As an IT manager, you know that maintaining a secure and efficient work environment is paramount to the success of your organization. One essential practice to achieve this is segregation of duties (SoD). SoD refers to dividing essential tasks and responsibilities among different individuals to reduce the risk of fraud, errors, and unauthorized access.
Therefore, leveraging suitable software for your SoD requirements ensures that no single employee can control an entire process from start to finish, creating a system of checks and balances that fosters accountability and enhances data integrity. For this reason, it is important to choose the software suitable for your organization.
Segregation of duties is vital in safeguarding an organization's assets and sensitive information. When different employees handle distinct stages of a process, it becomes difficult for malicious individuals to manipulate or misuse data undetected.
This is especially important in high-risk areas such as finance, procurement, and access control, where an individual with unrestricted authority can cause significant harm if malicious intent is involved.
By clearly defining roles and responsibilities, SoD mitigates the potential for both intentional and unintentional errors. Even well-intentioned employees can make mistakes, but with SoD in place, errors are more likely to be caught and corrected before they escalate into significant issues.
Additionally, SoD supports compliance efforts, ensuring your organization meets industry standards and regulatory requirements.
To effectively set up and handle the separation of tasks in your company, you can use specialized SoD software. But, in reality, there is no SoD software available in the market. It is mainly the software that comes with SoD capabilities.
The solutions with SoD capabilities are designed to help you automate managing who can access what and have visibility on what users are allowed to do in different systems and apps.
However, choosing the right software that suits your organization is essential. Before you start looking at specific tools, getting what your company needs is a must. This will be the base for finding a solution that fits perfectly with your business.
Also, it's vital to look at how your organization is structured and how things get done. Figure out the leading jobs and duties in different departments of the company, like finance, HR, and IT. Understanding how tasks are given out, and done, will help you understand where it's crucial to have that separation of duties.
This blog post will discuss the essential things to consider when choosing suitable software for implementing SoD practice in your organization.
4 Things to Consider While Choosing Software With SoD Capabilities
When evaluating solutions for enforcing SoD, you should consider the following factors to select the right tool for your organization’s specific needs.
1. Must have RBAC capabilities
You, being an IT manager, are responsible for maintaining a secure and efficient working environment. Thus, you know the significance of SoD in preventing potential fraud and errors.
However, ensuring proper SoD can be complex, especially in large organizations with numerous users and varied roles. This is where role-based access control (RBAC) capabilities in software become indispensable, streamlining your efforts and safeguarding your business operations.
RBAC capabilities in the software for SoD provide you with centralized control over user access and permissions. By defining distinct roles and assigning appropriate access rights to each role, you can ensure that employees can only perform tasks essential to their job roles.
It will prevent accidental or intentional misuse of privileges and help you maintain regulatory compliance with industry standards and data protection laws.
Furthermore, a key thing to think about is keeping your data safe. Imagine your software as a shield that guards against potential data leaks. It does this by ensuring that each person only has the exact access they need to do their job – no more, no less. This lowers the chance of someone getting into sensitive info or important systems without permission.
So, when your software has this kind of protection, it creates a work environment that's safe and smooth. Your team members can get to the things they need right when they need them, and you won't have to spend as much time fixing access problems. All in all, this system helps everyone get more done.
2. Allows customizing the permission settings and access levels
One critical aspect to consider while choosing software with SoD capabilities is its ability to offer customizable permission settings and access levels. This feature is pivotal in bolstering security measures and providing you with the control you need to manage your team and system operations effectively.
With this flexibility of customizing permission settings and access levels, you can fine-tune who gets access to what data and functions, ensuring that each team member only has access to the specific resources required to perform their tasks.
Further, it minimizes the risk of accidental or intentional data breaches, as employees won't have unnecessary access to sensitive information outside their responsibilities' scope.
