IT Teams
• 6 min read
How To Prioritize & Mitigate SAM Risks
2nd August, 2023
SHARE ON:
Assessing risks is one of the parts of software assets management (SAM). The impact level of these risks is based on the four quadrants it falls under. As an IT manager, you must constantly monitor these quadrants and address them in priority to mitigate them from causing any damage to your IT assets.
Software assets management risks must be addressed in a timely manner, no matter how many software licenses you use and vendors you work with. To handle this, you should have a systematic approach that considers both the volume and risk associated with each software vendor.
With this approach, you can classify each software vendor on a 2X2 matrix based on their risk and volume, allowing you to prioritize your efforts based on the quadrant in which each vendor falls.
For instance, high risk with high impact should be prioritized over low risk with high impact. This way, you can focus your efforts on software vendors that pose the most significant risks to the organization while also considering the volume of usage.
Analyzing SAM risks is important for you to understand how it can impact your IT assets and what best approaches you can follow for risk mitigation.
Prioritizing SAM Risks: Classifying by Risk and Volume (No. of incidences)
Here are the key factors to consider for effective SAM:
1. HRHV (High Risk, High Volume)
Did you know using software from mega-vendors like 'Google Workspace' can be a double-edged sword? On the one hand, it can be highly efficient and help streamline your business operations. But on the other hand, without proper compliance measures in place, it can pose a significant operational risk to your organization.
That's where the HRHV quadrant comes in. This quadrant represents software types that are high risk and high volume, and if you're not careful, non-compliance could lead to massive financial penalties and legal issues. But don't fret just yet! By taking proactive steps, you can mitigate operational risks and avoid any nasty surprises down the road.
One way to do this is by engaging the vendor's sales team and aligning internal stakeholders. This ensures that everyone is on the same page when it comes to compliance measures and reduces the likelihood of any discrepancies that may attract unwanted attention from vendor audit teams.
Another way to mitigate operational risks is by keeping an eye on press releases from your company. Any discrepancies in licenses purchased and publicly available employee count could be red flags for vendor audit teams, and by monitoring these discrepancies, you can quickly address any issues and avoid costly penalties.
2. HRLV (High Risk, Low Volume)
As an IT leader, you're always on the lookout for ways to maximize your returns. However, in the world of software management, it's crucial to remember that with "low volume comes high risk." This is especially true in the HRLV quadrant, where specialized software programs carry a high non-compliance risk due to their high unit price.
These specialized software programs include modules in ERP, Database, and IT Server management software that offer great benefits but also come with significant penalties if not properly managed. To make matters worse, some vendors use complicated metrics like Indirect usage, CALs, and Cores, making these software programs even trickier to manage.
The biggest risk associated with these specialized software programs is the financial risk of non-compliance penalties. The penalties for non-compliant installations are very high, and businesses could end up paying a hefty price if they're not careful.
That's why carrying out an internal audit and taking control of software management is highly recommended before sourcing additional licenses. By effectively managing these specialized software programs and ensuring compliance, businesses can mitigate the financial risks associated with non-compliance penalties.
3. LRHV (Low Risk, High Volume)
Are you aware that even some of the most popular software that you use for free on your personal computer may require a license when used in a commercial environment? That's right! The LRHV quadrant houses well-known software such as Winzip, Avast antivirus, TeamViewer, and pdf converters, which are free for personal use but require proper licenses in a commercial setting.
While the risk of non-compliance in this quadrant may be low, it's still crucial to remain compliant, as penalties for non-compliance can quickly increase. However, the good news is that the exposure per computer in case of an audit is much lower than in high-risk software, making it easier to manage.
The primary risk mitigated in the LRHV quadrant is operational risk, which can be easily managed by carrying out remote uninstallations and replacing the software with free alternatives. This reduces the risk of non-compliance penalties and helps businesses save money on unnecessary software expenses.
4. LRLV (Low Risk, Low Volume)
In the LRLV quadrant, businesses risk installing unauthorized and non-business-related software on their systems. This poses a significant threat to the integrity and security of the company's network. The risks associated with this quadrant are mainly operational and reputational.
Employees may install various types of software on their work computers, from educational programs to the latest video game craze. Such software can slow down the system's performance, disrupt business operations, and compromise network security. In addition, installing non-business-related software on work computers may also negatively impact the company's reputation.
However, with proper education and automated tools, businesses can mitigate these operational and reputational risks. Educating employees on the importance of removing non-business software and providing automated tools for removing unauthorized software can help regain control over the company's network and keep it safe from unnecessary risks.
