All Blogs

Zluri Recognized as a Leader in the 2024 Gartner® Magic Quadrant™ for SaaS Management Platforms
Zluri has been recognized as a Leader in the 2024 Gartner® Magic Quadrant™ for SaaS Management Platforms. Zluri was positioned as a Leader in the Gartner® report for our ability to execute and completeness of vision.

Software Renewal Management: A 101 Guide
Learn the essentials of software renewal management to manage & ensure seamless SaaS operations for your business efficiently.

Okta Pricing: A Buyer’s Guide For 2024
Find the best Okta pricing in our 2024 buyer's guide for a cost-effective tier tailored to your business needs.

Events with Zluri: Q1 FY2025 recap
Here we are summarizing the key events we were a part of this quarter and we are delighted to share the key takeaways from these events.

A summary of KuppingerCole's Executive View on Zluri’s SMP and IGA
This report explains how Zluri is one of the few organizations that combines the comprehensive capability to enable centralized visibility, management, and identity governance and administration of all the SaaS applications used by customer organizations.
![Top 20 SaaS Management Platforms [2024]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/1QknrZq2Zh40QxHkAPPegV/56fb3529131774e37623927fc3d60438/Best_30__SaaS.jpg?w=400&h=266&fl=progressive&q=50&fm=jpg&fit=pad)
Top 20 SaaS Management Platforms [2024]
Explore the top 20 SaaS management platforms designed to effectively manage and control your organization's SaaS stack.

Fast-track contract uploads with Zluri’s Smart Contracts
Zluri's AI-powered contract intelligence ingests contract files and auto-populates contract details, saving hours of manual effort. Centralize all your contracts and simplify contract management with Zluri

How to Simplify Audits with Multi-Level Access Reviews
Learn how Zluri simplifies complex audits and streamlines multi-level access reviews to meet compliance requirements

7 Identity and Access Management Trends
Explore the 7 Identity and Access Management trends for 2024 with our comprehensive guide. Embrace the new trends to maintain a secure access environment
Difference Between IAM and IGA
Discover the crucial differences between IAM and IGA. Make informed decisions for robust security and efficient access controls.
User Access Review Process: 5 Key Steps
Dive into details of the user access review process, its importance, how it works, benefits, and a step-by-step guide to implement the process.

Uncover 7 Stages of Procurement Cycle in 2024
Explore the essential guide to procurement cycle from supplier selection to review supplier, gain insights and strategies to optimize your procurement process.

Corporate Credit Card Policy Best Practices - 2024
This article will walk you through the procedure for creating an effective corporate card expense policy and will also show you some of the best practices in managing the spending made through a corporate card.
SaaS User Management: A Comprehensive Guide for 2024
Dive into strategic insights and best practices for efficiently managing user access, permissions, and authentication in your SaaS environment.

Service Accounts Vs. User Accounts: What Is The Difference?
Explore the key differences between service account vs user account with our in-depth comparison blog.

6 Procurement KPIs You Need to Track in 2024
Unlock procurement success in 2024 with our comprehensive guide on the essential 6 procurement KPIs that every business needs to track with our expert insights.

7 Strategies for Segregation of Duties Policy Management
Learn top 7 essential Segregation Of Duties Policy Management strategies to enhance your organization's efficiency and accountability.
Digital Transformation Framework- A Guide For 2024
The perfect digital transformation framework to suit your organization's needs. Explore the ultimate guide and take charge of your digital transformation journey.

Top 20 IT Asset Management Software - 2024
Find the Best IT Asset Management Software that perfectly fits your organizational needs. Organize & maximize your tech investments with our Top 20 Picks!
Top 12 Okta Alternatives & Competitors in 2024
Discover the top alternatives of Okta in both the domains, i.e., lifecycle management and identity governance & administration that can empower your enterprise.
Segregation of Duties (SoD) - A 101 Guide
Understand the challenges, best practices, and the importance of effective Segregation of Duties implementation for robust internal controls & risk management.
SaaS Operations (SaaS Ops) - The Complete Guide
SaaS operations consist of procuring the right set of SaaS apps, managing access to these apps by users/departments, monitoring their usage, and offboarding them properly when they are no longer needed.

Top 10 Mobile Device Management (MDM) Software in 2024
MDM tools enable IT teams to manage, secure and enforce policies on smartphones, tablets, and other endpoints. Moreover, it improves the security and functionality of mobile devices in an enterprise while also keeping the corporate network safe.

A Complete Guide to ISO 27001 Audit
Streamline your ISO 27001 audit process with expert tips and tools to ensure compliance, manage risks, and simplify audits.

ISO 27001 vs SOC 2: 5 Key Differences
Explore what sets ISO 27001 vs SOC 2 apart with the help of our comparison blog

Example Of PHI (Protected Health Information)
Discover the example of PHI & learn about the importance of safeguarding sensitive medical data in healthcare settings.

Top 8 Vendor Management Skills & How to Develop Them
There is a list of skills a successful vendor manager ought to possess. Although some of these skills are crucial for other jobs, they are particularly critical for any position in the vendor management industry.

Segregation of Duties Policy and Procedure: An Overview
Learn how to enhance security, prevent fraud, and streamline operations with our guide on segregation of duties policy and procedure.

7 Identity & Access Management Risks
Explore the 7 identity and access management risks that can jeopardize your organization’s data security.

Vendor Risk Management Policy: A Risk Prevention Measure
With our in-depth guide, explore vendor risk management policy, its importance, steps to create one, and best practices to follow.

What Is HIPAA Omnibus Rule?
Get an overview of the HIPAA Omnibus Rule, its key provisions, requirements, & and its role in protecting sensitive patient information.

Segregation of Duties (SoD) Risks to Address in 2024
Discover key insights into mitigating Segregation of Duties risks & learn how to safeguard your organization from errors & security breaches.

Zluri's Comprehensive Approach to Sensitive Data Security: Safeguarding Your PII
Here's how Zluri built the most secure SaaS Management platform that helps safeguarding your PII data with enhanced approach towards privacy

Top 12 SOC Automation Tools in 2024
12 SOC Automation Tools: 1. Zluri 2.Vanta 3.Drata 4.Scrut 5.Secureframe 6.Sprinto 7.AuditBoard 8.HyperProof 9.Tugboat 10.Logicgate 11.DuploCloud 12.Thoropass.

6 Strategies To Improve Third-Party Security
Discover essential strategies to enhance your third-party security to protect your business from vendor-related risks.

6 Best Network Automation Tools in 2024
Network automation uses software and technology to perform and manage network configuration, provisioning, and maintenance tasks without human intervention.

Segregation Of Duties Matrix Template
Optimize Your Security with our Separation of Duties Matrix Template! Discover how our intuitive solution streamlines access controls and compliance management.

6 Crucial Identity And Access Management Metrics
Explore the 6 key identity and access management metrics curated by our experts to help you detect your organization's IAM system’s performance.

Top 13 Compliance Automation Tools in 2024
Compliance automation tools ensure the protection of specific kinds of data and are governed according to the applicable regulation. For example, specific kinds of patient data need to be protected according to HIPAA regulations.
16 Best Single Sign-on Tools in 2024
In this post, we'll discuss major SSOs available in the market, their features, pros, and cons to make it easy for you to make the right decisions.
Access Provisioning Lifecycle: 5 Key Stages
Learn the stages of the access provisioning lifecycle and discover effective strategies for managing access throughout the process.
Identity and Access Management: A 101 Guide
Learn about Identity & Access Management by exploring components, benefits & best practices for securing digital identities & controlling access to resources.

How To Create A Risk Management Methodology?
A comprehensive guide to risk management methodology, covering standards, & key practices for effective risk mitigation and control.

Contract Renewal Process: All You Need To Know
Learn expert insights and tips for successful contract renewal and streamline negotiations to maximize value for your organization.
9 Step SOX Compliance Checklist
Explore SOX Compliance Checklist guide on adhering to the Sarbanes-Oxley Act requirements to enhance your organization's compliance practices.

6 Essential Steps in User Access Management Audit - 2024
Discover the key 6 steps to streamline your user access management audit process in 2024. Ensure data security and compliance with our expert guide.

A Guide to ISO 27001 IAM Implementation
Boost your data security confidently by adhering to ISO 27001 Identity and Access Management compliance.

Top 12 Subscription Management Tools in 2024
10 Subscription Management Tools 1.Zluri 2.Zoho Subscriptions 3.Sage Intacct 4.ProfitWell 5.Recurly 6.Zuora 7.sticky.io 8.SaaSOptics 9.Billsby 10.FastSpring

ISO 27001 Automation: Enhancing efficiency and security
Understand how ISO 27001 automation transforms your compliance management process, making it more efficient, secure, and streamlined.

Risk Management Framework: Key Components & Best Practices
Our in-depth guide will help you explore risk management frameworks (RMFs), the steps involved in them, the most common frameworks, and best practices.
![Top 12 Cloud Asset Management Software [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/1nAQCdZyGTtEKNPDhVSXGt/beff3e1eeae330dd0f596f95c0eafa4f/Top_12_Cloud_Asset_Management_Software.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 12 Cloud Asset Management Software [2024 Updated]
Explore the top 12 Cloud Asset Management Software for 2024. Stay ahead in the digital landscape by optimizing your cloud asset utilization & management.

Microsoft Entra Vs. Okta: Which IGA Tool To Choose?
Discover the key differences between Microsoft Entra vs Okta to find out which IGA tool best suits your organization's needs.

Best 10 Software License Management Tools in 2024
Software license management (SLM) is part of overall software asset management (SAM). It involves the process of optimizing, documenting, and controlling total IT costs. An SLM tool helps to monitor and maintain all the software licenses of the organization.

Vulnerability Management: Definition & Process
Our comprehensive guide will help you explore vulnerability management, its stages, benefits, challenges, and best practices.

Top 11 User Access Review Tools for Your IT Team in 2024
11 User Access Review Tools: 1. Zluri 2.LogicManager 3.ManageEngine 4. Vanta 5.SecurEnds 6.Lumos 7.Brainwave GRC 8. Cypago 9.ConductorOne 10.Zilla Security 11.Opal

Top 13 Identity and Access Management Tools|2024
Discover the best identity and access management tools. Streamline security & access control with these IAM solutions. Find the perfect fit for your organization

SaaS Contract Management: An In-Depth Guide
Unlock the full potential of SaaS contract management with our in-depth guide for 2024. Explore key insights & tips for effective contract management workflows.

Top 14 IT Service Management Tools (ITSM Tools) in 2024
ITSM tools are very important and play a critical role in managing IT assets' lifecycle. It helps you to make informed decisions based on data and also helps to mitigate any future issues and damages.

Enterprise Access Management - A 101 Guide
Learn the essentials of enterprise access management with our comprehensive 101 guide.

Top 7 Keycloak Alternatives In 2024
Discover the top 7 Keycloak alternatives in 2024 & find the perfect identity and access management solution for your needs.

Top 9 IT Asset Discovery Tools in 2024
Keeping an inventory of all the hardware, software, and services within an organization is essential for ensuring the optimal use of these resources. But, discovering these IT assets is complex, especially for SaaS applications.

ISO 27001 Controls Annex-A: All You Need To Know
This guide covers everything you need to know about ISO 27001 Controls for enhanced information security & regulatory compliance.
9 Identity & Access Management (IAM) Best Practices
Discover the current trends in Identity and Access Management & fortify the security of your digital infrastructure with IAM best practices for 2024.

Top 10 CMMC Compliance Software in 2024
10 CMMC Compliance Software: 1.Zluri 2.Sprinto 3.SecureFrame 4.Drata 5.AuditBoard 6.Scrut 7.Eventlog Analyzer 8.Onspring 9.Logic Manager 10.Comply Assistant

ITIL Service Request Management: A 101 Guide
Discover the benefits and process for streamlining ITIL Service Request Management in your organization to efficiently handle service requests.

CMMC Compliance: An In-depth Guide
Explore what is CMMC compliance, level of CMMC, compliance requirements, benefits, checklist, and CMMC compliance cost with our in-depth guide.
SailPoint Vs. Okta: Which IAM Solution Is The Perfect Fit?
Determine the ideal IAM solution that caters to your SaaSOps team’s needs by closely comparing SailPoint vs Okta core capabilities.

Help Desk Vs Service Desk: 6 Key Differences
Understand the difference between help desk vs service desk with our compassion guide.

GDPR Checklist: Step-By-Step Guide
Explore our step-by-step GDPR Checklist to successfully comply with data protection regulations.

Fine Grained Authorization: An Ultimate Guide
Learn how FGA enables IT teams to define precise access policies, minimize the risk of unauthorized access & maintain compliance with regulatory requirements.

CMMC Certification Cost: How To Manage It?
Learn about CMMC certification costs, the factors influencing certification expenses, & how to manage them effectively with expert tips

Compliance Risk Management: An In-Depth Guide
With our in-depth guide, explore compliance risk management, the steps involved in it, the difference between compliance and risk management, and best practices.

Ephemeral Access: All You Need to Know
Understand what is Ephemeral Access, how does it works, why you need it, and use cases with our comprehensive guide.

SCIM vs SAML: Key Differences
Explore the differences between SCIM and SAML for identity management in this detailed guide, enhancing security and streamlining user data.

Saviynt Vs. Sailpoint: Which IAM Tool To Choose?
Explore the difference between Saviynt vs SailPoint to determine which IAM solution can be a better choice for your organization.

Ticket Statuses: A Guide for IT Teams
Discover the fundamentals of ticket statuses in our guide. Learn how to streamline workflow, improve communication, and enhance user satisfaction.

How To Negotiate SaaS Contracts?
Learn how to negotiate SaaS contracts effectively with our expert tips & secure the best terms for cost, scalability, and support.

8-Step SOC 2 Audit Checklist
Ensure SOC 2 compliance with our comprehensive 8-step SOC 2 audit checklist, covering key requirements for a successful audit process.

SOC 1 vs SOC 2: What Is The Difference?
Our comparison guide will help you understand the difference between SOC 1 and SOC 2 and which one to choose.

Top 10 Essential Soft Skills For IT Teams
From effective communication to problem-solving, the article dives deep into the soft skills for IT teams to elevate productivity, and collaboration.

Complex Contract Management Made Simple With Zluri
Read this blog to explore how Zluri simplifies complex contract management processes, saving time, reducing costs, and enhancing operations.

SaaS Renewal Best Practice for IT and Procurement Teams
SaaS renewal is a crucial part of SaaS vendor management, and it comes under SaaS governance. However, manual renewals can also take weeks if renegotiation is required; hence it is necessary to be prepared.

Access Review Delegation: A Quick Guide
Get a thorough overview of Access Review Delegation. Explore key practices for efficient access reviews, ensuring secure and streamlined processes.
Top 10 Lansweeper “IT Asset Management” Alternatives for 2024
Though Lansweeper is a good IT asset management tool, it has many drawbacks, like it occasionally gets slowed down. There are many other IT asset management tools available in the market which may fulfill your organization's requirements if you're looking for Lansweeper alternatives.

Top 11 IT Service Request Software in 2024
11 IT Service Request Software: 1.Zluri 2.SysAid 3.EasyVista 4.HelpScout 5.Onedesk 6.Integrify 7.HappyFox 8.Invgate 9.ManageEngine 10.Zoho Desk 11.SolarWinds

User Provisioning Policy: 5 Components to Consider
Discover how to manage user access effectively with our guide on user provisioning policies and learn key components to enhance security and productivity.

SaaS Subscription Management: A Detailed Guide
Learn everything about SaaS subscription management & how to handle subscriptions while optimizing your SaaS landscape efficiently.

7 Data Loss Prevention Best Practices
Identifying a data breach can take a significant amount of time. The chief factor that results in such data loss or exposure is the lack of protection.

Coaching Leadership Style: A Beginner's Guide
Learn coaching leadership essentials, effective strategies, and team inspiration for success.

Importance Of Automating Access Requests
Learn about the significance of automating access requests & how automation enhances efficiency and improves security & compliance.

The Best Software Asset Management Tools in 2024
SAM tools play a critical role in managing the software lifecycle. It helps you make informed decisions based on data and helps mitigate any future issues and damages.

7-Step SaaS Security Posture Management Checklist
This post explores the key elements of the SaaS security Posture Management- Checklist, providing insights for building a resilient and secure digital environment.

Ticket Tagging: All You Need To Know To Do It Right
Learn all about ticket tagging and how to do it in the right way with our comprehensive guide.

OKR vs KPI: What Is The Difference?
Our comparison blog will help you understand the difference between OKR and KPI and which one to choose.

15 Best Cloud Management Platforms in 2024
Find the top 15 Cloud Management Platforms in 2024 for efficient cloud management, enhanced security, and cost optimization.

IT Service Desk Metrics To Track for Operational Excellence
Explore 11 key IT service desk metrics that can help measure the effectiveness and performance of your service desk.

Top 9 IT Ticket Management Software in 2024
9 IT Ticket Management Software: 1.Zluri 2.Zoho Desk 3.DevRev 4.HappyFox 5.Jira Service Management 6.ManageEngine 7.Mojo Helpdesk 8.SolarWinds 9.BoldDesk

Top 15 IT Security & Privacy Frameworks
The top 15 IT Security & Privacy Frameworks that help protect your organization's data & ensure compliance with industry standards.
![Top 13 Renewal Management Software [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/6C2CZKwx2hBnzOg8WFF5aj/3e02a60c178a16643e23f76f43d39cf8/Renewal_Management_Software.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 13 Renewal Management Software [2024 Updated]
10 Renewal Management Software: 1.Zluri 2.Vendr 3.Zylo 4.LeanIX 5.AssetSonar 6.Sastrify 7.Revenera 8.Torii 9.CloudEagle 10.Axonius

SaaS License Management: An In-Depth Guide
Our in-depth guide will help you explore SaaS license management, its importance, challenges, and best practices.

Top 8 Service Account Management Tools in 2024
8 Service Account Tools: 0.Zluri 1.ManageEngine 2.Delinea 3.Okta 4.Active Directory Pro 5.CheckPoint 6.CyberArk 7.StrongDM 8.Netwrix

IT Support Requests - An Overview
Discover common issues in IT support requests and a solution to manage them efficiently in your business, enhancing employee satisfaction.

Top 8 Challenges of Cyber Security & How to Address Them
Explore 8 common challenges of cyber security and how you can effectively address them with our in-depth blog.

IT Ticketing System: All You Need To Know
Discover everything you need to know about IT ticketing systems, from benefits to key components and implementation strategies.

IT Asset Management: An Ultimate Guide
Discover what IT asset management is, its types, processes, and best practices to optimize your business operations and maximize ROI.

What Are Excessive Permissions?
Discover what is excessive permissions, the reasons & consequences of excessive permissions and the different scenarios in which they tend to occur.

Top 11 Automated Provisioning Tools in 2024
11 Automated Provisioning Tools: 1. Zluri 2.Okta 3.SolarWinds 4.SailPoint 5.JumpCloud 6.Google Cloud 7.AWS CloudWatch 8.VMware 9.Oracle 10.Lumos 11.BetterCloud

What Is IT Operations (IT ops)?
Learn roles and responsibilities, processes, popular fields of IT operations to optimize your IT infrastructure and drive business success.
What Is An RFQ, RFI & RFP: Detailed Comparison 2024
Learn what is an RFQ, RFI, & RFP. Explore their individual roles & empower your business with informed decision-making with our complete comparison guide.

What Is Access Control? The Beginners Guide
Discover what is access control, how it works, its types, components, core purpose, importance, and best practices with our in-depth guide.
Okta Vs. Cognito: Which IAM Tool To Choose?
Determine which IAM tool is more suitable by closely comparing Okta and Cognito’s key functionalities.
IT Asset Manager Job Description: Roles & Responsibilities
Learn everything about IT asset Manager’s job description. Read this comprehensive guide to gain insights into the roles and responsibilities of this profession

SOX Readiness Action Plan
Understand what is SOX readiness and how an organization can become SOX ready with our in-depth guide.
![Top 10 Contract Renewal Management Software [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/2rmSehQl188quDZkKkYpaN/0154e07684e7cf4bbe299af6a5dab102/Contract_Renewal_Management_software.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 10 Contract Renewal Management Software [2024 Updated]
Discover 10 contract renewal management software and learn how these can optimize your contract renewal processes for greater efficiency and profitability.

SOC 2 Access Control: Challenges & Implementation
Explore the challenges and strategies for implementing SOC 2 Access Controls in this insightful blog.

5 Key Benefits Of Automated Provisioning
Explore the 5 main benefits of automated provisioning and understand how it's far better than your outdated manual method.

Service Desk Ticket Handling Process: 5 Key Stages
Learn about the key steps and effective strategies for service desk ticket handling process in this insightful guide.

Jira Ticketing System: An In-Depth Guide
Explore what is the Jira ticketing system, the stages Jira tickets undergo, benefits, and ways to effectively implement it with our in depth guide.

Just Enough Access: An Ultimate Guide
Explore our in-depth guide to understand the concept of Just Enough Access, its operational mechanisms, and the difference between JIT and JEA.

Events with Zluri: Q4 FY2024 recap
That's a wrap for the Q4 events of 2023-24 fiscal year and here we are, bringing the snippet from the events filled with insights and takeaways.

Internal Ticketing System: A Beginner’s Guide
Discover everything you need to know about internal ticketing systems in this comprehensive guide.
IT Administrator Job Description for 2024
Dive into key responsibilities, crucial skills, and the evolving role of IT administrators in optimizing organizational infrastructure with our article.
Top 9 Microsoft Azure Active Directory Alternatives in 2024
Explore the top alternatives to Microsoft Azure Active Directory in 2024. Find comprehensive solutions tailored to your IT needs.

