Okta has been a pioneer in identity management. Besides, it boasts top-notch features that help organizations adopt, deploy, and manage their cloud applications. However, now there are some equally reliable and efficient competitors of Okta, which do the same at a comparatively much lesser cost. This is why companies look for Okta alternatives.
Okta offers a suite of solutions that simplify the complexities of identity management. From single sign-on (SSO) to adaptive multi-factor authentication (MFA), lifecycle management, workflows, and governance, Okta has got your back.
In addition, Okta helps your team connect people securely with technology by utilizing cloud-based security protocols. These protocols are powerful enough to allow users to access their data on any device while still being safe. Okta integrates seamlessly with existing directories, identity systems, and 4,000+ third-party applications.
Let's have a look at Okta's key solutions with their benefits, cons, and ratings.

Okta's Solutions with its Benefits
- Single Sign-On (SSO): With Okta’s SSO, your users can access all their applications with a single set of credentials, eliminating the need to remember multiple usernames and passwords. This saves time and enhances security by reducing the risk of weak or reused passwords. For your IT team, it means less password-related support tickets and more streamlined access control.
- Adaptive Multi-Factor Authentication (MFA): Okta's adaptive multi-factor authentication solution evaluates various factors, such as location, device, and user behavior, to determine the appropriate level of authentication required. With this two-factor authentication, you can rest easy knowing that sensitive data is protected, and your team won't be burdened with unnecessary authentication challenges.
- Lifecycle Management: Okta's lifecycle management automates this process. When an employee joins or leaves the organization, access privileges are automatically adjusted or revoked. Your team no longer needs to manually track and update user accounts, ensuring compliance and reducing the risk of unauthorized access.
- Workflows: This solution allows your IT team to automate repetitive tasks and create customized workflows tailored to your organization's needs. This efficiency boost saves time, reduces the potential for human error, and keeps your IT team focused on strategic projects instead of manual tasks.
- Governance: Okta's governance solution allows you to define and enforce access policies and roles, ensuring that the right people have the right level of access. This enhances security and simplifies auditing and reporting for compliance purposes.
Drawbacks of Okta
- Okta has relatively high contract minimums, so it may not be the best fit for small businesses. This can be a concern, as you might find the pricing structure less accommodating for your budget and needs.
- Okta’s pricing structure for its features can be confusing and inconsistent. This lack of transparency in pricing can make it difficult for you to plan and budget effectively.
- Your team might find the initial setup of Okta's solution challenging. This can consume valuable time and resources during implementation. This can also delay getting the solution up and running, potentially affecting the organization's productivity.
Customer Rating
- G2: 4.4
- Capterra: 4.7
Now that we've explored Okta's limitations, let's shift our focus to the array of alternatives available for Okta's two primary offerings: the Lifecycle Management solution and the Identity Governance solution.
6 Alternatives of Okta's Lifecycle Management Solution
Here are the best 6 Okta alternatives to its lifecycle management solution.
1. Zluri - The Best Alternative to Okta

