As an IT manager, ensuring the smooth functioning and security of your organization's IT infrastructure is crucial. IAM tools like Microsoft Azure Active Directory enable you to effortlessly manage user identities and their access to various applications and data. However, considering Active Directory alternatives ensures your organization stays agile and adaptable to emerging technologies, evolving security threats, and changing business needs.
Empower your organization with Microsoft Azure Active Directory (Azure AD), a robust solution that streamlines user access to internal and external resources. Azure AD facilitates seamless access to corporate intranet applications and cloud apps tailored to your business needs.
Experience the convenience of enabling users to effortlessly connect to external resources such as Microsoft 365, the Azure portal, and a myriad of other SaaS applications. You can eliminate repetitive password inputs by implementing single sign-on (SSO) through Azure AD, enhancing user experience and boosting overall productivity.
With Azure AD and SSO, users gain frictionless access to SaaS apps. This configuration ensures that each user can navigate through their designated apps without the hassle of repetitive logins. Azure AD generates secure tokens locally stored on employees' devices, enhancing data security and accessibility.
Moreover, fortify your organization's security posture with the option to implement multi-factor authentication (MFA) for critical company resources. Azure AD ensures that your company's assets remain protected while providing a user-friendly experience.
Now, let's know more about Active Directory.
Key Features of Microsoft Azure Active Directory
Let's discuss a wide range of essential features of Microsoft Azure Active Directory.
- Centralized User Management: Active Directory simplifies the complex user management task by providing a centralized hub. This centralized approach reduces the risk of errors and accelerates the onboarding and offboarding processes.
- Seamless Authentication and Authorization: With Active Directory, your team can fortify their organization's security posture through robust authentication and authorization mechanisms. This granular control enhances data security and safeguards against potential breaches.
- Group Policy Management: Azure AD empowers you with unparalleled control over the configuration settings of computers within the network. Through Group Policy Management, administrators can enforce security policies, deploy software updates, and standardize system configurations across the organization.
- Efficient Resource Management: You can efficiently organize and categorize network resources, such as printers, servers, and applications, providing a structured view of the entire ecosystem. This streamlined resource management translates to quicker issue resolution, proactive monitoring, and improved overall network performance.
- Simplified Directory Search and Retrieval: Active Directory's powerful search and retrieval capabilities empower you to quickly locate and retrieve essential information. Whether searching for a specific user, group, or resource, the intuitive interface ensures administrators can easily navigate through the directory.
- Scalability and Flexibility: Active Directory seamlessly scales to accommodate changing needs. This advanced feature ensures that Active Directory remains a reliable foundation for IT infrastructure, supporting growth and innovation without compromising on performance.
Drawbacks of Microsoft Azure Active Directory
Some of the drawbacks of Microsoft Azure Active Directory are mentioned below.
- Managing tasks manually without sufficient automation can turn routine processes into tedious and time-consuming chores for your team. This lack of automation in Active Directory might lead to a heavier reliance on manual efforts, potentially hindering the efficiency of day-to-day operations.
- When comparing costs, Active Directory may not be as cost-efficient as some alternative solutions available in the market. This could pose a challenge if you're looking to optimize the budget while still ensuring effective and streamlined operations within the organization.