Identity Providers: What They Are & How Do They Work?
Learn about the role of Identity Providers in digital authentication and access management & how it streamlines user authentication processes across various online services and platforms.
Top 9 User Lifecycle Management Software To Try In 2024
Discover the top 9 user lifecycle management software for 2024 to streamline user onboarding, offboarding, engagement & retention.
8 User Access Management Best Practices
Discover essential user access management best practices to streamline access control, enforce security policies, and prevent unauthorized access.

Top 14 Vulnerability Scanning Tools in 2024
14 Vulnerability Scanning Tools: 0.Zluri 1.ManageEngine 2.Balbix 3.Tenable 4.Intruder 5.Acunetix 6.GFI LanGuard 7.Qualys 8.BeSecure and more.

IT Service Management (ITSM): 101 Guide
Explore what is ITSM, its core components, benefits, best practices, and metrics with our in-depth guide.

Understanding the Different Types of Purchase Orders
Explore the various types of purchase orders and discover their significance in procurement. Ensure smooth transactions with the right PO type.

What Are Service Accounts?
Learn what are service accounts, its types, importance, and best practices to streamline its management process with our comprehensive guide.

8-Step HIPAA Compliance Checklist
Get a jumpstart on compliance with Zluri's complete HIPAA compliance checklist. Stay up-to-date with the latest standards & excellent compliance management!

10-Step ISO 27001 Checklist
Streamline your ISO 27001 compliance journey with our comprehensive checklist and meet regulatory requirements effortlessly.

8 Ticket Handling Best Practices For IT Teams
Explore the 8 ticket handling best practices that will help your IT team streamline the ticket management process.
User Access Management Policy & Procedure
Learn how to enhance security, streamline workflows, and ensure compliance with our expert insights on user access management policy and procedure.

13 SOX Compliance Best Practices
Discover expert-recommended SOX compliance best practices that help ensure the accuracy of financial reports and the effectiveness of internal controls

How To Automate Compliance Workflows?
Learn key steps to automate compliance workflows to enhance compliance management & regulatory adherence in your organization.

How Zluri Helps with SOX Readiness
Discover the top ways in which Zluri streamlines access certification processes, enforces sod policies & provides real-time monitoring to bolster SOX readiness.

Top 11 Identity Governance & Administration (IGA) Solutions
Discover top Identity Governance and Administration solutions to streamline user identity management, access control & compliance for enhanced cybersecurity.

Group Sprawl: What Is It & How To Fix It?
Effective strategies to mitigate group sprawl with advanced access control solutions in 2024. Learn how to manage Microsoft 365 Groups efficiently!

Vendor Access Management: An Ultimate Guide
Explore what is vendor access management, its challenges, core capabilities, and proven strategies for effective vendor access management with our guide.

Master SaaS Budget Planning: A Guide for Finance Team
SaaS budget planning made easy! Explore 5 strategies to manage SaaS budgets effectively and maximize your resources.
6 Single-Sign On (SSO) Best Practices in 2024
Discover how to enhance security, simplify user access, and improve productivity with our comprehensive guide to SSO best practices.

Access Rights Management: A 101 Guide
Explore what is access rights management, how it works, benefits, challenges, and best practices to implement with our comprehensive guide.
Top 10 Components of a SaaS Agreement Checklist
Explore the top 10 components essential for a robust SaaS agreement contract, curated by industry experts with our SaaS Agreement Checklist.
Uncovering The Software Reseller Business Model: A Comprehensive Analysis
Explore the intricacies of the software reseller business model, uncover its benefits, challenges, and find tailored solution for your successful SaaS buying journey!
Zluri + Jamf: Unified Zero-touch Onboarding/Offboarding for devices & apps
With a platform like Zluri, you can easily automate Jamf tasks & user access to devices & applications at ease. Learn how the platforms come together and solve the automated management constraints.
Launching Self-Service Access Requests | Zluri
Zluri's Access Requests help boost user productivity with a slack-first experience, powered by automation under the hood that cuts support times & costs.
SOX 404(b) Compliance: Critical Steps for Preparation
Discover essential steps for preparing for SOX 404(b) compliance, ensuring thorough adherence to regulatory standards and effective internal control systems.

User Access Review Report: Key Components & Importance
This blog post explores user access review reports to bolster security and compliance, providing essential insights for IT teams in today's work environment.

Identity and Access Management Framework: An Overview
Explore the key elements of a robust Identity and Access Management (IAM) framework that enhances security, streamlines user access, and ensures compliance.

Top 15 CASB Software in 2024 (Cloud Access Security Broker Tools)
Cloud Access Security Broker (or CASB) sits between organization users and cloud service providers and monitors the network traffic for enforcing companies' security policies.

Zluri vs BetterCloud: 5 Key Comparisons
Compare key differences between Zluri vs BetterCloud to find the ideal SaaS management platform & streamline your IT operations efficiently.

SOX Automation: A Guide To Simplify Compliance Process
Effortlessly streamline SOX compliance with our SOX automation guide and stay ahead in regulatory adherence.

What Are SOX Controls?
Learn about SOX controls, their importance, and how they promote financial responsibility and transparency.

User Access Review Control: Challenges & Best Practices
Explore the challenges & best practices of User Access Review Control to enhance your organization’s security and compliance.

Top 8 User Provisioning Software & Tools |2024
Explore the top 8 user provisioning software and tools that are designed to effectively streamline user access management.

SOX Compliance Consultants: Critical Skills Required
Discover the essence of SOX Consulting in this comprehensive overview. Explore key insights, when to hire & skills required for SOX consultants.

SaaS Security Posture Management: An Ultimate Guide
Explore what SaaS security posture management is, its importance, how it works, how it's different from other security solutions, and more with our in-depth guide.

SOX Audit: Step-by-Step Process
Discover essential steps for conducting a SOX audit process. Learn how to ensure compliance, identify risks & strengthen internal controls effectively.

The Cost Of SOX Compliance In 2024
The latest insights into the cost of SOX compliance, the financial implications, & compliance strategies to ensure your business stays ahead.

What Is Sarbanes-Oxley (SOX) 302?
Explore what is SOX 302, its requirements, disclosure committee responsibilities, difference between SOX 302 and 404 with our in-depth guide.

Zluri vs Trelica: Which is Better & Why?
Explore the ultimate comparison between Zluri and Trelica, two leading SaaS management platforms. Discover their key features, and which one is suitable for your business needs.
Penalties For SOX Violation
Understand SOX violation meaning and penalties for non-compliance with our comprehensive guide.
Top 8 CMDB Tools for Effective Configuration Management
Unleash optimal efficiency in 2024 with our top 8 CMDB Tools for seamless Configuration Management. Streamline & Elevate your IT operations to new heights.

41% of Enterprises Miss Access Reviews Deadlines, According to Our Research
Our study shows that manual access reviews can be risky. Furthermore, manually verifying who has access to what resources is time-consuming and tedious and makes collaboration difficult

Top 7 Corporate Credit Card Management Software in 2024
It helps organizations streamline their expense management process and gain greater control over their spending. The key features include real-time tracking, automated reporting, fraud detection, and integration with accounting systems.

Zero Trust Identity And Access Management: A 101 Guide
Explore what is zero trust, the role of IAM in zero trust, its key components, and 7 best practices for successful zero trust identity and access management implementation.
J-SOX vs Sarbanes-Oxley Act (SOX): 6 Key Differences
Explore the key differences between J-SOX and SOX compliance to stay ahead of regulatory challenges with expert insights and practical advice.

SOX Walkthrough: Challenges & Best Practices
Discover challenges, best practices, and expert tips to ensure compliance and streamline your internal controls process for a successful SOX walkthrough.

Top 10 IT Change Management Software In 2024
Explore the top 10 IT change management software of 2024 to streamline your IT processes, featuring in-depth analysis and user-friendly tools.
Sox 302 vs 404: Understanding the Difference
Understand the difference between SOX 302 vs 404 with our insightful comparative blog.

Zylo vs Zluri: A Detailed Comparison
Discover your organization's ideal SaaS management platform by closely comparing Zylo and Zluri's key functionalities.

Role Mining: What It Is, Benefits, & Objectives
Discover the power of role mining in simplifying access management. Learn how this streamlines user permissions, enhances security, and operational efficiency.

11 Common SOX Compliance Challenges
Explore the most common SOX compliance challenges organizations encounter while striving to adhere to SOX regulations.

Top 11 Service Request Management Software In 2024
Discover top-notch service request management software with our curated list of 11 expert-recommended solutions.
Access Management: A Comprehensive Guide
Explore what is access management, its significance, difference between identity vs access management, and best practices with our comprehensive guide.

6 Key Considerations for Effective Vendor Assessment
Discover the essential 6 Key Considerations for Effective Vendor Assessment & learn how to evaluate vendors, mitigate risks, and make informed decisions.

SOX User Access Reviews for Publicly Traded Companies
This post discusses the importance of SOX user access reviews for publicly traded companies in ensuring compliance and security.
![Top 12 SOX Compliance Software [2024 Updated] - Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/2fAviWLH06ESqkY23fRYYp/54eb9da7a3ec891f0bcdd2bcdeaffb1f/SOX_Compliance_Software.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 12 SOX Compliance Software [2024 Updated]
Explore the top 12 expert-recommended SOX compliance software that will help your organization seamlessly adhere to SOX compliance requirements.

How to Create an Access Control Policy Template?
Discover the ultimate steps involved in an access control policy template to streamline your security protocols and ensure compliance effortlessly

Zluri vs Torii: Exploring Features, Benefits & Differences
Discover an in-depth analysis of Zluri and Torii, the leading contenders in SMP, and choose the ideal fit for your business requirements.
Top 12 AIOps Platforms in 2024
AIOps is an approach to automate critical activities in IT operations by combining big data and machine learning.
Access Request Management: An Ultimate Guide
Discover strategies for effective access request management to streamline processes & optimize user access permissions to safeguard your organization's data.
Career In Identity And Access Management
Explore the dynamic career in identity and access management and understand its roles, qualifications, skills, and salaries in this comprehensive guide.

How to Implement Identity and Access Management?
This guide outlines key steps and benefits for successful IAM implementation to protect sensitive data, mitigate risks & optimize operational efficiency.

7-Step Pre IPO Checklist for SOX
Get IPO-ready with our 7-step pre ipo checklist for SOX compliance. Ensure your company meets regulations effortlessly before going public.

User Access Review Procedure - An Overview
Ensure data security & regulatory compliance with user access review procedure. Discover steps & benefits for conducting a user access review procedure.

User Access Review Policy: An Overview
Discover the importance of a comprehensive user access review policy and its key components to ensure robust security and compliance. Dive in now!

SaaS Spend Optimization: A Comprehensive Guide
Dive into our comprehensive guide and optimize your SaaS software spending, maximizing value in every investment.
User Access Review Template: 7 Key Components
Streamline your security by staying compliant and reducing risks. Get the latest insights and a comprehensive template to ensure user access is always in check.

7 Best Practices For Service Accounts
Discover the essential best practices for managing service accounts effectively to enhance security, streamline operations, and maximize efficiency.
![Top 15 Procurement Management Software [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/2CV9SE17yXyMT0ETw6fbbh/6f5bb225cfcaa1d2ea6b6ee10e643afd/procurement_management_software.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 15 Procurement Management Software [2024 Updated]
Elevate your procurement processes with the latest insights! Find the top 15 procurement management software to streamline your operations & enhance efficiency.
Access Governance: A 101 Guide
Learn how access governance helps manage user access, enforce security policies & maintain regulatory compliance, ensuring the integrity of sensitive data.

SAM vs. SMP: Why SMP is a Better Option for SaaS Management
Discover the key differences between SAM and SMP, and find out why SMP emerges as the superior choice for SaaS Management.
SOC Vs SOX: An In-Depth Analysis Of 6 Key Differences
Explore the difference between SOC vs SOX compliance with our in-depth analysis Guide. Understand how both of these compliance impacts your organization.
Top 6 IT Operations Management Best Practices
Elevate Your IT Operations: Discover the Top 6 ITOM Best Practices for Streamlined Efficiency and Enhanced Productivity!
8 Best Practices For IT Governance in 2024
Discover the key IT governance best practices to streamline operations, manage risks, and enhance compliance in your organization.

Top 8 User Account Management Software In 2024
Explore the top 8 user account management software designed to simplify and streamline the process of managing user accounts.

What Are Time Based Access Controls? How To Implement Them?
Understand what are time based access controls and how to implement them with our in depth 2024 guide. Explore how to manage access based on time criteria.
What Is Identity Sprawl: The Ultimate Guide For 2024
Understand the key concept of Identity Sprawl, challenges one can face, and best practices to mitigate identity sprawl with our comprehensive guide

User Access Review Best Practices
Learn about user access review best practices to streamline processes, mitigate risks & ensure optimal access control with expert insights & proven strategies.
CyberArk vs. SailPoint: Which IGA Tool To Choose?
Discover the key differences between CyberArk vs SailPoint to find out which IGA solution best suits your organization's needs.
User Access Review Checklist: 6 Key Components
Uncover the 6 key components of a user access review checklist crucial for robust security Master access control data integrity with our comprehensive guide.
![Top 12 Supplier Risk Management Software [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/4jnxc72JvWgMUrWVwzdSbJ/96387735a9541d74a164d932f7cf8cd6/supplier_risk_management_software.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 12 Supplier Risk Management Software [2024 Updated]
Discover the top 12 supplier risk management software to shield your supply chain from potential risks and ensure uninterrupted operations.
User Access Reviews: A 101 Introductory Guide
This blog post explores user access reviews to bolster security and compliance, providing essential insights for IT teams in today's work environment.

Understanding Privilege Creep: Impact & Prevention Strategy
Understand “privilege creep” with our expert guide. Learn how it affects your organization's growth & discover strategies to mitigate it effectively.

SaaS Cost Management: Master Your SaaS Spendings Today
Explore and gain the Secrets to SaaS Cost Management in a Snap – Your Shortcut to Savings and Efficiency!

Top 10 Endpoint Management Software Picks for 2024
Discover your perfect endpoint management software in our top 10 list of tools. Compare, Choose, and Secure your endpoints in 2023!

The Top 8 Software Reseller Programs for 2024
Discover the top 8 software reseller programs of 2024 curated to empower businesses in redefining partnership success & revenue growth.
The Top 8 SaaS Discovery Methods for 2024
Streamline your software utilization for enhanced business efficiency with our guide to the top 8 SaaS discovery methods.
Top 8 Identity and Access Management Training Courses
Discover the top 8 Identity and Access Management training courses to enhance cybersecurity skills and gain expertise in IAM today.

Centralized Vs. Decentralized Access Management
Understand the key difference between centralized and decentralized access management with our comprehensive guide.

Top 4 Identity and Access Management Challenges
New cloud-based IAM solutions are rising favorably as they standardize and streamline identity management. However, when businesses adopt cloud computing, managing administrator access is challenging.
Top 10 Cloud Migration Tools for 2024
Discover the top cloud migration tools of 2024 designed to optimize data migration, enhance security and ensure a seamless journey to cloud-based environments.

Identity & Access Management Maturity Model - A Guide For 2024
Explore the 4 distinct levels of IAM maturity & the 3 key components shaping secure access control in our identity and access management maturity model guide.
Top 8 Identity and Access Management Books
Discover the essential reading list for IT managers with our top 8 Identity & Access Management book recommendations. Unlock insights & enhance IAM strategies.

Identity and Access Management Policy Template - 2024
Discover the ultimate guide to identity and access management (IAM) policy template for 2024. Ensure data security and compliance with this essential resource.

Effective SaaS Risk Management - A Guide for 2024
Learn how effective SaaS risk management can ensure security and resilience & the essential strategies for mitigating risks in your SaaS ecosystem in 2024.
Policy Based Access Control (PBAC) - A Guide for 2024
Explore this comprehensive guide to Policy based Access Control for safeguarding sensitive data & ensuring compliance through effective policy-driven controls.

5 SaaS Management Best Practices (2024 Edition)
Discover 5 SaaS management best practices in our beginner's handbook for 2024. Streamline your organization's SaaS strategy with expert insights.
What Is The Principle Of Least Privilege (PoLP)?
Explore the key concepts, benefits, and best practices of least privilege access principle to enhance security and access control with our in depth guide
Temporary Elevated Access for SaaS Apps
Explore what temporary elevated access is to enhance operational flexibility and learn the key intricacies for a seamless and secure access management process.
Launching Access Management for Modern Enterprises | Zluri
Access management is broken and here's Zluri solving the problem for Modern Enterprises. Extend Access beyond SCIM, Control access to fine grained level and Manage access via Slack.

Why Your SaaS Management Tools Are Failing You
The most important of these is data accuracy. It varies on the kind of discovery engine you use.

Role-Based Access Control: A Comprehensive Guide |2024
Learn how Role-Based Access Control works, benefits, implementation strategies & best practices to enhance security & manage user permissions effectively.

Top 7 Separation of Duties Policy Examples for 2024
Explore examples of separation of duties policy to enhance your organization's internal controls to mitigate risks, prevent fraud & ensure compliance.
Google Workspace Automation - User lifecycle and admin tasks on auto-pilot
We often associate familiarity with trust, a significant factor users consider when purchasing a product. One striking example is Google, which is widely recognized and used by millions of people as their primary search engine.

SOX Compliance: A Comprehensive Guide
Dive into the latest strategies, best practices, and cutting-edge Access Review solutions that streamline your journey to SOX compliance.

Birthright Access - A Comprehensive Guide
Unlock the potential of Birthright Access with our guide and elevate security in your organization. Discover the key to streamlined access management with our innovative solution.

Top 10 Provance Alternatives to Consider in 2024
Null

SCIM Provisioning: A Complete Guide
Unlock the full potential of SCIM provisioning with our comprehensive guide in 2024. Explore the ins and outs of this essential identity management process.
Mastering SaaS Access Management: A Guide for IT Teams
Unlock the key to seamless SaaS Access Management in 2024 with expert insights, best practices & elevate your understanding over access to your SaaS solutions.
![Top 11 Enterprise Access Management Solutions [In 2024]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/iDOA6byt947srAhDDQW4D/ae2cdde23caf57b905bdeec23cc6ed75/Enterprise_access_management_solutions.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 11 Enterprise Access Management Solutions [In 2024]
Explore the top 11 enterprise access management solutions of 2024 and make informed choices to enhance your organization's security and efficiency.
Cost Avoidance vs Cost Savings in Financial Management
Explore proactive measures and strategic approaches that differentiate between cost avoidance and cost savings in financial management.

How User Access Reviews Help Adhere To SOX Compliance
Discover the importance of User Access Reviews in ensuring your organization's strict adherence to SOX compliance.

Streamline Your SaaS Operations With These 5 Workflows
This article will explore five key IT automation workflows to help SaaS companies streamline their operations and take their business to the next level. Whether you're just starting out or have been in the game for a while, implementing these workflows can help you achieve greater success in your SaaS operations.
Optimize IT Efficiency with User Provisioning Workflows
Discover the power of optimized provisioning workflows for businesses. Learn how to automate and accelerate your provisioning processes to enhance efficiency.

What is Conditional Access?
Unlock the power of secure data management and streamline your organization’s data protection strategy with our comprehensive guide to Conditional Access.

SaaS Tracking Template: Keep Track of Your SaaS Apps
If you are having difficulty managing your SaaS apps, this SaaS tracker template will save you time and help you keep track of spending on these apps. This template will also help you plan for upcoming renewal and record license details.
Identity Management Vs Access Management: 5 Key Differences
Discover the differences: identity management vs access management. Learn how they impact security and efficiency in modern businesses.

9 Best Automation Tools for SaaS Operations (and SAM/ITAM) Teams
Automating repetitive and manual tasks not just saves time but also enables IT teams, to focus on more important tasks. Automation ensures consistency on a scale and prevents human error.
Top 10 BetterCloud Alternatives & Competitors in 2024
BetterCloud is a pioneer in the SaaS Management Platform category and it's a remarkable product but that doesn't mean it's right for every company.

Top 11 IGA Solutions for Your Organization in 2024
IGA solutions play a pivotal role in fortifying your organization's security posture. It empowers your team to centrally manage user identities, access rights, and entitlements across various SaaS platforms. IGA minimizes the risk of data breaches, insider threats, and unauthorized access by ensuring users access the right resources.

Top Incident Management Tools in 2024
Information technology (IT) teams use different tools to ensure that work is done properly and end-users are working efficiently. But there is always a chance of deviation or unexpected problems which occur in between the work.
How to Conduct Periodic User Access Review
Enhance your organization's security and compliance efforts with a proactive and thorough approach to periodic user access reviews & their intricacies.

SaaS Portfolio Management: A Comprehensive Guide | 2024
Discover the significance of SaaS portfolio management and explore 6 tried and tested strategies for effective portfolio management.

Things to Consider Before Choosing a Secure SaaS Vendor
Businesses must look at the primary criteria for security and ensure that SaaS vendors meet suitable security measures. As such, the SaaS vendors will have access to critical information about the business processes.
Credential Management: The Ultimate Guide
Discover all about credential management, its definition, importance, and best practices with our comprehensive 2024 guide.

Why Is User Access Review Important?
Understand the significance of user access reviews in the evolving threat landscape with our detailed 2024 guide.

3 Ways to Optimize Microsoft 365 License Costs
After talking with multiple IT managers and analyzing their Microsoft licenses, we almost always find a lot of budget wastage in the form of unused licenses and underused apps.
Top 10 Software Cost Reduction Strategies for 2024
Discover the top 10 proven strategies tailored for software cost reduction in 2024 without compromising operational excellence.

Top 10 Application Portfolio Management Software in 2024
Application Portfolio Management, often known as APM, refers to the process of managing and optimizing inventories of software applications in order to accomplish particular business goals.