Moreover, assigning different access levels to different roles ensures that employees only have the minimum permissions necessary to fulfill their job duties. This approach significantly reduces the risk of unauthorized access attempts and limits the potential damage that could result from a security breach.
The software with customizable permissions simplifies the process of granting and revoking access. Instead of managing complex access rights on multiple systems, you can centralize the control within the software. This streamlines administrative tasks, saves time, and reduces the chance of administrative errors that might lead to security vulnerabilities.
In addition to strengthening security, customizable permission settings and access levels can help you comply with industry regulations and internal policies. By defining clear boundaries and restrictions for each role, you ensure that your organization adheres to mandated guidelines, avoiding potential legal repercussions and financial penalties.
3. Provide audit trail and real-time monitoring capabilities
To ensure seamless operations and safeguard sensitive data, you need robust software that offers audit trails and real-time monitoring capabilities. These features serve as the foundation for comprehensive security, regulatory compliance, and risk management.
Audit trails play a pivotal role as they record a chronological sequence of all activities within the software. Each action is meticulously logged, from user access and authorization changes to data modifications and system configurations. This transparent record helps you track every movement, granting unparalleled visibility into the system's operations.
Audit trails act as an invaluable forensic tool in case of any discrepancies or security breaches, enabling you to retrace steps, pinpoint the root cause, and swiftly respond to potential threats.
In addition, real-time monitoring is essential to a solution with SoD capabilities, enabling you to maintain a proactive stance against potential risks. With real-time monitoring, you gain immediate insights into user activities, access attempts, and any suspicious behavior within the system.
This data allows for prompt detection and response to anomalies, unauthorized access attempts, or policy violations, minimizing the window of opportunity for malicious actors to exploit vulnerabilities. You can implement timely measures to block unauthorized access, revoke privileges, or initiate alerts, thus preventing security breaches before they escalate.
4. Calculate ROI
Before you finalize your selection for the software with SoD capabilities, it's essential to calculate the chosen software's return on investment (ROI) to ensure it aligns with your organization's goals and budget.
Calculating ROI involves assessing the potential benefits and cost savings that the software can bring to your organization.
Firstly, consider the financial aspect - will the software lead to significant cost reductions in terms of manual oversight, audit preparation, and compliance management? By automating access controls and permissions, the software can reduce the need for time-consuming manual reviews, freeing up your IT team's valuable resources for more strategic tasks.
Evaluating the ROI of the software can help you assess its impact on risk reduction and security enhancement. The software's ability to detect and prevent potential conflicts of interest or risky user activities can safeguard your organization from costly security incidents and reputational damage.
Furthermore, by calculating the software's ROI, you better understand how it aligns with your organization's unique requirements. Not all solutions with SoD capabilities are created equal, and some may offer additional features that suit your organization's specific needs.
Additionally, considering ROI helps you make a more compelling business case to stakeholders and decision-makers. When you can demonstrate the financial benefits and improved security posture that the chosen software brings, you're more likely to gain support and approval for your investment. The ROI analysis provides concrete evidence of the software's value, making it easier to justify its adoption.
Opt for Zluri’s IGA Solution That Helps You Meet SoD Requirements
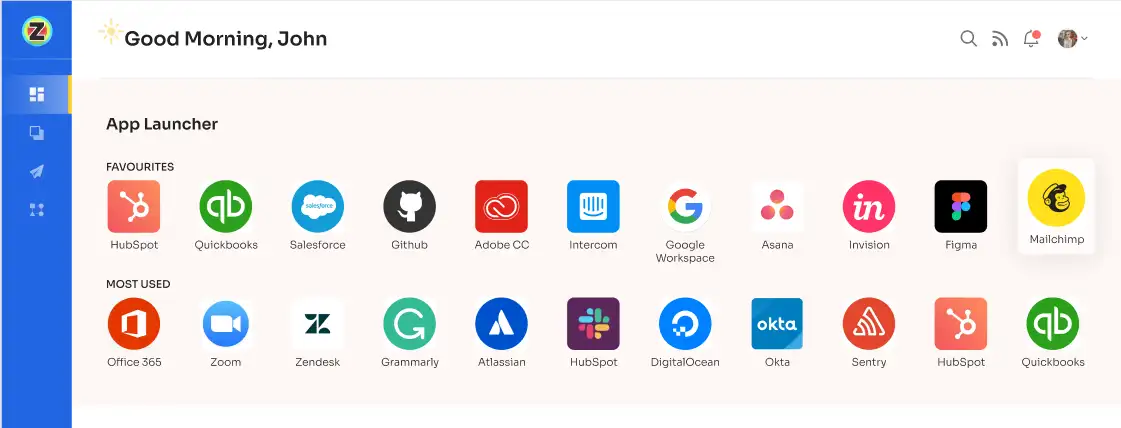
Zluri offers a powerful identity governance and administration (IGA) platform specifically designed to meet your requirements to implement SoD. With Zluri’s IGA platform, you can effortlessly control access to all your applications, from the moment users join until they leave.
Zluri's IGA platform gives you the ability to maintain complete control and enhance security through essential features like user provisioning, automated access reviews, and self-service access requests. By using the platform, you can make sure that each user's access is properly managed and aligns with your organization's policies. This ensures not only stronger security but also compliance with necessary regulations.
Now, let's explore how Zluri stands out from other IGA tools by offering unique capabilities.
Empower your SoD capabilities with Zluri’s discovery engine
Zluri uses 9 discovery methods to gain complete visibility into your organization's SaaS landscape. These methods include browser agents, IDPs & SSO, direct integrations, desktop agents, active directories, HRMS platforms, MDM platforms, finance systems, and CASB platforms. This empowers your team to identify and manage SaaS applications effectively.

