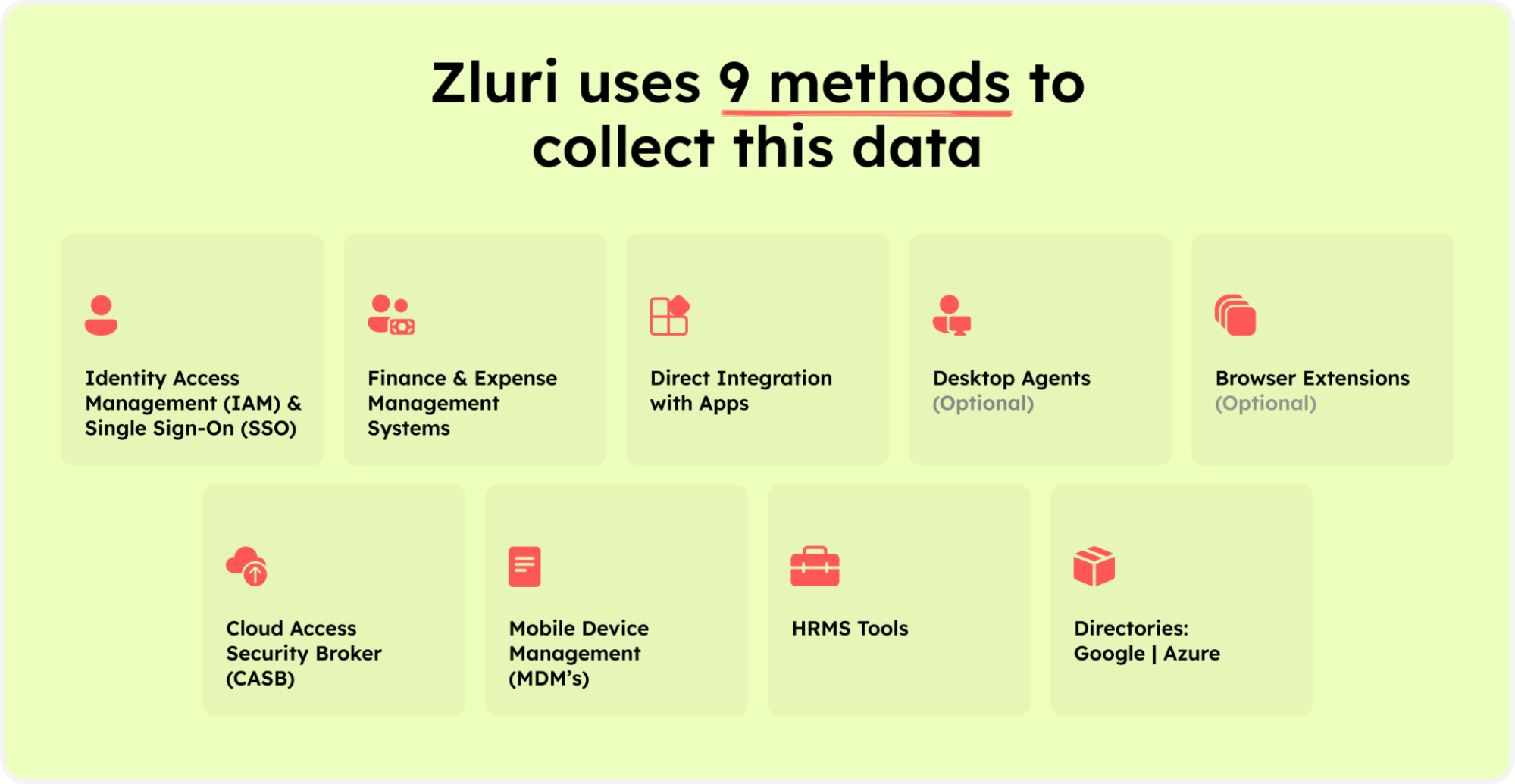
Zluri’s nine discovery methods
Furthermore, it also automates the identification of managed, unmanaged, and shadow IT apps. This automation eliminates the manual workload of categorizing SaaS apps and recording user access data, leading to substantial time and resource savings.
In addition, with Zluri, your IT team can simplify access management, ensuring that the right employees have the appropriate permissions for service accounts. By doing so, it becomes easier for your IT team to govern and control the access permissions and maintain a secure access environment.
How does it make it all possible? It offers advanced capabilities such as user lifecycle management, access request management, access certification, and more. Let’s learn more about it in detail.
They can easily determine which user has access to which particular applications, their login/logout time, whether the user status is active or inactive, which department the user belongs to, the level of access permissions (e.g., read, edit, or delete) they are holding, and more.
Furthermore, with the help of these fine data points, your IT team can easily understand the access patterns/user behavior and ensure that only the authorized user accesses the organization's sensitive SaaS app data. By doing so, your IT team can maintain a well-governed and secure environment.
Not only that, it also automates the process of identification of managed, unmanaged, and shadow IT apps. This automation eliminates the need for manual efforts in categorizing SaaS apps and documenting user access information, significantly saving time and resources.
- Enables Your IT Team To Ensure User Access Aligns With Their Role Throughout Their Tenure
Zluri's automation engine features automate repetitive access management tasks, such as provisioning, de-provisioning, access modification, request management, etc. Let's find out how it works.
- Securely Grant And Revoke Access Upon Onboarding/Offboarding
With Zluri, your IT team no longer has to invest their productive time in tedious manual processes and the risks associated with overlooked permissions. Zluri is here to automate everything, freeing up your IT team from the repetitive task of managing access permissions. With Zluri, you no longer have to waste time on manual onboarding and offboarding. Instead, you can automate these processes effortlessly.
How does Zluri do it? Well, your IT team can create and customize workflows for onboarding and offboarding. These workflows allow them to securely grant access to SaaS apps and data to multiple new employees simultaneously with just a few clicks. They can assign access based on new hires' job roles, positions, and departments, ensuring employees have access to all the required apps and data from day one.
And when it's time for an employee to depart from your organization, access can be promptly revoked. This makes your team more efficient, boosts productivity, and maintains a secure environment for user identities and SaaS app data.
- Promotes Ticketless Access Request Management: Enabling Your Employees To Quickly Gain Access To Required Apps
Now comes a critical phase where the risk of access mismanagement arises. We know how access needs to keep on changing. It can be because of changes in role, department, or position of employees, or they may simply need access to certain apps for specific tasks.
So, the IT team must keep a tab on all these changes and assign employees the right access to new or required apps. However, manual approving access can take up to a day. Zluri introduces ticketless access request management to address this concern, automating the access approval process and saving your IT team and employees productive time. Let's see how Zluri's ticketless access approval process works.
Zluri offers an Employee App Store (EAS), a self-serve model that offers a curated collection of IT-approved and verified SaaS applications. This app store is designed to provide employees with the flexibility to choose from the EAS, granting them instant access to their preferred applications without waiting for days.