5 Best Practices for Microsoft 365 Offboarding in 2024
When an employee exits, what is the first thing that you will do? It's a straightforward answer; you will revoke all the employee's access. However, the catch here is that you have to remove all access immediately, the moment when the employees leave.

How IT Segregation of Duties Helps Strengthen IT Security
Discover the pivotal significance of IT Segregation of Duties (SoD) and the top ways to fortify your organization's security posture.
What is Just in Time Access? It’s Types and Benefits
Explore the Power of Just-In-Time Access. Learn how this enhances security, and empowers businesses to grant access precisely when needed.

What Is Zero Standing Privilege? A Comprehensive Guide
Discover what zero standing privilege is, its significance, its benefits, and how to implement it effectively with our in-depth 2024 guide.
SaaS Evolution: A Strategic Guide to SaaS Change Management
Understand what SaaS change management is and its type, importance, benefits, and strategies to manage change effectively with our in-depth guide in 2024.

Why Is Access Management Crucial For An Organization?
The organization requires flexible and efficient access control solutions to meet the business's needs. This is where access management plays a major role in an organization to overcome all the potential challenges and effectively deal with them by automating the IT processes.

How to Choose an Identity Access Management Tool
When evaluating IAM solutions, organizations should consider the following factors to ensure they select the right tool for their specific needs.
Top 10 Netwrix Alternatives & Competitors | 2024 Updated
The blog discusses the top 10 Netwrix alternatives to address your diverse access governance needs. Find the perfect fit for your organization.
7-Step Identity And Access Management Checklist
Explore our Identity and Access Management checklist designed to enhance your security measures for safeguarding your digital assets effectively.

7 Key Benefits of Identity and Access Management
Enhance security & stay compliant with these 7 benefits of Identity and Access Management. Leverage these IAM benefits & get a more secure digital workplace.

Top 8 Identity Governance Solutions in 2024
Top 8 Identity Governance Solutions in 2024

How to Automate Onboarding Using Zluri
You can use App Catalog & Access Request to provide access to applications to new joiners. It automates the whole SaaS access management process.

Top Employee Experience Tools to Consider in 2024
Employee experience tools have become a vital part of modern organizations, aiming to enhance the engagement and productivity of employees.

User Access Review Audit- How To Keep A Check?
Gain valuable insights into user access review audits & essential practices. Ensure your organization stays secure & compliant with expert guidance.

Top 8 IT Operations Management Tools in 2024
IT operations involve managing IT infrastructure and maintaining the day-to-day activities that keep an organization running seamlessly.
Orphaned Accounts: How To Identify & Mitigate It?
Learn to identify, manage, and mitigate the hidden risks of orphaned accounts. Elevate your data integrity and fortify security with our expert insights.

Role & Responsibilities of SaaSOps Manager (With JD)
The role of a SaaS operations manager is to perform various business enabling tasks that were traditionally performed by the IT department, such as IT asset manager, software asset manager, or the more general IT administrator. The key difference is instead of playing a supporting role; this role is to get the complete benefit SaaS has to offer without the risks.
Top 9 Sophos Alternatives & Competitors in 2024
9 Sophos Alternatives: 0.Zluri 1.Citrix 2.Miradore 3.Ivanti 4.ManageEngine 5.Microsoft 6.Hexnode 7.VMware 8.Scalefusion 9.Trend Micro

What are the Best Practices for SaaS Security?
SaaS security is a crucial component of SaaS management, which encompasses tasks such as discovering SaaS apps, tracking their usage, eliminating shadow IT, duplicating apps, removing unused licenses, and more.
![Top 10 Splashtop Alternatives & Competitors [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/2DNLor8JpxUJgtSQ659h19/6a6764086d0114e51da6d7cfc2f32a19/splashtop-alternatives.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 10 Splashtop Alternatives & Competitors [2024 Updated]
Explore the top-rated 10 HappyFox alternatives in 2024 to effectively streamline the IT service management process.
Top 11 Identity Server Alternatives & Competitors In 2024
Discover the Top 10 Identity Server Alternatives and Competitors for 2024 – Explore the best solutions to meet your identity & access management needs.

Remedying Shadow IT within your organization - A Complete Guide
In this article, you'll learn how to remedy shadow IT and before that, we help you understand the ways in which it affects your organization.
Top 9 Flexera Alternatives & Competitors in 2024
9 Flexera Alternatives: 1.Zluri 2.Augmentt 3.Zylo 4.Bettercloud 5.Binadox 6.ManageEngine 7.AssetSonar 8.Ampliphae 9.Cledara
Top 11 Pipefy Alternatives for IT Teams in 2024
Discover the top 11 Pipefy alternatives for 2024 & compare leading Pipefy competitors to business process automation & streamline business processes efficiently.
Ivanti Alternatives & Competitors: Top 9 ITSM Tools In 2024
Looking for top-rated Ivanti alternatives? Explore our top expert recommendations for 2024 to find the best IT service management solution for your needs.
Forrester’s Latest SaaS Security Posture Management Report Identifies Zluri as a Strong Performer Amongst Top Providers
As SaaS adoption increases, so do security risks. In this Forrester's latest SaaS Security Posture Management report, Zluri is named a Strong Performer amongst leading SSPM vendors. Access the complete report.

SaaS Spend Management: Win the Battle Against SaaS Overspending
Excessive spending on SaaS not only makes you spend more money but imposes security problems too. Learn how a SaaS Spend Management platform helps with this.
Zero Trust vs Least Privilege: 5 Key Differences | 2024
Explore the differences between Zero Trust & Least Privilege in cybersecurity strategies & their core principles, scope, implementation & risk mitigation approaches.

BetterCloud Vs. Okta: Which IGA Solution Is Better?
Understand the difference between BetterCloud vs Okta to determine which one will be a perfect fit for your organization's needs.
Top 9 SysAid Alternatives & Competitors in 2024
9 SysAid Alternatives: 1.Zluri 2.Freshservice 3.Agiloft 4.Solarwinds 5.Jira 6.ServiceNow 7.Microsoft System Center 8.BMC Helix 9.Cherwell
Top 10 Rippling Alternatives for Workforce Management | 2024
Explore the top 10 Rippling alternatives for effective workforce management in 2024 to streamline your HR processes & enhance overall organizational efficiency.

Top Tools to Help you Stay HIPAA Compliant
To stay compliant means adhering to laws, health, safety, data, and security standards set by the land government. For a business to operate, following all the regulatory compliance requirements is essential.

10 Policies to Ensure Reliable SaaS Management
SaaS management is a practice for IT teams to ensure proper use of SaaS resources, maintain a good employee experience, and meet business goals while keeping data safe and secure.

SaaS Spend Management: How Zluri Helps IT Leaders Deal with Budget Cuts?
The SaaS apps are easy to procure, install, use, and update. Therefore, creating effective SaaS adoption strategies for better workflow in business processes is crucial.
CapEx vs OpEx: A Guide for IT Teams
Understand the critical differences between CapEx & OpEx across key business aspects & explore their impact, purpose & management disparities.

6R Strategy for Cloud Migration
An organization's cloud migration strategy includes prioritizing workloads for migration, determining the correct migration plan for each individual workload, developing a pilot, testing, and adjusting the strategy based on the results of the pilot.

How to Automate Zoom With Zluri
One of the major challenges IT teams face is the adoption of streamlined SaaS management for apps like Zoom, let's have a look at how Zluri solves it.

Mastering SaaS Cost Optimization: A Strategic Playbook
Unlock strategies for your SaaS cost optimization operations in 2023 with our playbook. Minimize expenses with these proven strategies & actionable tips.
Appy Pie Alternatives & Competitors To Try In 2024
Explore top 10 Appy Pie alternatives for cutting-edge workflow management & discover powerful platforms that streamline processes & boost productivity.
![Top 9 Zendesk Alternatives & Competitors [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/32PL65Ip8FFwl0fI0pI1u2/c8c6180914aa48e6d079120269d05992/Zendesk_alternatives.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 9 Zendesk Alternatives & Competitors [2024 Updated]
Discover 9 great options instead of Zendesk for 2023. Get better customer support with improved features. Switch today for a smoother experience!

How To Improve Employee Experience - 3 Way For IT Teams
In today's times, employee experience is a critical component of any successful business. With the rise of the gig economy and the proliferation of remote work, employees have more options than ever before when it comes to where and how they work.

How To Do A Successful Procurement Negotiation
During the negotiation process, it is helpful to have an objective that is crystal clear. Therefore, before starting with the discussions, you should ensure that you have a clear head on your requirements.

Effective IT Audit Management: A Guide Fot IT Teams
Think of the audit process as a check-up for your organization; it will reveal any underlying issues that need to be addressed.
SaaS Governance:The Guide to SaaS Excellence| 2024
SaaS Governance - a key driver for business success. Explore how effective governance can streamline operations, fortify security, & maximize cost savings.

7 Biggest Challenges Encountered By IT Teams in 2024
Null

How High-Growth Companies Can Reduce SaaS Spend
High-growth companies are always searching for tools that fuel their operations and expand their financial path. As a result, the amount being spent on these SaaS applications has increased substantially.
![Top 8 Atera Alternatives & Competitors [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/54FmCHvvRD5DhRjiW6GWtc/f6724fba9e129247948529f701789b47/image.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 8 Atera Alternatives & Competitors [2024 Updated]
Explore the 2024 top 8 Atera alternatives & competitors recommended by our experts to simplify the remote monitoring and management process.

Understanding SaaS Compliance: A Guide for IT Teams
Explore what SaaS compliance is and the significance it holds. Besides, discover a comprehensive SaaS compliance checklist for 2024 to build a robust framework.

5 Key Metrics For Review Of User Access Rights
Unlock the key metrics to seamless review user access rights management in our comprehensive article to enhance security and efficiency.
User Provisioning: A Comprehensive Guide
Explore the comprehensive insights into user provisioning, unravel its benefits, & discover how enterprises can leverage automation in this guide.
Federated Identity Management: A Comprehensive Guide | 2024
Learn how federated identity management makes accessing different platforms easier and boosts security. Find out its benefits and how it actually works.
![Top 8 CyberArk Alternatives & Competitors [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/3ySXvmL0WIkP61HdTuuPRb/62d674d0428bfeb276405e2d73471673/CyberArk_alternatives.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 8 CyberArk Alternatives & Competitors [2024 Updated]
Explore best CyberArk alternatives in 2024. Find secure, efficient solutions tailored to your business's IT security needs.
How MDM Tools Help Automate Device Management Tasks?
Explore how MDM tools can automate device management tasks seamlessly with our 2024 in-depth guide.

Top 10 Network Security Tools in 2024
Network security prevents unauthorized access of information or misuse of the organizational network. It includes hardware and software technologies designed to protect the safety and reliability of a network and data.
SaaS Contracts: Types & Key Clauses
Discover the ins and outs of SaaS contracts, explore key clauses, and delve into the nine types of SaaS contracts with our comprehensive guide.

Running Business Impact Analysis for Your SaaS Stack
Though being immune to external risks may not be possible, we think that companies can mitigate most of the risks and safeguard themselves by planning ahead.
404(a) vs 404(b) In SOX Compliance - 6 Key Differences
Uncover the critical distinctions between Sarbanes-Oxley Act 404a & 404b in the respective roles & implications for internal controls & reporting requirements.

Software Asset Management (SAM)- The Complete Guide
Software Asset Management (SAM) is about making getting the most from your software tools while minimizing the risks associated with them.
![How to Choose a SaaS Management Platform? [Updated - 2024]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/6haCFyf7AXV8SxXmTccn8i/e370b39aea7209dcf0e31721de34b937/header__9_.png?w=400&h=254&q=50&fm=png&fit=pad)
How to Choose a SaaS Management Platform? [Updated - 2024]
The discovery engine is the foundation of a SaaS management solution. Any SMP can be only as good as its discovery engine. All the other features, like license, vendor, contract management, spend optimization, etc., are based on the discovery engine.

SaaS Optimization: A Comprehensive Guide
The complete SaaS Optimization Guide tailored for modern IT teams, with the latest updates for 2024. Optimize efficiency & reduce costs with expert insights!
Top 11 Symantec Competitors & Alternatives in 2024
11 Symantec Competitors: 1.Zluri 2.SailPoint 3.Okta 4.ManageEngine 5.RSA 6.JumpCloud 7.Microsoft 8.BetterCloud 9.PingIdentity 10.CyberArk 11.Fischer Identity

Identity & Access Management Strategy: A Complete Overview
Learn the importance and how to create an identity and access management strategy to enhance the organization’s security system with our comprehensive guide.

Business Application Manager Job Description (2024)
Business application managers are responsible for managing one or more computer applications or programs within an organization. The programs may include software such as online stores, customer relationship management systems, pay roles systems, and even manage vendor relations.
Top 10 Kayako Alternatives & Competitors in 2024
Kayako is a cloud-based “Help Desk” software that provides IT teams with a centralized platform for managing employee support inquiries and tickets.

Separation of Privilege Security Principle : A Guide in 2024
Explore the intricacies of the Separation of Privilege Security Principle to defend against security attacks and mitigate potential risks.

The Top 5 SaaS Buying Trends in 2024
While procuring a new solution, the IT procurement team looks for fewer obstacles in the buying process. Adding a new solution to the technology stack should streamline and simplify work instead of making it a complex process.

Cloud Based Software License Management - A Guide for 2024
Explore the latest strategies & innovations in cloud based software license management for 2024 to streamline your organization's license processes efficiently.

Salesforce License Management: Challenges & Best Practices
Uncover common challenges associated with Salesforce license management and explore the best practice with our in-depth guide.
Top 10 Compliance Management Software in 2024
Explore the top 10 expert-recommended compliance software designed to help organizations deal with complex regulatory landscapes.
![Top 10 Uipath Alternatives & Competitors [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/7oUHvJaMBMgFxNj0gnp5pN/4a559fc1c2ce7a04b844431ab945b2ca/uipath_Alternatives.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 10 Uipath Alternatives & Competitors [2024 Updated]
Find the leading UiPath alternatives in 2024 with our updated list of the top 10 options. Get powerful automation solutions tailored to meet your business needs.

Best SaaS Buying Platforms in 2024
SaaS buying platforms help organizations to create a seamless buying experience and establish an appropriate workflow for the buying process.

Top 5 SaaS Security Posture Management Tools
A SaaS security posture management (SSPM) tool ensures that the threats and vulnerabilities are proactively managed. In addition, it reduces the manual workload efforts from security teams by automating various tasks, which helps in mitigating and minimizing the security risks of SaaS applications.

JumpCloud Vs. OneLogin vs Zluri: Which Tool Is The Best?
It also conducts periodic audits and generates reports and analytics that enable IT admins to track employees' activity and identify potential security issues.

SaaS Vendor Management: 101 Guide
Dive into strategic insights that empower businesses to optimize vendor relationships, streamline processes, and maximize the value of their SaaS investments.

Vendor Relationship Management - A Guide for IT Teams
Discover expert advice, best practices & innovative approaches shaping Vendor Relationship Management in 2024 to enhance collaboration & mitigate challenges.
![Top 8 Sonar Software Alternatives & Competitors [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/2gORsFl57ZYhtbgE88dTqq/19723a7c15c2504e3a75bdf54c7a3097/sonar_Software_Alternatives.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 8 Sonar Software Alternatives & Competitors [2024 Updated]
Looking for Sonar software alternatives? Explore our top 8 picks for 2024, featuring in-depth comparisons to help you choose the best solution for your needs.

How to Get SOC2 Certified in 2024
Before you hire a certified public accountants (CPA) firm to run the audit, you can study the audit criteria on the American Institute of Certified Public Accountants (AICPA) website in detail. This will give you a good understanding of the requirements and help you do a self-assessment before the auditing team arrives.

IT Asset Management (ITAM) Best Practices in 2024 Across the Globe
IT Asset Management (ITAM) is a collection of business practices to track and manage the lifecycle of IT assets. It integrates financial, inventorial, and contractual aspects of the IT assets to optimize spending and achieve optimal IT-business alignment.
Attribute Based Access Control (ABAC) - A Complete Guide
Learn how ABAC enhances security by regulating resource access & its advantages, implementation, and significance in modern cybersecurity strategies.

How Zluri Helps With Jamf Automation in 2024?
Discover the power of seamless Jamf automation with Zluri + Jamf Pro integration. Unlock efficiency, enhance user experiences, and stay ahead of the curve.
Top 10 SolarWinds Alternatives For Asset Management |2024
This post discusses the top 10 SolarWinds alternatives for robust asset management in 2024. Get efficient tools to enhance your asset tracking & optimization.
![Top 9 Genuity Alternatives & Competitors [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/2zXgyYlRVkksOCoDh3Pf1Q/8a5812a294bd10d17ebfe78409b0043d/Top_8_Genuity_Alternatives.jpg?w=400&h=266&fl=progressive&q=50&fm=jpg&fit=pad)
Top 9 Genuity Alternatives & Competitors [2024 Updated]
9 Genuity Alternatives: 1.Zluri 2.Jira 3.SolarWinds 4.Zoho Desk 5.Freshservice 6.Halo 7.Zendesk 8.ManageEngine 9.HappyFox

Top 9 OneLogin Alternatives in 2024
Though OneLogin is a good identity and access management tool, it is also expensive. There are many other IAM tools available that may meet your requirements if you’re looking for a cost-effective solution.

8 Proven Strategies For Effective SaaS Data Management
Discover the significance of SaaS data management, unlock the advantages of SMP, and delve into 7 impactful strategies for better data management.

Why Should You Automate Offboarding? And How to Do It
Offboarding is a tedious and challenging process since it requires careful and thorough deprovisioning of all the IT accesses of departing employees.
IT Compliance Audit - A Comprehensive Guide in 2024
Master IT compliance audits with our step-by-step guide. Learn essential tips to safeguard your company against IT risks.

Tackling Tail Spend in SaaS: Managing Unseen Costs
Explore the concept of tail spend, uncover its causes, discover the benefits of an efficient tail spend management system, and learn effective strategies for managing it.
Top 10 Zapier Alternatives & Competitors in 2024
10 Zapier Alternatives: 1.Zluri 2.Celigo 3.Microsoft Power 4.Workato 5.Make 6.Boomi 7.Tray.io 8.Pabbly Connect 9.Mulesoft 10.IFTTT
Software Sourcing Vs Software Procurement: Similarities and Differences
Explore the nuances of software sourcing vs software procurement and understand their key similarities and differences for informed decision-making.
Top 11 Cloud Cost Management Tools To Try In 2024
Explore the top 11 cloud cost management tools of 2024. Streamline your cloud expenses and optimize your resources for better efficiency.
![Top 9 Boomi Alternatives & Competitors [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/3scDszncnExSi4NjHnJNj7/b68f860751d0e2e36ddc54376c9a216f/boomi-alternatives.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 9 Boomi Alternatives & Competitors [2024 Updated]
Explore the top expert-recommended 9 Boomi alternatives & competitors for 2024 that offer better automation and integration capabilities to streamline workflows.
Top 10 Secure Access Service Edge (SASE) Tools in 2024
Explore the transformative world of SASE tools in 2023 and how they are reshaping business security.
Top 10 SailPoint IGA Alternatives To Consider In 2024
Streamline your access governance process with our expert-curated list of the top 10 Sailpoint alternatives for seamless identity governance and administration.

SaaS Procurement: The Right Way To Procure SaaS in 2024
Unlock savings with our ultimate guide to SaaS procurement that equips your IT procurement team with expert insights like benefits, process, and solution.
Privileged User Access Review: Your Ultimate guide for 2024
Delve into Privileged User Access Reviews, understanding their definition and expert-recommended best practices with our comprehensive guide.

Top Technology Trends That CIOs Cannot Overlook in 2024
Technology and business operations are becoming more and more intertwined. The job of CIOs and IT leaders is not limited to IT operations anymore.

A Guide for IT Administrators - Top Interview Questions in 2024
This is to gauge the candidate's understanding of system administration and ability to adapt quickly to unfamiliar situations.

Top 10 Alternatives to Okta Lifecycle Management in 2024
Today, multiple options are available for lifecycle management solutions similar to Okta. This article has compiled a list of 12 alternatives to Okta that have been evaluated and determined to be among the top options in the industry.

What Is Customer Identity And Access Management: Guide|2024
Explore the basic fundamentals of customer identity and access management, its importance, and how it enhances data security with our in-depth 2024 guide

Top 10 Nintex Alternatives in 2024
Pipefy provides automated workflows and centralizes the data forces, including bots and API connectors.
Snow Software Alternatives & Competitors - 2024
Exploring Snow Software alternatives? Dive into our comprehensive reviews and feature analysis of the leading solutions in 2024 to make an informed comparison!
Top 10 Cloud Migration Service Providers in 2024
Discover the top 10 cloud migration service providers of 2024. Ensure your organization's SaaS data is securely transitioned to the cloud.
IT Workflow Management: The Ultimate Guide
At its core, workflow management is all about automating repetitive processes. It involves identifying the steps your team members need to take to complete a specific business goal and creating a set of workflows to streamline those processes.
Top 9 JumpCloud Alternatives & Competitors in 2024
Explore top JumpCloud alternatives in 2024 and find the best directory platform for your IT needs.

Top 10 Network Security Service Providers in 2024
By outsourcing network security, IT and security teams can focus on other critical aspects of their job, such as developing and implementing new IT strategies, managing network infrastructure, and responding to critical IT incidents.

Top 11 IT Risk Management Software in 2024
11 IT Risk Management Software: 0.Zluri 1.Scrut 2.Drata 3.ZenGRC 4.SecurityScorecard 5.LogicManager 6.Oracle 7.Archer 8.OneTrust 9.Sai360 and more.
7 Key Steps to Master Quarterly Access Reviews
Discover the 7 essential steps to master quarterly access reviews and enhance your security protocols with our guide for robust data protection.

