Here's a detailed exploration of the contrasts between RBAC and PBAC and their implications for your unique access needs.
Effective access management is pivotal in bolstering any organization's cybersecurity framework. When access controls are not adequately implemented, there's a risk of sensitive information falling into unauthorized hands, resulting in data breaches, intellectual property loss, and potential financial harm.
Among the various access management models available, two prominent ones are Role-Based Access Control (RBAC) and Policy-Based Access Control (PBAC). Both RBAC and PBAC have distinct approaches to determining access rights and permissions for users, making them critical considerations for IT teams responsible for securing organizational resources.
This comprehensive blog explores the distinctions between RBAC and PBAC, empowering your IT teams to make informed decisions that align with your unique security needs and business requirements. Let's explore the key differences and discover which access control paradigm best suits your organization.
RBAC vs PBAC: 5 Key Difference
RBAC and PBAC are two distinct approaches to access control, each offering unique features and functionalities. Understanding their key differences is essential for making informed decisions about the most suitable access management model for their needs. So, let’s get started:
1. Access Control Mechanism
One of the primary contrasting parameters between Role-Based Access Control (RBAC) and Policy-Based Access Control (PBAC) lies in their access control mechanisms.
- RBAC operates on a role-centric approach, where access rights are predetermined based on predefined roles. Users are assigned specific roles, and permissions associated with those roles dictate their level of access within the system. The access control decisions are made solely based on the user's assigned role, leading to a relatively straightforward and hierarchical access management structure.
- On the other hand, PBAC employs a policy-centric approach, making access decisions dynamically based on policies and rules. PBAC policies are more fine-grained and can consider various attributes and contextual factors, such as time, location, user attributes, relationships between identities and resources, and more. This enables PBAC to provide more flexible and adaptable access control, accommodating the complexities of modern organizational environments.
RBAC's rigid role-based mechanism can sometimes lead to either over-privilege (where users may have access beyond their actual needs) or under-privilege (where users may lack necessary access for their tasks). While PBAC's policy-centric mechanism allows for more contextual control over access, making it suitable for dynamic and evolving environments.
You must carefully evaluate your specific access control needs and consider factors such as role dynamics, complexity, and contextual requirements to choose the most appropriate access control model for their unique environment.
2. Flexibility & Granularity
RBAC is relatively straightforward and effective in organizations with clearly defined roles and static access requirements. However, it lacks the flexibility and granularity offered by PBAC. PBAC allows for more sophisticated access control by considering attributes like time, location, user attributes, and relationships between identities and resources.
- RBAC offers a structured and hierarchical approach, providing simplicity and ease of administration. However, it may lack fine-grained control, as access is determined based on predefined roles, which may not cover all specific scenarios.
While effective in its simplicity, RBAC has certain limitations in terms of authorization. It focuses solely on a user's role, disregarding dynamic attributes and conditions that may change, such as time, location, or device. With fixed access rights, RBAC does not accommodate temporary changes, such as when an employee is temporarily assigned to a different department, leading to potential access gaps or inefficiencies in access control management. - On the other hand, PBAC allows for greater flexibility and fine-grained control over access decisions through policy rules. This approach enables more customized access based on specific attributes, time, location, and other contextual factors.
In contrast to RBAC, PBAC provides robust support for environmental and contextual controls. This allows policies to be configured to grant access to resources based on specific times, locations, and even relationships between identities and resources. PBAC facilitates effortless addition, removal, or modification of user groups, while obsolete permissions can be swiftly revoked with a simple click.
3. Ease of Implementation
- RBAC is a well-established access control model that has been widely adopted in various systems and applications. Its concept is relatively simple to grasp, as access rights are tied to predefined roles, and users are assigned to these roles accordingly. Implementing RBAC in an organization with clear role definitions can be relatively straightforward, as it involves setting up roles, associating permissions, and assigning users to roles. Many systems already come with built-in RBAC capabilities, making it convenient to integrate into existing infrastructure.