But Zluri doesn't stop at discovery. The platform goes above and beyond by integrating with over 300 SaaS applications. This means you get real-time data, valuable insights, and AI-powered alerts to stay informed.
With API-based integrations, Zluri ensures the in-depth discovery of data across all your SaaS applications, leaving no information hidden. You can trust that Zluri provides 100% visibility into your SaaS environment.
Now, let's look at how Zluri's discovery engine aids in separating duties.
Let’s say you work in a company where different teams manage different software. The finance team handles the expense management tool, the IT team oversees API connections, and the security team takes care of SSO. With Zluri, each team can access the specific information they need without interfering with the others. This way, responsibilities are neatly divided, and everyone can focus on their own tasks efficiently.
Implement access control with Zluri’s automation engine
Zluri's automation engine is a smart driving system for your organization. It handles who can access what in a really easy way, making sure everything works super smoothly. It's like having a bunch of rules that it always follows to keep things fair and square.
With Zluri's automation engine, your IT teams can easily ensure that the right people have the right permissions. This helps keep everything secure and follows the idea of SoD, making sure no one has too much power all at once.
Now, let’s explore Zluri’s automation capabilities that help you to control access and implement SoD successfully.
- Lifecycle Management
Zluri's IGA solution offers user lifecycle management capabilities for simplifying and securing user access in your organization. With Zluri's IGA platform, you can easily manage user accounts throughout their journey, from onboarding to offboarding, all while maintaining strict security measures.
When it comes to onboarding, Zluri's IGA makes the process a breeze. New employees can quickly access the applications and resources they need, thanks to automated processes and seamless integration with HR systems. Your IT teams can efficiently set up user accounts across multiple applications from a centralized location, reducing errors and administrative workload and ensuring that new hires have the right access from day one.
But Zluri's capabilities don't end there. When employees leave the organization, Zluri's automated deprovisioning workflows empower your IT teams to revoke user access across all applications. This mitigates the risk of abandoned accounts and potential security breaches. This way, you can enforce SoD practice, ensuring that users only have access to the resources and applications necessary for their role and nothing more.
Let’s consider your IT department as a complex network with various roles: one team member oversees network security while another manages software deployment. This division of responsibilities is crucial to maintain a balance of control and access.
With Zluri's IGA, you ensure that no individual within your IT organization possesses excessive privileges. It's akin to providing each team member with precise access to their designated roles and having access control within the organization.
In addition, Zluri offers unique features that differentiate it from others, ensuring effective access management:
Customizable workflows: With Zluri, you can set up pre-defined workflows tailored to your organization's specific requirements, eliminating the need for manual granting and revoking access permissions. The intuitive interface allows you to customize workflows based on user roles, departments, and seniority levels.