Device Access Control: A Comprehensive Guide
Explore the key components, benefits & future-proofing considerations of Device Access Control in 2024 with our comprehensive guide.

Best Salesforce Identity Alternatives in 2024
Salesforce Identity allows IT teams to grant the right access to the right people at the right time. In addition, they can control who can access the organization's data and applications running on the Salesforce platform, cloud, on-premises, and on mobile devices.

Top 8 Zylo Alternatives in 2024 for SaaS Management
Though Zylo is good, it may not be the right fit for your organization, depending on whether you are looking for a SaaS management platform with ease of use, value for money or flexibility to integrate with other tools. There are many other SaaS management tools that may fulfill your requirements.

Top 9 Centrify Alternatives in 2024
Centrify is an identity management solution that assists businesses in adopting, deploying, and managing cloud applications. This facilitates the SaaS app adoption in a secure manner.

Top 12 Data Loss Prevention (DLP) Tools in 2024
12 Data Loss Prevention Tools: 0.Zluri 1.Symantec 2.Forcepoint 3.McAfee 4.Endpoint Protector 5.Digital Guardian 6.Google Cloud 7.ManageEngine and more.

Top 9 Jumpcloud Identity Lifecycle Management Alternatives
With Zluri, you can automate the onboarding and offboarding process, saving IT teams' productive time and eliminating human errors. In addition, you can securely and efficiently grant, modify, and revoke access.

Outlook vs Gmail For Business: Which One Is Better?
Find the ideal email & productivity solution with our comprehensive comparison of Outlook vs Gmail for business. Make the right choice for your organization!

Top 8 Torii Alternatives in 2024
Torii has many limitations, but the major reason organizations may shy from going with it is the low number of direct integrations.

Top 8 Alternatives to Vendr in 2024
We've listed top 8 alternatives to Blissfully and their pros and cons.

Redundant SaaS Apps: A Guide for 2024
Explore the pitfalls of overlapping SaaS solutions and learn strategic approaches to consolidate and optimize your SaaS stack by eliminating redundancies.

Top 10 Access Request Management Tools in 2024
Access request management is a part of IT security operations that prevent unauthorized users from accessing and stealing potential organizational data. It stores user information, their roles, the teams they belong to, and the policies that must be implemented.
![Top 9 Omada Alternatives & Competitors [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/12W42x3wnssmK3jpsYdNYl/bf0e8d17e932ee2f177707e58e8d2ca6/image__98_.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 9 Omada Alternatives & Competitors [2024 Updated]
Explore the 2024 top 9 Omada alternatives & competitors recommended by our experts to simplify identity governance and access management.

Top 6 Identity And Access Management Use Cases in 2024
Discover 6 widely recognized identity and access management use cases curated by our experts.

10 Best IT Certifications In Demand Today (2024)
Discover the top 10 IT certifications in demand in 2024. Stay ahead in your tech career and ensure you're certified in the right areas.

Data Classification: How SaaSOps Managers can Secure Organizational Data
The primary goal of data classification is to regulate the classification, use, disclosure, and security of the company's data, as well as that of its data subjects, in accordance with the needs, contractual as well as regulatory requirements.
![Top 9 AssetSonar Alternatives & Competitors [Updated 2024]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/1VArdeo2CvsfDRpP2wNkxM/810e1ff5d00490a1752cb087c3a360e9/assetsonar_alternatives.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 9 AssetSonar Alternatives & Competitors [Updated 2024]
Discover the top 9 AssetSonar alternatives in 2024 that align with your team's unique needs and elevate your IT asset management strateg
Top 9 MuleSoft Alternatives & Competitors in 2024
9 MuleSoft Alternative: 1.Zluri 2.Workato 3.Zapier 4.Boomi 5.Make 6.Tray.io 7.Kissflow 8.Celigo 9.Apigee

9 Best IBM Security Verify Alternatives in 2024
Symantec IGA provides comprehensive identity and access management solutions and governance to IT teams with its capabilities such as simplified logins, access requests, and access certifications.

Top 4 ITAM Challenges And Solutions to Overcome Them
Improper management of IT assets can lead to vulnerabilities in the organization. Failure to track the hardware and software assets can result in cybersecurity and compliance risks due to easy accessibility to SaaS applications.
![10 Microsoft Entra Alternatives & Competitors [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/3iAhzZb5fQJbmuNEIlBMD9/da227e50a6c83831c07fc664f3c61622/image__27_.png?w=400&h=254&q=50&fm=png&fit=pad)
10 Microsoft Entra Alternatives & Competitors [2024 Updated]
Explore the top 8 Microsoft Entra alternatives for your business needs in 2023. Find the right solution for effective permission management

Top 8 Calero Alternatives in 2024
Torii offers a unified view of SaaS spend and allows IT admins to monitor, categorize, and track expenses in real time. Further ensures you only pay for what you require. How does it do that?
![8 Lacework Alternatives For Cloud Security [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/6iChixq5vFTZGr3HFUtbQs/97ab6d7752d04385d52f056c1872bd16/lacework_alternatives.png?w=400&h=254&q=50&fm=png&fit=pad)
8 Lacework Alternatives For Cloud Security [2024 Updated]
While Lacework offers robust cloud security, there are other user-friendly options to explore. Dive into the top 8 Lacework alternatives for optimal security solutions.
![Top 8 Sastrify Alternatives For SaaS Spend Management [2024]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/5oYHxgtD4mifnNQRrxDVA7/31af910ad81fc6f2ca50146b4aaffb76/image__110_.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 8 Sastrify Alternatives For SaaS Spend Management [2024]
Explore our 2024 top 8 recommended Sastrify alternative that not only offers similar functionalities but also provides additional features to manage SaaS spend.

Reflecting on the Remarkable: 2023 Events Roundup
A year of events and we are here presenting all the insights into the 2023 Zluri events across the world. Fasten your seat belts as we dive deep into the 2023 events roundup.
![Top 11 Cloud Security Posture Management (CSPM) Tools [2024]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/6E7jo67n93syun8bJMdcqb/ab2f62bb49a8460a8f83b188bf75ccd3/Cloud_Security_Posture_Management_Tools_copy.jpg?w=400&h=266&fl=progressive&q=50&fm=jpg&fit=pad)
Top 11 Cloud Security Posture Management (CSPM) Tools [2024]
11 CSPM Tools: 1.Lacework 2.Fugue 3.Prisma Cloud 4.Trend Micro 5.CheckPoint 6.Orca Security 7.CrowdStrike 8.ZScaler 9.Cloud Checkr and more.
Top 10 Forcepoint DLP Alternatives & Competitors in 2024
Discover the leading Forcepoint DLP alternatives and competitors to safeguard your business's sensitive information and maintain data security excellence.
Top 10 CobbleStone Alternatives & Competitors To Try In 2024
Find the Best CobbleStone Alternatives for Efficient Contract Management | Streamline Your Contract Processes with Top 8 CobbleStone Competitors
Top 10 Asset Panda Alternatives & Competitors| 2024 Updated
Seeking Asset Panda alternatives? Explore our 2024 list of top competitors offering advanced features & cost-effective solutions for IT asset management.
Top 9 Mobile Application Management Software in 2024
Dive into the top 9 mobile application management software in 2024 and safeguard your sensitive employee's mobile app data. Make an informed choice now!
What Is SaaS Management: A Comprehensive Guide | 2024
Explore the world of SaaS management with our in-depth 2024 guide. Understand the definition, challenges, strategies and key benefits of SaaS management.
![Top 12 Privileged Access Management Tools [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/5F4a7kQpqq4sNAehptd28w/6cf4d6ec2323a7d04c46a3f51ba54d80/privileged_access_management_software.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 12 Privileged Access Management Tools [2024 Updated]
Explore the top 12 privileged access management tools curated by our experts to manage privileged accounts and access seamlessly.
Top 9 Miradore Alternatives To Try In 2024
9 Miradore Alternatives: 0.Zluri 1.Jamf Now 2.ManageEngine 3.Addigy 4.Fleetsmith 5.AirDroid 6.Esper 7.Lightspeed 8.Kandji 9.Hexnode

What Are SaaS Licenses: Everything You Need To Know
Unlock key insights on SaaS licenses and discover everything you need to know for informed decision-making. Dive into the details now!

Top 8 Cloud Infrastructure Monitoring Platforms in 2024
Null

Top 7 SIEM Tools in 2024
Microsoft Sentinal is a SIEM tool that has been used for decades, as it is known for its security posture. It enables you to stop threats before they affect the organization's structure, and SIEM provides a birds-eye view across the organization.
![Top 10 Netskope’s CASB Alternatives & Competitors [2024]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/3ZjTFxg1Hkb10czoi7NBqo/2a3643fbb4350e18e7b279e233636feb/netskope_alternatives.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 10 Netskope’s CASB Alternatives & Competitors [2024]
Looking for Netskope alternatives? Discover the top 10 CASB tools in the market that might just be the perfect fit for your IT team's needs.

Top 8 Alternatives to Symantec DLP in 2024
There are several other Symantec alternatives that you can check to choose the best solution for your organization.
![Top 11 One Identity Alternatives To Try [2024-Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/6grG9UVODmlV1HF4gZ80UW/a7597f725a250522e4404bef7b16f263/One_Identity_alternatives.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 11 One Identity Alternatives To Try [2024-Updated]
Explore the top 11 One Identity alternatives for robust identity management. Find the solution that fits your security needs in 2024.
Top 10 ConnectWise Automate Alternatives & Competitors |2024
Seeking ConnectWise Automate alternatives? Discover the top 10 contenders in 2024 that offer robust features and competitive pricing for IT management.
Top 9 Axonius Alternatives & Competitors in 2024
9 Axonius Alternatives: 1.Zluri 2.BetterCloud 3.Substly 4.Basaas 5.Torii 6.Productiv 7.Ampliphae 8.Zylo 9.G2 Track
Top 10 BMC Helix Alternatives & Competitors in 2024
10 BMC Helix alternatives: 1. Zluri 2. TOPdesk 3 . Jira 4. Freshservice 5. SysAid 6. SolarWinds 7. Spiceworks 8. BOSSDesk 9. ServiceNow 10. Zoho Desk

Top 10 Data Recovery Software in 2024
10 Data Recovery Software: 0.Zluri 1.Stellar 2.Recuva 3.EaseUS 4.Disk Drill 5.Wise 6.OnTrack 7.R-studio 8.Wondershare 9.Redo Rescue 10.MiniTool
![Top 12 Workflow Automation Tools [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/345el2duBmrchhc7nhJseT/4684db5f7786611cdc0c3f74c0a3429f/workflow_automation_tools.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 12 Workflow Automation Tools [2024 Updated]
Discover the top 12 workflow automation tools designed for IT teams in 2024. Streamline your tasks and boost efficiency – learn how with our in-depth guide.
Top 13 Enterprise Architecture Tools To Try In 2024
Explore the top 13 enterprise architecture tools designed to align your IT and business strategies. Discover the ideal solution for your organizational needs.

Top 19 IT Managed Service Providers (MSPs)- 2024 Updated
Gain top-tier outsourcing services with our best IT Managed Service Providers (MSPs). Enhance your organization's IT processes with increased productivity.
![Top 8 HappyFox Alternatives & Competitors [Updated 2024] - Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/6qcQk4FO2cqV6E9tEsA31Y/43ce0c79a678802b4570902929aadc90/image__35_.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 8 HappyFox Alternatives & Competitors [Updated 2024]
Explore the leading 8 HappyFox alternatives recommended by our experts in 2024 to streamline the IT service management process effectively.

10 SaaS Access Control Best Practices - 2024
Access control systems and processes limit access to sensitive information, such as customer information, employee data, intellectual property, trade secrets, operational or inventory information, and industry-specific data.
Top 9 Auth0 Alternatives & Competitors To Try In 2024
Explore the curated list of top 9 Auth0 alternatives recommended by our experts to help your IT team streamline authentication and authorization process.

Top 11 Access Governance Software for Your IT Teams
We have handpicked the 11 best Access Governance Software with their key features to enhance your access governance strategy and make informed decisions.

Role of IGA In A Layered Approach To Security | 2024
Uncover the intricate layers of security, including MFA and SSO, ensuring a robust defense against evolving cyber threats.

Top G2 Track Alternatives in 2024 (In-Depth Comparison)
This article will discuss the various alternatives to G2 Track that will help your organization save costs and optimize your SaaS stack.
![Top 9 ForgeRock Alternatives [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/1AKEFw8KSzWb8PS03uQ1BI/c76bf31275cc2d86d7ff0e846ec00948/ForgeRock_alternatives__1_.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 9 ForgeRock Alternatives [2024 Updated]
Looking for ForgeRock alternatives? Explore our top picks for 2024 to find the best identity access management solution for your needs.

Privileged Access Management: An In-Depth Guide
Gain insights into what privileged access management is, its types, benefits, importance, best practices, and PAM solution key features with our comprehensive 2024 guide.
Top 12 PCI DSS Compliance Checklist in 2024
Explore the essential 12 components of the PCI DSS Compliance Checklist for 2024. Stay ahead as an IT manager by understanding the intricate details of PCI DSS.
![Top 10 Basaas Alternatives For SaaS Management [2024]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/6wZ95YoTtveTDlCKFZFK7i/56ac38e183eda14deb7ef6ed71980952/Basaas_Alternatives.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 10 Basaas Alternatives For SaaS Management [2024]
Find the 10 best Basaas alternatives for SaaS management: Zluri - SailPOint - Torii- G2Track- Vendor- Apptio Cloudability SaaS - BetterCloud- Subtly-LeanIX- Zylo

Top 8 InvGate Alternatives in 2024
InvGate offers a robust IT service management module, allowing IT teams to streamline service delivery processes and improve service levels. This module includes incident, problem, change, and service level management.

Top 7 Tanium Asset Alternatives for IT Teams - 2024
However, if you are looking for an affordable IT asset management tool, then Tanium Asset may not be the best choice as it involves expensive acquisition costs.
Top 14 IT Process Automation Tools To Try In 2024
Discover the leading 14 IT process automation tools in 2024. Elevate efficiency, simplify workflows, and stay at the forefront with these innovative solutions.

SaaS Challenges that Affect Financial Planning and Analysis
Financial planning and analysis bridge the organization's IT resources to strategic direction. It allows the organization to monitor and analyze the performance against set parameters.

9 Top SaaS Trends for 2024
In this blog, we will go through the new SaaS trends that are about to happen in 2024. Being aware of these trends will help you figure out the important software-related decisions that you need to make as an IT leader.

Top 7 Alternatives to LeanIX in 2024
Though LeanIX is a good SaaS management platform, it is expensive. There are other affordable alternatives to LeanIX that also have the same or more beneficial features.
Top 10 Icertis Alternatives & Competitors To Try In 2024
Explore superior options with our list of the top 10 Icertis alternatives for enhanced contract management. Compare and find the perfect fit for your needs.

Best Alternatives to Intello in 2024
In this article, we will discuss the top alternatives to Intello. But before that, let’s learn more about Intello.

Top 9 IT Alerting Software in 2024
IT alerting software is an operational response automation solution that helps IT teams assess events critically, locate the right people, automate outreach, and improve communication and collaboration.
Top 10 “Track-IT” Help Desk Alternatives In 2024 (ITSM Tool)
Track-IT is a reliable IT help desk software with endpoint management capabilities, allowing your IT teams to log, track, and prioritize user requests and queries.

Zluri + Jamf - Rewinding to the Jamf Nation User Conference (JNUC)
If you missed out on the JNUC event, we've highlighted all the key moments and the overall agenda in this blog of the event at Austin, Texas.
Top 11 Workato Alternatives To Consider In 2024
Explore the top expert-recommended 11 Workato Alternatives in 2024 that offer better automation and integration capabilities to streamline workflows.

Device Lifecycle Management - A Guide for 2024
Explore the intricacies of planning, procurement, provisioning, maintenance & decommissioning in our guide for Device Lifecycle Management in 2024.
Top 10 SaaS Spend Management Tools in 2024
10 SaaS Spend Management Tools: 1.Zluri 2.Quolum 3.Spendesk 4.Ramp 5.Certero 6.Lumos 7.Expensify 8.Brex 9.Airbase 10.SAP Ariba
![Top 15 GRC Software Solutions [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/227l8P85RiT0sXOqp4n8UB/d0ab27955a93a9c84ae2bd4b98f9fc17/grc_software.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 15 GRC Software Solutions [2024 Updated]
Find the top 15 GRC software of 2024 with our comprehensive reviews to help manage your governance, risk, and compliance needs efficiently.
Top 9 Citrix Alternatives & Competitors To Try In 2024
Explore the top 9 Citrix alternatives for 2024. Compare features, pricing, and read expert reviews to choose the best solution for your IT needs.
Top 9 Cledara Alternatives & Competitors in 2024
9 Cledara Alternatives: 1.Zluri 2.Basaas 3.BetterCloud 4.Vendr 5.NachoNacho 6.FlexeraOne 7.G2 Track 8.LeanIX 9.ManageEngine
Top 9 Jamf Connect Alternatives & Competitors in 2024
Discover the leading 9 Jamf Connect alternatives and competitors for 2024. Compare pros, cons, and ratings to find a suitable solution for your IT team.

Top 8 Device42 Alternatives To Streamline IT Infrastructure
Here are some potential drawbacks of the Device42 tool that you should consider:Limited Integration, Steep Learning Curve, High Cost
5 Vendor Relationship Management Best Practices in 2024
Dive into the best practices for strong vendor relationships. Elevate your business efficiency and boost ROI by mastering vendor relationship management.
Top 9 Hexnode Alternatives & Competitors To Try In 2024
9 Hexnode Alternatives: 0.Zluri 1.Scalefusion 2.ManageEngine 3.Miradore 4.Esper 5.Citrix 6.N-able RMM 7.Ivanti 8.Jamf Pro 9.Addigy

Top 8 Snipe IT Alternatives & Competitors For 2024
Discover the top 8 Snipe IT alternatives in 2024 that align with your team's unique needs and elevate your IT asset management strategy.

5 Reasons to Automate Identity Lifecycle Management
With identity lifecycle management, companies can improve productivity, reduce IT workload, and maintain high levels of security.

Top 7 RSA Alternatives 2024
RSA Identity and Access Management (IAM) helps IT teams automate the process of granting and revoking access, improving productivity and efficiency. It provides various identity and access management solutions, including identity governance, access management, and identity assurance.
Understanding the Key Differences Among PAM, PIM, & PUM
Learn the differences between PIM, PAM, and PUM & their unique roles for enhanced data security.

The Essential Steps for Achieving a Zero Trust Security Model in Your SaaS Environment
While building a robust Zero Trust model may seem complex, the key to success lies in teamwork, implementing and enforcing strategies, and a commitment to reaching goals without obstacles.
Top 12 Service Desk Software in 2024
12 Service Desk Software: 1.Zluri 2.Help Scout 3.SysAid 4.Freshservice 5.ZohoDesk 6.Jira 7.ServiceNow 8.ManageEngine 9.Salesforce 10.Spiceworks and more.
Top 8 Duo Security Alternatives For IT Teams To Try In 2024
Exploring Duo Security alternatives? Dive into our in-depth comparisons of the competitors & discover the best fit for your organization’s needs in 2024.

Top 10 Expense Management Software in 2024
10 Expense Management Software: 0. Zluri 1. Expensify 2.Zoho Expense 3. Spendesk 4. Netsuite 5.Rippling 6.ExpensePoint 7.Rydoo 8. Emburse Certify and more.
Top 9 Fortinet’s CASB Alternatives in 2024
The solution has advanced threat protection capabilities, including malware detection and prevention, to help you safeguard your organization from potential security breaches.
![Top 12 Workload Automation Software [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/47zyTIGsfWRV5ozzwb0rEs/97e4177a5aceb241c7c51c1aae15e925/workload_automation_software.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 12 Workload Automation Software [2024 Updated]
Explore top 12 workload automation software for IT teams in 2024 and streamline your tech operations efficiently.
Top 9 Coreview Alternatives & Competitors in 2024
9 Coreview Alternatives: 1.Zluri 2.AssetSonar 3.CloudM 4.G2 Track 5.Genuity 6.Apptio 7.Lumos 8.ManageEngine M365 Manager Plus 9.SailPoint Identity Sceurity
![Top 11 SnapLogic Alternatives & Competitors [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/4ZWtMdlJM9N2Vtwseteek7/5ebbbf055a917cfa203ddb1d5f5dcb0a/image__66_.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 11 SnapLogic Alternatives & Competitors [2024 Updated]
Explore the best SnapLogic alternatives for Intelligent Integration in 2024. Find the top integration solutions to streamline your business processes.

Comprehensive Guide to GDPR Compliance for SaaS Companies
Explore expert insights on assessing GDPR compliance in software as a service effectively. Learn key evaluation strategies in this comprehensive guide.

The Cost of Employee Turnover and its Impact on ITAM, SAM SaaSOps Teams
In the event of an employee departure, IT is entrusted with locking down all systems, changing passwords, and collecting the company's equipment. It's possible that employees may also have access to the company's client list. They may additionally be using BYOD (bring your own device) for performing tasks.

Uncovering the Hidden Risks of SaaS in Your Organization
Despite the benefits, SaaS adoption adds challenges like security risks to IT teams. As more organizations move their data and applications to the cloud, the potential risks of data breaches and cyberattacks increase.

Top 14 Contract Management Platforms in 2024
12 Contract Management Tools: 1. Zluri 2. Icertis 3. Contractworks 4. Trackado 5. Conga 6. ContactBook 7. SpotDraft 8. Ironclad 9. PandaDoc and more.