- In contrast, PBAC can be more complex to implement due to its policy-centric nature. PBAC policies are designed to be more flexible and fine-grained, accommodating a wide range of attributes, conditions, and contextual factors. Creating and managing these policies may require more effort and careful consideration to align with the organization's specific access control needs. Furthermore, PBAC may require additional customization or integration with existing systems to fully leverage its capabilities.
It's important to note that the ease of implementation for both RBAC and PBAC can vary depending on your organization’s existing infrastructure, the level of access control complexity, and the resources available for implementation requirements.
4. Adaptability To Changing Environments
Another key contrasting parameter between Role-Based Access Control (RBAC) and Policy-Based Access Control (PBAC) lies in their adaptability to changing environments.
- RBAC is well-suited for organizations with stable and well-defined roles. Once roles are established and permissions assigned, RBAC provides a relatively static access management structure. Defining numerous similar but slightly different roles becomes challenging as companies grow, numbering in the thousands or tens of thousands. Determining granular permissions for these roles can be difficult. Additionally, tracking role changes for users or revoking unneeded permissions poses security and compliance risks, leading to audit issues.
While RBAC is effective in environments where access requirements remain consistent over time, it may face challenges in dynamic settings where roles frequently change or when temporary access adjustments are necessary. Managing changes in RBAC systems, such as adding new roles or modifying existing ones, may require careful coordination and potential disruptions to the access control framework. - On the other hand, PBAC excels in adapting to changing environments due to its policy-centric nature. PBAC policies can be crafted to consider various attributes and contextual factors, making it more flexible and accommodating of dynamic access requirements. As organizational needs evolve, PBAC allows for seamless policy updates without significant disruptions. Policies can be modified to reflect new role definitions, changes in user attributes, or changes in access conditions, ensuring access control remains relevant and aligned with the evolving business environment.
PBAC's adaptability extends beyond accommodating role changes; it can also cater to other evolving aspects, such as changes in regulations, industry standards, or security best practices. Organizations operating in dynamic and complex environments can benefit from the ability to fine-tune access control based on real-time factors, such as time of access, location, and relationships between identities and resources.PBAC's ability to adjust access control policies in response to changing conditions makes it a powerful solution for organizations that require a more agile and responsive access management framework.
5. Centralized Control vs. Distributed Control
A crucial contrasting parameter between Role-Based Access Control (RBAC) and Policy-Based Access Control (PBAC) is their approach to control and administration.
- RBAC typically follows a centralized control model. A centralized RBAC system manages access control decisions and role assignments from a central authority or administration point. The roles and permissions are defined and enforced uniformly across the entire organization. This centralized approach ensures consistency in access management, simplifies administration, and reduces the risk of discrepancies in access rights.
- On the other hand, PBAC often employs a distributed control model. PBAC allows for more decentralized and fine-grained access control. Policies can be defined and managed independently for different organization resources, applications, or departments. This distributed control approach grants more autonomy to individual resource owners or application administrators, who can tailor access policies to their specific needs and requirements. PBAC's distributed model is particularly advantageous in large organizations or complex systems where access requirements may vary significantly across different areas.
Ultimately, the choice between RBAC and PBAC depends on your organization's specific needs, complexity of access requirements, and desired level of control and flexibility. A hybrid approach combining RBAC and PBAC elements might be suitable in certain scenarios to leverage the strengths of both access control mechanisms. Introducing Zluri, a top-notch, autonomous, and automated Identity Governance and Administration (IGA) platform.
Zluri's IGA: Beyond RBAC & PBAC - Next-Level Access Governance
In the modern organizational setting, your organization relies on a multitude of systems and applications, some on-premise and others in the cloud. Employees access these systems from various devices and locations, and the complexity grows with contractors, managed service providers, consultants, and bots all requiring access.
As a result, access governance has become a tangled web, making it challenging to ensure proper security. IT teams now require real-time visibility into user access privileges and their activities, necessitating a comprehensive understanding of who has access to what, when, and from where.
Zluri’s IGA solution ensures that access is granted only to authorized users under specific circumstances.