Zluri's two products-SaaS management and Lifecycle Management platforms-provide automation solutions for every stage of the employee lifecycle. In addition, the platforms offer a range of features designed to streamline and simplify the processes involved in managing employees within an organization.
Effortlessly Identifying User Access and SaaS App Data with Zluri's Data Discovery Engine
Zluri boasts a unique advantage over its competitors by excelling in data discovery, thanks to its primary focus as a SaaS management platform. This expertise proves highly valuable, particularly in the realm of identifying SaaS app data and user access information.
In essence, Zluri simplifies the process for your IT team to seamlessly analyze and discover data related to SaaS apps and their users. How does Zluri accomplish this feat? Through Zluri's nine comprehensive discovery methods, including MDMs, IDPs & SSO, direct integration with apps, finance & expense management systems, CASBs, HRMS, directories, desktop agents (optional), and browser extension (optional), your team can collect all the pertinent data concerning user access and SaaS applications.
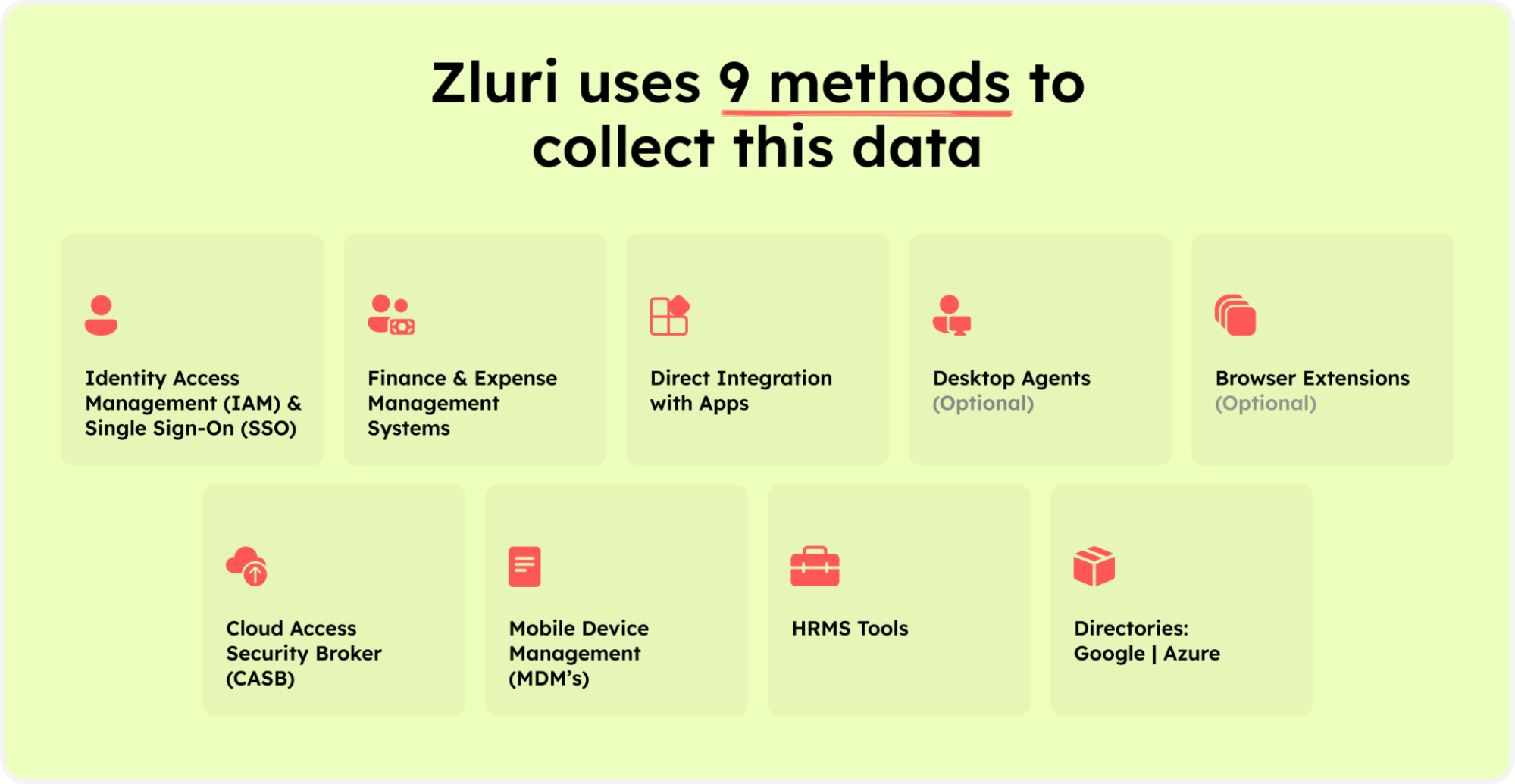
Zluri’s nine discovery methods
By utilizing these methods, your team can easily determine who has access to specific applications, identify active users, assess the permissions granted to them, and categorize employees accessing the apps as critical users or not, among other insights.
Note: It is backed by Kuppingercole's research and analysis report, that Zluri provides accurate and up-to-date data about which applications users have access to, and what level of access they have.
Access to such granular contextual data empowers your IT team to perform access reviews effortlessly. This streamlined review process enhances efficiency, minimizes the risk of oversights, and ensures that access privileges align with user roles while complying with regulatory requirements. Zluri is your key to efficient access management and compliance.
- Automate User Provisioning during the Employees Onboarding
Zluri's user lifecycle management is designed to help your IT team effectively onboard new employees. One of the key features of Zluri is its ability to provide new employees with access to resources they need on their first day.
This includes access to essential software and systems and training and onboarding materials. In addition, Zluri's workflow automation enables admins to efficiently assign various SaaS apps, such as Slack, Trello, and Grammarly, to new employees through one simple click.
Additionally, admins can create custom workflows and save them as 'playbooks' for future use. These templates can also be easily modified or removed as necessary. This helps new employees hit the ground running and contribute to the organization as quickly as possible.