4 Best Practices to Mitigate SAM Risks
Effective SAM is essential for minimizing risk and maximizing the return on investment in your software ecosystem. To achieve this goal, there are several best practices that you can follow to mitigate risk and ensure compliance with licensing agreements.
1. Building a culture of risk management
Building a risk management culture is one of the most important best practices. It involves ensuring that every organization member knows the importance of SAM and how non-compliance can negatively impact the business.
By promoting the use of authorized software, providing training on licensing requirements, and implementing clear policies for software usage, you can create a culture that prioritizes SAM compliance.
2. Regular SAM assessments and updates
Secondly, regular SAM assessments and updates are crucial. This involves taking stock of all software assets, tracking usage and licenses, and identifying potential risk areas. By regularly updating your SAM strategy, you can ensure that your software inventory remains up-to-date and compliant.
3. Engaging stakeholders
Thirdly, engaging stakeholders is essential to successful SAM. This includes working with vendors to obtain licenses, collaborating with IT teams to implement SAM best practices, and communicating with business units to ensure software usage aligns with organizational goals.
4. Monitoring and evaluating risk mitigation efforts
Finally, monitoring and evaluating risk mitigation efforts is critical. By monitoring the effectiveness of SAM processes, you can identify areas for improvement and make adjustments to reduce risk further. Regular evaluations of your risk mitigation efforts can also provide insights into emerging trends and help you avoid potential compliance issues.
Well, to adhere to the best practices for SAM risk mitigation and staying up-to-date with software inventory, look no further than Zluri - an ultimate SMP that specializes in providing comprehensive solutions for SAM risk mitigation.
How Zluri helps with SAM risk mitigation
Are you tired of managing your organization's ever-growing list of SaaS applications? Do you find it challenging to track who is using what and how much it's costing you? If so, Zluri is here to help!
Application Discovery
Are you tired of manually tracking all the SaaS applications used within your organization? Do you worry about compliance risks and security vulnerabilities associated with unknown software? If so, Zluri is here to help you mitigate risk and optimize your software landscape!
Zluri's discovery engine is the most advanced in the industry, using five methods to discover all your apps. These methods include SSO, finance/expense management systems, direct integration with apps, desktop agents, and browser extensions, ensuring no application goes unnoticed.
With Zluri, you have full visibility into your SaaS environment, enabling you to manage your software stack more effectively. Zluri's comprehensive app library, the largest in the world, gives you access to detailed information about each application, including its features, pricing, and compliance information.

