Your company announced it's pursuing SOC 2 certification.
The auditor's first question: "Show me evidence of access reviews for the past 12 months."
You open your folders. You have:
- Spreadsheets from Q1 and Q3 (Q2 is missing)
- Email threads where managers said "looks good"
- A few Jira tickets marked "In Progress" from six months ago
- No formal signed attestations
- No proof that violations were actually remediated
The auditor takes notes. You can see this isn't going well.
This scenario plays out at organizations that run manual access reviews—they do the work, spend the time, involve the people, but when the audit happens, they can't prove it.
Proof matters. Because auditors aren't just checking that you tried. They're checking that your access reviews actually made you more secure.
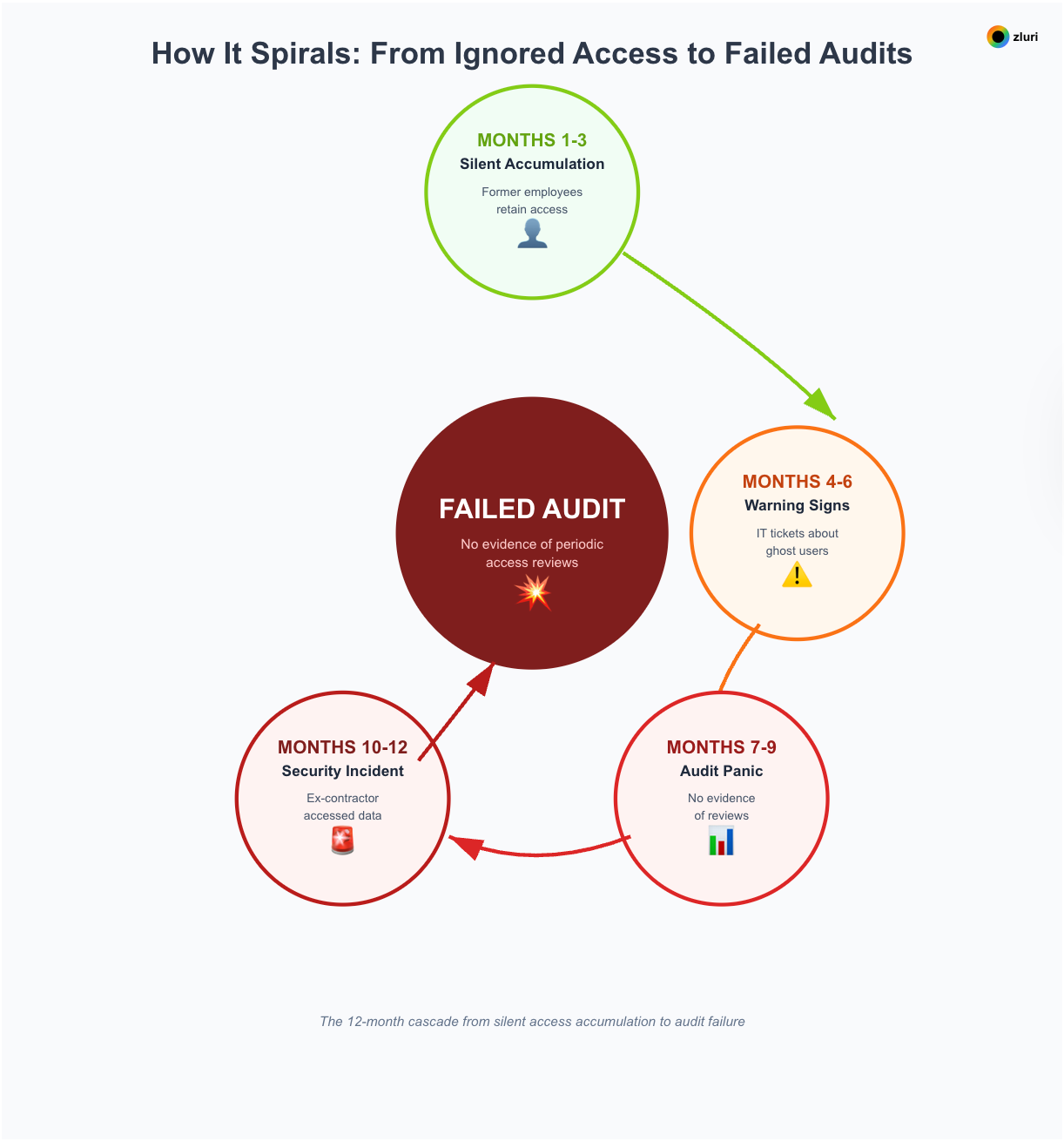
When security researchers examine breach data, they find patterns. A former employee still had access months after leaving. A contractor from last year's project never got deprovisioned. An intern somehow accumulated admin rights to production systems.
These aren't sophisticated attacks. They're basic access hygiene failures—exactly what access reviews are supposed to prevent.
Access reviews prevent these audit nightmares when done right. Here's why they're fundamental to security and compliance.
What access reviews actually do
Access reviews are systematic processes where you validate that every person's (whether employees, consultants, contractors, or partners) access to every application is appropriate for their current role and employment status.
Not once during onboarding. Not just when something goes wrong. Regularly—typically quarterly or semi-annually—you verify that access still makes sense.
The review asks simple questions: Does this person still work here? Did their role change? Do they still need admin access? Should this contractor who finished their project 3 months ago still have credentials?
Without systematic reviews, you're operating on assumptions: "We probably deprovisioned that person," "Access was probably appropriate when granted," "Managers probably know what their team needs."