- One notable drawback of Active Directory is the learning curve associated with its setup and configuration. This learning curve can contribute to delays in deploying the system and impact the overall productivity of your IT team.
- Moreover, some users have reported the integration of Azure Active Directory with non-Microsoft systems as a potential issue. If you're seeking seamless integration across diverse systems, this challenge could create complications, requiring additional time and resources to address compatibility issues.
We have compiled a list of the best Microsft Azure Active Directory alternatives that you can consider for your organization's identity and access management.
9 Microsoft Azure Active Directory Alternatives
Now, let's explore various Active Directory alternatives.
1. Zluri
Unleashing the full potential of efficient access management within your organization can be a formidable challenge. Zluri emerges as the ultimate solution, delivering a robust access management solution that places you firmly in control.
Experience unparalleled precision in overseeing access to your SaaS applications throughout their entire lifecycle with Zluri's cutting-edge access management platform. Elevate your security protocols and seamlessly comply with regulatory requirements at every turn.
Zluri excels in streamlining access control, reinforcing security measures, ensuring regulatory compliance, and facilitating self-service access requests. Empower your team to enforce organizational policies effectively by aligning user access with established protocols.
Taking it a step further, Zluri uses 9 discovery methods to gain complete visibility into your organization's SaaS landscape. These methods include browser agents, IDPs & SSO, direct integrations, desktop agents, active directories, HRMS platforms, MDM platforms, finance systems, and CASB platforms. This empowers your team to identify and manage SaaS applications effectively.
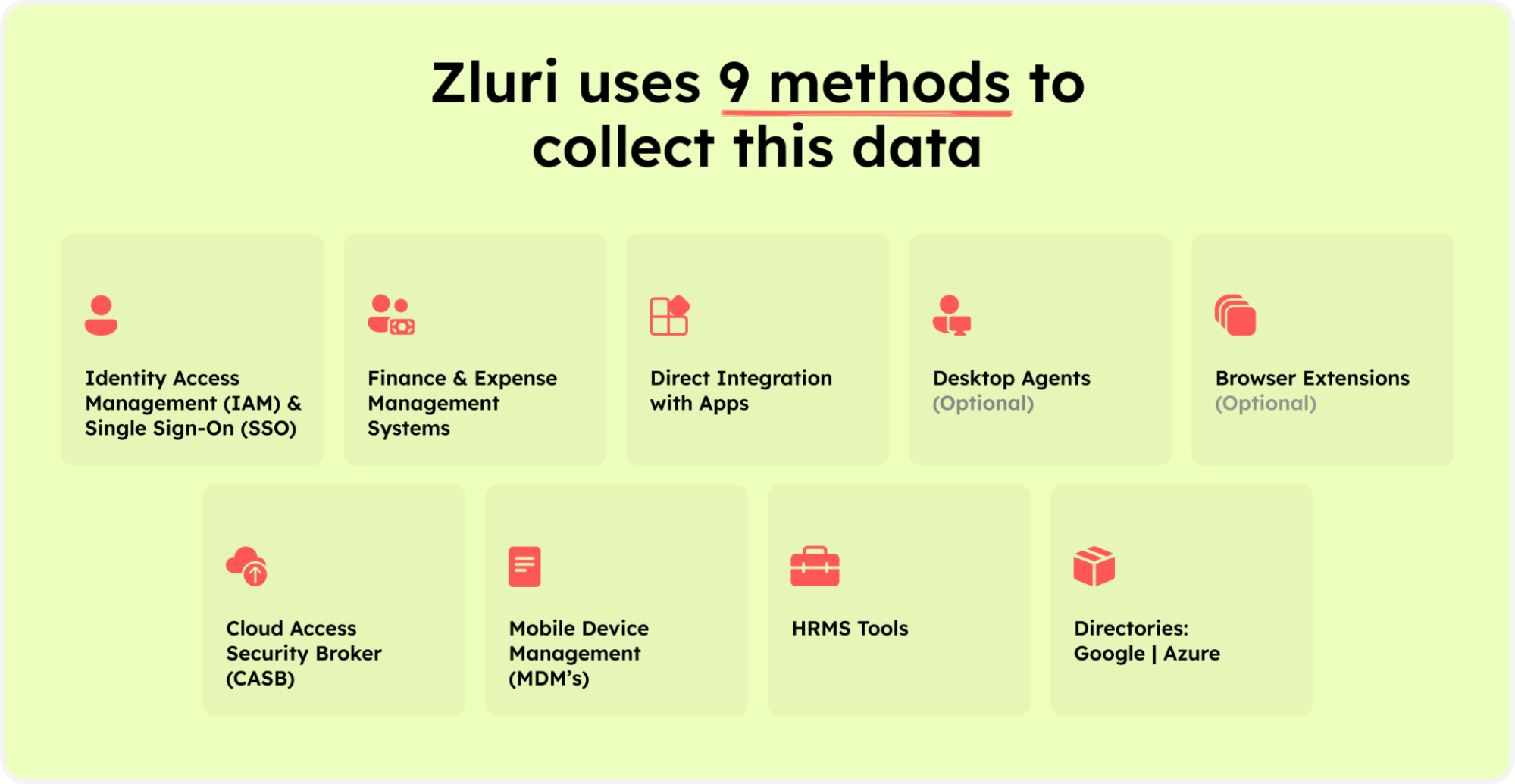
Zluri’s nine discovery methods
What truly sets Zluri apart is its seamless integration with over 300 SaaS applications. This extensive network translates into real-time data, invaluable insights, and timely alerts to keep you well-informed. With Zluri's API-based integrations, gain a comprehensive understanding of your SaaS environment, leaving no information concealed.
Let's delve into how Zluri revolutionizes access management, unlocking a new realm of efficiency for your organization.
- Automate your access control with Zluri
Elevate your organization's access control strategy to new heights with Zluri's all-encompassing user lifecycle management (ULM) platform, prioritizing robust security measures for optimized control. The platform simplifies both onboarding and offboarding processes, enhancing operational efficiency and reducing security risks.
Streamlined Onboarding
Zluri's ULM platform revolutionizes the onboarding experience for new employees, providing secure access to essential resources. Integrated seamlessly with your HR systems, Zluri empowers your IT team to centrally create user accounts across various applications, minimizing errors, alleviating administrative burdens, and ensuring that new hires possess accurate access privileges right from day one.
Efficient Offboarding
Zluri's capabilities extend throughout the entire employee lifecycle. During offboarding, the platform's automated deprovisioning workflows facilitate the swift revocation of user access across all applications. This proactive approach mitigates the risk of abandoned accounts and potential security breaches, ensuring a seamless transition during employee departures and safeguarding your digital assets.
Unique Features for Access Management
Zluri sets itself apart with distinctive features designed to significantly enhance access control.
Customizable Workflows: Say goodbye to manual access permission management with Zluri's customizable workflows. Tailor predefined workflows to suit your organization's needs, adapting to user roles, departments, and seniority levels, and streamlining access control to align with your unique requirements.