Top 15 Essential IT Vendor Management Tools for 2024
Discover the top 15 IT vendor management tools for 2024 for revolutionizing vendor relationship management, streamlining operations & enhancing efficiency.
What Is Mobile Device Management System: A Complete Overview
Learn what a mobile device management system is, its components, importance, benefits, and checklist with our in-depth guide.
Zluri joins forces with Syscor to expand in SEA and EMEA
Here is a brief blog on Zluri's partnership with Syscor highlighting how it overcomes the challenges left behind because of decentralization in SEA and EMEA region.
Top 10 Password Management Software To Try In 2024
Discover the top 10 password management tools for 2024, innovative features to empower IT teams in safeguarding sensitive credentials.
Top 11 ManageEngine ITAM Competitors & Alternatives for 2024
Explore the Top 11 Competitors & Alternatives to ManageEngine ITAM for streamlined operations & boosted efficiency.

Top 8 Apptio Alternatives in 2024
Though Apptio is a good SaaS management solution, the occasional errors in it cause frustrating experiences.
What is Identity Governance and Administration? 2024 Guide
Master identity governance and administration for your organization with our in-depth 2024 guide to IGA strategies and best practices.

Top 8 Microsoft System Center Alternatives in 2024
Microsoft System Center smoothens the process of deploying software. This is achieved through features such as automated deployment, which eliminates the need for manual installation procedures, and centralized management, which allows administrators to manage applications and systems from a single console.

Extend the Value of Okta by integrating with Zluri
Zluri+ Okta integration enhances Okta's group-based access with resource-level access control, allowing IT teams and app owners to precisely specify the resources and permissions a user should have within applications.
Centralized Identity and Access Management: A 101 Guide
Explore our in-depth guide on centralized identity and access management. Gain some best practices to strengthen your organization's security.
3 Ways User Access Review Helps Comply With PCI DSS
Explore the expert recommended way on how user access reviews helps adhere to PCI DSS regulatory standard.

Access Management Policy: Ensuring Compliant Access Control
Explore the significance of access management policy, discover its key aspects, and understand the guidelines that need to be adhered to with our in-depth guide
Access Control vs Access Management: 5 Key Comparisons
Unlock the Secrets of Access Control vs Access Management: Discover the Key Differences for a Secure Digital World.

Streamlining Least Privilege Access Automation via Zluri
Discover seamless least privilege access automation with Zluri: simplify complex access controls, enhance security, reduce errors &configure role-based access.
Top 9 RSA Alternatives & Competitors To Try In 2024
9 RSA Alternatives: 1.Zluri 2.OpenIAM 3.ManageEngine 4.One Identity 5.Microsoft Azure AD 6.Bravura 7.Okta 8.Omada Identity 9.ForgeRock

Access Provisioning: A Complete Guide
Unlock the latest insights into Access Provisioning in 2024. Discover strategies, tools, & best practices for efficient user onboarding in this guide.

11 Top User Access Management Tools in 2024
Explore the top 11 user access management tools that can help your IT team effectively manage user access and secure crucial data from security beaches

Spend Analysis: How To Manage Procurement Spend
Spend analysis is the practice of analyzing the spend in a procurement process for business results, reducing costs and increasing efficiency.

Master Service Agreement Checklist: 11 Key Essentials
Ensure your business is thriving with our comprehensive Master Service Agreement Checklist. Don't leave crucial details to chance - get started today!

Top 10 Software Asset Management Service Providers in 2024
Top Software Asset Management Service Providers 1.Zluri 2.Anglepoint 3. SoftwareOne 4.Deloitte 5.Crayon 6.Softline 7.Insight 8.Livingstone

The Complete User Access Management Guide For 2024
Learn the key concepts, importance, and best practices of user access management to maintain data integrity with our comprehensive guide.

7 Identity And Access Management Consulting Companies
Explore the top 7 identity and access management consulting companies that provide expert guidance to streamline the IAM process within your organization.
Identity And Access Management Analyst Job Description
Learn about IAM Analyst’s roles, responsibilities, qualification criteria & salary details with our identity & access management analyst job description guide.

4 Types of SaaS Vendor Lock-ins
In this post, you're going to learn about different types of SaaS vendor lock ins. You'll also learn issues that arise due to SaaS vendor lock-ins, there causes and solutions.
Why is Zluri the Best IGA Platform In 2024?
Discover the unique features offered by Zluri that make it a leading IGA platform in 2024.
Top 10 Zscaler Alternatives & Competitors To Try in 2024
Explore the top 10 Zscaler alternatives and competitors for 2023. Discover powerful options for enhancing your network security and cloud protection.
4 Types of Access Control
Explore key insights on access control & its types to bolster organization's security. Make informed decisions & safeguard sensitive data & assets effectively.
Top 8 Google Workspace Alternatives & Competitors In 2024
Discover the leading alternatives to Google Workspace in 2024. Get the 8 productivity & collaboration tools that offer unique features for your business needs.
Top 12 PagerDuty Alternatives & Competitors in 2024
12 PagerDuty Alternatives:1.Zluri 2.xMatters 3.BigPanda 4.Datadog 5.Rootly 6.Better Uptime 7.AlertOps 8.ServiceNow 9.Jira 10.ServiceNow ITSM 11.Moogsoft 12.Sentry
User Access Reviews: Roadmap to Achieve ISO 27001
Learn how conducting user access review can adhere to stringent ISO 27001 compliance regulation with our comprehensive blog.
RPA vs Workflow Automation: Decoding The Differences
Dive into the automation world with our “RPA vs. Workflow Automation” guide. Explore the differences between these two approaches and which one suits your needs best.
![Top 10 Vanta Alternatives & Competitors [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/42fsUPYEXHKeQfBPre7Qbi/b6c4091eadc13800a66bfda0b042c275/vanta_alternatives.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 10 Vanta Alternatives & Competitors [2024 Updated]
Exploring Vanta alternatives in 2023? Uncover top choices based on accessibility, affordability, user ratings, and more. Find your perfect fit today.
Top 9 Access Rights Management Systems In 2024
Explore the 9 expert-recommended access rights management systems that are designed to effectively manage user access rights within the organization.
Top 8 SysAdmin Tools For IT Teams To Try In 2024
Discover the top 8 SysAdmin tools curated for IT teams in 2024. Streamline your operations with these essential solutions for efficient system administration
Zluri Updates (September 2023) - Compliance Report, Request to Forego, Remove Admin Access
Every month, we will highlight the newest updates to our features so you can get a sneak preview of what's new. We've been working hard to improve your experience by adding new features, and we're ecstatic to show you what we have in store.
SaaS Operations Glossary
Knowing the terms and acronyms used in SaaS operations will help you to communicate and collaborate better.

SaaS Renewal Management: A Guide To Optimize SaaS Renewals
Learn everything you need to know about SaaS renewal management with our comprehensive SaaS renewal management guide.

How to Manage User Access & Permissions in SaaS Applications
Gain expert insights into how to efficiently manage user access and permissions in your organization with our comprehensive guide.

5 Reasons Why You Need a SaaS Management Platform
Discover how implementing a SaaS management platform can help your IT team streamline the IT process in your organization with our in-depth guide.

How to Manage Data Sprawl in 2024: 5 Efficient Ways
Learn 5 effective ways for managing data sprawl. The article’s insights will help you regain access control, streamline operations, and ensure data security.
Pipefy Vs. Kissflow: Which Automation Tool Is Better?
Explore the difference between Pipefy vs Kissflow to determine which automation tool can be a better choice for your organization.

JumpCloud vs Okta vs OneLogin: Which ULM Tool Is Suitable?
Explore the top user lifecycle management (ULM) solutions - JumpCloud, Okta, and OneLogin. Discover the strengths, weaknesses, and unique features of each.

Enhance Google Drive Security: 7 Best Practices To Follow
Our experts 7 best practices to fortify your Google Drive Security! Ensure your digital world stays worry-free with enhanced file and data protection.

Mastering SaaS Integrations: Essential Steps for SMPs
Explore our strategic guide for mastering SaaS integrations. Learn essential steps for seamless integration, enhancing efficiency in SaaS management platforms.

Zluri & HRMS Integration: Automate Onboarding & Offboarding
Streamline HR Processes with Zluri's HRMS Integration for Effortlessly automated Onboarding and Offboarding processes. Make the most out of Zluri's Zero-Touch automation.
Ping Vs. SailPoint: Which IAM Tool Is A Better Choice?
Discover the key differences between Ping vs SailPoint to find out which IAM tool best suits your organization's needs.

Understanding Principle of Least Privilege: In-Depth Guide
Explore the key concepts, benefits, and best practices of least privilege access principle to enhance security and access control with our in-depth guide.

Top 5 Strategies To Reduce Duplicate SaaS Subscriptions/Apps
Optimize Your SaaS Portfolio: Get 5 proven strategies to reduce duplicate SaaS subscriptions/apps. Get more value from your SaaS investments with these top 5 approaches!
SWG Vs CASB: Which Is A Better Security Solution?
SWG vs. CASB: Which cloud-based proxy reigns supreme in safeguarding SaaS app data? Dive deep to discover the ideal solution for modern cybersecurity.

Top 9 Trend Micro Alternatives & Competitors for 2024
Explore the leading Trend Micro alternatives and competitors for robust cloud security solutions. Find the perfect fit for your cloud protection needs.
Top 3 Challenges of Mid-Lifecycle Change Management
Explore the top 3 challenges faced during mid-lifecycle change management. Discover expert insights and effective strategies to navigate transitions smoothly.

6 Ways To Achieve Immediate ROI With Zluri
Discover expert-recommended 6 ways of attaining immediate return on investment (ROI) with Zluri.

Azure AD Vs. SailPoint: How Do They differ?
Explore the key differences between Azure AD vs SailPoint to find out which IAM platform best suits your organization's needs.
Workato vs Boomi: Which One To Choose?
Discover the key differences between Workato vs Boomi to find out which platform best suits your organization's needs.

Top 5 Personal Subscriptions Management Apps 2024 + How to Choose
The subscription business model is booming. Previously dominated by newspapers, magazines, gyms, utilities, and telecommunications firms, more products and services are being offered to more people through subscriptions than ever before

Centrify Vs. Okta: Which ULM Tool To Choose?
Understand the key differences between Centrify vs Okta to determine which ULM platform is a better choice for your organization's needs.

5 Vital Strategies for Unlocking Sustainable Business Growth
Explore 5 vital strategies that will elevate your business, enhance productivity & uncover actionable techniques to unlock lasting success.
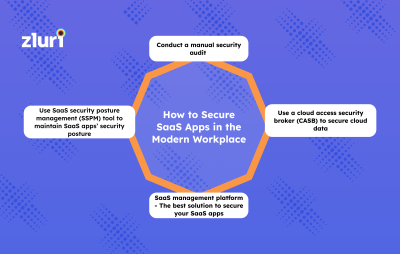
How to Secure SaaS Apps in the Modern Workplace
Factors like lack of centralized SaaS management, poor visibility over SaaS users' data, and improper access distribution are some of the reasons why cloud failures happen. This is why you will need to track high-risk apps and users who access them, their access levels, and the kind of data shared.

5 Best Practices for Mitigating IT Risks with a ULM Platform
Discover the top 5 best practices for effectively mitigating IT risks using a ULM platform to enhance security & ensure seamless IT management.

Vendor Relationship Manager Job Description
Foster Strong Vendor Partnerships | Explore Vendor Relationship Manager Job Description & Responsibilities | Enhance Supplier Collaboration in your organization

OneLogin vs Duo Security: Which IAM Tool is Suitable for Your IT Teams?
Understand the key differences between OneLogin vs Duo Security to determine which IAM platform is more suitable for your organization's needs.
Automate ServiceNow with Zluri's Integration
With Zluri’s direct integration with ServiceNow, you can easily track which users hold licenses & how frequently they use ServiceNow. You can also monitor ServiceNow usage & optimize spend.

How To Get More Out Of Salesforce By Integrating With Zluri?
Learn how to get more out of Salesforce investment by integrating with Zluri with our guide.
JumpCloud vs SailPoint: Which IAM Tool To Choose?
Understand the key differences JumpCloud vs SailPoint to determine which IAM platform is a perfect fit for your organization's needs.
JumpCloud vs Azure AD: Which ULM Tool is Suitable for Your Organization?
Explore the difference between JumpCloud vs Azure AD to determine which one can be a perfect fit for your organization.

How Zluri's Discovery Engine Works
Any SMP is as good as its discovery engine. This is because only depending on the discoverability of the SaaS in an organization the SMP will be able to manage, optimize and secure the applications.

7 Steps For An Effective SaaS Buying Process in 2024
Discover key steps involved in the SaaS buying process to make informed decisions. Streamline your SaaS procurement with our proven roadmap today.

How To Get More Out Of PagerDuty By Integrating With Zluri?
Learn how to optimize your PagerDuty investment by seamlessly integrating with Zluri.

Identity as the New Perimeter: Role of User Access Reviews
Explore the role of User Access Reviews in cloud service & remote work & learn how to keep access privileges in sync with business needs & security standards.

3 Ways to Enhance IT Service Delivery with a ULM Platform
Explore 3 effective ways to enhance your IT operations using a User Lifecycle Management (ULM) platform for streamlined processes & unparalleled performance.
ServiceNow vs Freshservice: Which ITSM Tool Is Better?
Explore the ultimate showdown: ServiceNow vs Freshservice! Discover the perfect IT management solution for your team with our in-depth comparison.

6 Strategies for Securing Privileged Access
Get the top 5 strategies for securing privileged access security within your organization. Safeguard your data with these essential tips.

5 Best Practices For Software License Management
Discover the top effective software license management best practices and understand why they're vital for your business

Cloud Access Governance: In-Depth Guide
Take control of your cloud access governance. Our guide empowers you to manage app and data access effectively. Explore the path to secure cloud operations

Top 4 Ways to Enhance User Offboarding Process
Discover the top 4 ways to enhance your user offboarding process & streamline transitions & retain valuable insights with our expert insights.
All You Need To Know About CIEM: Challenges, Role, & Pros
Gain complete insights into CIEM challenges, its role, and benefits with our comprehensive guide.
5 User Provisioning Best Practices for SaaS Apps
Discover the proven 5 user provisioning best practices recommended by experts.
Workato vs MuleSoft: Which Automation Tool is Suitable?
Explore the key differences Workato vs MuleSoft to determine which automation platform is a perfect fit for your organization's needs.

6 Strategies to Establish A Culture Of IT Service Excellence
Learn the strategies to foster a culture of IT service, improve customer satisfaction, and boost your productivity.
How Zluri Helps You Get More Out Of Freshdesk?
Learn how to unlock the full potential of your Freshdesk investment by integrating with Zluri.

Boomi vs MuleSoft: Which Automation Tool is Suitable?
Discover the ultimate comparison between Boomi and MuleSoft, two leading automation tools to make an informed decision for your business.

Top 5 Components of Microsoft Office 365 Security Checklist
Explore the essential elements of the Microsoft Office 365 Security Checklist crucial for safeguarding your Office 365 environment effectively.

How Zluri Helps You Get More Out Of GitLab (Self Managed)
Discover how Zluri enhances your GitLab (Self Managed)- Integration experience, empowering you to optimize your workflow and productivity.

Okta vs OneLogin: A Comprehensive Analysis of The Two IAM Solutions
Explore a detailed comparison of Okta and OneLogin IAM Solutions with valuable insights and how Zluri proves to be a better fit amongst them.

Automate workflows on Jira with Zluri’s powerful integration
With Zluri’s direct integration with Jira, you can easily track which users hold Jira licenses & how frequently they use Jira. Learn more about Zluri's workflow capabilities.
5 Key Steps of How ULM Simplifies IT Operations
Explore the 5 essential steps of simplifying IT operations with ULM & streamline complex environments, enhance security, and optimize business efficiency.

How You Can Get More Out of Insightly in 2024?
Dive into our guide for effective CRM and project management. Explore the latest strategies to boost your business productivity with Zluri’s automation.
Boomi vs Zapier: Which Automation Tool To Choose?
Explore the key differences Boomi vs Zapier to determine which automation tool is a perfect fit for your organization's needs.

ForgeRock Vs. Okta: Which ULM Tool To Choose For Your Team?
Compare ForgeRock and Okta: Explore their solutions, authentication capabilities, integrations, and pricing to make an informed decision.
7 Best Employee Offboarding Software Tools for IT Teams In 2024
Explore the top 7 offboarding software options recommended by our experts to enhance your IT team's efficiency in managing the employee offboarding process.

Top 4 Ways to Improve User Onboarding Process
Discover the top 4 ways to enhance your user onboarding process & elevate user experience, boost engagement & increase retention with these proven methods.

6 Vendor Management KPIs You Must Track
Evaluate 5 crucial Vendor Management KPIs compiled by our experts to make informed data-driven decisions.

5 Ways to Track SaaS Expenses in 2024
Dive into our essential guide for tracking and optimizing SaaS expenses. Explore proven ways to keep your SaaS spending in check.

How Zluri Helps You Get More Out Of Zoho Projects?
Learn how to optimize your Zoho Projects investment by seamlessly integrating with Zluri.

Saviynt vs. One Identity - Which is The Suitable IGA Tool?
Compare Saviynt and One Identity to determine the best IGA tool for your organization with their features, integrations, and pricing to make the right decision.
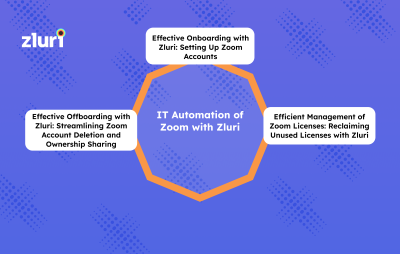
Zoom Automation for IT teams with Zluri
Managing multiple SaaS applications like Zoom can be challenging for IT teams, especially in larger organizations with many employees. Manual management of these applications can be time-consuming, error-prone, and often requires significant resources.
4 Ways to Master Request Management for IT Teams
Effective IT support management is vital for maintaining productivity and minimizing downtime. Streamlining IT support processes can significantly benefit both IT managers and their teams.
How To Get More Out Of Tableau via Integration With Zluri
Learn how to extract maximum value from Tableau - Zluri integration and elevate your business processes to new heights.
How Zluri Helps you Get More Out Of Freshservice ITSM
Unlock the full potential of Freshservice with Zluri. Streamline your IT operations and boost productivity. Discover how Zluri can empower your business today

How to Get More Out of Harvest Via Zluri’s Integration?
Explore our expert guide on maximizing your time tracking and project management capabilities. Elevate your business with Zluri’s automation today!

How Zluri Helps Get More ROI From Okta Investment
Explore the integration of Zluri and Okta to boost your IT team's efficiency and security. Get more out of Okta with Zluri’s automation capabilities.

How to get more out of Asana via Integration with Zluri ?
Unlock the full power of Asana with seamless integration through Zluri & learn how to maximize your productivity and streamline your workflow
MuleSoft vs SnapLogic: Which Is The Better Integration Tool?
Discover which among Mulesoft vs Snaplogic is an ideal integration tool for your business with the help of our comparison blog.

6 Best Approaches For An Effective User Access Review
Learn the top 6 best approaches for conducting an effective User Access Review. Enhance your organization's cybersecurity with expert insights & actionable tips.

Top 3 Reasons Why ULM Tools Fail with Midlife Cycle Changes
Uncover 3 key reasons behind the failure of ULM tools in handling mid-lifecycle changes & insights into enhancing effectiveness of user management strategies.
How To Get More Out Of Slack-Via Automation
Maximize Slack's potential through Zluri automation. Learn how to supercharge your productivity with these efficient automation techniques.
How To Get More Out of Box via Integration with Zluri
Unlock the full potential of Box with seamless integration powered by Zluri. Learn how to enhance your workflow, improve collaboration & optimize productivity.

Top 5 Strategies for Mastering IT Budget Management
Discover the ultimate guide to IT budget management with top 5 strategies. Master financial planning, optimize resources & achieve business goals efficiently.
How Zluri Helps You Get More Out Of Zoho Projects?
Learn how to optimize your Zoho Projects investment by seamlessly integrating with Zluri.

BetterCloud Vs. JumpCloud: Which ULM Tool To Choose?
Determine which ULM tool is a perfect fit for your organization by closely comparing BetterCloud and JumpCloud’s core capabilities.
NetIQ Vs. SailPoint: Which IAM Solution To Choose?
Explore the difference between NetIQ vs SailPoint to determine which IAM solution can be a perfect fit for your organization.

Optimizing User Provisioning for New Employees: A Guide|2024
Learn how user lifecycle management (ULM) tools streamline onboarding, save time, reduce errors & enhance security for new employees.
Everything You Need To Know About Role Modeling In 2024
Learn about role modeling key concepts, challenges, importance, and how Zluri helps in the implementation of role modeling with our comprehensive guide.
ManageEngine ITSM vs SolarWinds ITSM: 5 Key Factors
Compare ManageEngine vs SolarWinds ITSM solutions to find the right fit for your needs. Make an informed decision for effective IT service management

The Top 5 Common Causes of Data Breaches in 2024
Understand the gravity of the top 5 common causes of data breaches and the critical steps to empower your organization against cyber risks.

Separation Of Duties & Internal Controls: What’s The Difference?
The crucial dynamics of Separation of Duties Internal Controls in 2024. Stay updated with the latest insights for effective governance & risk management.
Saviynt vs. CyberArk: Which Is The Best IGA Tool?
Compare Saviynt and CyberArk to find the best IGA solution. Explore their features, security, compliance, integrations, and more to make an informed decision.

8 Proven Best Practices To Optimize IGA
Explore the 8 expert-recommended best practices for effective identity governance and administration with our in-depth guide.

Access Reviews: Understanding the Concept & Key Benefits
Uncover the concept and key benefits of Access Reviews with our informative guide. Enhance your understanding of access management strategies.
4 Practices to Ensure Security through User Provisioning Tools
Explore 4 essential practices to bolster your security with user provisioning tools. Learn the essential steps for a safer digital environment.