- Automate Mid-lifecycle changes with Zluri Lifecycle Management Platform
Another important aspect of Zluri is its ability to automate the SaaS approval process for mid-lifecycle changes. Organizations can easily manage and approve new software and systems requests without needing manual intervention. This helps to ensure that employees have the tools and resources they need to be productive and efficient without adding unnecessary complexity to the process.
The App Catalog & Access Request from Zluri is a tool that streamlines and automates the process of approving and assigning new software and licenses to employees. This can save HR, and IT teams time and give employees greater autonomy and control over their tools.

- Securely Automate Employees Offboarding
Zluri provides a secure way to deprovision employees when they leave the company. Upon an employee's departure from the organization, it is crucial to revoke all of their SaaS licenses to protect the organization's data. This process can be time-consuming if done manually, but with Zluri, the offboarding process can be completed within a few hours. In addition, revoking licenses prevents further access to company apps and minimizes the risk of data breaches.
Additionally, automation tools can transfer ownership of ongoing SaaS app licenses or data and integrate with cloud directories for storing, using, and sharing data through cloud services. Using offboarding playbooks and pre-defined workflows can also make the process more efficient. These playbooks can be edited as needed and used multiple times.

Experience the power of Zluri for yourself and discover how it can streamline and optimize the management of your employee lifecycle. Request a demo today and take the first step towards improving your employee lifecycle processes!
Additionally, with all the benefits that single sign-on tools like Okta provide, there are some drawbacks also. SSOs are costly and require a huge amount of time to implement. Then, many occurrences of security breaches have been seen due to misconfiguration owing to their difficult implementation.
Additionally, Okta is not the best solution for de-provisioning users from SaaS apps. In some cases, ex-employees still have access to applications after leaving the organization. Furthermore, SSOs are not good with data retention and transfer from apps while onboarding users.
Zluri: The Proper Way of Deprovisioning
Deprovisioning via Zluri can be done with ease with a single click. In the back, the following four steps take place:
- Remove access to devices: To begin with, we revoke the authentication from all the devices. So, if a user is signed in on three devices, the user can't access the app from any of these devices.
- Data backup: Then, we transfer the data to another user or take a backup of the data. So, no data loss happens even though revoking the access is so easy from the admin perspective.
- Revoke the user license: Further, Zluri returns to the application and removes the user because all the data has already been transferred.
- Remove SSO: Finally, we remove the SSO as well.
During de-provisioning, Zluri doesn't stop at SSO-level authorization. It monitors the usage of the SSO system as well. For example, it monitors users for which apps they have access to, what level of permissions they have for the apps, their sign-in logs, audit logs, and access logs.
If a user still has access to any app or has not been removed (in rare cases), Zluri alerts you that the user can still use the application.

Pros
- Zluri provides a comprehensive employee lifecycle management solution that includes tailored provisioning and deprovisioning processes. These workflows ensure that all necessary steps are taken throughout the employee's tenure for seamless and efficient management of the entire employee lifecycle, ensuring compliance and consistency in all HR processes.
- Zluri offers a comprehensive platform that connects to over 300+ APIs allowing organizations to seamlessly integrate their systems, resulting in faster and more efficient custom integrations.
- The tool incorporates advanced digital security measures by integrating with different SSO and MFA providers to provide secure provisioning of SaaS apps for new employees.
- Zluri is dedicated to ensuring that it stays current with industry standards and customer needs by including regular updates to ensure compliance with regulations.
- The implementation process is smooth and efficient, with a dedicated customer success team available to address any questions or concerns.
- Zluri's user-friendly interface makes it easy for users to navigate and utilize all of its features effectively.
Cons
- While Zluri boasts the ability to create custom integrations, it often means a more intricate setup process. This increased complexity can translate to additional time and effort required from your IT team to configure the custom integrations.
Customer rating
- G2: 4.8/5
- Capterra: 4.9/5
2. MiniOrange