Onboarding

Offboarding
Powerful App Recommendations & In-App Suggestions: Zluri analyzes user profiles, departments, and seniority levels to provide context-based app recommendations, ensuring optimal provisioning.

The platform also offers in-app suggestions, enhancing user productivity by recommending necessary actions for efficient task execution. Empower your IT team to make informed decisions and boost overall operational efficiency.

Reusable Playbooks: Save customized workflows as predefined "playbooks" with Zluri, eliminating the need to recreate processes for each user. This feature streamlines the access management process, saving time and ensuring consistency. Apply these playbooks quickly to maintain efficiency and consistency in access control procedures.

- Simplify your access requests with Zluri's EAS
Zluri spearheads innovation with its cutting-edge self-serve solution - the Employee App Store (EAS). This transformative platform simplifies the intricate process of managing user access during role transitions, providing your organization with the tools to efficiently control and streamline access to resources.

Let's explore how.
Efficient Role-Based Access Control: The EAS facilitates swift and efficient access control during role transitions, ensuring employees have precisely tailored permissions to fulfill their job responsibilities. This robust RBAC feature empowers your organization to govern access effectively, safeguarding sensitive information within the enterprise.
Precision in Access Approval: With the EAS, you and designated approvers can easily review and authorize access requests aligned with employees' specific job roles and responsibilities. This ensures that permissions granted are finely tuned to the unique needs of each individual within the organization.
Transparent and Hierarchical Approval System: Zluri's transparent approval system operates on three levels: app owners, reporting managers, and IT admins. Decision-making privileges are distributed hierarchically, allowing higher-level authorities to override decisions made by lower-level admins or managers. This structured hierarchy ensures a seamless approval process while maintaining ultimate control over access.
Enhancing Transparency in the Rejection Management: In case an access request is declined, decision-makers can provide detailed comments explaining the reasons behind the rejection. This transparency in the access request process is invaluable, ensuring employees understand the basis of decisions.
Flexibility with Customized Request Modifications: Approvers within the EAS have the flexibility to modify specific requests as needed. This adaptability allows organizations to align access permissions with changing organizational requirements.
Empower Users through Change Tracking Capabilities: Zluri further enhances user awareness and engagement with its "changelog" feature. Users can now keep track of updates related to their access requests, including approvals or rejections, alterations in license duration or tier, and comments added by any admin. This transparency keeps users informed, promoting a collaborative and informed organizational culture.
- Ensure security and compliance with Zluri’s access review
Ensuring robust security and compliance measures in the dynamic access management landscape is non-negotiable. Zluri leads this domain, offering an unparalleled user access review solution to enhance security, streamline compliance processes, and simplify user access reviews and permission management.