Onboarding

Offboarding
Powerful app recommendations & in-app suggestions: Zluri also provides contextual-based app recommendations based on user profiles, department, seniority level, etc., making it convenient for your team to choose the appropriate apps for provisioning.

Moreover, it offers in-app suggestions to enhance user productivity by recommending required actions for efficient task performance.

Reusable Playbooks: By saving these workflows as predefined “playbooks”, Zluri eliminates the need to recreate workflows for each user, further streamlining the process and increasing operational efficiency.

But what happens when a user’s role changes during the mid-lifecycle transitions?
- Access request management
Zluri makes managing user access during role changes super easy with its Employee App Store (EAS). This smart tool empowers your IT team to control employees' access to important tools and applications.
With the EAS, your team or designated approver can review and approve access requests based on employees' job roles and responsibilities. This ensures that access permissions are aligned with their specific needs, helping you maintain proper access controls and protect sensitive information within your organization.

Zluri's approval system is transparent and has three levels: app owners, reporting managers, and IT admins. Higher-level authorities can override decisions made by lower-level admins or managers, giving them the ultimate say.
In case an access request gets rejected, decision-makers can provide comments explaining the reasons for the rejection, ensuring transparency and clarity in the process. Approvers also have the flexibility to modify specific requests if required.
Now, let’s see ho Zluri’s EAS helps you meet your SoD requirements.
For instance, an IT department with various responsibilities like server maintenance, database management, and application support. Each of these tasks needs different levels of access to systems and tools. Without a proper system, an employee who is responsible for server maintenance might end up having access to sensitive customer data stored in databases, which poses a security risk.
With Zluri's EAS, during a role change or when a new IT employee comes onboard, their access needs are clearly defined based on their specific role—whether it's server maintenance, database management, or application support. The IT manager or designated approver can review and approve these access requests according to the predefined rules.
This prevents any single individual from having excessive access that could lead to a breach. SoD is maintained as the right checks and balances are in place, ensuring that no one person has conflicting responsibilities or too much control over critical systems.
In addition, to keep users well-informed, Zluri offers a "changelog" feature where users can track updates related to their access requests. This includes information on request approvals or rejections, changes in license duration or tier, and comments added by any admin. This keeps users updated and aware of any changes or decisions made regarding their access to applications.

Ensure security & compliance with Zluri’s access certification
Zluri's IGA solution streamlines the user access review in your organization. This powerful platform offers a centralized hub where security, GRC (governance, risk, and compliance) teams, and auditors can effortlessly review and report on user access.

With Zluri, you can say goodbye to manual and cumbersome processes. Set up access review parameters, select reviewers, and schedule campaigns with ease. The intelligent automation feature of Zluri evaluates user access rights using predefined rules, significantly saving time and reducing errors compared to traditional spreadsheet reviews.
But Zluri doesn't stop at just reviews. It takes security to the next level by offering auto-remediation capabilities. In case of any access violations detected, Zluri takes immediate corrective actions. This ensures your organization's security is strengthened, and compliance with SoD capabilities is maintained. It helps prevent unauthorized data breaches by promptly revoking access for terminated employees or those with outdated privileges.
Zluri is more than just a security tool; it empowers you with comprehensive reports. These reports offer valuable insights into access patterns, vulnerabilities, and compliance status. With this information at your fingertips, you can easily demonstrate compliance to auditors and make informed decisions about access management.

Zluri's unique approach to access reviews sets it apart from other IGA tools. Let’s see how.
Continuous Access Reviews: It allows you to conduct regular and scheduled certifications of access permissions. With recurring certifications, you can ensure a consistent and systematic review of access rights. This helps you quickly spot and address security weaknesses, protecting your organization from potential threats.
On the other hand, scheduled certifications offer planned and timely evaluations, reducing the risk of overlooking critical access issues. This proactive approach ensures that access privileges remain up-to-date and help you maintain SoD across the organization.

To further simplify the certification process, Zluri provides you with industry-standard certificate templates. These templates follow recognized guidelines, making the certification process efficient, comprehensive, and accurate. You can rely on Zluri to maintain a standardized approach, ensuring that your access reviews align with best practices and security standards.
Real-time Access Reviews: Zluri leverages the power of artificial intelligence (AI) to boost data security and streamline compliance procedures. It works by continuously analyzing user activity, access patterns, and system logs in real-time. This way, it can quickly detect any unusual or potentially risky actions, helping you proactively prevent security threats and safeguard sensitive information.
With Zluri, you get access to real-time monitoring of access privileges, allowing you to promptly address any access-related issues. This reduces the risk of unauthorized access or misuse of data within your organization.

One of Zluri's key strengths is its AI compliance capabilities. It provides intelligent insights and recommendations to ensure your access controls align with industry regulations and standards. By leveraging AI technology, Zluri simplifies the compliance process, making it easier for your organization to meet regulatory requirements, particularly when it comes to SoD capabilities.









.svg)



.svg)
.svg)
.svg)
.svg)

.svg)

.svg)

.svg)
















.webp)







.webp)
.webp)





.webp)