MiniOrange is a leading access management solution designed to help you streamline and optimize the entire user lifecycle within your organization. It offers a comprehensive suite of features to simplify user onboarding, authentication, access control, and offboarding.
MiniOrange simplifies onboarding and offboarding by providing a hassle-free method for adding new users to your system or revoking access rights. Whether it's employees, partners, or customers, MiniOrange's intuitive interface ensures a seamless transition into your ecosystem, reducing the time and effort needed for setup.
Moreover, MiniOrange ensures that only authorized users gain access to your systems through multi-factor authentication (MFA) and Single Sign-On (SSO). This extra layer of security significantly reduces the risk of unauthorized access and data breaches.
Pros
- MiniOrange offers an impressive array of pre-built integrations, which is a huge advantage for your team. These integrations allow your team to effortlessly connect and collaborate across various software and tools.
Cons
- When it comes to audit reporting, MiniOrange could benefit from more intuitive and effective features. This complexity can be challenging for you, requiring clear and actionable insights into your system's security and user activity.
Customer rating
- G2: 4.4/5
- Capterra: 4.5/5
3. JumpCloud

JumpCloud's user lifecycle management solution offers a robust and user-friendly approach to tackling these challenges, making it an indispensable tool for your IT team. It simplifies the user onboarding process, allowing you to easily get new team members up and running. With its centralized platform, you can provision users, assign roles, and grant access to the right resources in just a few clicks.
Similarly, JumpCloud streamlines the offboarding process, allowing your team to disable accounts and remove access privileges in a snap. This ensures the security of your systems and data, even when employees move on.
Further, JumpCloud's solution is adaptable to your organization's needs. Whether you're a small startup or a large enterprise, you can customize it to fit your specific requirements. As your organization grows, you can scale up without any hassle, making it a cost-effective choice.
Pros
- One of the most valuable aspects of JumpCloud is the effortless control over user access and permissions. This means you have a powerful tool at your disposal to efficiently manage who has access to what within your organization's systems.
- With JumpCloud, you can swiftly grant administrative privileges to those who need them, ensuring that your team can carry out their tasks without unnecessary delays or complications.
Cons
- One notable drawback is that the JumpCloud Agent doesn't update itself automatically to the latest version and has no manual update option. This means that your team needs to proactively monitor and manage the agent updates, which can be a potential source of inconvenience and extra work.
- Furthermore, some aspects of JumpCloud can be moderately confusing during the initial setup. This initial confusion could lead to a learning curve for your team, especially when they are just starting to work with JumpCloud.
Customer rating
- G2: 4.5/5
- Capterra: 4.7/5
Also Read: To know its detailed comparison with Okta, you can read JumpCloud vs Okta
4. ManageEngine ADManager Plus

ManageEngine ADManager Plus is your go-to solution for user lifecycle management. It simplifies complex tasks, enhances security, and boosts efficiency. Say goodbye to manual, time-consuming processes and hello to a smoother, more productive IT environment.
With ADManager Plus, you'll have more time to focus on strategic IT initiatives and less on administrative tasks. The tool also sends real-time alerts and notifications, helping you stay on top of changes and security events.
Pros
- ManageEngine's ADManager Plus offers a versatile array of tools to elevate your onboarding process, making it more efficient and tailored to your organization's unique needs.
- The software also empowers you to gain valuable insights through in-depth reports. These reports are vital for identifying your organization's security risks and compliance issues.
- One of the standout features of ADManager Plus is its user-friendly interface and dashboard. This user-centric design ensures you can quickly implement and manage your IT processes, saving time and effort.
Cons
- One significant challenge is that certain updates have resulted in compatibility issues within your Active Directory environment. This means that precious time is spent troubleshooting and seeking help, which can slow down the overall IT management process.
- Another concern is that the upgrade process with ADManager Plus remains largely manual. This manual aspect can be a drawback, implying that routine upgrades require more hands-on attention and effort.
Customer rating
- G2: 4.5/5
- Capterra: 4.4/5
5. Ping Identity