Efficient Access Validation with Intelligent Automation:
- Zluri utilizes intelligent automation to assess user access rights based on predefined rules.
- Significantly reduces the risk of human errors associated with manual reviews.
- Configurable review parameters, reviewer designation, and scheduled campaigns for consistent and efficient access reviews.
Auto-Remediation for Enhanced Security:
- Zluri goes beyond conventional access reviews with auto-remediation capabilities.
- Immediate corrective actions upon detecting access violations bolster organizational security posture.
- Mitigates the risk of unauthorized data breaches, especially during employee role changes or departures.
Comprehensive Reports for Informed Decision-Making:
- Empowers enterprises with comprehensive reports providing insights into access patterns, vulnerabilities, and compliance status.
- Facilitates transparency for auditors and enables informed decisions regarding access management.
- Ideal for IT managers overseeing global expansion, ensuring compliance with international data protection regulations.
Pros
- Revolutionize your access management with Zluri, setting itself apart from conventional IAM tools with its seamless implementation and user-friendly interface. Your IT team will experience a hassle-free onboarding and usage process.
- Zluri's robust alerting system guarantees prompt notifications of any unauthorized access, providing your IT team with the proactive tools needed to protect sensitive data effectively.
- With Zluri, your team gains the ability to customize actions, strategically limiting or revoking access to crucial applications and users. This unique capability significantly elevates your organization's data security, putting you in control of access management like never before.
Cons
- While Zluri offers an extensive integration ecosystem, it's crucial to note that your IT team may face an augmented workload. This heightened workload could potentially hinder their capacity to concentrate on strategic initiatives and promptly address critical issues, posing a challenge to overall operational efficiency.
Customer Rating
- G2: 4.8/5
- Capterra: 4.9/5
2. Okta

Okta, one of the notified Active Directory alternatives, is an identity & access management software that allows deep integration with more than 100 applications that can be accessed using multiple devices with maximum security.
Okta helps in IT transformation by speeding up their movement with automation and removes friction by creating a great customer experience with customized secure applications. It also prevents data breaches by establishing people as new security borders. It does so by setting a standard for identity that is neutral and independent.
It allows immediate conditional access to all the applications with the SSO (single sign-on) feature and also provides double authentication that prevents attacks on identity. Furthermore, this type of authentication enables lifecycle management, firmly controls API access, and manages the directory centrally.
Okta enables connecting all your applications in days rather than months with prompt access to 1000s of pre-built integrations. Furthermore, it allows for manually adding apps to the network, easy integration and setup, and they are cautiously repaired, constantly monitored, and their secure authentication and provisioning taken care of.
Pros
- Elevate your business with the Okta Workforce Identity solution, streamlining the integration of diverse applications, even those not originally designed to collaborate. Spend less time troubleshooting compatibility issues and redirect your team's efforts toward boosting productivity.
- This cutting-edge tool guarantees secure connectivity for your software, regardless of its location. Safeguard software integrity, enhance security, and ensure accessibility, even in remote or diverse work environments.
Cons
- While the solution excels in many aspects, occasional delays in push notifications may disrupt timely responses to critical events, posing challenges to maintaining seamless operations and addressing issues promptly.
- Moreover, although robust, the tool's interface may have room for improvement in user-friendliness. Your security team might find navigation a bit challenging, potentially slowing down workflow and introducing the possibility of errors or inefficiencies.
Customer Rating
- G2: 4.4/5
- Capterra: 4.7/5
3. Avatier Identity Anywhere