How To Implement Zero-Touch Provisioning In Your Company?
Learn the 6 essential steps that your IT team needs to follow in order to seamlessly implement zero touch provisioning in your organization.
How Automated User Access Reviews Help In Secure Offboarding
Explore the proven ways how automated user access helps your IT team securely offboard employees in your organization.

Okta vs. AuthO: Which Tool Is Better To Improve Security?
Explore how Okta vs AuthO differ with the help of our comparison blog.

Top 8 Mistakes to Avoid while Choosing a SaaS Management Platform
Choosing the wrong SaaS management platform can lead to a lack of centralized visibility and control, inefficient cost management, security and compliance risks, manual and error-prone workflows, and limited scalability and flexibility.

Mastering Vendor Management: Top Strategies for CIOs to Drive Success
To succeed in vendor management, CIOs and IT and procurement teams must prioritize vendor relationships. They should identify vendors that align with their organization's strategic objectives and prioritize them based on their importance.
SaaS Sprawl - The Ultimate Guide
When an organization has a large number of SaaS applications in its SaaS stack, it gives rise to SaaS Sprawl.

How Zluri Helps You Get More Out Of Azure AD
Unlock the full potential of Azure AD with Zluri. Discover how our solutions empower your organization in harnessing Azure AD to its maximum capabilities

Netskope vs Zscaler: Which One Suits Your Requirements Better?
Compare Netskope vs. Zscaler: Explore their features, integrations, security capabilities, and pricing to find the best CASB tool for your organization.

6 Best Practices For Effective IT Helpdesk
Explore the proven ways to effectively implement IT helpdesk in your organization. Learn the key insights to streamline support and enhance efficiency.
OneLogin Vs. Azure Active Directory: Which ULM Tool is Suitable?
Compare OneLogin and Azure Active Directory to find the best User Lifecycle Management (ULM) tool for your organization.

7 Mistakes to Avoid while Choosing an User Lifecycle Management Platform (ULM)
To ensure you make the right decision, it's essential to avoid common mistakes that many CIOs like you encounter during the selection process. These mistakes can lead to inefficient workflows, compatibility issues, and missed opportunities to optimize your organization's productivity
Top 7 Cloud Migration Challenges & How To Overcome Them
Cloud migration can help your organization become more agile, efficient, and competitive in today's rapidly evolving business landscape
CASB Vs SMP (Cloud Access Security Broker vs SaaS Management Platforms): Which Is Apt For Strengthening Software Security
CASB and SMP are one such solutions that will guard your enterprise against potential threats.

Revolutionize Your Employee Experience with Zluri’s User Lifecycle Management Platform
Zluri's key capabilities and provides a step-by-step guide for creating onboarding/offboarding workflow, giving insights into how these workflows can enhance your employee experience.

Identity & Access Management for Healthcare- Analyzing the Need
Explore the challenges encountered by the healthcare industry and learn how modern IGA solutions help mitigate those risks with our in-depth guide.

6 Key Features of Identity Governance & Administration Tools
Explore the essential features of Identity Governance & Administration Tools. Discover the power of seamless user management & advanced security.
Automating User Access Reviews: Your Ultimate Guide For 2024
Learn how to automate user access review with our expert guide. Discover how automation can bolster security measures for your organization.
Secure IT Offboarding Checklist - 7-point step for IT and Security teams
Offboarding an employee from your organisation requires diligent and streamlined operations, here is a complete checklist of secure IT offboarding.
How To Effectively Govern Service Accounts?Guide For 2024
Explore the expert-recommended way of managing and governing service accounts to strengthen your organization’s security posture with our in-depth guide

Total Cost Of Ownership & Return On Investment: Key Metrics For Evaluating Your SaaS Stack
Calculating TCO and ROI lets you decide which SaaS apps provide the greatest benefits to streamline your organization’s IT processes.
How to Choose SoD Software: A Guide for IT Teams in 2024
Discover the essential things to consider to select the right SoD (Segregation of Duties) software for your enterprise to streamline compliance and security.
IT Manager Job Description with Role & Responsibilities
The role of an IT manager is to effectively manage the organization's IT processes, ensuring the implementation of technology solutions that best serve the needs of the company. They identify suitable systems and applications that meet the organization's requirements and improve employee productivity.

What Is Identity Governance Framework: Guide For 2024
Learn the core concept of the identity governance framework, its importance, and best practices with our in-depth guide
Top 10 Avatier “Identity Anywhere” Alternatives in 2024
Avatar Identity Anywhere Alternatives: 0.Zluri 1.Microsoft Azure 2.Okta 3.JumpCloud 4.SailPoint 5.Oracle 6.Ping Identity 7.ForgeRock 8.CyberArk 9.RSA

Okta Vs. Duo Security: Which IAM Tool To Choose?
Compare Okta and Duo Security to find the suitable IAM tool for your organization with their features, zero trust strategies, security analytics, and pricing.
RBAC vs. PBAC: 5 Crucial Differences IT Teams Should Know
Compare RBAC and PBAC with their flexibility, use cases, access control, etc. to determine the best access management strategy for your business.
Decoding Access Control: RBAC vs. ABAC - Which Rules the Roost?
Compare RBAC and ABAC to determine the best access management strategy for your business.
RBAC vs. ReBAC: Which Model is Right For You?
Explore the ideal access control model for your requirements in this comparison guide: RBAC vs. ReBAC, helping you make the right choice between the two.

How To Prioritize & Mitigate SAM Risks
Software assets management risks must be addressed in a timely manner, no matter how many software licenses you use and vendors you work with.

Top 7 Finance Compliance Certifications in 2024
Discover the key to financial sector success! Explore the most valuable finance compliance certifications for 2023 in our expert guide.

Identity Governance vs Identity Management
Dive into the differences of Identity Governance vs.Identity Management. Ensure security, compliance & enhance user experience in one comprehensive guide.s.
Process Automation - A Definite Guide for 2024
Process automation is using technology to perform tasks without direct human intervention. It is an increasingly important aspect of modern businesses as it can lead to increased efficiency, reduced errors, lower costs, and improved productivity.

Maverick Spend - The Ultimate Guide (Causes and Ways To Avoid It)
Avoiding maverick spend is crucial for organizations seeking better financial management, maintaining compliance, and safeguarding their reputation.

Reimagining Employee Lifecycle Management with Slack and Zluri
Employee lifecycle management is no longer a chore but a competitive advantage for businesses

Top 10 SoD Software for Your Organization in 2024
The 10 Best SoD Software: 1. Zluri 2.SecurEnds 3.SailPoint 4. Okta 5.ForgeRock 6.One Identity 7.RSA 8.Hyperproof 9.Omada 10.Saviynt.

6 Ways To Implement Least Privilege with Identity Governance
Learn 6 effective expert strategies for implementing least Privilege with modern identity governance to fortify your organization's security & minimize risks
SailPoint vs. OneLogin: Which User Lifecycle Management Tool is Suitable for Your IT Teams?
Compare SailPoint and OneLogin to find the suitable ULM tool for your organization with their features, and pricing to make an informed decision.
Access Recertification - A Complete Guide in 2024
Dive into Access Recertification with our comprehensive guide. Learn the process and steps involved in streamlining access recertification in your organization.
SailPoint vs ForgeRock: Which IGA Tool To Choose?
Discover which among SailPoint vs ForgeRock is an ideal IGA solution for your business with the help of our comparison blog

6 Questions to Ask While Selecting an IGA Software in 2024
Explore the 6 key questions you must ask while choosing the right IGA tool and make strategic decisions to enhance your organization’s security and compliance.

Top 10 Data Access Governance Solutions in 2024
Explore our definitive list of the top 10 Data Access Governance solutions that can safeguard your data security with the right solution in 2023.

Top 9 Apps in Zoom App Store
Null
Zluri's Identity Governance & Administration Platform Overview
Zluri's Modern IGA solution helps companies mitigate security and compliance risks. Govern access to your SaaS for the entire user lifecycle through user provisioning, automated access reviews, and self-service access requests.

Lightspeed leads Zluri’s $20M funding round as SaaS management platform takes off
Fresh funding round to enable growth across North America and expand into Europe. Zluri to double-down on AI as Identity Governance functionality makes an impact with users.

How to Optimize Your Microsoft 365 Licenses with Zluri?
We are pretty sure that the price hike announced by Microsoft in August 2021 wouldn't have faded from your mind yet. At least not for us! Microsoft is like that oldest tradition that businesses never want to give up—but its recent price hike came as a shocker to almost everyone.
Top 8 Alternatives To Hornbill ITSM Tool In 2024
Hornbill is an ITSM software designed to help your IT teams manage IT services and support operations.
Oracle Vs SailPoint: Which IGA Tool Is An Ideal Choice?
We performed a comparison between Oracle and SailPoint based on various parameters that will help you choose the suitable tool for your organization.

Unveiling the Pros and Cons of Shared IT Service Accounts to Manage Your SaaS
Shared It Service Accounts are convenient but they make you compromise on security. Here are the pros and cons of Shared IT Service Accounts.

3 Strategies For CFOs To Optimize Software Spend
Certain challenges hinder CFOs from optimizing SaaS spend. For example, it becomes difficult for the finance team to keep track of SaaS spend while managing a large number of SaaS apps.
Saviynt Vs. Okta: Which IGA Tool To Choose?
Compare Saviynt vs Okta with up to date features to choose the suitable IGA tool for your organization.

Top 10 Software License Tracking Tools
Software license tracking tool helps organizations proactively identify available, deployed and unused, or underused software licenses. Further, it ensures that deployed licenses are aligned with the compliance requirements and helps in keeping audits ready.

Entitlement Management: A Comprehensive Guide
Explore what Entitlement Management is & discover how automated solutions empower efficient control over user access permissions with our 2024 guide.

Reasons Why You Need a Lifecycle Management Platform
It also improves employee experience by eliminating the waiting period to access required apps, which helps increase their productivity and efficiency.
Top 9 Micro Focus NetIQ Alternatives for Your IT Team - 2024
9 Micro Focus NetIQ Alternatives: 1. Zluri 2.Oracle 3. Okta 4.SailPoint 5.Saviynt 6.IBM Security Verify 7.Bravura 8.One Identity 9. Brainwave Identity Analytics

10 Best Applications For IT Teams In HubSpot App Store
If you are looking to enhance your team's efficiency, these apps will surely help take your HubSpot experience to the next level.

How Zluri can Detect and Manage ChatGPT Users for Improved Data Privacy and Security
ChatGPT poses a significant threat to data privacy and security, and it is essential for companies to track and manage its usage.

3 Major Types of Software Licenses & Its Categories
Explore the fundamental types of software licenses and their diverse categories & insights into the diverse landscape of software usage rights and regulations.

Top 10 Entitlement Management Software in 2024
We have handpicked the 10 best entitlement management tools along with their features and ratings. These insights empower you to choose the suitable tool.

Jira Vs ServiceNow: Which ITSM Platform Is Better?
Compare Jira and ServiceNow with their features like incident management, knowledge management, and more to make an informed decision.
9 Leading Oracle IGA Alternatives for Your IT Team
Uncover the Top 10 Oracle identity governance alternatives. Tailor your access governance strategy with the perfect solution that suits your unique requirements

IT Security Solutions: Top Tools To Protect Your IT Assets
IT security solutions refer to a set of tools, technologies, and processes designed to protect digital assets and networks from unauthorized access, theft, damage, or disruption. These solutions include software and services that detect and respond to cybersecurity threats like malware, viruses, hacking attempts, and phishing attacks.

Freshservice vs Zendesk: Which IT Service Management Tool Is Ideal for Your IT Team?
Choosing the Best ITSM Tool: Freshservice vs Zendesk - Optimize Your IT Team's Performance Today and Unleash Efficiency in your Organization!

Saviynt Vs. ForgeRock: Which IGA Tool To Choose?
We performed a comparison between Saviynt and ForgeRock based on several parameters to choose the suitable IGA tool for the organization.

The Power of Collaboration between CIOs and CTOs - Maximizing Organizational Success
Cross-functional teams are a valuable asset for any organization. They bring together experts from different departments to collaborate and solve complex problems.

Strategies for CIOs and CISOs to Work Together Effectively
To mitigate these risks, both CIOs and CISOs must develop a shared understanding of the risks and priorities of their organization. This allows both parties to work together to develop and implement comprehensive security strategies that protect the company from potential threats.
Top 9 Saviynt IGA Alternatives for Your IT Team in 2024
9 Saviynt IGA Alternatives: 1.Zluri 2.Okta 3.Omada 4.Oracle 5.One Identity 6.RSA 7. Symantec 8. ForgeRock 9.IBM. Explore the solutions with their pros and cons.

5 Questions to Ask For Selecting the Best SAM Tool for Your IT Team
An ideal SAM tool contains all the above three integral components to manage software assets. Choosing one will help you enjoy the following benefits: enhanced visibility over your SaaS stack, compliance management, and more.
Top 8 Okta Identity Governance Alternatives To Try In 2024
Explore the list of top 8 Okta identity governance alternatives recommended by our experts to help your IT team effectively manage and govern access

CIO CFO Collaboration - An Essential to SaaS Spend Management
It's a bold move that can transform your company's ability to make wise financial and technological decisions.

Okta vs Keycloak vs Zluri: Which IAM Solution To Choose?
Compare Okta and Keycloak with their features like SSO, lifecycle management, etc. to make an informed decision on choosing the right IAM tool.

Simplifying Endpoint Management - Best Practices for IT Teams
Endpoints are the most vulnerable entry points for cyber attacks, and when compromised can lead to a security breach in the entire organization. With the increasing frequency of cyber-attacks, it's essential to have robust endpoint management in place to protect sensitive data and prevent unauthorized access.
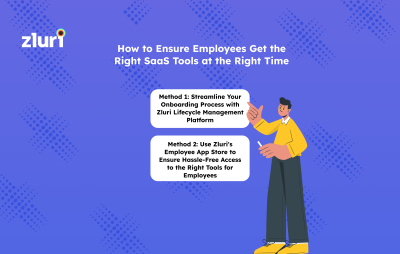
How to Ensure Employees Get the Right Tools at the Right Time
Relying on traditional methods (using tickets-based legacy systems) to manage IT needs may not suffice in today's rapidly evolving business landscape. The tedious and time-consuming process of onboarding employees using traditional methods can frustrate the IT team and the new employees.
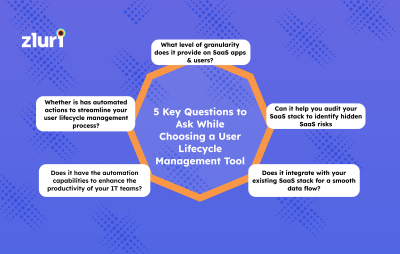
5 Key Questions to Ask While Choosing a User Lifecycle Management Tool
Consider the following questions to unlock the full power of the user lifecycle management tool.

Introducing Zluri APIs - Extensibility Beyond Integrations That Aren’t Off-the-Shelf
Zluri APIs can be called from internal and external applications to create a bridge that helps assign licenses, manage contracts, and a lot more!

Discover the Reports in Zluri’s SaaS Management Platform
Zluri SaaS reports provide you insights into the performance of SaaS applications, usage, adoption, spend, helping CIOs and IT managers make informed decisions about their SaaS investments.

Key Metrics To Track Software Asset Management
Effective SAM can help IT managers avoid these pitfalls by providing accurate inventory management, license compliance tracking, and vulnerability management. IT managers can then make data-driven decisions that reduce costs, improve operational efficiency, and minimize risks by tracking key metrics.
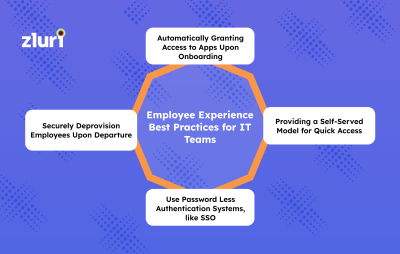
Employee Experience Best Practices for IT Teams
Many organizations today follow manual methods to manage app approvals, so employees need help gaining access to applications to start with their work. They have to wait for several days or weeks and fail to get the right access at the right time, which impacts employees' productivity and reduces efficiency as it disrupts workflow.
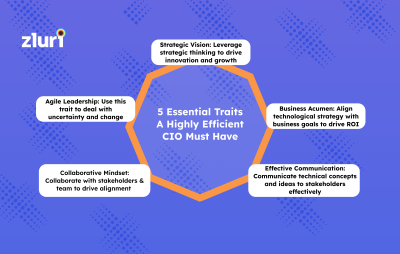
5 Essential Traits A Highly Efficient CIO Must Have
As the job role involves collaborating with multiple stakeholders and executing strategic decisions, you will be required to develop or possess a few traits, no matter whether you are a seasoned or an aspiring CIO.
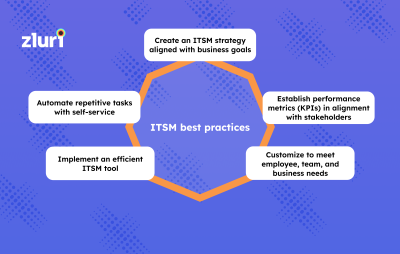
Achieving ITSM Excellence: Best Practices for Organizations
IT Service Management (ITSM) refers to the set of policies, processes, and procedures that an organization follows to design, deliver, manage, and improve IT services. It is critical for IT teams in organizations as it enables them to manage IT services efficiently and effectively.

Top 10 Apps in PagerDuty App Store
PagerDuty's App Store features a range of top apps that provide businesses with the tools they need to manage incidents, automate workflows, and gain real-time insights into their IT infrastructure. From popular tools like Jira, Slack, and AWS to industry-specific tools like Zendesk, Salesforce, and Splunk, PagerDuty's App Store has it all.

Zoom Automation - How Can You Get More Out Of It?
Unlock the full potential of Zoom automation and discover how it can elevate your productivity and efficiency, maximizing your Zoom experience
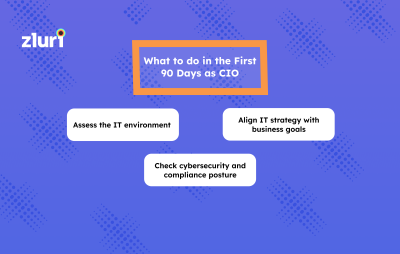
What to do in the First 90 Days as CIO
When a new CIO enters an organization, the first 90 days of a CIO's tenure are critical for setting the stage for success in the role. Therefore, the CIO should focus on learning the organization's culture, processes, and technology infrastructure during this time.

Navigating Cybersecurity in the Age of SaaS: Insights from Todd Dekkinga, CISO @ Zluri
We sat down with Todd to discuss challenges faced by modern IT teams, the evolving role of a CISO, and how one can catch up with the latest trends.

Workato vs Zapier: Which Tool Perfectly Meets Your Requirements?
Compare Workato and Zapier with their features and pricing structure to find the best solution for your business needs.
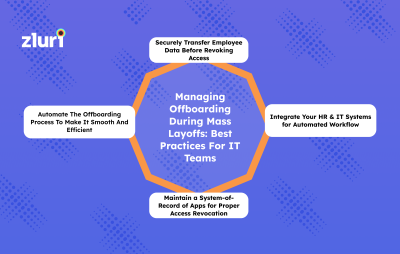
Managing Offboarding During Mass Layoffs: Best Practices For IT Teams
Offboarding employees becomes quite a task during mass layoffs. This is because it comes with tight timelines, making it challenging for you to revoke access for many employees from different job roles or departments on time.

Ping Identity vs. Okta vs Zluri: Which Is Better Fit For You?
Compare Ping Identity vs Okta with their features, use cases, integrations, and more to choose the suitable solution for the organization.

Okta vs Active Directory: Which Identity Management Tool is Right for Your Organization?
Compare Okta vs Active Directory to find the best identity management solution for your business.
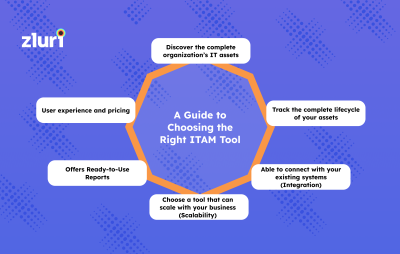
A Guide to Choosing the Right ITAM Tool
The first step in choosing the right ITAM tool is understanding IT teams' needs. Identifying the organization's size and complexity of the IT infrastructure, including the number and types of IT assets that need to be managed, will help IT teams determine the organization's specific IT asset management needs.

Zendesk Vs ServiceNow Vs Jira: Which ITSM Platform To Choose?
We compare Zendesk, ServiceNow, and Jira with their capabilities and pricing structure to help you choose the suitable ITSM solution for the organization.
Jira Vs Freshservice: Which ITSM Tool Is Better?
Comparing Freshservice & Jira: Discover which ITSM tool best suits diverse business needs, from startups to IT industries.
Remedy vs ServiceNow: Which is the Suitable ITSM Solution?
Remedy vs. ServiceNow. Explore which solution is suitable in this in-depth comparison article. Make an informed choice for your ITSM needs!
IT Risk Assessment - All You Need to Know
A key advantage of IT risk assessment is that it helps IT teams gain visibility into current and emerging risks that may potentially affect the organization's operations, assets, and intellectual property to mitigate the security risks.