Ping Identity offers a comprehensive user lifecycle management solution tailored to your organization's needs. It simplifies onboarding, enhances security and compliance, and streamlines user offboarding.
Ping Identity software is designed to seamlessly integrate with your existing IT infrastructure. Whether you use cloud-based or on-premises systems, Ping Identity can be tailored to your organization's needs, reducing deployment complexity and minimizing disruptions.
Moreover, with SSO, adaptive authentication, and seamless integration, Ping Identity provides a robust framework to manage user access efficiently. With Ping Identity, users can reset passwords, update personal information, and manage their accounts, reducing the burden on your IT team and improving overall user satisfaction.
Pros
- Ping Identity offers you the advantage of seamless and hassle-free software setup. This means you can swiftly get your system up and running without the usual complexities.
- Ping Identity ensures lightning-fast deployment and upgrades. Ping makes it a breeze when you need to roll out updates or improve your system. The process is swift and efficient, minimizing downtime and ensuring your operations run smoothly.
Cons
- One challenge you may face with Ping Identity is transitioning from on-premises solutions to cloud offerings. You may need to allocate more time and resources to navigate this shift, and a learning curve might be involved in managing cloud-based systems effectively.
- Another potential issue is the complexity of role management and entitlement creation within Ping Identity. This can increase demands on your IT team's time and expertise, potentially impacting efficiency.
Customer rating
- G2: 4.4/5
6. SailPoint Identity Platform