Avatier Identity Anywhere, one of the best alternatives to Active Directory, is an enterprise identity management software that enables them to reduce and eliminate dual administration. It has a rollback feature that helps users go back to the older versions of individual documents per business requirements.
This tool also sends real-time notifications when an unauthorized individual creates changes in the company database. In addition, the meddling detection feature provides accurate data storage and administration.
Avatier's self-service password management provides the workforce with a seamless ability to securely authenticate with several multi-factor authentication varieties. In addition, the staff requires a self-serve password reset and synchronization without making an expensive and time-consuming call to support. Thus, this feature is reliable and efficient.
SSO(single sign-on) is another feature that helps the staff gain secure access to the organization's cloud applications. Avatier's SSO allows access to the workforce in crucial times with a JIT (Just in time) application user that helps in provisioning and deprovisioning.
Pros
- Access permissions become easy with Avatier, making the task of setting them up a straightforward and efficient process for your team. Avatier's user-friendly interface ensures that managing access permissions is easy and doesn't consume unnecessary time or resources.
- The platform empowers your IT team by providing a robust password management tool. This tool proves invaluable as it enables your team to effortlessly reset multiple passwords on a daily basis. Avatier's solution simplifies and streamlines the password reset process, saving time and enhancing overall efficiency for IT managers.
Cons
- Navigating the intricacies of this tool may pose a challenge when it comes to efficiently handling diverse tasks. Your team might find themselves logging into multiple platforms to achieve their goals seamlessly.
- If you prioritize a swift setup without compromising on efficiency, this tool may not align with your needs. Consequently, the delay in harnessing the tool for streamlined identity management could hinder your team's ability to perform tasks effectively.
Customer Rating
- G2: 4.6/5
- Capterra: 4.8/5
4. JumpCloud

JumpCloud, one of the prominent Active Directory competitors, is a complete directory platform for companies, and it allows the administrators to control IT domains in the cloud, remote, on-prem, etc. Using this tool, the admins can wield a simple web interface for provisioning, granting access, and managing resources that the employees required for daily usage.
It simplifies importing users from existing platforms and creating new users within JumpCloud, permitting access to the systems, networks, tools, and other resources.
The application identity management feature of JumpCloud helps businesses allow employees to make their own choices about getting collaboration tools to help them complete their tasks. This application basically serves as an authoritative directory for individual enterprises.
Pros
- The cutting-edge solution provides a myriad of customization possibilities for authentication and authorization, putting the power in the hands of your IT team to efficiently oversee identities and preemptively thwart any unauthorized access.
- For organizations predominantly utilizing Mac OS, our tool stands out as an ideal choice, seamlessly integrating with the operating system for a seamless user experience.
Cons
- However, budget-conscious decision-makers may find our solution less feasible as it comes with a higher price tag compared to alternative options for optimizing your identity management workflow.
- While the tool excels in many areas, its reporting capabilities may fall short of expectations. This limitation could impede your ability to monitor identities effectively, potentially leading to difficulties in streamlining processes and maintaining optimal security measures within your organization.
Customer Rating
- G2: 4.5/5
- Capterra: 4.7/5
5. AWS IAM

AWS IAM, one of the best Active Directory alternatives, is a smart, intuitive IAM solution that allows companies to control access to AWS(Amazon Web Services) based resources and APIs with firm security. The organizations can administer the users and user groups or schedule particular access rights to several AWS resources with the help of this IAM module within.
The organizations can then determine specific terms and conditions, like the exact time of the day, and control the staff's access factors. The access factors include their original IP address to see if they have active authentication with any MFA device and if they use SSL (Secure Sockets Layer).
It is compatible with SAML 2.0 apart from the original association samples offered by AWS Console SSO.
The application is available in the AWS user account with no extra charges, and the user pays only for using other services offered by AWS. There are also no additional charges for the AWS MFA security feature that augments the password, username, and other credentials.
Pros
- One significant benefit is the granular access that AWS IAM provides, ensuring that your users get precisely the permissions they need at different levels. This granularity ensures a secure environment while allowing for streamlined workflows.
- IAM stands out for its user-friendly interface, making it easy for both IT and non-IT professionals to navigate. Even individuals without a technical background can efficiently manage access permissions through the intuitive console.
- AWS IAM seamlessly integrates with a multitude of AWS services, enhancing its versatility. This integration ensures that access controls established through IAM extend seamlessly across various AWS offerings.
Cons
- One notable drawback is the potential complications arising from integrating specific third-party security tools. Compatibility issues or the necessity for extra configurations can pose hurdles, requiring additional time and effort to ensure seamless integration.
- Another aspect that you might need to consider is the user experience within the AWS Cloud Security interface. Some users may find it a bit perplexing and not as user-friendly as desired. This could result in a steeper learning curve for your IT team, potentially leading to delays in setting up and managing access controls effectively.
Customer Rating
- G2: 4.4/5
- Capterra: 4.8/5
6. Keycloak