Employees can raise access requests, and approvers can review and grant or deny access based on defined policies. This ensures that access privileges are granted in a controlled and auditable manner.
But how will your team come to know about changes in employee roles? Zluri offers a seamless solution for keeping your team informed about changes in employee roles. By integrating with your organization's HR system, Zluri automatically retrieves updated employee data and presents it on a centralized dashboard. This easily accessible information helps IT admins verify employee details efficiently before managing access privileges.

Whether granting or removing access, your team can ensure that access aligns with employees' current roles and responsibilities, enhancing security and maintaining a well-managed access environment.
Furthermore, your team need not worry about how to monitor these processes because, with Zluri, nearly everything is possible; your IT team can get a 360-degree view in a centralized dashboard with the help of its monitoring capabilities, which employee has been granted access to which applications, the level of permission assigned, which access are recently revoked, and more.
Moreover, by gaining such visibility, your IT team can detect suspicious user activities, like unauthorized access attempts, and take immediate action or implement security measures to safeguard sensitive SaaS app data from breaches or cyberattacks.
- Helps Maintain Well Governed Access Environment With It’s Access Review Capabilities
Most organizations highly emphasize data security and compliance, and Zluri understands the significance of these. That's why Zluri’s identity governance and administration makes it easier for your IT team to ensure every employee can access the organization's SaaS app data and maintain data security.
It conducts periodic access reviews to ensure access rights align with employees' roles and responsibilities and prevent unauthorized access by evaluating access patterns and user behavior. Also, with Zluri’s IGA, your IT can ensure all the compliance requirements are met and become ready for upcoming audits.
Not only that, Zluri’s IGA takes it a step further by offering unique capabilities to help your IT streamline the entire access review. So, let's understand in detail how Zluri's access review capabilities function.
Key Access Review Capabilities of Zluri
Given below are the key capabilities of Zluri’s access review that enable your IT team to streamline the access review process effectively and efficiently:
- Review Automation
With Zluri, you can automate the entire review process, enabling your IT admin to make the access review process 10x faster and reduce efforts by 70%. It allows your IT team to evaluate user access automatically, eliminating the need for manual review tasks.
- Auto Remediation
Zluri simplifies access remediation by automatically revoking access based on predefined conditions. When criteria are met, such as expired user accounts or policy violations, your IT team can immediately take action and revoke access.
Another example is an employee with administrative-level access to a specific application, although their job role does not necessitate such elevated permissions. Ideally, he should only have user-level access to the application. To tackle this situation seamlessly, Zluri automatically modifies the employee's access permissions, downgrading them to the appropriate user-level access, aligning precisely with their job requirements.
Doing so minimizes the risk of unauthorized access and strengthens your overall security posture.
- Auto-Generated Reports
With the help of these features, your team no longer has to spend time manually generating reports. It gathers the app access-related data and automatically generates reports such as access patterns, which users are no longer actively using a particular application, login/logout attempts, and unauthorized access attempts. It provides your IT team with up-to-date insights and analytics.
Furthermore, by delivering reports directly to your inbox, Zluri ensures your team stays informed and can seamlessly track access review outcomes.