Access reviews replace assumptions with evidence.
Reason 1: Security—preventing breaches from the inside
Insider access shows up in breach after breach
External attackers get headlines. But when investigators trace how breaches actually happened, insider access—whether malicious or just forgotten—shows up repeatedly.
And "insider" doesn't just mean current employees.
It includes former employees who still have credentials, contractors whose projects ended months ago, employees who changed roles but kept old permissions, and third-party vendors with persistent access. Each represents a potential breach vector that remains invisible until something goes wrong.
A contractor still has admin access—6 months after the project ended
A contractor starts a 6-month Salesforce integration project in January.
Week 1: IT provisions admin access. The project completes in June.
The contractor moves on to their next client. Access doesn't get revoked because nobody remembered to add this app to the offboarding checklist, the Jira ticket got closed as "complete" without verification, the contractor used their personal email (not the client's domain), and nobody thought to check after the project ended.
December: That contractor—now working for a competitor—still has admin access to your customer database, pipeline data, and pricing models.
Without systematic quarterly reviews, this access stays active indefinitely. You'll discover it during a breach investigation—after the damage is done.
Reason 2: Compliance—meeting regulatory requirements
Every major compliance framework mandates regular access reviews. But frameworks don't just require reviews. They require proof.
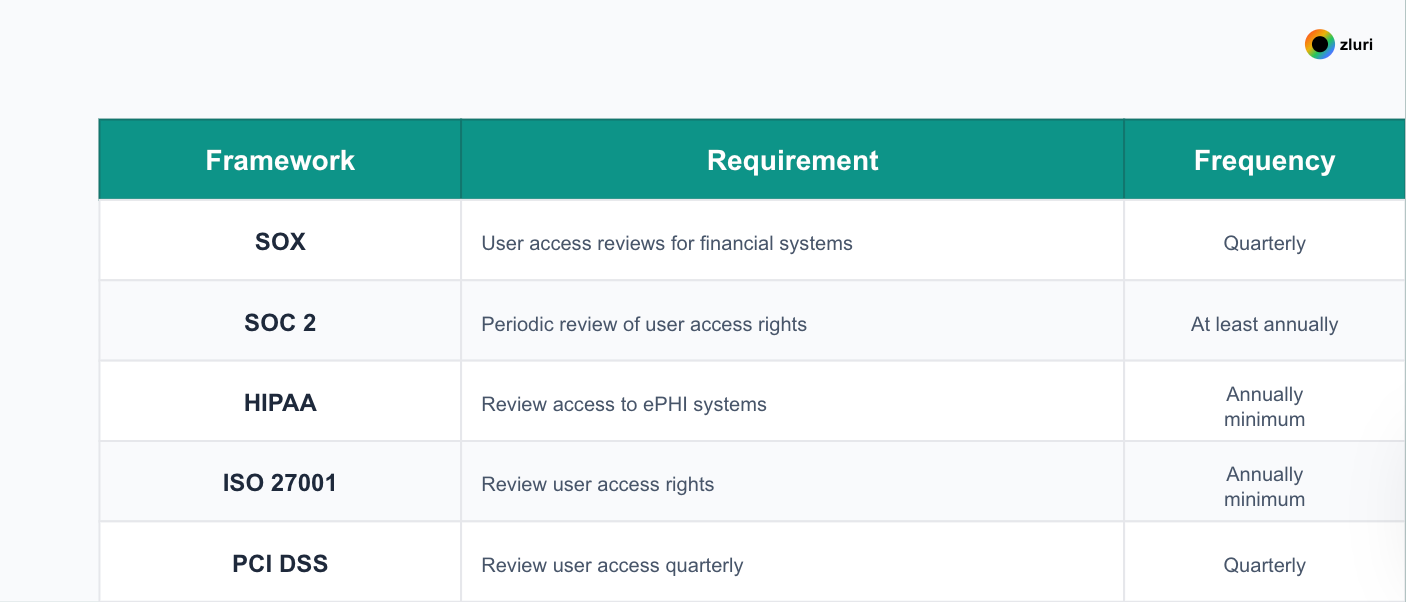
Here's what auditors actually check: evidence reviews happened on schedule, formal signed attestations, proof violations were remediated, and complete audit trails showing WHO reviewed, WHAT they decided, WHEN remediation occurred.
Reason 3: Cost optimization—eliminating wasted licenses
Without quarterly access reviews that include usage data, you can't identify users licensed but never logged in, dormant accounts (90+ days inactive), appropriate license tier, or duplicate licenses. Access reviews combined with usage intelligence turn cost optimization from annual budget panic into systematic savings.
Reason 4: Operational efficiency—stopping the reactive firefighting
With systematic quarterly access reviews, instead of scrambling for answers, you have them ready. Access reviews create a single source of truth across all your applications.
Reason 5: Risk management—continuous visibility
Regular access reviews transform access governance from reactive to proactive. Instead of violations accumulating indefinitely, they're identified and remediated within one review cycle—typically 90 days maximum.
Access reviews are fundamental, not optional
Organizations without systematic access reviews face higher breach rates, compliance failures, wasted spending, operational chaos, and accumulated risk.
The question isn't whether access reviews are important. They are. The question is whether you'll implement systematic reviews before an audit failure, security breach, or budget crisis forces your hand.
See who has access to what in your environment and prioritize access risks.
[Start Discovery Scan] → Book a Demo to understand your complete access landscape across all applications





.png)

.svg)