Keycloak, one of the notified Active Directory alternatives, is an open-source IAM tool. It adds authentication to applications and secures the services with no hassle. This platform lets userbox. The interesting part is that even if Keycloak is open-source and is built with a simple design, it comes with advanced features like social login, identity brokering, and user federation.
The users can authenticate through Keycloak without using individual tools, meaning the other existing applications do not have to deal with any login forms and authenticate users or store them. Using this platform, the employees are not required to log in repeatedly to access other applications once logged into Keycloak from pre-existing apps.s skips storing users and authenticating accessors and is available out of the
Pros
- Keycloak, as an open-source solution, seamlessly integrates into your existing IT infrastructure, offering a hassle-free implementation process. This gives you a smooth transition without the complexities often associated with adopting new systems.
- Keycloak is equipped with versatile features that cater to the diverse needs of IT configurations. Its support for LDAP, SAML, OIDC, and OAuth workflows empowers you to set up and manage user authentication in a way that aligns perfectly with your organization's requirements.
- The user setup capabilities of Keycloak simplify your user management tasks. Whether it's creating, modifying, or managing user accounts, Keycloak streamlines these processes, allowing your team to focus on strategic initiatives rather than getting bogged down by routine administrative tasks.
Cons
- While Keycloak offers multitenancy and high-availability configurations, some users might require further improvement in this aspect. This means the current experience may pose challenges in achieving the desired level of efficiency and performance in complex, multi-faceted IT environments.
- One notable concern about using Keycloak is the perceived limitations in the documentation. The materials available may not cater comprehensively to the diverse scenarios and configurations you and your team encounter in their day-to-day operations. This shortfall can potentially lead to increased time spent troubleshooting and configuring, impacting the overall efficiency of IT management.
Customer Rating
- G2: 4.2/5
7. Oracle Identity Management

Oracle Identity Management, one of the best Microsoft Azure competitors, helps to manage user identity across the organization. This platform is scalable for directory services, access control, and identity governance. It helps build stronger security, capture business prospects, and simplify compliance through multiple access that includes social and mobile. Oracle's identity cloud service is completely integrated and uses a multi-tenant cloud platform to deliver access management and key identity features.
This Active Directory replacement is a solution for authorization and authentication purposes for the operating system, database usage, and tools in large enterprises. Using Oracle, the user can administer and manage passwords and provision and knit an extensive workflow mechanism. It also supports attestation, meaning the users can allow access rights to other individuals from time to time.
It delivers a risk-aware end-to-end MFA and SSO that integrates systems across the cloud on-site and identities smoothly. This platform can deploy images in its cloud infrastructure or in the on-site data centers; it can also help organizations gain flexible access control for the existing tools and help them migrate easily to the cloud.
Pros
- Empower your team with Oracle Identity, allowing them to effortlessly create groups, efficiently manage user access, and ensure a seamlessly streamlined identity management process within your organization.
- Designed with large organizations in mind, especially those with numerous users and systems, the solution is tailored to provide a unified view of all user identities and their access across the entire organization. This comprehensive approach not only simplifies identity management but also fosters the growth of your organization.
Cons
- However, it's essential to note that Oracle's user interface is intricate, necessitating the use of multiple applications to achieve desired outcomes. This complexity can pose considerable challenges for your team, hindering the efficient streamlining of identity management processes.
- Moreover, it's important to acknowledge that there is a learning curve associated with the tool. Your team will need to invest time in mastering the tool to unlock its full potential. This investment, although substantial, ensures that your organization can leverage the tool effectively for optimal identity management outcomes.
Customer Rating
- G2: 3.7/5
- Capterra: 4.4/5
8. OneLogin