SailPoint Identity Platform is a one-stop solution for all your user lifecycle management needs. It streamlines the entire process, from onboarding to offboarding and everything in between.
With this platform, you can grant and revoke access, manage passwords, and easily oversee user privileges, all from a centralized location. It eliminates the need for multiple tools and manual processes, saving valuable time and resources.
SailPoint provides a robust framework to protect your organization's sensitive data. It ensures that users have only the necessary access, preventing unnecessary exposure to potential security risks. It also helps detect and mitigate any unusual or suspicious activity, safeguarding your company from insider threats.
Pros
- One of the most significant advantages of SailPoint Identity is its user-friendliness. It offers a seamless way to control access to critical resources, ensuring a smooth user experience throughout their lifecycle within your organization.
- SailPoint equips your team with the ability to have complete control over the backend code, which is a powerful feature. This means you can easily manipulate workflows and rules to tailor the tool to your organization's specific requirements.
Cons
- One of the key drawbacks is the prevalence of bugs and cache problems. These issues can hamper system performance and lead to disruptions in day-to-day operations.
- Additionally, the installation process for SailPoint Identity can pose a significant obstacle. It is often described as complex and difficult to navigate, especially for those without extensive technical expertise.
Customer rating
- G2: 4.4/5
Also Read: To know its detailed comparison with Okta, you can go through SailPoint vs Okta
6 Alternatives to Okta's Identity Governance Solution
Now let's discuss the various Okta competitors for its identity governance solution.
1. Zluri
Is your IT team grappling with the complexities of access permissions, data security, and compliance standards? If so, Zluri has the perfect solution for you.
Introducing Zluri's cutting-edge identity governance and administration (IGA) solution, meticulously crafted to address the challenges of managing user lifecycles, access requests, and access certification workflows. With Zluri's IGA Solution at your disposal, your IT team can seamlessly oversee access with a strong focus on efficiency, compliance, and the utmost data security.
In the previous section, we delved into how Zluri streamlines app discovery and provides seamless access for your employees while ensuring secure access revocation when employees depart from your organization.
Now, let's dive deeper into how Zluri ensures access management while effortlessly meeting all your compliance requirements.
Zluri Leverages User Access Review to ensure security and compliance
In the realm of access management, the critical phase of access reviewing is indispensable for maintaining data security. Ensuring that every user holds the right level of access to applications and data is paramount. However, the manual approach to access reviewing can be detailed and inefficient, requiring your IT team to compile user lists, assess user statuses, scrutinize access patterns, and survey the myriad of apps that users access.
Enter Zluri, the solution that offers a seamless pathway to access certification. Zluri streamlines the entire access review process, providing a structured and automated approach to verify and validate user entitlements. This not only assists your IT team in ensuring that access privileges are audited regularly but also in detecting unauthorized access and meeting compliance requirements.
Zluri goes beyond these access review capabilities, boasting a range of exclusive features that set it apart from the competition. Let's delve into them one by one.
Unified Access Review
Elevate your IT team's capabilities with Zluri's Unified Access Review feature. This powerful tool empowers your IT department to identify which users can access various SaaS applications and critical data. It consolidates these invaluable insights into a centralized access directory where all user access-related data is securely stored.
Imagine you're onboarding a new employee who will be working in the Sales department. With Zluri's unified access review, your IT team can swiftly determine the precise access privileges the employee needs.
By leveraging the information stored in the centralized access directory, your team can allocate the appropriate user roles, ensuring the employee has access only to the tools and data relevant to her job, all while maintaining security and compliance standards.
But it's not just onboarding where Zluri shines. Consider the scenario of an employee who has just left the company. Offboarding can be a complex process, with multiple systems and applications to disentangle. Zluri simplifies this by providing your IT team real-time insights into the employee’s recent activities and access.
When the ex-employee’s account is deactivated, Zluri's alert capabilities notify your IT team immediately if there are any unauthorized attempts or suspicious activities associated with his account. This helps ensure the former employee’s access is revoked promptly, reducing the risk of security breaches or data leaks.
In addition, Zluri's activity and alert capabilities play a vital role in everyday operations. They provide your IT team with real-time information about users' activities, such as new logins or access changes, allowing reviewers to make well-informed decisions during access reviews. This ensures that the right individuals maintain access at all times, promoting security, compliance, and operational efficiency.
Zluri's unified access review feature is the cornerstone of effective access management, offering a seamless solution for your IT team to oversee access privileges and keep your organization's operations running smoothly.
Automated Access Review
Zluri simplifies access reviews by fully automating the process. Simply log in to Zluri, create a certification, and select the apps or users that require review. The reviewers will then carry out the review and provide you with the results via email.
This automation delivers results that are tenfold more efficient than manual methods, reducing the efforts of your IT team by a significant 70%. Let's explore how this automation works in detail.
By leveraging contextual data from Zluri's unified access feature, your team can go one step further by establishing access rules based on these insights. For example, if an individual holds an admin role on Salesforce, you can effortlessly create a review policy tailored to that specific scenario.
Subsequently, the scheduled certification feature comes into play, enabling your team to generate certifications based on the gathered information. This empowers you to take actions in alignment with the insights you've obtained.
These insights may include data such as the last login, department information, user status (active or inactive), and more, which guide your decisions during the review process. These decisions may involve determining whether the user's current access should be maintained or if any modifications are necessary.
Equipped with Zluri's context-rich information, your team can confidently make decisions that align with your access management policies, ensuring that the right users have the appropriate access, all while upholding data security.
Secure Access Orchestration/Auto-Remediation
Upon completion of the access review, the changes required as per the actions set during certification creation are set into motion. These actions, such as access modification or removal, are integral to secure access orchestration. This seamless process ensures access is managed securely and efficiently, safeguarding your organization's data and resources.
For instance, when creating a new certification in Zluri, your team will encounter the configuration action. Under this, they will need to create deprovisioning playbooks and modification playbooks. If the reviewers decline access permissions, the deprovisioning playbook runs automatically, and the same goes for the modification playbook. In both scenarios, the reviewers need to provide relevant reasons for their decisions, whether access permission is declined or modified.
Note: These actions occur automatically after the review, hence the term 'auto-remediation process.' Zluri also offers integration features that prove immensely valuable during data gathering. These integrations enhance the access review process and bolster the overall security posture of your organization.
For instance, when reviewing critical components such as the Identity System and core applications, Zluri seamlessly integrates with platforms like Salesforce, Okta, Azure, and others. These integrations are vital in gathering essential data from the identity system and SaaS applications, providing invaluable insights and streamlining the review process.
Furthermore, Zluri generates reports akin to audit logs or audit trails. These reports serve as essential documentation to share with auditors or keep for future reference. Audit trails serve as roadmaps, illustrating changes made during previous reviews.
For instance, if an employee's access level was downgraded from admin to user, it becomes crucial to review and ensure that the access remains appropriate or if there were any subsequent changes back to admin. Understanding the reasons behind such upgrades is essential for maintaining proper access control.
Zluri automatically generates reports on these changes, further facilitating the review process.
Pros
- Zluri provides periodic access reviews and certification that empowers your IT team to efficiently manage access rights. Managers and data owners can seamlessly validate permissions, ensuring that only authorized individuals have access to sensitive information.
- Zluri's analytics, reporting, and auditing functionalities provide your IT team with the capability to identify and address high-risk access privileges. With access to this critical data, your IT team can proactively manage security risks, reinforcing your organization's defenses against potential breaches.
- Zluri is designed to ensure that your organization remains in compliance with both internal policies and external regulations. This proactive approach to compliance safeguards your business from potential legal and security risks, making your IT team's job of upholding these standards significantly easier.
- With Zluri’s real-time alerts on suspicious activities like unauthorized access attempts and security breaches, your IT team can immediately protect your SaaS app data from potential security risks. This level of vigilance helps prevent breaches and data loss.
Cons
- Zluri's powerful analytics and auditing capabilities may demand a significant portion of the IT budget and staff resources. Balancing the allocation of these resources with other critical IT needs can be a complex task for you and your team.
Customer Rating
- G2: 4.8/5
- Capterra: 4.9/5
2. Saviynt IGA