Curious about Zluri's magic behind it all?Many access governance solutions often operate at a high level, handling provisioning and de-provisioning of access without offering granular insights into individual access data and actions. Acknowledging this need for a more innovative approach, Zluri steps forward with its advanced Identity Governance and Administration (IGA) platform, reshaping how organizations govern access privileges and permissions. It enables you to define fine-grained access policies based on various attributes and conditions, ensuring that access is granted only to authorized users under specific circumstances.
The tool streamlines access requests, approvals, and access reviews through workflow automation, ensuring efficiency. It empowers IT teams with control over authentication, authorization, data protection, and compliance.

Well, Zluri recognizes that effective identity governance & administration begins with a comprehensive discovery of access privileges and user activity, which is why it incorporates a discovery engine. And to effectively work on these discovered insights, it offers an automation engine that facilitates swift and effective actions. These two engines collectively enable a range of possibilities.
Now, let's delve into the details...

- Unleash a Top-notch Discovery Engine To Gain User Access Data:
The initial step in establishing a robust access governance policy is visualizing and mapping the connection between identities and resources. Zluri provides IT admins with a clear view of authorized actions for each identity across all organizational assets.
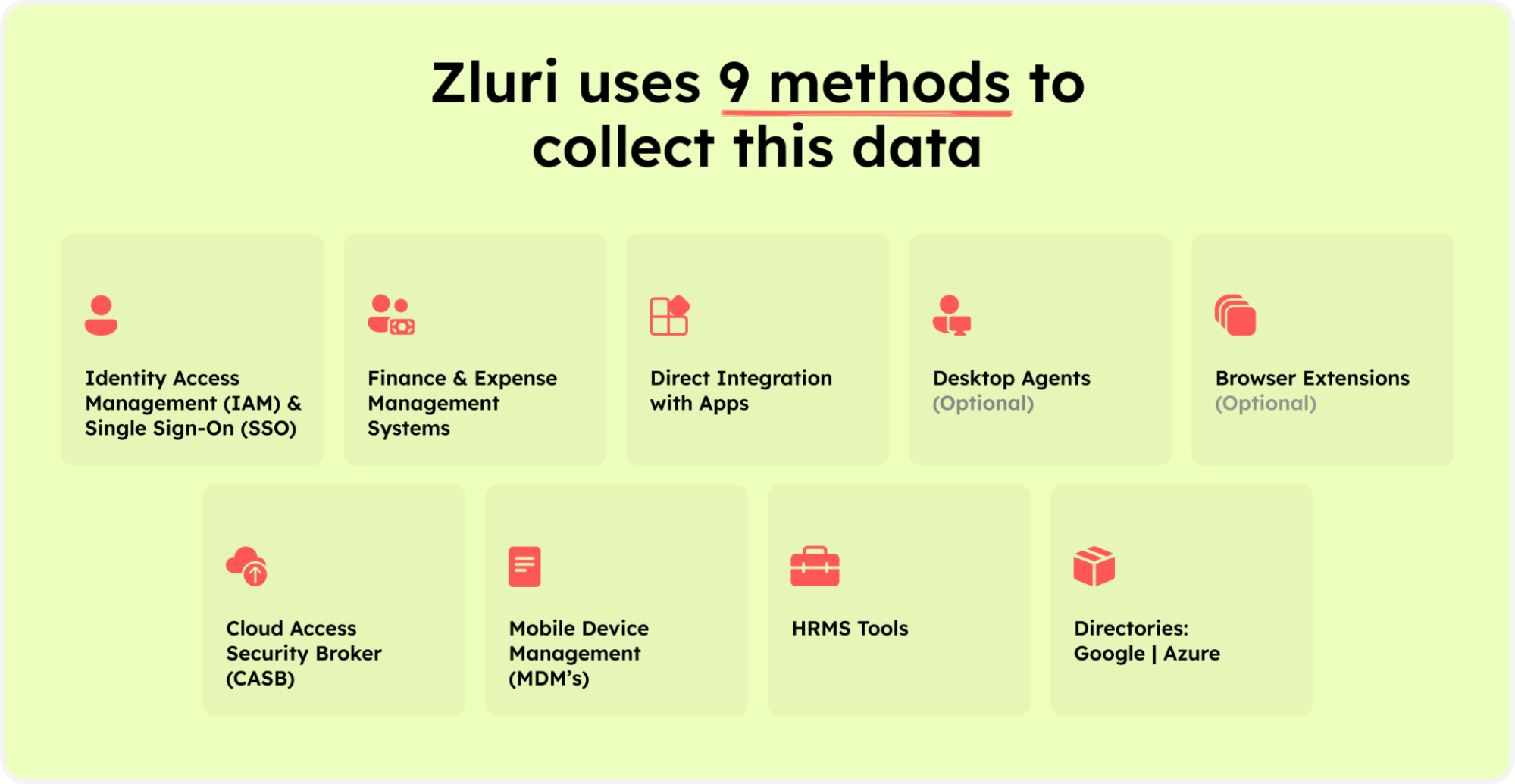
Zluri’s nine discovery methods
With its nine powerful discovery methods, Zluri delivers real-time visibility into user access data. These methods include MDMs, IDPs & SSO, direct integration with apps, finance & expense management systems, CASBs, HRMS, directories, desktop agents (optional), and browser extension (optional).
As per KuppingerCole’s analysis, Zluri provides a single source of truth for all SaaS applications in an organization.
With its robust discovery engine, Zluri empowers your IT team to analyze SaaS apps and user-related data effortlessly. Further, it helps your IT teams identify app access, user activity, permissions, and critical user categorization.
Integrating with popular Identity systems, it streamlines authentication process for employees. With access to 300+ SaaS apps and API-based integration, Zluri ensures 100% visibility, fortifying security measures against breaches.
Leveraging these approaches, your team can easily discern application access, active users, permissions granted, vital user categorization, and beyond. Consequently, once you reveal the granted access privileges for each user, their management and access control becomes hassle-free.
- Boosting Security & Efficiency:
Zluri's Automation Engine optimizes access workflows, enforcing policy adherence and hence streamlining the whole access governance process. Automation rules and triggers enable personalized and autonomous access provisioning, modifications, deprovisioning, and access review processes, streamlining administration, and enhancing IT management capabilities.
Unveiling Zluri's Modern IGA Core Capabilities

- Ensuring the Right Access for the Right Individuals with ULM Solution
In the intricate world of identity governance and administration, access provisioning, managing ad-hoc access requests, and access revocation play pivotal roles. Zluri's user lifecycle management (ULM) solution bridges the gap between these crucial endpoints, providing smooth and efficient access provisioning and deprovisioning. With ULM, IT teams can effectively manage user access privileges throughout their tenure in the organization, ensuring security and compliance with ease. In short, Zluri ensures that the right users have the appropriate level of access at all times.