Zendesk Vs Jira: Which Is The Better ITSM Tool
Discover the ideal ITSM solution for your IT team needs by closely comparing Jira service desk and Zendesk’s key functionalities.
User Provisioning Mistakes to Avoid
While balancing these two tasks, IT teams can make several mistakes in the user provisioning process that can impact the organization's security posture and operational efficiency.
How To Optimize User Access Requests & Approvals for SaaS Tools
Efficient monitoring and tracking of access requests also help detect and address suspicious activity. This results in improved user productivity and optimized access management.
How to Improve IT Procurement & Sourcing
Effective IT procurement and sourcing have evolved from just a support function to a key driver for success in the technology-driven world. With the rapid evolution of technology, IT leaders must ensure that they procure and source the right IT solutions and services that align with their overall business strategy, goals, and budget.
4 Best Practices for User Lifecycle Management
With efficient ULM best practices in place, IT teams can manage user access to company resources, prevent unauthorized access, streamline the onboarding and offboarding process, and reduce the risk of data breaches.
Factors to consider before purchasing a SaaS software
Refrain from letting the complexity of the SaaS buying process deter you. Instead, use it as an opportunity to uncover what your team values most from purchase to purchase. Discussing these points and defining the parameters before negotiations can simplify buying and guarantee you get what you need without any issues.
Ivanti vs Freshservice: Which ITSM Tool is Better?
Explore the key difference between Invanti vs Freshservice to find out which ITSM tool is well-suited for your organization.
Understanding Data Loss: Causes, Prevention, and Best Practices
Data loss refers to any process or event that leads to data being destroyed, erased, or made unreadable by a user and/or program or application. It is when information is destroyed intentionally or accidentally and can be caused by people or processes inside or outside of an organization.
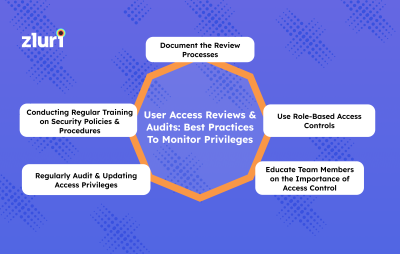
User Access Reviews & Audits Best Practices To Monitor Privileges
User access reviews and audits are critical to data security and access management. It involves regularly assessing and reviewing user access privileges to various systems, applications, and data within an organization.

Top 7 Configuration Management Tools
Configuration management controls changes to an organization's IT infrastructure, including hardware, software, and network settings. This process is essential for ensuring that applications run smoothly, without conflicts or errors, and integrate with your existing systems.

Top 7 Binadox Alternatives
Null

How to Automate Identity Lifecycle Management
Ever thought about what processes are involved in establishing lifecycle management? If not, here we discuss it in detail.

Reducing the Risk of SaaS Sprawl with the Power of Automation
To prevent SaaS sprawl, it is essential to have centralized app procurement and employee training. IT managers should also establish automation models to develop and analyze organizational SaaS inventory and ensure that apps and users are properly tracked and monitored.

Okta vs CyberArk: Which Tool is The best?
After learning the difference between Okta and CyberArk, you might have better understood which tool will be optimal for your business process to enhance productivity and increase efficiency.

How Zluri Automates Identity Lifecycle Management to Reduce IT Friction
Furthermore, it streamlines IT processes such as provisioning new hires, setting permissions and access levels, monitoring unauthorized activity, and revoking access when necessary.

Collaborate with these 5 Stakeholders for a Successful SaaS Management
Collaboration of stakeholders is the key to well-structured SaaS management. It streamlines the process of managing SaaS apps in the organization and enhances the decisions. Also, it helps to mitigate security and compliance risks.
Workforce Identity and Access Management: An Ultimate Guide
Explore the power of workforce identity and access management to streamline security protocols, enhance productivity, and safeguard sensitive data effectively.

Top Tools for IT Teams in 2024
The tools range from monitoring and analytics software to task management and collaboration tools. With the right set of tools, IT professionals can automate repetitive tasks, reduce manual errors, and streamline workflows.

4 Key Points To Consider While Buying An ITSM Tool
Choosing an appropriate ITSM tool consumes a lot of time as various high-quality ITSM solutions are available in the market.

Upgrade Your SaaS Selection: The Ultimate Software Evaluation
Selecting the right software tool can be daunting, but making the right choice is critical for your business. Whether you want to improve productivity or enhance collaboration, finding the right SaaS solution can make all the difference.

Automate User Provisining with Zluri Lifecycle Management Platform
Zluri, a User Lifecycle Management tool, enhances productivity by granting access to new employees on day one.

4 Innovative Secrets To CIO's Success
Do certain CIOs possess a unique quality or some secrets that set them apart from others? Well, yes. Innovative CIOs have a clear vision for how technology can drive the business forward and can communicate that vision effectively to stakeholders.

6 Key Metrics to Track for Improved SaaS Stack Management
Monitoring these metrics helps you take measures to mitigate the risk of a breach. Further, Using SaaS reports, you can identify trends and patterns in application usage, which leads to informed decisions about which applications to keep and remove.

How Zluri Lifecycle Management Tool Helps with Audit & Compliance
Manually doing the audits to review the app approvals, employee activities, and app compliance can give inaccurate results and numerous errors.

SaaS Vendor Compliance: Essential Tips for CIOs
Imagine a scenario where a vendor's software system experiences a sudden crash, causing significant disruption to your organization's operations.

Top 8 Microsoft 365 Management Software
It gives IT teams a centralized view of the entire IT infrastructure that helps manage and monitor the office 365 environment.

Zluri - An Integrated Lifecycle Management platform
Zluri is a cloud-based lifecycle management platform that allows IT teams to streamline employee lifecycle management.

Zluri - An Intelligent User Lifecycle Management Platform
The short answer is 'contextual app recommendations' and 'in-app suggestions'. Read on to know more in detail.

User Provisioning - A Comprehensive Guide to Manage User’s Lifecycle
User provisioning has become challenging with the rise of hybrid work and the increased use of cloud-based services. This is because third-party providers often manage these services, making it difficult to control user access.
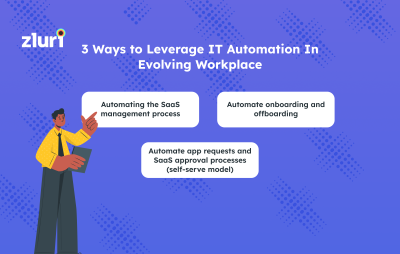
3 Ways To Leverage IT Automation In Evolving Workplace
As evolving businesses focus on saving cost and time and want to receive better results with every project, you should push these tools to their fullest potential. Thus, if you still desire more efficiency, leveraging automation is the most productive way.
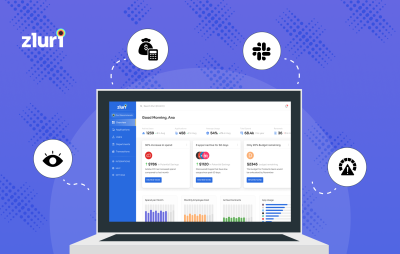
Zluri Lifecycle Management Overview
Zluri lets you automate each step of an employee's lifecycle in the organization, i.e., onboarding, mid-lifecycle, and offboarding. However, aligning the available resources with each stage of the employee lifecycle is challenging. In addition, the increasing SaaS sprawl and shadow IT can lead to huge expenses and underused apps.

How CIOs become IT thought leaders
An IT thought leader is an individual or organization recognized as an expert in their industry or field and consistently influencing and shaping the opinions and decisions of others. This distinction is earned through a combination of expertise, experience, innovative ideas, and a proven track record of delivering results.
How does Zluri Lifecycle Management Enhance Productivity & Security?
Plus, the tool even gives all apps a risk and threat score, determining their potential risk to your ecosystem. With Zluri, IT teams can know that their employee's lifecycle management is in good hands.

Why Procurement Needs SaaS Management?
A rise in SaaS adoption has led procurement teams to choose SaaS. This is because they're easily accessible and less expensive than on-premise software. Therefore, they must consider the cost benefits of SaaS and cloud-based solutions.

The 10 Best iPaaS Software in 2024
10 Best iPaaS Companies: 0.Zluri 1.Zapier 2.Workato 3.Boomi 4.SAP 5.MuleSoft 6.Tray.io 7.Celigo 8.TIBCO 9.TeamDynamix 10.SnapLogic

Instant Onboarding & Offboarding - Automation in the New Normal
one of the biggest challenges of LCM is keeping up with the constant daily changes, either in digital identities or permissions. For example, when new employees join, they must be given appropriate access permissions. However, when an employee resigns, the process must be reversed, and their access must be revoked.

How to Grant Dynamic And Secured Access - 6 Tips from SaaS Ops Experts
It can figure out and suggest with 100% accuracy what tools the new users will need access to based on their job title and department. This makes it easier for IT asset managers to find and set up tools.

Top 9 SailPoint’s Lifecycle Management Software Alternatives
Null

Measures to Strengthen your Microsoft 365 environment
For example, M365, by default, allows users to freely share files and leave meetings open to anyone, which can be a security concern.
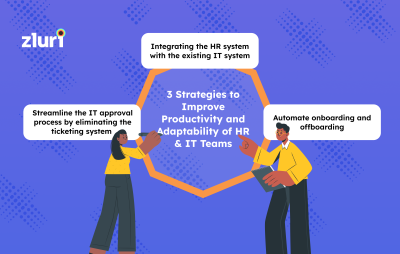
3 Strategies to Improve Productivity of HR & IT Teams
One of the HR and IT departments' most essential tactics is integrating the HR system with the IT system. This can help ensure that data is shared between the two departments, which can help improve the efficiency and accuracy of both.

Why Automating User Lifecycle Management is Crucial
User Lifecycle Management is a crucial component of any organization's IT infrastructure. It works on the principle of one user, one identity within one infrastructure. For example, IT admin makes one identity for one employee who attains all the required authorized access to SaaS applications in the business processes.

How To Boost IT Teams’ Efficiency with IT Process Automation
IT process automation, or ITPA, is the practice of automating IT services, support, and operational tasks into business workflows. It uses artificial intelligence, application programming interfaces (APIs), and other tools to automate repetitive tasks.

HR-Driven IT Provisioning Solution
In organizations practising manual methods, their HR will log employees' data in the HR system using spreadsheets. Further, the data will be delivered to the IT team in the form of a ticket by email.

4 Tips to Make a Successful Career in SaaS Management
While managing SaaS tools in an organization, it is necessary to develop strategic and analytics thinking. This helps the individual see how applications being considered for the organization will profit the business and streamline workflows.
![Top 11 ServiceNow Alternatives & Competitors [2024 Updated]- Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/3gshS8Mrbl7mmtcyhN9VBo/dc48b7883e925352619a34d9966d3c9c/Servicenow_Alternatives.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 11 ServiceNow Alternatives & Competitors [2024 Updated]
Exploring alternatives to ServiceNow? This blog highlights the top 11 ServiceNow alternatives & IT management solutions tailored to your business needs.

Here's How to Solve User Lifecycle Management Problem in Your Organization
One of the biggest challenges with LCM is keeping up with the constant changes in digital identities and permissions.

What is a Three-way Match & What is Its Importance?
Three-way matching is a validation process involving different stakeholders in the supply chain, and it's a crucial step in the procurement process. It involves matching a vendor or supplier's invoice to your company's purchase order and the delivery receipt or receiving the report.

5 Best Practices for Managing a Decentralised SaaS Environment
SaaS decentralization creates a flexible environment for employees to operate seamlessly in business processes. It improves productivity as it gives freedom to the employees to choose their required apps.

5 Ways To Practice Cost Avoidance While Buying SaaS
Cost avoidance is an effective technique for reducing software spending throughout the contract. However, poor procurement negotiation or lack of understanding of the contract terms and circumstances may lead to wasting thousands of dollars.

How Lifecycle Management is Associated with Regulatory Compliance
Maintaining evidence trails is crucial for audits as it helps to support the company's claim of adherence to regulatory frameworks. Evidence is used to verify the accuracy and compliance of a company and assist auditors in making informed decisions.

Use Zero Trust Security to Address SaaS Security Concerns
The SaaS applications are generally managed by a third party and are out of the organization's control. Therefore, it is difficult for companies to ensure that their SaaS apps are secure and data is maintained.

Getting Started with Zluri Lifecycle Management Tool
Zluri allows organizations to simplify complex IT processes to increase efficiency and maintain the flow of business processes.

4 Common SaaS Sources of Shadow IT
It discovers 100% of apps used in the organization and categorizes them according to their use case. So, if 32 analytics tools are being used inside the company, you can check if all of them are approved and even required.

4 SaaS Metrics You Should Continually Monitor and Report to the Management
It can be tracking renewal dates, managing application usage, tracking users, etc. To avoid letting this happen, there are specific SaaS reporting metrics that you must continually monitor. But which metrics should you rely on?

How CFOs can Leverage SMPs to Optimize SaaS Spending?
So, it becomes crucial for CFOs to manage SaaS spending to attain the organizational goal efficiently. CFO needs to monitor and regulate the expenditure on SaaS applications to do better cost management and get the ROI of apps.

Access Certification: An Ultimate Guide
Discover the importance of access certifications in ensuring regulatory compliance and safeguarding organizational security & enhancing operational integrity.

Top 9 NinjaOne Alternatives | 2024
The blog discusses the top 9 NinjaOne alternatives & the leading helpdesk solutions in 2024. Find the right platform for your ticketing & helpdesk needs today!

5 Ways for SaaS Cost Optimization During Recession
Due to the increased purchasing of Saas applications, it is becoming time-consuming to evaluate the organization's existing software and determine how it can be used effectively. This results in a need for more visibility into the SaaS stack, and businesses continue to make wasteful purchases, increasing SaaS expenses.

8 Commonly Confused IT Terms
Here is a list of commonly confused or interchangeably used IT terms to help you avoid conveying the wrong information and stay relevant.

5 Best Practices to Improve Your SaaS Procurement Process
SaaS procurement is a process that allows you to choose the right SaaS tools and vendors for your organization, assess their compliance and security standards and implement them properly.

Top 10 Multi-Factor Authentication Software for IT Teams
Discover the top 10 multi-factor authentication software empowering IT teams with enhanced security. Safeguard your digital assets with these MFA tools picks!

4 Signals that it's Time to Automate SaaS Management in Your Organization
IT automation is more beneficial than manually managing SaaS apps with spreadsheets. This is because it reduces the workload of IT teams.

What Is Budget Variance, And How Can It Impact Your SaaS Spend?
A budget variance is a difference between the amount allotted for a given department or project and the amount spent on it.
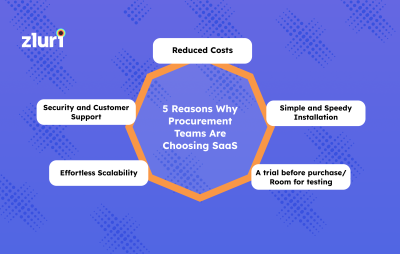
5 Reasons Procurement Teams Choose SaaS Over On-Premise Tools
Today, finding vendors for SaaS and screening them to ensure they adhere to the organization's primary security and compliance standards are part of the procurement process.
Top 11 Kissflow Alternatives & Competitors in 2024
Explore robust Kissflow alternatives in 2024 to elevate your process automation features tailored to your organization's unique business needs.

The Most Prevalent 10 SaaS Management Misconceptions That Every IT Team Must be Aware Of
Surprisingly, a large percentage of IT decision-makers and business executives need clarification about the management of SaaS apps.

Remote Work Security Best Practices for IT Teams
To prevent any data breach, it is important to ensure that employees, as well as security teams, have the right set of tools and methodologies to deal with the different challenges of remote work.

SaaS Spend Analytics: A Comprehensive Guide
Spend analytics is designed to identify areas that could use more attention so that valuable insight can be found in real-time, ensuring organizations can prioritize projects and streamline their entire process.

How to Automate IT Tasks
By automating routine and repetitive IT tasks, businesses can reduce errors, improve productivity, and free up valuable resources to focus on strategic initiatives.

Zluri Updates (November 2022): Bulk License Mapping, Workflow Automation
It's a new month again; with that, it's time for our latest set of updates that we have brought into the platform.

How Zluri Helps IT Teams Improve their Productivity
Zluri empowers you to take control of the SaaS stack of your organization. It offers various features which help you tackle and manage SaaS-related issues.

Software Asset Management with the SAM Beast David Foxen
David speaks about his passion for ITAM and SAM and his interest in the industry. He also talks about the changes ITAM has undergone in the last 12 years of his career. He also highlights how the SaaS landscape has made our lives easier and gives valuable insights into managing SaaS applications.

Implementing Zero Trust - A SaaS Management Perspective
Zluri makes a backup of the data in those apps while canceling the user's licenses so that the admin can transfer it to the newly hired owner.

How to Manage Software Assets
Software asset management (SAM) in the SaaS world is very different from traditional on-prem software asset management. Traditional SAM was focused on tracking and optimizing the software licenses.

KPIs for Modern IT Teams - 2024
The IT deployment success rate will help you to analyze the potentiality of the systems deployed for business growth.

4-Step Vendor Offboarding Checklist
Third-party risks are a big part of vendor offboarding procedures. An organization that doesn't have a centralized database of vendors and a well-defined offboarding process leads to significant risks like third-party data breaches and compliance issues.

6 Investments CIOs Must Make Before Recession Hits
An SMP provides your organization with a streamlined process for discovering, managing, sharing, and storing data and creating workflows to automate your tasks.

How SaaS Management Platforms helps in Eliminating Security Risks
An SMP gives a central place to discover SaaS apps in use throughout the organization automatically. It helps to manage and secure users, apps, data, files, folders, and user interactions within SaaS apps.

Zluri Updates (October): Action Scheduling, Due In Date For Playbooks, Reconnect Flow For Primary Source Integrations
As October comes to an end, it's time to roll out some latest product updates from Zluri.
SaaS Procurement vs SaaS Purchasing - What's the difference?
Purchasing is more transactional, but procurement is a strategic procedure that takes multi-departmental inputs while closing any deal for the company.

4 Ways of Revoking Access to Tools While Offboarding Employees
Most companies lack processes around deprovisioning SaaS apps while offboarding.

How IT Teams Can Automate Deprovisioning During Offboarding
Manual deprovisioning of apps makes offboarding complex and time-consuming for IT teams.

Zluri Updates (September): True up and downs in Licenses, Improved Source Filter, Google SSO Login
We have released some essential features like Amortization Settings in Licenses, Improvement in Source Filter and more this month. Apart from that, we have also developed many other enhancements & new direct integrations for this month to help you save time and money in managing SaaS.
8 Key Learnings about Shadow IT and Rethinking ITAM from Jeremy Boerger
Jeremy speaks about his Y2K experience and the struggles he dealt with On-prem software. He also speaks about Shadow IT, the advantages and challenges of the cloud, and how ITAM has helped organizations break through the challenges.
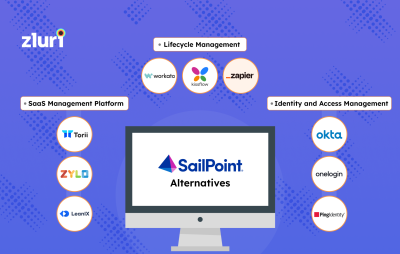
Top 10 SailPoint Alternatives & Competitors In 2024
Explore the top 10 SailPoint alternatives recommended by our experts to help your IT team streamline identity and access management process.

Reseller Agreements - A Definite Guide
IT resellers are involved in purchasing software, hardware, and many other services from manufacturers, wholesalers, and distributors and selling them to their customers.
SASE vs. CASB: Which is the Suitable Security Solution?
Discover the key differences between SASE and CASB to find out which solution aligns with your organization's security needs and make an informed decision.

5 Mistakes to Avoid While Estimating SaaS Spend
For your understanding, we have prepared a list of five common mistakes.

DLP Policies: A Guide To Strengthening Data Security
Unlock the secrets of robust Data Loss Prevention (DLP policies) and fortify your data security with our comprehensive guide. Explore now!

Why You Should Outsource Your SaaS Buying
SaaS procurement can take a lot of time and isn’t an easy job to be done. It requires expertise in evaluating SaaS products for their usage, security, and compliance and negotiating price and terms (SaaS agreements).
![Top 16 Business Process Management Tools [2024 Updated] - Featured Shot](https://images.ctfassets.net/eolgt3xbz2ko/3uiSYztbRztwEWivemqUWH/1c8b8c44c153890025b35e10dd54e69a/business_process_management_tools.png?w=400&h=254&q=50&fm=png&fit=pad)
Top 16 Business Process Management Tools [2024 Updated]
Discover the top 16 business process management tools of 2024 to streamline and optimize your operations with our definitive guide.
10 Best Ping Identity Competitors & Alternatives in 2024
We have handpicked 10 Ping Identity Alternatives like Zluri, Duo Security, LastPass, JumpCloud, Microsoft Azure AD, and more with their pros and cons.

4 Ways of Giving Quick Access to Tools While Onboarding Employees
Giving employees access to tools while onboarding is an important task for IT admins. Multiple ways to onboard new employees, like SMPs and SSOs, provide a seamless experience.

What Makes Zluri the Most Accurate SaaS Management Platform
Zluri has the largest direct integration number, over 750 applications, and keeps growing every month.

How Zluri Saves Time and Money for IT Teams
Zluri is a SaaS management platform that provides all of the features necessary to manage your SaaS apps.

Zluri Updates (August): SAML Login, Playbook delay feature , Bulk Onboarding/ offboarding
We have released some essential features like SAML Login, Playbook delay feature , Bulk Onboarding/ offboarding and more this month. Apart from that, we have also developed many other enhancements & new direct integrations for this month to help you save time and money in managing SaaS.

12 Vendor Security and Privacy Assessment Software (RFP Issuer and Responder)
Vendor security and privacy assessment software assists in identifying, evaluating, and regularly reevaluating the vendors.

Top 7 Tools for Managed Service Providers (MSPs)
When businesses outsource their IT services to managed service providers (MSPs), it gets complex for them to manage the IT tasks of multiple organizations.

How to Track Software License
The lack of appropriate software license management can cost your company time, money, and valuable resources. In order to optimize your valuable time and money, a centralized solution is a must that will track the various software licenses in the organization.