With Saviynt, your IT team can leverage its powerful identity warehouse, enabling frictionless access and establishing a robust security framework with Zero Trust in your hybrid and multi-cloud environments.
Saviynt's advanced governance capabilities and cloud identity warehouse help your IT team mitigate security risks by detecting and preventing unauthorized access attempts. It provides complete visibility into identity and access, empowering better decision-making through AI/ML-driven recommendations, automated provisioning, and remediation.
Pros
- One of the standout advantages of Saviynt IGA is its seamless integration with a wide range of tools. This streamlined integration saves time and ensures that all your tools work together smoothly, reducing operational headaches.
- Saviynt IGA also provides an access risk assessment feature, which allows your team to identify and mitigate potential risks related to user access. This helps proactively manage and reduce access-related vulnerabilities, enhancing the organization's overall security posture.
- Saviynt IGA simplifies access certification, making reviewing and validating user access rights easier. This streamlined process not only ensures compliance but also saves time and effort.
Cons
- One challenge with Saviynt IGA is that when users change roles within the organization, their entitlements should change accordingly. However, if the entitlements do not update as expected, Saviynt removes the user's existing entitlements but fails to reissue them. This leaves the user without any entitlements, leading to operational disruptions.
- Saviynt IGA's reporting and analytics sections are not as effective as they could be, hindering your team’s ability to oversee and optimize identity governance and administration processes.
Customer rating
- G2: 3.5/5
- Capterra: 4.5/5
3. Symantec IGA

Symantec IGA platform is a cutting-edge cloud-based identity governance and administration solution designed to help you maintain tight control over who can access your organization's critical systems and data. It simplifies the complex task of managing user identities and their access permissions, all while ensuring the highest level of security.
It enables you to create a well-structured and controlled environment for managing user identities and access rights. This means you can easily define who gets access to what, when, and under what circumstances. Such a level of control minimizes security risks, helps maintain compliance with industry regulations, and streamlines your overall IT operations.
Pros
- With its user-friendly interface, Symantec IGA helps your team streamline their daily tasks, giving them more time to focus on strategic initiatives and less time wrestling with complex systems.
- Symantec IGA seamlessly adapts to the evolving needs of your business, ensuring that your identity governance and administration processes can grow with you. This flexibility is a significant advantage, allowing you to avoid costly and time-consuming system migrations.
- Symantec IGA provides a protective shield around your organization's sensitive data and critical operations. You can trust Symantec IGA's robust security measures to safeguard against threats and breaches.
- Moreover, its reliability ensures that identity and access management processes continue functioning smoothly, reducing downtime and minimizing disruptions to your IT environment.
Cons
- Symantec IGA, being a premium product, often comes with a higher price point. You might need to consider their budget constraints carefully and assess whether the benefits outweigh the upfront expense.
- Symantec IGA, despite its strengths, can pose challenges on the administrative front. You may find that the back-end experience for administrators involves a fair amount of clicking and navigating through various settings and options, leading to a steeper learning curve and potential inefficiencies in the administration process.
Customer rating
- G2: 3.5/5
- Capterra: 4/5
Also Read: To know it’s more competitors, you can walk through Symantec Alternatives
4. Oracle Identity Governance