Zluri streamlines access provisioning for new users, automating access rights based on predefined roles and eliminating manual errors. By automating this process, IT teams save time and reduce administrative overhead, enhancing overall operational efficiency. On top of that, Zluri simplifies deprovisioning when users leave or change roles, revoking access rights with ease to prevent unauthorized access and reduce data breach risks.
With smooth access management & governance, Zluri helps maintain a strong security posture and aligns with best practices in identity governance and administration.
Zluri's efficient access lifecycle management offers three unique features:
- Customizable Workflows: Zluri enables you to tailor pre-defined setups to your organization's needs, eliminating manual access granting and revoking. Intuitive custom workflows based on user roles, departments, and seniority levels ensure effective access management.

- Onboarding workflow

Offboarding workflow
- Intelligent App Recommendations: Zluri suggests apps based on user profiles, departments, and contextual factors, streamlining provisioning and enhancing productivity.

- Zluri goes the extra mile by offering advanced in-app suggestions, empowering your team to efficiently add employees to various channels, groups, or projects and send automated welcome messages.

- Reusable Automation Playbooks: Save onboarding and offboarding workflows as predefined templates, boosting operational efficiency and making the process seamless and efficient.

- Onboarding Playbooks

Offboarding Playbooks
- Enhanced Access & Entitlement Management for 150+ Apps
Zluri simplifies the complexity of managing access and entitlements across a diverse array of applications. With seamless integration and a unified interface, IT teams efficiently control user access for over 150 apps. The platform’s granular access policies align users with their roles, reducing unauthorized access risks.

Zluri's deep entitlement management ensures users only access what they need, bolstering security and compliance across the application landscape.
- Effortless Ad-hoc Requests Management: Ticketless Solution
Zluri's Employee App Store (EAS) revolutionizes access governance, simplifying ad-hoc requests and approvals during role changes.
EAS helps your IT teams gain full control over access based on job roles, providing a personalized experience. Its custom SaaS workflows streamline requisitions, approvals, and revocations with a transparent approval system for effective decision-making.

Further, the \"changelog\" feature promotes transparency and accountability, allowing employees to track request status and updates.
- Be Audit-Ready with Zluri's Automated Access Certifications
Zluri's Access Certifications solution ensures seamless compliance audits in the era of decentralized SaaS. Granting privileged access to employees has become more convenient, but it also brings new complexities in managing and controlling those privileges. Zluri's automated access certification simplifies user access reviews and permission management, providing a centralized platform for IT teams and auditors to review and report on users' access.

Its Access Certifications create a thorough and traceable log of user access, providing a distinct snapshot of authorized personnel for essential resources. By proactively confirming access rights and upholding a resilient audit trail, you can adeptly maneuver the intricacies of data security and regulatory adherence.
Using intelligent automation, Zluri's platform assesses user access rights based on predefined rules, streamlining the review process and reducing errors compared to manual methods. Instant auto-remediation capabilities promptly address access violations, enhancing security and ensuring compliance.

Zluri empowers IT teams to swiftly revoke access for terminated or outdated privileges, mitigating unauthorized data breaches. Its extensive range of reports offers valuable insights into access patterns, vulnerabilities, and compliance status, facilitating compliance and enabling informed access management decisions.
What sets Zluri apart is its continuous access reviews, providing recurring certifications to consistently validate permissions. Its scheduled certifications ensure timely reviews, addressing critical access issues and bolstering security.

Leveraging AI-powered compliance, Zluri elevates data security and simplifies compliance efforts. Real-time access reviews scrutinize patterns and user behavior, promptly detecting anomalies for proactive threat mitigation. Continuous monitoring ensures instant visibility into access privileges, enabling swift action on potential issues.

Zluri's AI compliance capabilities provide intelligent insights, aligning access controls with industry regulations to minimize compliance risk. Furthermore, Zluri offers industry-standard certificate templates, streamlining the certification process with comprehensive, accurate, and guideline-aligned documents.
Experience the future of access governance with Zluri today and unlock unparalleled protection for your valuable data. Book a demo right away!









.svg)



.svg)
.svg)
.svg)
.svg)

.svg)

.svg)

.svg)
















.webp)







.webp)
.webp)





.webp)