7 Tools for Eliminating Shadow IT that Actually Works
To eliminate all the risks arising from shadow IT, you need a tool to help you gain visibility to all the software in your organization.

Zluri Updates (July): Integrations version 2, Filters in workflows , Optimization Summary Report
We have released some essential features like "Integrations version 2", "Filters in workflows", and more this month. Apart from that, we have also developed many other enhancements & new direct integrations for this month to help you save time and money in managing SaaS.

How to Manage SaaS Renewals
Too many SaaS apps in the organization give rise to issues in managing SaaS renewals. It is quite time-consuming to keep track of a large number of SaaS app renewals.

6 SaaS Management Mistakes to Avoid
Traditional methods of keeping track of all SaaS applications and their purchases is a time-consuming, error-prone, and effortful task. Proper SaaS management helps discover, organize and streamline SaaS applications across the organization.

How to Optimize Your SaaS Spend
The more SaaS apps are used, the more difficult it becomes for IT departments to manage them. This is due to the limited visibility into the company's SaaS ecosystem and no ownership.

CASB Deployment Modes (And How to Choose?)
There are two types of CABS deployment modes, one is proxy, and the other is API.

An Overview of Zluri’s App Catalog & Access Request
The App Catalog & Access Request dashboard is loaded with the apps in your organization. Employees can find details like which apps they are using and what apps are used in their department. This helps employees choose the right apps that will meet their needs.

Top 8 Alternatives to Eracent
Zluri is a SaaS management platform that helps IT teams discover, optimize, manage and secure the SaaS apps in the organization.

Top 6 Alternatives to Beamy
Zluri is a SaaS management platform that helps IT teams discover, optimize, manage and secure the SaaS apps in the organization.

7 Software Procurement Services for Better SaaS Negotiation
Software procurement is a tricky job. For every app, there are multiple software vendors available, and you might be wondering how to get the best deal for your company.

How to Optimize Your Zoom Licenses with Zluri?
When there are multiple users for Zoom across an organization, its license management can be challenging.

How CIOs can Ensure Business-IT Alignment (BIA)
Business-IT alignment effectively uses a company's IT resources to accomplish the organization's business goals. In a strategic sense, it is a method for predicting the company's future information technology requirements, ensuring that it will be ready to address the challenges posed by its rivals.

Digital Resilience for Modern IT Teams
Digital Resilience supports businesses by providing a number of solutions to help them recover fast from disasters or disruptions utilizing digital technologies and processes.

How to Eliminate Shadow IT
With their increased adoption in recent times, SaaS apps make up for the major portion of shadow IT. They are the main driver of shadow IT, and this is a growing concern for IT teams.

Top 12 Resources for IT Teams
IT teams must equip themselves with the latest skills and knowledge and keep an eye on the latest technology updates and releases.

How to Optimize your Google Workspace Licenses
There are high chances that your current Google Workspace license is unoptimized. Inappropriate SaaS management practices may lead to inefficiencies in the form of unused licenses, redundant apps, and more. You might end up paying more than what is required. Moreover, it might raise compliance and security issues.

How to Become IT Director
An IT director is the head of the IT department of a company. They manage information and computer systems

Zluri Updates (June): Automation Rules, Download Licences & Contracts , Integration Admin Role
We have released some essential features like "Automation Rules", "Integration Admin role" and more this month. Apart from that, we have also developed many other enhancements & new direct integrations for this month to help you save time and money in managing SaaS.

IT Procurement Manager Job Description w/ Role & Responsibilities
IT procurement covers the activities involved in acquiring new technologies for your business. IT procurement brings a lot of responsibilities for IT procurement managers, that are required to smoothen the procurement process.

Privileged Identity Management - A Definite Guide
A privileged account is commonly used by IT administrators, security teams, helpdesk, application owners, database administrators, etc. And are usually secured by passwords, multi-factor authentications, keys, session recordings, and behavior analytics, to name a few.

Lessons from the Okta Breach for IT Asset Managers
Attackers belonging to the Lapsus$ hacking group successfully compromised an endpoint used by a third-party support engineer of the Site by connecting to it using RDP (Remote Desktop Protocol).

Zluri Updates (May): SaaS Governance Insights, Procurement Admin Role, SaaS Owners
We have released some essential features like "SaaS Governance Insights", "Workflow Overview" and more this month. Apart from that, we have also developed many other enhancements & new direct integrations for this month to help you save time and money in managing SaaS.

IT Security Manager Job Description
The work of the IT Security Manager comprises the planning and execution of security procedures that safeguard the data and information of an organization from being intentionally attacked, accessed without authorization, corrupted, or stolen.

IT Director Job Description
An IT Director oversees all information technology functions in the company. He/she is in charge of a team of IT managers and manages the company's technology operations. The implementation of new IT systems and policies is also done by an IT Director. Depending on the size and purpose of a company, the role of an IT director can vary greatly.

How to Become a CIO
A CIO must be able to look at technology from both a business and technical perspective. The CIO should be able to demonstrate their ability to drive organizational transformation, build a creative culture, and develop a strategy to align IT with business.

Steal Our CIO Job Description
The chief information officer (CIO) is the executive in charge of the company's entire IT strategy and objectives. The CIO is responsible for ensuring that the organization's particular goals are met via the implementation of the IT infrastructure.

Top 10 Tugboat Logic Alternatives
Compliance automation technology empowers businesses to streamline compliance-related workflows such as risk assessments, control evaluations, testing, and corrective action planning. As a result, it saves a lot of time compared to the manual process.

What is DLP & How Does it Work? Explained 101
Data loss prevention is one of the vital strategies that can prevent your sensitive information from getting leaked online. You need to understand the ins and outs of DLP to implement the strategies in your existing business ecosystem.

How to Retain IT talent
A company's commitment to employee retention is demonstrated via the implementation of policies and programs that reduce employee turnover.

SaaS Stats for CIOs & IT Heads
SaaS causes the proliferation of shadow IT, overspending, and security breaches. To curb all of these at once, IT leaders must be equipped with an automated SaaS Management tool that offers a centralized view of all the SaaS applications running in the organization.

ITAM vs. ITSM
ITAM and ITSM are the two most common responsibilities in the ITOps domain. The use cases and working approaches of the two, on the other hand, are complementary yet vastly different.
How to Establish SaaS Ownership in Your Organization
Bringing accountability and ownership across organizations for SaaS applications is one of the foundational steps to ensure that organizations' SaaS stack is optimized and fully utilized.

8 Tools for IT Teams in the Remote Workplace
IT and security teams also use tools for securing endpoint devices and applications that employees use so that organizations' data remains secure. Apart from collaboration, communication, and security, there are many other tools that organizations can use and provide to employees to ensure that work is done properly in a remote work setup.

Zluri Updates (April): Financial System Filters, Redundant Apps Report, and Custom Entity Type
We have released some essential features like "Redundant Apps Report", "Financial System Filters" and more this month. Apart from that, we have also developed many other enhancements & new direct integrations for this month to help you save time and money in managing SaaS.

Zluri Awarded ITAM Review Certification for Enterprise SaaS Management
We are beyond excited to announce that Zluri has received the Enterprise SaaS Management certification from the prestigious The ITAM Review.

9 Service Level Agreement Best Practices To Follow
Elevate your service delivery with these 9 essential service level agreement best practices. Ensure seamless operations and customer satisfaction for your organization.

How to Evaluate GDPR Compliance of Your SaaS Stack
Businesses have a growing dependency on SaaS apps, and they use different types of SaaS tools to function every day. Not having clear visibility of the SaaS apps you use should certainly make you question one thing, which is - how you will mitigate the risks that are associated with each of these SaaS tools.

Recruiting IT Talent: Elements of a Successful Hiring Strategy
The demand for IT talent is so high that employers cannot afford to simply sit back and wait for the right candidate to walk through the door.

How IT Teams Can Prevent Insider Threats in Organization
A malicious insider can steal the information knowingly. On the other hand, a negligent insider unknowingly or mistakenly acts as an agent for threat.

What it is like working as a content writer at Zluri?
I still remember my first day at Zluri. As an amateur writer coming from a journalist background, content writing for a B2B company was a bit overwhelming.

How to Stay Audit-Ready for HIPAA Compliance
It is always best to make the necessary changes to comply with HIPAA requirements before being notified of any audits. HIPAA compliance should be a must if you are a company that works with Protected Health Information. You need to be proactive as you hold the responsiblity to keep the information secure.
Top 9 Must-Read Books for CIOs & IT Executives
Looking for the best books for CIOs & IT leaders? Discover our top picks to enhance your IT knowledge and leadership skills.

SaaS Pricing Models: A Procurement Guide for IT Teams
The primary model of SaaS is paying a subscription fee for using a product/service. It involves ongoing payments that follow pricing models which the SaaS vendor might offer after considering their profits and value for the buyers.

Top SOC 2 Services (Firms)
Selecting a SOC 2 Auditor: While looking at the website, social reviews and asking in your network if they have worked with the firm that does SOC 2 audits are preliminary. There are various other factors such as price, experience/specialization, and process of conducting SOC 2 audit that you should also look for. Further, any firm conducting SOC 2 audit must be AICPA certified.

Key Metrics Every IT Asset Manager Should Track (ITAM KPIs)
There are different metrics that show the efficiency of your organization's IT asset management (ITAM) practices. From the number of used licenses to unused licenses to spare laptops, all show how efficiently your organization's software and hardware assets are managed.

Zluri Updates (March): Global Search, License/Contract Discount and Bulk Edit Licenses
We have released some essential features like "Global Search", "License/Contract Discount" and more this month. Apart from that, we have also developed many other enhancements & new direct integrations for this month to help you save time and money in managing SaaS.

7 Steps for Building a Strong Cloud Migration Plan
To begin with cloud migration, it is essential to do the groundwork first. It will help you better tackle the challenges that you will face later on in this process.

Types of Authentication Methods (Digital Authentication Methods)
You can think of digital authentication as the first line of defense against an organization's resources. It ensures that only authorized users have access to the organization's information.

SaaS Buying Made Easy for IT Teams
When it comes to SaaS buying, it is very important to understand how to choose a product worth the purchase in the long run. With so many SaaS options to choose from, enterprises have unlimited alternatives at their disposal.

What are SSO Security Risks and its Drawbacks
Single Sign-On (SSO) is convenient for users, but it creates new security risks for the organization. Instead of requiring users to log in separately for each resource, an SSO system allows organizations to use a single username and password to access multiple resources.

IT Budget Planning: 7 Tips to Keep in Mind
Having a well-laid out IT budget is crucial for your IT department as it provides them with a roadmap to project operations. Management can easily see where the money is going and what resources are available. This eliminates the need to justify or request any IT expenses later on.

Drawbacks of CASBs (Cloud Access Security Brokers) in the Remote World
While traditional cloud access security brokers had their share of benefits, organizations must understand why they aren’t suitable for modern requirements. And plan a way out to move to a modern cloud-first solution, like SaaS management platforms.

Zluri Updates (February): Upgraded Applications, Upgraded Users and Restricted App Emails
We have released some essential features like "Upgraded Applications", "Payment Term for Licenses" and more this month. Apart from that, we have also developed many other enhancements & new direct integrations for this month to help you save time and money in managing SaaS.

What is Shadow IT? How SaaS Apps are Driving the Next Wave of Shadow IT
SaaS apps makes up for the bulk of the shadow IT in organizations today.

Benefits of Shadow IT: A Latent Force Driving Innovation & Productivity
Though it poses compliance & security risks, it drives innovation in your company and improves your employees' productivity. One good SaaS app discovered by one team member can benefit the whole team. One rising tide lifts all the boats

Shadow IT Risks: Security, Compliance and Financial Risks due to SaaS Apps
Shadow IT in the SaaS world brings various security, compliance, and financial risks.

Employee Offboarding: 5 Security Guidelines for a Remote Workplace
Almost all employees use some kind of the company's services and assets in today's remote working system. For example, they may be provided with laptops, desktops, mobile phones, SaaS subscriptions, and access to the company's confidential data.

SaaS Lifecycle Management: How to Manage SaaS Vendors Lifecycle
Your SaaS lifecycle starts with finding the best vendor that suits your organization’s needs, managing those vendors, tracking their performance, terminating contracts, if needed.

Zluri Partners With Minet For The Israel Market
Zluri, a SaaS Management Platform that helps IT teams discover, secure, and manage their tech stack, has announced its partnership with the procurement and supply chain giant Minet Technologies based in Israel.

Zluri Updates (January): Recommendations, App-Wise Spend Reports and Custom Views
We have released some essential features like "App-wise spend report", "Custom views" and more this month. Apart from that, we have also developed many other enhancements & new direct integrations for this month to help you save time and money in managing SaaS.

SaaS Management Platform Zluri raises $10M led by MassMutual Ventures
SaaS Management Platform Zluri, has raised $10M in a Series A round of funding led by MassMutual Ventures with participation from existing investors, Endiya Partners and Kalaari Capital. Zluri had previously raised $2M, from Endiya Partners and Kalaari Capital, in its seed round in January 2021.
7 Software Asset Management Best Practices: From Reactive to Proactive
Getting aligned on your KPIs with the management is a critical first step to streamlining software asset management. Read on for a comprehensive understanding of the SAM best practices used by businesses around the world.

Zluri Updates (December): On/Off-boarding Workflows, Bulk Action Grouping and User activity Report
The biggest and the most expected feature release of the year, "Workflows automation," is all set and ready for you. Apart from that, we have also developed many other enhancements & new direct integrations for this month to help you save time and money in managing SaaS.

Mitigate SaaS Vendor Risks with Zluri
It's not enough to evaluate vendors at the time of onboarding. Continuous monitoring helps you keep a tab on your spending and the safety and protection of sensitive data.

Remote Onboarding Checklist for IT Teams
With work-from-home becoming the new normal, remote onboarding for new employees is the need of the hour. One of the most complicated tasks at this stage is giving new employees access to all the necessary software and web-based applications required.

Zluri Updates (November): User Merging, 2 Factor Authentication & Primary Source Selector
Zluri's main motto is to make SaaS management easy peasy lemon squeezy for our users. That's why we put in our best every day to set out new features and improvements every month. This month also we have updated Zluri with some valuable features that can help you ace SaaS Management. Let's have a look at them!

Preparing for a SOC 2 Audit? All You Need To Know
SOC2 stands for System and Organizational Control Level 2. It is a set of audit criteria used for assessing whether an organization has appropriate checks and balances in place for securely handling customer information.
Negotiating IT Contracts - The Comprehensive Guide
Negotiating a SaaS IT contract is the first step in ensuring quality service for your business. The benefits of a SaaS IT contract involve cost-effectiveness, reduced setup time, intuitive user interface, and better performance.

SaaS Stack for SMBs and Enterprises
Choosing the right SaaS tool can be challenging as there are many tools out there in the market for every need, and based on your requirements and preferences, you have to see which is best for you.

Zluri Updates (October): New Security & Compliance Module & License Optimization Report
We've released many new updates this month: New Security & Compliance Module, License Optimization Report, 55 Direct Integrations And More.

How It Feels to Be an Intern at Zluri: A Discussion with the Intern Class of 2021
Zluri welcomed 15 fireballs to help us out in DevOps, Marketing, and the Design team. All of them represented the reputed institution BITS Pilani in India. They have played a wholesome role in helping Zluri propel beyond and above.

How to Convince Your Boss to Invest in an SMP?
With proper data and reasoning you can convince your boss to go ahead with SMP. The benefit which the SaaS management platform adds to your organization is immense. Remember, in the post-pandemic world, SMPs are becoming a must for the IT department.

Employee Offboarding for IT & HR: A Data-Backed Case Study
The HR & IT departments have been facing the heat of offboarding a good number of the remote workforce since 2020.
Top 9 Freshservice Alternatives in 2024
Explore the top 9 Freshservice’s IT service management alternatives recommended by our experts to help your IT team streamline service desk operations.

Zluri Updates (September): Granular Authorization Types, Security Filters, & Vendors Contracts
We've released many new updates this month: Multiple Instances Connection, Granular authorization types, 35 New Direct Integrations and more.

What We Learnt Analyzing 150M+ SaaS Usage Transactions
Zluri recently hit a ground-breaking record of analyzing 200M SaaS usage transactions. The process taught us a lot of valuable lessons that helped us make Zluri better every day.

Managing SaaS in an Enterprise
Think about an enterprise that has more than 3000 employees. They need a clearly structured SaaS management plan; else, they will get into the trap of SaaS sprawl.

Zluri Updates (August): Browser Extensions & Security Module
Welcome to Zluri's latest product updates for August. We've released many new updates this month: Custom Sort, Filter, & Columns B

How SaaS is Powering the Next Big Revolution
With software getting ubiquitous, we believe a new revolution is coming—the software revolution. The SaaS delivery model has made software better, faster, and cheaper.

Deprovisioning: SSOs vs. Zluri
During deprovisioning, Zluri doesn't stop at SSO level authorization. It monitors the usage of the SSO system as well. For example, it monitors users for which apps they have access to, what level of permissions they have for the apps, their sign-in logs, audit logs, and access logs.

Zluri Updates (July): Getting Started Guide & Active Users
Welcome to Zluri's latest product updates for July. We've released many new updates this month: Getting Started Guide, Active Users, 37 New Direct Integrations and more.

Symptoms of an Unoptimized SaaS Stack (+ Solutions)
In this post, we've discussed 7 symptoms of an unoptimized SaaS stack and solutions to optimize the same.

Zluri Updates (June): New Integration Screen & Faster Onboarding
Welcome to Zluri's latest product updates for June. We've released many new updates this month: New Integration Screen, Faster onboarding, 14 New Direct Integrations and more.

Software License Optimization: How to Maximize Your ROSS (Return on SaaS Stack)
ROSS (Return on SaaS Stack) is a framework that helps you evaluate and optimize the value you get from your SaaS stack.

Zluri Updates (May): Category-Wise Spend, Multi-Currency Support & User Log
Welcome to Zluri's latest product updates for May. We've released many new updates this month:Category-Wise Spend, Multi-Currency Support & User Log, 8 new direct integrations and more.
Shadow IT in the SaaS World - A Complete Guide
In this post, you'll learn about shadow IT due to SaaS apps. You'll also learn the most common types of shadow apps categories, shadow IT risks, and shadow IT benefits.

How Different Industries Manage SaaS: A Data-Backed Study
In a partnership with Pulse, we conducted a survey to understand how various industries tackle SaaS Sprawl.

Zluri Updates (April): Scheduled Exports and Reports
Welcome to Zluri's latest product updates for April. We've released many new updates this month: Scheduled Exports and Reports, Manually Add Application Users and Usage and more.

A Framework to Eliminate SaaS Wastage
‘Muda’ is used to describe any activity that uses resources but doesn't generate value. It is the Toyota system for identifying and eliminating waste in all forms. It is the same thing that helps Toyota sell more cars than Ford, General Motors, and Honda at a higher margin.
SaaS Management: 3 Key Challenges
With this explosion of SaaS at companies, there arise SaaS challenges caused by apps getting out of your control. These SaaS challenges varies in three dimension: spend management, security and complance risks, and various SaaS operations tasks like automating SaaS procurments, renewals, employees onboarding and offboarding.

Zluri Updates (March): Notes, App Type, Merging & Mapping
Welcome to Zluri's latest product updates for March. We've released many new updates this month:‘Notes’ to keep track of your tasks, ‘Application Type’ feature to sort your SaaS stack from other applications and more.

Everything you need to know about the cloud marketplace before you step in
Initially, the cloud market just consisted of third-party apps. Now they have evolved bigger as a sophisticated distribution platform that offers its users the functionality to explore, procure, and deploy relevant SaaS applications at present.

Announcing our seed funding
In our endeavor to bring Zluri to life and build a sustainable organization, we have raised USD 2M from Endiya Partners and Kalaari Capital as seed funding. We are excited to have Sateesh Andra and Vani Kola on our board to help us along the way.

Let’s talk about SaaS security and why you must be proactive
Undoubtedly, Software as a service (SaaS) has changed how the global workforce operates

Do You Know Your SaaS Stack?
The question ‘Do you know your SaaS stack’ might sound pretty elementary at first glance.

Subscription-based Software (SaaS) is the Panacea for Almost Anything
Before sharing the software stack that we have deployed or about to deploy, I want to share how we make software buying decisions in the current boot-strapped stage of zluri.com.

20 Best Books to Accelerate Your Digital Transformation
Business benefits of digital transformation include higher enterprise-wide productivity and efficiency, enhanced user experience, in-depth and accurate insights, faster and better business decisions, and improved agility and innovation, resulting in increased business revenue and sustainability. We have got the 20 best books that can help you accelerate your digital transformation journey. Let's dive right in.

A plugin to boost your productivity on Google Meet
Remote work has been the norm for some time now and productivity tools have been on steroids for a while. Last month our team logged in 7 hours per day on an average over google meet. That’s a whole lot of time. Also, data from Techcrunch shows that Google Meet is one of the most downloaded app during these times

Understanding 'Shadow IT' and its Risks – Quick Intro
Shadow IT is essentially any software or hardware that runs without IT knowing about it. These can be

Why Zluri? Why now?
Nothing vast enters the life of mortals without a curse. - Sophocles

The Case for Building a SaaS Management Tool Ground Up
In the early part of my career (circa 2010), I had the privilege of working with some of the large Fortune 500 enterprises. During those days, the cloud wasn’t still too mainstream (Market Size - 5.56 Billion USD), and we were all fascinated looking at the data centers managed and maintained by my employer.

The Story of Forgotten Subscriptions & the Birth of Zluri
One Saturday evening, I got an email notification that I was charged $80 for an Adobe Creative cloud subscription. I was beyond confused—I could not recollect when I had purchased it.