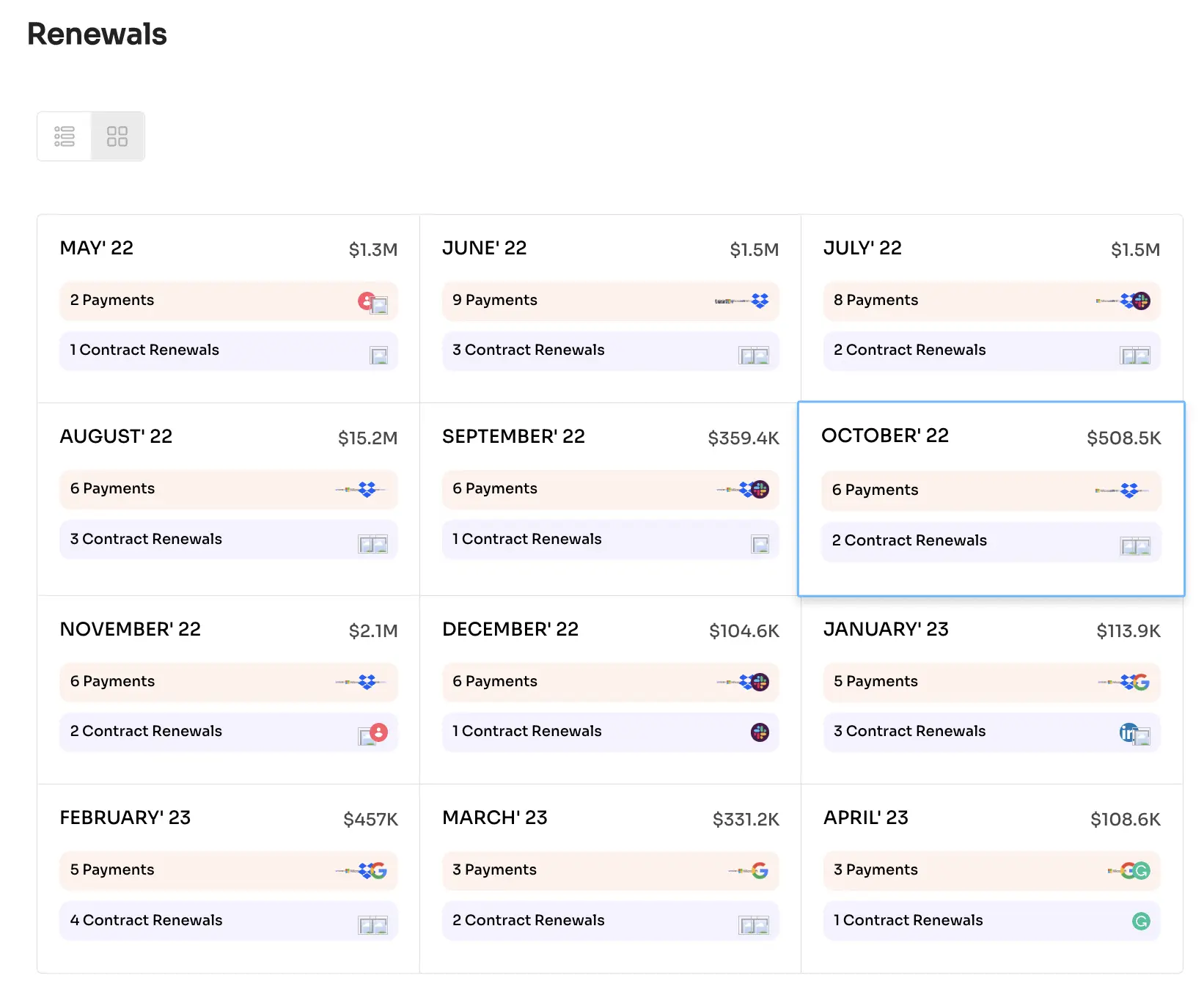
Renewal monitoring
With Zluri's renewal monitoring, you can rest assured that you won't miss any upcoming payments or contract renewals. Zluri alerts you well before upcoming renewals, giving you enough time to decide whether or not you need the app.
Zluri's SaaS Renewal Calendar provides alerts 30 days, 15 days, and 1 day in advance for contracts and 7 days and 1 day for payments. You can even set custom alerts, ensuring that you prioritize high-value contracts.
Using the SaaS usage insights from Zluri, you can make informed decisions about whether to renew or terminate a contract. Zluri also helps you negotiate better deals in terms of cost and terms, leveling the playing field for IT, procurement, and finance teams.
By leveraging Zluri's renewal monitoring, you can mitigate the risks of unknown expenses and unexpected renewals. You can make informed decisions about your SaaS applications, ensuring that you are only paying for what you need and that you are getting the best deal possible.
Cost Optimization
Zluri traces your SaaS ecosystem and monitors, measures, and helps you take control of your SaaS spending. With Zluri, you can easily identify which applications cost you the most money and which are not being used to their full potential.
Zluri's spend optimization reports provide valuable insights on how to optimize your spending across different app categories. Standardizing your applications and eliminating budget wastage ensures your business gets the most out of its SaaS spending.
With Zluri's help, you can optimize your SaaS spending and mitigate the risks associated with overspending on unnecessary applications. By identifying which applications cost you the most money and which are not being used to their full potential, you can make informed decisions about which applications to keep and which ones to eliminate.
Vendor Management
With Zluri, you can easily maintain a SaaS system of record by integrating it with your core business system. This allows for a seamless vendor life cycle management process, with predefined workflows tailored to your business needs.
By using Zluri's vendor management system, you can mitigate the risks associated with vendor management. With automated tracking of vendor contracts and performance, you can quickly identify any potential issues before they become problematic.
Additionally, Zluri's system helps ensure vendor compliance with regulations and industry standards, reducing the risk of legal or financial penalties.
Overall, Zluri helps you mitigate risk in managing your SaaS applications by providing comprehensive visibility, optimizing your SaaS spending, ensuring timely renewals, and streamlining vendor management. With Zluri, you can have peace of mind knowing that your organization is equipped with the best tools to manage your software stack effectively and mitigate potential risks.
What are you waiting for? Book a demo today!
Related Blogs
See More
Subscribe to our Newsletter
Get updates in your inbox