OneLogin, one of the notified alternatives to Active Directory, is an easy-to-use software for managing identities and access. Users can rely on the particular to provide services like resource optimization, top-notch operational efficiency, feature-rich product functionality, and value-leading identity. In addition, it has features like single sign-on (SS), a unified directory, user provisioning, adaptive authentication, mobile identity, compliance reporting, and more.
Also, admins can use the software to protect their company by centralizing and securing all devices, applications, and end users through a single portal.
OneLogin helps protect important company information and allows employees to access all apps with a single set of credentials. OneLogin also helps to enforce security policies across the organization.
Pros
- Discover a cost-effective alternative to Active Directory with OneLogin solution, designed to streamline your software expenses and free up resources for crucial IT infrastructure enhancements.
- Experience simplified password management that alleviates your IT team from the hassles of handling password-related issues, such as resets and forgotten passwords.
Cons
- Unlike solutions that necessitate frequent password changes, leading to an uptick in support requests, our tool enables your IT team to redirect their focus from routine password management tasks to more strategic IT projects, enhancing overall productivity.
- While other tools may introduce downtime, disrupting access to associated software and causing widespread operational interruptions, the solution ensures a swift response from your IT team to minimize any potential impact.
Customer Rating
- G2: 4.3/5
- Capterra: 4.7/5
9. Ping Identity

Ping Identity, a notified Azure Active Directory alternative, builds identity security for the global enterprise with an intelligent identity platform that has many features, such as single sign-on (SSO), multi-factor authentication (MFA), directory, and more.
With cloud deployment options like identity-as-a-service (IDaaS), containerized software, and more, Ping helps businesses find the right balance between security and user experience for their employees, customers, and partners. Ping has solutions for both IT teams and teams of developers.
Ping Intelligent Identity is an all-in-one system that can be used with any supported identity provider to manage identities and trigger automated processes. In addition, businesses can use the cloud platform's solutions set to determine and settle on the best combination of requirements and use cases.
Pros
- Ping Identity presents a user-friendly interface, providing an alternative to JumpCloud with seamless navigation. Rapid onboarding of new users by your IT team minimizes training periods, enhancing software utilization, and subsequently, decreasing support requests while boosting overall productivity.
- Responsive customer service and engineering support teams at your disposal ensure swift resolution of technical issues, reducing downtime and promoting a smoother workflow. This empowers your IT team to concentrate on strategic tasks rather than spending valuable time troubleshooting problems.
Cons
- Due to synchronization issues, workflow disruptions can hinder operational continuity, particularly in offline mode. This may necessitate increased time and effort from your IT team, resulting in heightened support requests and diminished productivity.
- An administrative interface that lacks intuitiveness poses challenges for efficient software management and configuration. Overcoming this hurdle often demands additional training and support for your IT team.
Customer Rating
- G2: 4/5
- Capterra: 4.7/5
Manage Your User’s Access Efficiently: Choose the suitable Active Directory alternatives
Exploring alternatives to Active Directory represents a strategic initiative for IT managers like you, who are actively seeking tailored solutions aligned more precisely with their unique business requirements. Moreover, flexibility and scalability stand out as crucial factors, and a plethora of robust options are at your disposal to meet these evolving demands.
By delving into alternative IAM platforms, you can ensure your investment is in a solution that addresses your current challenges and scales seamlessly alongside your organization's growth.
Whether your focus is on cost-effectiveness, seamless integrations, or cutting-edge features, the diverse array of Active Directory alternatives opens up avenues for you to make well-informed decisions that drive efficiency and significantly enhance your overall identities and access management.
FAQs
What is Active Directory used for?
Integral to modern IT infrastructures, Active Directory plays a pivotal role in streamlining the management of devices, users, domains, and network objects. Organizations leverage Active Directory for its seamless and robust identity and access management capabilities, empowering them to efficiently oversee and control their digital environment.
Is LDAP similar to Active Directory?
It's crucial to compare between LDAP and Active Directory (AD). LDAP, which stands for Lightweight Directory Access Protocol, is a widely adopted standard application protocol serving as a versatile interface for communication with various directory services, including AD.
On the other hand, Active Directory takes a proprietary approach. It goes beyond the standards, offering a comprehensive suite of services and a robust database dedicated to identity and access management (IAM). AD doesn't just adhere to the LDAP protocol; it enhances it by providing a centralized and efficient solution for organizations to manage the lifecycle of user identities and control access seamlessly.









.svg)



.svg)
.svg)
.svg)
.svg)

.svg)

.svg)

.svg)
















.webp)







.webp)
.webp)





.webp)