Oracle Identity Governance provides comprehensive user lifecycle management and robust access entitlement controls for both on-premises and cloud environments. It offers efficient access requests and provisioning workflows, flexible role-based access control, and intelligent role-mining capabilities.
The platform enables your IT team to meet compliance objectives through granular entitlement management and customizable certification campaigns. With support for on-premises and cloud deployment, including Docker and Kubernetes, and seamless integration with Oracle Access Governance, your team can reduce compliance risk and enhance security posture.
Pros
- Oracle Identity Governance is a powerful software that makes managing multiple systems and users a breeze. With this tool, your team can efficiently oversee resource management and security, simplifying the overall management process.
- Oracle Identity Governance makes adding new applications a seamless process. You can easily incorporate new applications by directly modifying machine images via the identity & access management (IAM) system. This ensures a swift and efficient application integration process.
Cons
- Some of the technical terms and concepts within the software can be quite challenging to understand. This means investing more time and resources in training and onboarding to ensure your team can use the software effectively.
- This software doesn't have the most user-friendly interface. Navigating through the numerous applications can be a bit cumbersome, making it harder to quickly access the information you need.
- One notable downside is the presence of occasional bugs in the system. You might need to allocate resources for system maintenance and ensure that updates are applied promptly to keep the software running smoothly.
Customer rating
- G2: 3.7/5
- Capterra: 4.4/5
5. Omada Identity

Omada Identity is a comprehensive identity governance and administration (IGA) solution designed to alleviate these challenges. It empowers your team to efficiently manage user identities, roles, and access privileges across the organization.
Omada Identity simplifies identity management and access control, allowing your team to focus on strategic initiatives rather than getting bogged down in the complexities of user access. Omada Identity streamlines administrative tasks and reduces the risk of errors by providing a centralized and easy-to-use platform.
Pros
- The platform provides easy and swift access enablement, simplifying the process of granting and managing user access. This means you can efficiently and securely control who has access to what, reducing the risk of unauthorized data breaches.
- Omada Identity integrates various tools, making it exceptionally user-friendly for your team. With all the necessary tools and features neatly integrated, it's easier than ever to monitor and control user access, track user activities, and ensure security protocols are followed.
- With Omada Identity, you can effortlessly adjust user permissions and access levels as needed. The ease of modification ensures that the IT department can swiftly adapt to evolving organizational needs without unnecessary complexity or downtime.
Cons
- Setting up Omada Identity can take a long time and might be tricky. This can be frustrating for your team because it can delay important tasks and make it harder to meet deadlines.
- The way Omada Identity works could be improved. Even though it's super secure and powerful, the design could be more modern and user-friendly. As a result, your team might spend more time figuring out how to use it or helping others navigate it, which could be inefficient.
Customer rating
- G2: 3.8/5
6. Lumos

Lumos is your trusted partner in IGA. It offers a user-friendly platform that simplifies identity management, access control, and compliance enforcement. It provides a centralized platform for managing user identities. You can easily create, modify, or deactivate user accounts, reducing the risk of unauthorized access and data breaches.
With Lumos, you can enforce strict access policies. Define who gets access to what, when, and under which conditions. This granular control ensures that only authorized users can access sensitive systems and data.
Lumos easily integrates with your existing IT infrastructure using cloud-based applications, on-premises systems, or a hybrid environment. Lumos scales with your organization, ensuring your IGA solution remains effective and efficient as your organization grows.
Pros
- One significant benefit is that it simplifies role identification for end users, managers, and admins. It achieves this by having a strong foundation in Slack, a platform familiar to many users. This means that individuals can quickly and easily understand their responsibilities in the process.
- Unlike relying solely on emails, which can be easily overlooked or missed, Lumos employs Slack notifications with user-friendly action buttons. This approach leads to faster results and more efficient collaboration for everyone involved.
Cons
- One notable challenge when using Lumos is the learning curve that comes with it. Even with a dedicated support team in place, you'll still need to invest some effort to fully grasp how the software functions. This learning process can be time-consuming and might impact your team's workload.
Customer rating
- G2: 4.8/5









.svg)



.svg)
.svg)
.svg)
.svg)

.svg)

.svg)

.svg)
















.webp)







.webp)
.webp)





.webp)