- Recurring Certification
Through automated scheduling, your IT team can set up regular access reviews (after every 3-6 months). This ensures access permissions are continuously assessed and aligned with users' roles and responsibilities and standard access policies.
- Anomaly Detection
Zluri utilizes advanced AI-driven anomaly detection to identify risky access patterns and potential misconfigurations that may go unnoticed by human reviewers. Analyzing access data and user behavior enables your IT team to detect anomalies that indicate security threats or compliance issues.
This proactive detection strengthens your system's security and allows your team to take action to mitigate risks.
- Certification Templates
Zluri provides pre-built certification templates that simplify the review process across. Your IT team can also customize the templates to align with specific requirements.
- Continuous Reviews
Zluri ensures that access permissions are regularly assessed through continuous reviews. This ongoing process guarantees access remains up-to-date and aligned with access transitions/modifications. By continuously monitoring access and making adjustments as necessary, your IT team can maintain a secure and compliant access environment.
- AI Compliance
Zluri provides real-time notifications, keeping your team informed of compliance-related activities and changes. By adhering to regulatory standards and automating compliance checks, Zluri helps you meet all the compliance requirements and simplifies audit processes.
Let's see how your IT team can automate the access review process with Zluri.
Step 1: From Zluri's main interface, click on the 'Access Certification' module.
Step 2: Now select the option 'create new certification.' You have to assign a certification name and designate a responsive owner to oversee the review.
Step 3: Under Set Up Certification, choose the 'Application' option. Proceed further by selecting the desired application for which you want to conduct the review and choose a reviewer (generally, the primary reviewers are the app owners) accountable for reviewing access to that particular application.
After that, you need to select the fallback owner/reviewer; if the primary reviewer is unavailable, the fallback owner can review the user access (you can select anyone for the fallback reviewer whom you think is responsible enough). Also, the reviewers will get notified through the mail that they will conduct a review.

Once you are done selecting the reviewers, you can click on Next.
Step 4: Select Users for Review; choose the users you want to review for the selected application. Once you are done selecting the users, click on next. You will be able to view all the information related to the users. Then, you need to specify the criteria or parameters such as user department, job title, usage, and more. Now click on update and then click on next.
Note: Select only relevant data points you wish your reviewers to see while reviewing the access. By filtering the criteria appropriately, you enable your reviewers to make swift and well-informed decisions, streamlining the review process and ensuring efficiency.
Step 5: Now, the Configure Action page will appear; basically, you have to choose actions here. These actions will run after the review.
There are three actions:
Approved- once reviewers approve the user access, Zluri won't run any action, and the users can continue with their same access without any interruption.
Rejected- when the reviewer declines or doesn't approve the user access, you have to run a deprovisioning playbook to revoke that application's access from the user. If the user has access to critical apps, then you can request the assigned reviewer to manually deprovision the user access, or else Zluri's identity governance and administration will auto-remediate if it's not critical access.
Modify- In this last case, you again need to create a playbook to modify the user access. However, you need to state whether the access permission needs to be upgraded or degraded.
Step 6: Additionally, you can even schedule the actions by setting up the start date and within what time span you want the review to be completed.
Step 7: Lastly, you can keep track of the automated access review process by clicking on the 'Review Status' and view whether the review is still pending, modified, declined, or approved.
Also, you can add multiple applications and follow the same process for each selected application.
Zluri's IGA also gives the owner a snapshot view of the entire certification process status. Also, they can get an overview of the pending reviews and monitor the status of each app's review status, including their assigned reviewers and completion status.
You can even send reviewers reminders who are yet to complete their reviews.
Further, to streamline the reviewer process, Zluri's IGA provides reviewers with all the user access data in a single screen, i.e., the reviewer screen. For the same screen, reviewers can approve, modify, and decline access by verifying the data, and they also have to add relevant comments on the same.
Now, you will be able to view the entire status of the review process on the chart and once the process is completed and the owner (assigned reviewer of the certification process) is fine with the review. You can click on conclude, and it will send the reports straight away to the reviewers' email.
So, don't wait any longer! Book a demo now and see how Zluri's identity governance and administration can help your IT team effortlessly manage access.
IGA: Your Ultimate Solution To Manage, Control, & Govern Your Access
In this guide, we’ve provided you with a comprehensive overview of identity governance & administration. We explored the fundamental concepts, key components, and the evolving landscape of identity governance and administration.
These insights will help you understand how IGA helps in enhancing cybersecurity, access management, policy enforcement, and compliance. That way, you will be encouraged to opt for an IGA solution and implement strategies to protect digital identities and maintain a well-governed access environment.
FAQs
How does a modern Identity Governance and Administration (IGA) solution work?
IGA establishes rules and policies for managing, controlling, and governing user access. It automates access management tasks seamlessly, reducing the burden on your IT team and minimizing errors. Furthermore, it conducts regular reviews to ensure security and compliance, allowing proactive adjustments to evolving access needs.
What Is The Difference Between IAM and IGA?
IAM emphasizes providing access rights, whereas IGA broadens its scope by addressing vital identity governance elements like role-based access control, segregation of duties, and policy enforcement.









.svg)



.svg)
.svg)
.svg)
.svg)

.svg)

.svg)

.svg)
















.webp)







.webp)
.webp)





.webp)